- Cisco Community
- Technology and Support
- Security
- Network Access Control
- ISE DACL does not allow host to obtain DHCP address from cisco switch
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ISE DACL does not allow host to obtain DHCP address from cisco switch
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-23-2022 09:48 AM
We run ISE version 2.4
We have a DACL that gets assigned to specific MAC addresses to restrict their access to the LAN.
One of the entries in the DACL is as below to allow the host to pick up a DHCP address
permit udp any eq bootpc any eq bootps
When we host the DHCP on a remote server this works fine.
If we host DHCP services on a local cisco switch the host never picks up an IP address
Even if I change the DACL so it has a "permit any any" entry it still does not pick up an IP address.
It would seem that unless the DHCP requests are forwarded it does not reference the DACL until it picks up an IP address.
How can I assign a DACL in this situation?
- Labels:
-
Network Management
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-23-2022 09:58 AM
Hello,
--> If we host DHCP services on a local cisco switch the host never picks up an IP address
What do you configure on the switch, can you post the output of 'sh run' ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-23-2022 11:34 AM
NO ip dhcp snooping information option
I think since Core don't not config with DHCP snooping it refuse the DHCP request.
so add command above to access SW and check again.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-24-2022 01:06 AM
Hi All
The DHCP server does assign IP addresses to clients as long as there is no DACL applied to the interface.
It is not DHCP snooping or it would not assign IP addresses under any circumstances.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-24-2022 05:39 AM
OK. make sure remove dot1x config from any port assign VLAN to that port and see if client get IP from DHCP server WHEN the Core is DHCP server.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-24-2022 05:47 AM
It does work when dot1x is enabled as long as it does not have a DACL applied to the interface.
If I remove dot1x it also works as the DACL does not get applied.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-24-2022 05:56 AM
before authz the port from ISE,
do show access list
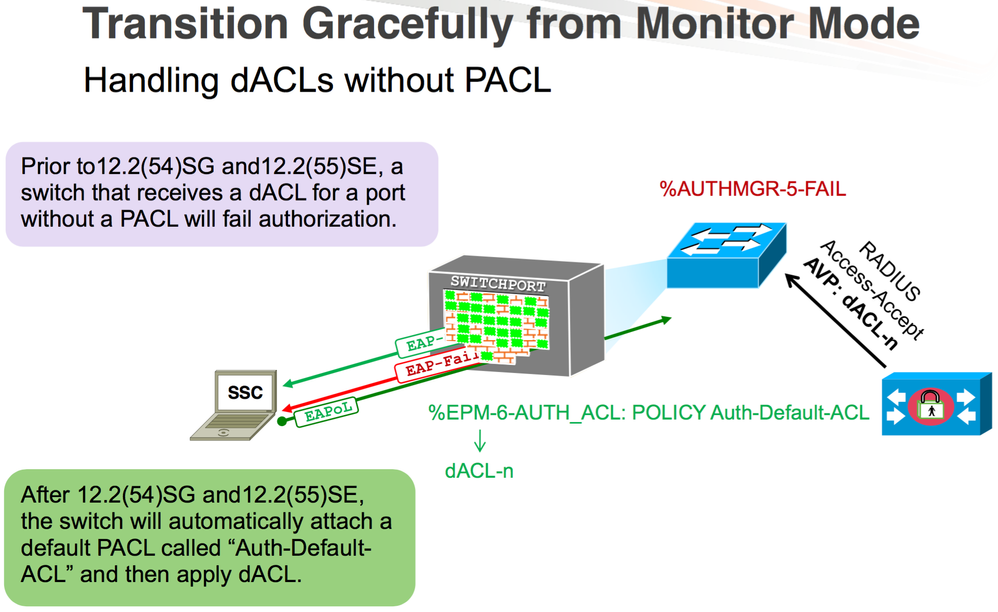
the DACL is add as PACL to port, so see if there is default PACL or not, if there is no add PACL and allow DHCP server connection, keep notice the DACL is add above the PACL line.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-23-2022 11:30 PM
The DACLs should handle the traffic even when the switch itself is the DHCP
Server. Can you debug ip dhcp server on the switch to see if the packets
are coming?
**** please remember to rate useful posts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-24-2022 05:02 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-29-2022 06:21 AM
I have done more testing and it seems it is not that the DACL is restricting access to the DHCP server, the DACL is simply not being applied.
If I remove the DACL from the Auth Profile the client authenticates, authorizes and is able to connect.
If I add the DACL to the AuthProfile the ISE logs show authentication and authorization is successful but the switch never authorizes the client and the DACL is not applied.
The ISE server is at a remote site behind a VPN hosted between two checkpoint firewall, I suspect the problem may be here somewhere.
These are packet captures from the Checkpoint firewall:
No Shutdown Access Port (no DACL Applied)
13:00:46.196700 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 345: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0xdf length: 301
13:00:46.468821 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 201: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Accept (2), id: 0xdf length: 157
13:00:46.483331 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 370: 10.240.100.15.58557 > 10.241.100.15.1646: RADIUS, Accounting Request (4), id: 0xb2 length: 326
13:00:46.740692 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 64: 10.241.100.15.1646 > 10.240.100.15.58557: RADIUS, Accounting Response (5), id: 0xb2 length: 20
13:00:46.742272 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 400: 10.240.100.15.58557 > 10.241.100.15.1646: RADIUS, Accounting Request (4), id: 0xb3 length: 356
13:00:47.000704 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 64: 10.241.100.15.1646 > 10.240.100.15.58557: RADIUS, Accounting Response (5), id: 0xb3 length: 20
Shutdown Access Port
13:01:32.434816 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 412: 10.240.100.15.58557 > 10.241.100.15.1646: RADIUS, Accounting Request (4), id: 0xb4 length: 368
13:01:32.692773 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 64: 10.241.100.15.1646 > 10.240.100.15.58557: RADIUS, Accounting Response (5), id: 0xb4 length: 20
No Shutdown Port (DACL Applied)
13:01:51.698746 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 345: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0xe0 length: 301
13:01:52.021105 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 275: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Accept (2), id: 0xe0 length: 231
13:01:52.027475 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 190: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0xe1 length: 146
No further response when port shut down
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-29-2022 06:09 PM
I hope this solve your issue, find below this note from cisco
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2022 03:32 AM
The Access Switch is a C3850 running 16.12.07
We have sites behind a DMVPN tunnel that work perfectly.
The two sites we have behind a VPN managed by Checkpoint gateways does not work.
ISE logs show auth was successful but if you look on the switch the port is in an unauthorized state and the DACL is not applied. The connecting device has a static IP assigned as DHCP would not assign an IP as the port is unauthorized.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2022 04:30 AM
There is check point the only reason make it stop CoA is port use by ise is block by check point.
I attach some port need for ISE.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2022 06:06 AM
We allow all traffic over the tunnel between our two networks.
Collected some more debugs, seems that when a DACL is applied it cycles between Access Challenge and Access Request.
10.241.100.15 is the Access Switch and 10.241.100.15 is the ISE server.
With no DACL:
11:22:14.559669 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 345: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x57 length: 301
11:22:14.831033 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 201: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Accept (2), id: 0x57 length: 157
11:22:14.844121 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 370: 10.240.100.15.58557 > 10.241.100.15.1646: RADIUS, Accounting Request (4), id: 0xe8 length: 326
11:22:15.099517 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 64: 10.241.100.15.1646 > 10.240.100.15.58557: RADIUS, Accounting Response (5), id: 0xe8 length: 20
11:22:17.039674 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 400: 10.240.100.15.58557 > 10.241.100.15.1646: RADIUS, Accounting Request (4), id: 0xe9 length: 356
11:22:17.294920 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 64: 10.241.100.15.1646 > 10.240.100.15.58557: RADIUS, Accounting Response (5), id: 0xe9 length: 20
With DACL in Auth Profile:
11:20:54.543484 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 378: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x4b length: 334
11:20:54.799208 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 173: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Challenge (11), id: 0x4b length: 129
11:20:54.804109 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 599: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x4c length: 555
11:20:55.057090 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 1185: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Challenge (11), id: 0x4c length: 1141
11:20:55.061545 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 433: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x4d length: 389
11:20:55.315242 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 1181: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Challenge (11), id: 0x4d length: 1137
11:20:55.320105 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 433: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x4e length: 389
11:20:55.573136 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 1181: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Challenge (11), id: 0x4e length: 1137
11:20:55.583272 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 433: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x4f length: 389
11:20:55.837131 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 1181: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Challenge (11), id: 0x4f length: 1137
11:20:55.841461 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 433: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x50 length: 389
11:20:56.096419 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 1181: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Challenge (11), id: 0x50 length: 1137
11:20:56.100885 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 433: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x51 length: 389
11:20:56.355026 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 200: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Challenge (11), id: 0x51 length: 156
11:20:56.363536 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 1412: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x52 length: 1368
11:20:56.363596 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 553: 10.240.100.15 > 10.241.100.15: udp
11:20:56.617143 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 173: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Challenge (11), id: 0x52 length: 129
11:20:56.621672 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 1412: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x53 length: 1368
11:20:56.621725 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 553: 10.240.100.15 > 10.241.100.15: udp
11:20:56.875091 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 173: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Challenge (11), id: 0x53 length: 129
11:20:56.879808 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 1412: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x54 length: 1368
11:20:56.879859 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 452: 10.240.100.15 > 10.241.100.15: udp
11:20:57.147458 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 264: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Challenge (11), id: 0x54 length: 220
11:20:57.154941 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 433: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x55 length: 389
11:20:57.465109 Out 00:1c:7f:80:aa:e4 ethertype IPv4 (0x0800), length 443: 10.241.100.15.1645 > 10.240.100.15.58417: RADIUS, Access Accept (2), id: 0x55 length: 399
11:20:57.472961 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 190: 10.240.100.15.58417 > 10.241.100.15.1645: RADIUS, Access Request (1), id: 0x56 length: 146
11:21:02.472703 In 00:42:5a:ff:9b:e2 ethertype IPv4 (0x0800), length 190: 10.240.100.15.58417 > 10.193.185.220.1645: RADIUS, Access Request (1), id: 0x56 length: 146
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2022 06:31 AM
aaa server radius dynamic-author <- do you add this command to SW?
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide