- Cisco Community
- Technology and Support
- Networking
- Cisco Catalyst Center
- Re: 9200 switch Virtual Network
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
9200 switch Virtual Network
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-14-2019 09:37 AM - edited 06-14-2019 10:30 AM
Dears,
i have a question here, what is the limitation of 1 no's of virtual networks in 9200L series switches,
Thanks
- Labels:
-
Cisco DNA Center
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-15-2019 03:37 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-16-2019 03:05 AM
Can you elaborate your question ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-17-2019 12:13 AM
Hi,
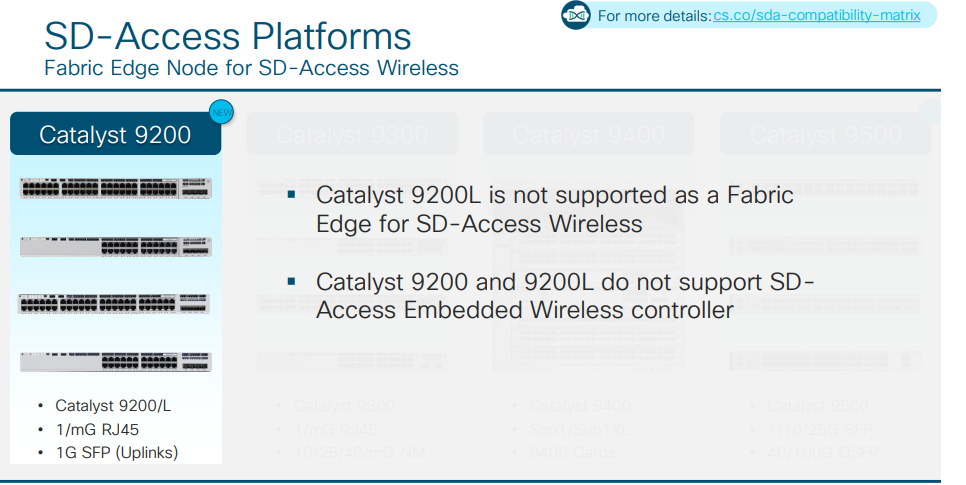
The 9200L switch is a basic equipment that intends to replace the 2960 for a branch office.
The 9200 model allows up to 4 VN, but the cost of the uplink makes you almost have to put 9300 as an access switch to be able to implement SD-Access without restrictions.
Be aware that with Wi-Fi controllers with 9200!- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-17-2019 09:59 AM
Total VNs or virtuals networks will be one in case of 9200 switch. This information is pulled from Cisco Datasheet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-18-2019 12:18 PM - edited 06-18-2019 12:22 PM
the virtual network's are the underlay network in the DNA center, ?? Please confirm
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-18-2019 06:51 PM
its actually the overlay. Also DNA Center is the controller, for managing everything including overlay network, the overlay can potentially span across multiple sites.
Interworking of SDA revolves around 3 protocols.
At Data plane - VxLAN
At Control plane - LISP
At Policy plane - Cisco TrustSec
This white paper is a good place to start learning more.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-21-2019 11:49 PM
Dears
so this means i cannot have a 2 PC's ( Corporate PC and Guest PC) on this switch with different Virtual Network , for example if i want a guest virtual network and corporate virtual network to co exist on this switch it is not possible, becz when DNA will push virtual network to switch it will accept only one instead of two numbers.
Please correct me
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-23-2019 03:40 PM
You are correct. Maximum one SD-Access Virtual Network (VN) on 9200L. So you can have either CORP VN or GUEST VN, but not both. Please also be advised that the restriction applies to the whole fabric site, not just the switch. If you have an SD-Access site with 40x C9300s and 1x C9200L, then the whole site is limited to one VN. This is because users could roam to anywhere at a site, so it's not possible to have different VNs on fabric edge switches at same SD-Access site.
Jerome
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-23-2019 10:19 PM
Dear Jerome,
Please also be advised that the restriction applies to the whole fabric site, not just the switch. If you have an SD-Access site with 40x C9300s and 1x C9200L, then the whole site is limited to one VN.
please elaborate more on the above statement.
OR in the other way to explain is as below.
That if we have multiple VN's on the network and it will be push from DNA to every switch hence the switch 9200L will not accept more than 1 , but if a user who is sitting on 9300 CORP VN and if he is moving to 9200L he will not get the access becz his port cannot be configured on the corp VN. this is what u want to mentioned.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-24-2019 05:21 PM
Hello,
DNA Centre will look at lowest capability switch in a fabric site and restrict the number of VNs on entire fabric site to the VN limit of the lowest capability switch. So, if you have a fabric site with 40x Cat 9300 and 1x Cat 9200L then the whole fabric site, including the Cat 9300 switches is limited to one VN.
Jerome
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-01-2020 10:52 AM - edited 04-01-2020 10:54 AM
Is there a roadmap to enhance the VNs at the 9200L or change the support of the VNs in the DNA - Center because we want to mount the 9200L sitches in case they have less depth to mount in the racks. But reducing the whole site to one VN is not
possible.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-01-2020 04:49 PM
I haven't heard about it, but you can reach out to your Cisco SE or AM, they will be able to get more recent info on this.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-25-2021 08:37 AM
Hi Jerome,
I know that is a old post, but this is still true?
Do you have any links from the Cisco docs about this?
Leonardo Santana
*** Rate All Helpful Responses***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-27-2019 05:53 AM
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide