- Cisco Community
- Technology and Support
- Security
- Duo Security
- Protecting Applications
- DUO MFA, Microsoft RRAS Setup, no option to change authentication provider because NPS is installed
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
DUO MFA, Microsoft RRAS Setup, no option to change authentication provider because NPS is installed
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-02-2023 04:59 AM
Hi,
I have a Windows Server 2016 Standard running the Duo Authentication Proxy, we currently protect Microsoft 365 with SSO, RD Gateway and Windows Logon, the next step is for us to protect the VPN Microsoft RRAS.
I have followed the instructions but when i get Change the RRAS Authentication Settings, I do not have the option to change authentication provider because NPS is installed.
What are the next steps? The documentation doesn’t cover this
- Labels:
-
VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-27-2023 08:40 PM
Hi AdamKnowles, Welcome to the Duo Community!
If you follow the Duo for RRAS documentation at duo.com/docs/rras and you have NPS and RRAS installed on the same server, you will need to follow a different set of instructions after successfully installing and configuring the Duo Authentication Proxy. This guide is not fully supported but has been used successfully to resolve support cases.
Please note that we do not recommend installing the Authentication Proxy on a shared, multi-purpose server.
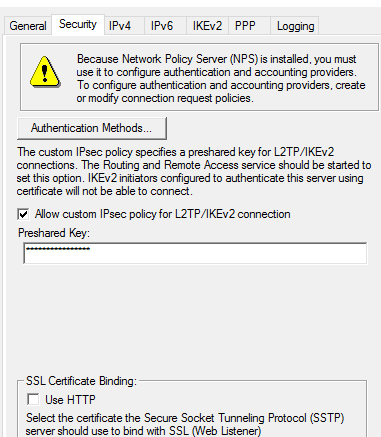
- Open the Routing and Remote Access management console.
- Right-click on your RRAS server and select Properties.
- Check the Allow custom IPsec policy for L2TP connection checkbox.
- Add your RADIUS secret in the Preshared Key section in NPS.
- Increase the RADIUS timeout to 60 seconds in the RADIUS server settings.
- Go to NPS > Remote RADIUS Server and set up a Remote RADIUS Server Gateway and point it at your Authentication Proxy’s IP address. Name it something you will remember. In this example it’s named DAG, but please note that these instructions do not involve a Duo Access Gateway in any way.
- In the NPS settings, go to Policies > Remote RADIUS Server and select the Microsoft Routing and Remote Access Service Policy properties.
- In the properties window, select the Settings > Authentication tab and then select Forward requests to your setup RADIUS server group. Select the group created in Step 2.
As noted above, it is not recommended to put the Auth Proxy on a shared, multi-purpose server, but if you do decide to put it on the same server as both RRAS and NPS, you will also need to make the following changes:
- Add the nas_ip= option to your Authentication Proxy’s [radius_client] section, and set it to a unique IP address that you wish to use for identifying Authentication Proxy traffic.
- Create a Connection Request Policy filtered to this NAS IP.
- Set the Settings > Authentication tab settings to “Authenticate requests on this server”.
- Ensure that this policy has higher priority than the one which forwards requests based on the Client IP.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide