- Cisco Community
- Technology and Support
- Networking
- Software-Defined Access (SD-Access)
- Re: How to setup authorization policy for site 1 and site 2
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2020 05:55 AM
I am setting up a SDA Demo using DNAC 1.3.3.7 and ISE 2.7 patch 1. I will have VN and IP Pool as below
| Site | IP Pool | VN | ISE VLAN tag ID/Name |
| 1 | 172.168.1.0/24 | Employee1 | 172_168_1_0-EMPLOYEE1 |
| 2 | 10.1.1.0/24 | Employee2 | 10_1_1_0-EMPLOYEE2 |
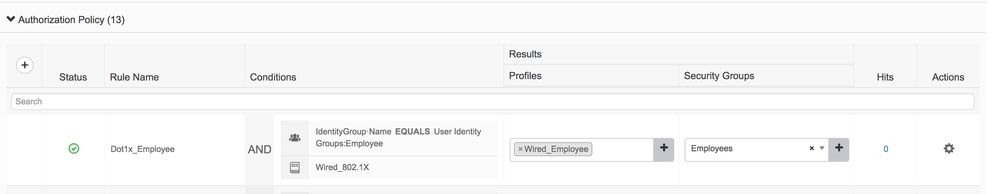
In ISE, I will setup authorization policy like below:
I want to modify this policy to two policies. One for site 1 and other one for site 2. My question is, I don't know how to modify the condition to match site 1 and site 2?
Solved! Go to Solution.
- Labels:
-
SD-Access
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2020 06:31 AM
Hello
You may group devices on each site and apply appropriate policy on specific group
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2020 07:10 AM
You have a few options. You could create two separate global radius policies and then rely on the normalised radius flow type (8021x), and the condition 'DEVICETYPE'. Utilizing DEVICETYPE you could group NADs to their respective areas, and build out the policies this way. However, this may interfere with a main benefit of SDA, the mobility aspect. I think a better option is to breakout your authz policies. Is it possible to integrate with two separate AD points, and then utilize the ExternalGroups condition? If not, for demo purposes why not just create two separate local ISE identity groups and reference each one individually and push policy for each respective site. This would be the quick way to do it IMO. Lastly, as another option you could focus on device profiling. In this scenario identify unique attributes ISE has gathered from the NAD sensors, and push policy based on profiled identity groups. The trick here is determining which attribute/s sets site1 and site2 a part from each other. HTH!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2020 06:31 AM
Hello
You may group devices on each site and apply appropriate policy on specific group
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2020 07:10 AM
You have a few options. You could create two separate global radius policies and then rely on the normalised radius flow type (8021x), and the condition 'DEVICETYPE'. Utilizing DEVICETYPE you could group NADs to their respective areas, and build out the policies this way. However, this may interfere with a main benefit of SDA, the mobility aspect. I think a better option is to breakout your authz policies. Is it possible to integrate with two separate AD points, and then utilize the ExternalGroups condition? If not, for demo purposes why not just create two separate local ISE identity groups and reference each one individually and push policy for each respective site. This would be the quick way to do it IMO. Lastly, as another option you could focus on device profiling. In this scenario identify unique attributes ISE has gathered from the NAD sensors, and push policy based on profiled identity groups. The trick here is determining which attribute/s sets site1 and site2 a part from each other. HTH!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide