- Cisco Community
- Technology and Support
- Data Center and Cloud
- Data Center and Cloud Knowledge Base
- Cisco ACI Ask the Experts FAQ: Network Automation & Programmability
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on
05-30-2021
08:38 PM
- edited on
02-15-2023
08:03 PM
by
Vivien Chia
![]()
Contents
- If there are multiple CSV files associated with different requests, how can this be achieved?
- I can associate domain to port directly in CLI mode, but must I call AEP in the interface policy group to associate domains in the GUI?
- Are there any samples or examples of creating multiple BDs/EPGs in one tenant and setting static ports in the EPG?
- What happens if the EPG was modified using the APIC before being deleted when restoring through terraform, wouldn't the changes be lost?
- In the subnet migration, what is the role of the 254 address that BD configured first? Because in the demo I saw that the address actually had been replaced.
- Since Ansible is ultimately converted to Python scripts, what is the difference between using Ansible and using Python directly?
- Is Terraform one of the recommended languages for Cisco in addition to Postman?
- Can I bring manually configured ACI information to the Terraform?
- Is it possible to operate PyCharm in a vi-like format?
- How do you handle sensitive data with Terraform? Ansible has something called vault where it encrypts the sensitive data and decrypts it when these variables are used.
- There’s three way of configuring ACI, via GUI/NXOS/Python, found that some of the show output mismatch while configure through CLI and GUI. Can we only use one method to configure ACI?
- Can you introduce the Rest interface structure of ACI and normally used actions?
- If we want to create a series of VLAN_EPG / adding multiple EPG to trunk. We can utilize the API Inspector to search all "POST" message required?
- What are the most commonly used links related to using Ansible with ACI?
- Any difference when using automation on Multi-site architecture?
- What are the available Cisco ACI utilities to effectively use the ACI REST APIs?
- Can I have more details about ACI Network programming interface architecture?
- Which are most commonly used ACI libraries?
- Can we use REST API for monitoring Cisco ACI?
- If we use Postman to get some Object - EPG etc then it contains some parameters that shows error 403 while pushing back. What exactly are those parameters?
Here are some commonly asked questions and answers to help with your adoption of Cisco ACI automated solutions. Subscribe (how-to) to this post to stay up-to-date with the latest Q&A and recommended Ask the Experts (ATXs) sessions to attend.
If there are multiple CSV files associated with different requests, how can this be achieved?
A: If it is in a collection you can select multiple requests by runner, a collection can only select a CSV file, it is recommended to summarize the variables to be used in these requests to the same csv file to execute together.
Recommended ATXs: Use Case Overview Planning: Automation and Programmability
I can associate domain to port directly in CLI mode, but must I call AEP in the interface policy group to associate domains in the GUI?
A: Yes, you’re correct.
Recommended ATXs: Use Case Overview Planning: Automation and Programmability or Deployment Best Practices: Automation and Programmability
Are there any samples or examples of creating multiple BDs/EPGs in one tenant and setting static ports in the EPG?
A: You can check the link for sample code by using Python within GitHub .
Recommended ATXs: Advanced Feature Overview: Using Python with Cisco ACI
What happens if the EPG was modified using the APIC before being deleted when restoring through terraform, wouldn't the changes be lost?
A: If the EPG/Tenant objects were created using TF then the tfstate will hold the latest info, if there are changes outside of TF then the changes must be imported manually to update the tfstate file.
Recommended ATXs: Adapting to Changes: DevOps Trends and Cisco ACI or Monitoring Best Practices: ACI with Ansible and Terraform
In the subnet migration, what is the role of the 254 address that BD configured first? Because in the demo I saw that the address actually had been replaced.
A: Before GW migrates to fabric, the server traffic is looking for external gateway. But the gateway needs to be deployed on the fabric leaf in advance to avoid packet loss after the server is migrated to the fabric. The demo does not perform the deletion, but replaces it with the real GW address in order to ensure the continuity of the network traffic, transit of virtual gateway to real GW.
Recommended ATXs: Deployment Best Practices: Automation and Programmability
Since Ansible is ultimately converted to Python scripts, what is the difference between using Ansible and using Python directly?
A. In fact, the purpose of using both ansible and python is to better deploy our ACI through automation, and both are good for repetitive daily tasks such as deploying repeatable environments. While python requires relatively basic programming skills, for ansible there is relatively less requirement for programming skills and the YAML format is more readable and easy to understand. In addition, Ansible provides a number of modules to support the management and operation of Cisco products. Customers can leverage these existing Ansible modules to accelerate their development.
Recommended ATXs: Use Case Overview Planning: Automation and Programmability or Advanced Feature Overview: Using Ansible with Cisco ACI or Advanced Feature Overview: Using Python with Cisco ACI or Upgrade Planning Best Practices: Automating ACI Upgrade with Ansible
Is Terraform one of the recommended languages for Cisco in addition to Postman?
A. Postman, Terraform, Ansible, Python, etc. are all available. Which automation tool you use depends on your current environment, business needs, etc. Many tools are complementary to each other.
Postman is a popular third-party REST API tool for interacting with the object store in ACI. It is very useful for testing API calls. Unlike Visore and Moquery, Postman can not only retrieve object information but also make configuration changes. If the target device uses JSON/XML, Postman can be used for integration. Postman can also interact with and manage network and server operating systems - so it is highly scalable. Postman can be used for initial deployment and creation of large numbers of BDs, vrf, tenant, etc., as well as GW migrations.
Ansible is a frequently used tool in Cloud Center, and no programming background is required to use Ansible.
Ansible is very versatile and scalable: it can manage many different operating systems and platforms. For example, network devices, servers, firewalls, etc. From the perspective of Cisco products, it can manage ACI, NX-OS, IOS, IOS-XR, etc.
Ansible is based on YAML. Unlike unintuitive Python scripts, YAML is a highly interpretable form that is easy for users to understand. Playbooks can be written to configure, deploy and coordinate multiple tasks and provide some more advanced functionality. Ansible and python are ideal for repetitive daily tasks - deploying repeatable environments.
Terraform uses the HCL language, which requires no development background and allows you to quickly deploy, build, and orchestrate configurations by simply calling the Resource that has been developed for each solution.
Terraform supports Cisco ACI as well as other Cisco solutions such as Intersight, and most public cloud environments. So with just the ability to use the HCL language, you can use Terraform in a variety of environments, which is one of the advantages of Terraform. We will also have related ATXs sessions to introduce the use of python, ansible, and in the DevOps course we will also introduce the use of terraform. Feel free to join us if you're interested in any of them.
Recommended ATXs: Use Case Overview Planning: Automation and Programmability or Advanced Feature Overview: Using Ansible with Cisco ACI or Advanced Feature Overview: Using Python with Cisco ACI or Upgrade Planning Best Practices: Automating ACI Upgrade with Ansible
Can I bring manually configured ACI information to the Terraform?
A. It's possible. Using the import function supported by Terraform, you can import configurations prior to terraform application into the terraform.
Recommended ATXs: Adapting to Changes: DevOps Trends and Cisco ACI or Monitoring Best Practices: ACI with Ansible and Terraform
Is it possible to operate PyCharm in a vi-like format?
A. You can perform the same operations as in a normal text editor. See more information.
Recommended ATXs: Use Case Overview Planning: Automation and Programmability or Advanced Feature Overview: Using Ansible with Cisco ACI or Advanced Feature Overview: Using Python with Cisco ACI or Upgrade Planning Best Practices: Automating ACI Upgrade with Ansible
How do you handle sensitive data with Terraform? Ansible has something called vault where it encrypts the sensitive data and decrypts it when these variables are used.
A. For opensource Terraform you can use a backend that supports encryption or in your vars file you can use 'sensitive' tag for a particular variable if you want to perform the operation manually or you can set a environment variable to store a password variable similar to AWSCLI auth. Additionally, you can use Terraform Cloud/Terraform Enterprise which provide masking feature for variables, or you can use Hashicorp Vault for your security perspective. Learn more.
Recommended ATXs: Adapting to Changes: DevOps Trends and Cisco ACI or Monitoring Best Practices: ACI with Ansible and Terraform
There’s three way of configuring ACI, via GUI/NXOS/Python, found that some of the show output mismatch while configure through CLI and GUI. Can we only use one method to configure ACI?
A. Suggest using GUI or Python to configure the device since some configurations done through the NX-OS style CLI are rendered in the APIC GUI. They can be seen but sometimes may not be editable in the GUI. Also changes made in the APIC GUI may be seen in the NX-OS style CLI but may not partially work. While mixing NX-OS style CLI and APIC GUI together may have some impact while doing per-interface configuration. Information detailed please refer this link below for the Mixing the NX-OS style CLI and APIC GUI part.
Recommended ATXs: Use Case Overview Planning: Automation and Programmability or Advanced Feature Overview: Using Ansible with Cisco ACI or Advanced Feature Overview: Using Python with Cisco ACI or Upgrade Planning Best Practices: Automating ACI Upgrade with Ansible
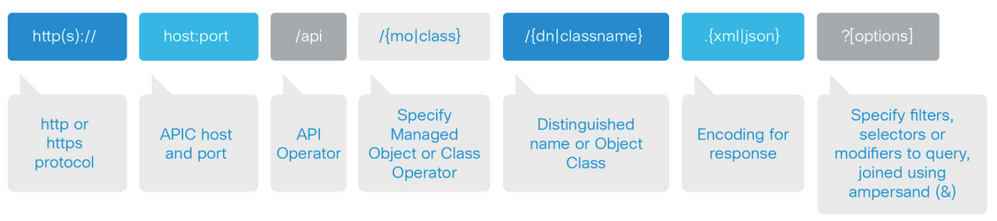
Can you introduce the Rest interface structure of ACI and normally used actions?
A. The call to the REST interface has the following structure:
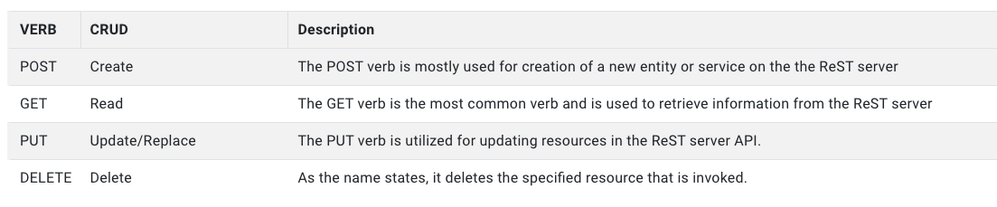
Rest (Representational state transfer) uses a set of Verbs to represent the actions that a request to the service is intended to accomplish. These verbs are GET, PUT, POST, DELETE and more.
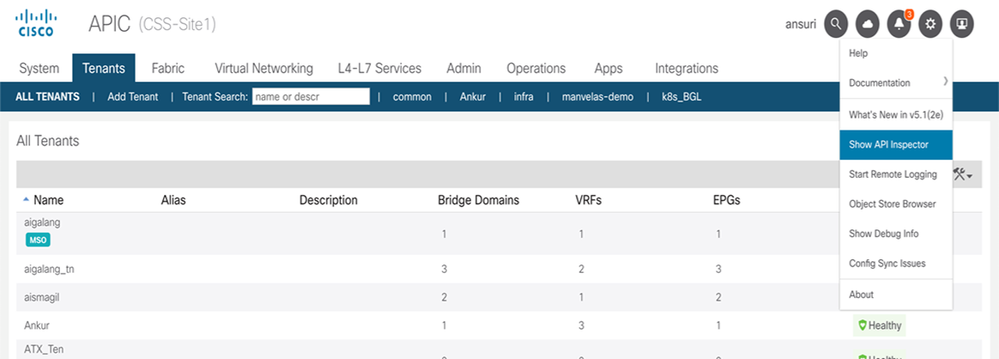
If we want to create a series of VLAN_EPG / adding multiple EPG to trunk. We can utilize the API Inspector to search all "POST" message required?
A. Yes, if you do not know how to write the payload, you can first create a VLAN_EPG , then copy the payload from API Inspector to postman. In API Inspector, need to search all “post” information and find the specific one for creating VLAN_EPG.
If you got multiple tasks need to do at the same time, please use Postman Runner to run multiple tasks.
Recommended ATXs: Deployment Best Practices: Automation and Programmability
What are the most commonly used links related to using Ansible with ACI?
A. Below links will help you understand how to install Ansible, use play command, build the playbook if you’re using Ansible for the first time:
Recommended ATXs: Use Case Overview Planning: Automation and Programmability or Advanced Feature Overview: Using Ansible with Cisco ACI or Advanced Feature Overview: Using Python with Cisco ACI or Upgrade Planning Best Practices: Automating ACI Upgrade with Ansible
Any difference when using automation on Multi-site architecture?
A. Like getting payload by using API inspector working with ACI, we’ve also got Swagger (Open API) to get the payload and working with MSO. Refer to more information related to Multi-site automation by using Ansible here.
Recommended ATXs: Use Case Overview Planning: Automation and Programmability or Advanced Feature Overview: Using Ansible with Cisco ACI or Advanced Feature Overview: Using Python with Cisco ACI or Upgrade Planning Best Practices: Automating ACI Upgrade with Ansible
What are the available Cisco ACI utilities to effectively use the ACI REST APIs?
A. API Inspector: The API Inspector is included in the APIC GUI. It provides a real-time display of REST API commands that the APIC processes to perform GUI interactions. The APIC user login drop-down menu includes the API Inspector option which opens the window shown in the figure below.
The API Inspector dynamically displays REST commands issued by the APIC. All operations that are performed in the GUI invoke REST calls to fetch and commit the information being accessed.
Visore Managed Object Viewer
Visore is a read-only management information tree (MIT) browser as shown in the figure below. It enables distinguished name (DN) and class queries with optional filters.
The Visore managed object viewer is provided with the APIC. It is at this location: http(s)://host[:port]/visore.html
Management Information Model Reference
The Management Information Model (MIM) contains all of the managed objects in the system and their properties.
The ACI object model is represented in the Management Information Tree (MIT) that is an object oriented data base. Every branch represents a functional area, and every node is a managed object - has a CLASS and a globally unique Distinguished Name formed by a parent name and the relative name.
Recommended ATXs: Use Case Overview Planning: Automation and Programmability / Deployment Best Practices: Automation and Programmability
Can I have more details about ACI Network programming interface architecture?
A. The REST API has both northbound and the southbound programmatic interfaces. The northbound REST API accepts configuration and access to management functions of the APIC. This interface provides access for automation tools, provisioning scripts and third party monitoring and management tools.
Southbound interfaces on the APIC allow for the declarative model of intent to be extended beyond the fabric, into subordinate devices. This is a key aspect to the openness of the ACI fabric, in that policy can be programmed once via the APIC and then pushed out to hypervisors, L4-7 devices and more, without the need to individually configure those devices. This southbound extension is realized through L4-7 Device Packages and the OpFlex protocol.
The L4-7 device package interface allows for ACI to apply policy to existing L4-7 devices that do not have an implicit knowledge of ACI policy. These devices can be from any vendor, so long as the device has some form of interface which is accessible via IP.
OpFlex is designed to allow the exchange of data for managed objects that are part of an informational model.
Recommended ATXs: Use Case Overview Planning: Automation and Programmability or Advanced Feature Overview: Using Ansible with Cisco ACI or Advanced Feature Overview: Using Python with Cisco ACI or Upgrade Planning Best Practices: Automating ACI Upgrade with Ansible
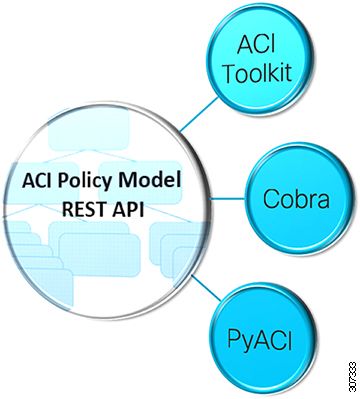
Which are most commonly used ACI libraries?
A. ACI provides a variety of access methods to read and manipulate this data.
All 3 libraries are simply wrappers to access the Rest API. Largely a tradeoff between personal preference, need for completeness, comfort with the ACI object model, and requirement for formal support beyond an active community.
APIC Toolkit
ACI Toolkit attempts to make life easier for the developer. Python libraries that allows you to quickly get the most common ACI workflows up and running. While the ACI Toolkit provides some useful tools for an operator to immediately use, the real value is in the ability to take these examples as a starting point, and modify or extend these samples to suit your particular needs.
Cobra
Cobra provides complete access to the object model but may be more difficult for beginning developers. The ACI engineering team uses Cobra. Much of the CLI on the ACI switches was developed with Cobra.
PyACI
PyACI provides alternative Python bindings for ACI REST API with the option to use XML or JSON payload. Facilitates authoring concise scripts Provides better logging.
Recommended ATXs: Use Case Overview Planning: Automation and Programmability or Advanced Feature Overview: Using Ansible with Cisco ACI or Advanced Feature Overview: Using Python with Cisco ACI or Upgrade Planning Best Practices: Automating ACI Upgrade with Ansible
Can we use REST API for monitoring Cisco ACI?
A. Application Policy Infrastructure Controller (APIC) saves network administrators time and frustration as it makes it easy to gather statistics and perform analyses using REST API. Because statistics are gathered automatically and policies are used and can be re-used in other places, human effort and error are minimized. Please use the guide to list down important ACI parameters which can be monitored.
Recommended ATXs: Adapting to Changes: DevOps Trends and Cisco ACI or Monitoring Best Practices: ACI with Ansible and Terraform
If we use Postman to get some Object - EPG etc then it contains some parameters that shows error 403 while pushing back. What exactly are those parameters?
A. 403 basically represents a component which is part of the ACI fabric object but can not be configured from ACI external. So based on the error it seems like lcown is an ACI internal object and hence you might want to remove it before POSTing. 403 error comes when the object is valid but can not be implemented by ACI Rest API calls.
Recommended ATXs: Deployment Best Practices: Automation and Programmability
|
Need more resources? Access the latest guides, recordings, other FAQs and more via Cisco ACI ATXs Resources. Want to learn more and get real-time Cisco expert advice? Through live Q&A and solution demos, Ask the Experts (ATXs) real-time sessions help you tackle deployment hurdles and learn advanced tips to maximize your use of Cisco technology. View and register for the upcoming Ask the Experts (ATXs) sessions today. [Pro tip: Subscribe to the event listing for new session updates.] |
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: