- Cisco Community
- シスコ コミュニティ
- ネットワークインフラストラクチャ
- [TKB] ネットワークインフラ ドキュメント
- DNAC: SFTP Compatibility Mode の無効化
オプション
- RSS フィードを購読する
- 新着としてマーク
- 既読としてマーク
- ブックマーク
- 購読
- 印刷用ページ
- 不適切なコンテンツを報告
589
閲覧回数
0
いいね!
0
コメント
オプション
- RSS フィードを購読する
- 新着としてマーク
- 既読としてマーク
- ブックマーク
- 購読
- 印刷用ページ
- 不適切なコンテンツを報告
2022-04-27 10:06 PM
はじめに
Cisco DNA Center の SFTP サーバ機能 (Kubernetes Service として実装) は古い AireOS Wireless LAN Controller との互換性確保のために、デフォルトでは CBC モードなど現在では脆弱とされるアルゴリズムをサポートする Compatibility Mode で稼働しています。
WLC として Catalyst 9800 をご使用の場合は SFTP Compatibility Mode を無効にすることをお勧めします。
古い AireOS WLC をご使用の場合も Compatibility Mode を無効とし、SWIM の使用や NACert (Network Assurance Certificate) のダウンロード時のみ一時的に Compatibility Mode を有効にするという運用をすることができます。
DNA Center 1.x での SFTP サーバ設定メニューは System Settings > Settings > SFTP でしたが、2.x では System > Settings > Device Settings > Image Distribution Servers に変更され、気が付きにくいため見落とされている可能性がありますのでご注意ください。
デフォルト状態の確認
DNA Center の tcp/22 に nmap で SSH アクセスすると CBC モードや hmac-sha1 が有効であることを確認できます。
% nmap -p 22 --script ssh2-enum-algos <DNA Center IP> Starting Nmap 7.92 ( https://nmap.org ) at 2022-04-27 20:47 JST Nmap scan report for <DNA Center IP> Host is up (0.023s latency). PORT STATE SERVICE 22/tcp open ssh | ssh2-enum-algos: | kex_algorithms: (12) | ecdh-sha2-nistp521 | ecdh-sha2-nistp384 | ecdh-sha2-nistp256 | diffie-hellman-group-exchange-sha256 | diffie-hellman-group-exchange-sha1 | diffie-hellman-group18-sha512 | diffie-hellman-group17-sha512 | diffie-hellman-group16-sha512 | diffie-hellman-group15-sha512 | diffie-hellman-group14-sha256 | diffie-hellman-group14-sha1 | diffie-hellman-group1-sha1 | server_host_key_algorithms: (3) | ssh-rsa | ssh-dss | ecdsa-sha2-nistp256 | encryption_algorithms: (6) | aes128-ctr | aes192-ctr | aes256-ctr | aes128-cbc | aes192-cbc | aes256-cbc | mac_algorithms: (4) | hmac-sha1 | hmac-sha2-256 | hmac-sha2-512 | hmac-sha1-96 | compression_algorithms: (3) | none | zlib |_ zlib@openssh.com Nmap done: 1 IP address (1 host up) scanned in 0.44 seconds
SFTP Compatibility Mode 無効化
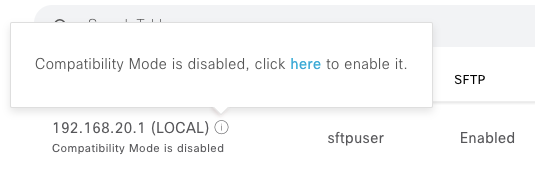
System > Settings > Device Settings > Image Distribution Servers で LOCAL (DNA Center 自身) の Information アイコンをクリックし、次に click here をクリックします。
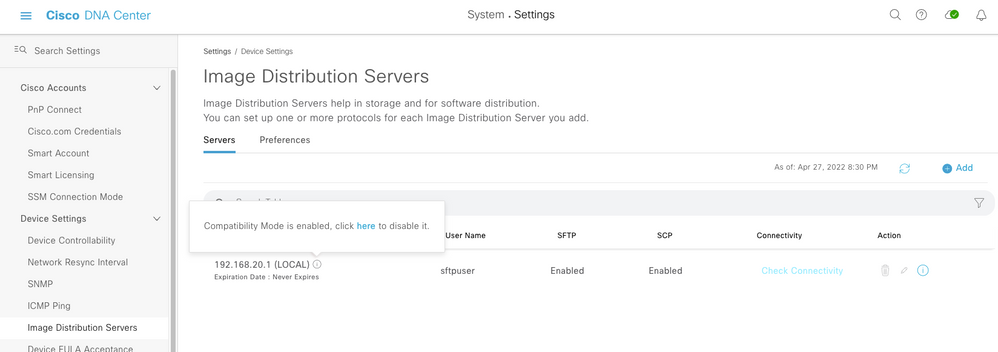
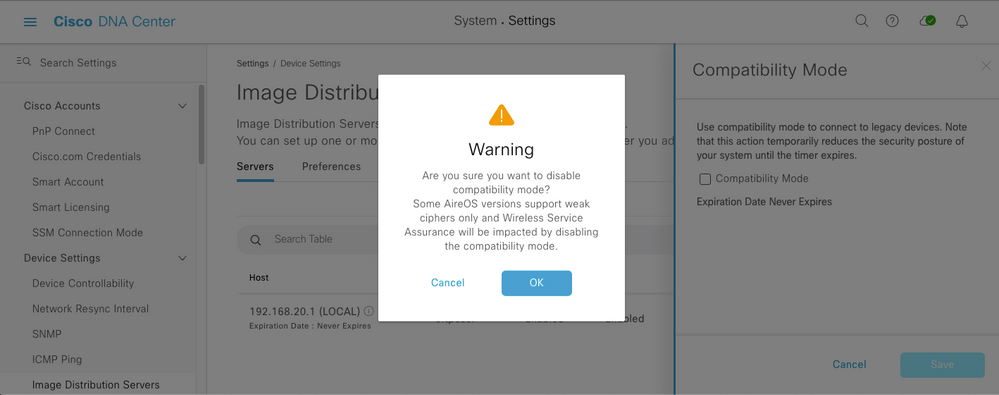
Compatibility Mode のチェックを外すと確認画面が出ます。内容を確認し、問題ないなら OK を押して設定変更を Save します。
設定保存後、Information アイコンをクリックし、disabled となったことを確認します。
再度 nmap でアクセスすると、CBC モードや hmac-sha1 が無効になったことを確認できます。
% nmap -p 22 --script ssh2-enum-algos <DNA Center IP> Starting Nmap 7.92 ( https://nmap.org ) at 2022-04-27 20:53 JST Nmap scan report for <DNA Center IP> Host is up (0.13s latency). PORT STATE SERVICE 22/tcp open ssh | ssh2-enum-algos: | kex_algorithms: (9) | ecdh-sha2-nistp521 | ecdh-sha2-nistp384 | ecdh-sha2-nistp256 | diffie-hellman-group-exchange-sha256 | diffie-hellman-group18-sha512 | diffie-hellman-group17-sha512 | diffie-hellman-group16-sha512 | diffie-hellman-group15-sha512 | diffie-hellman-group14-sha256 | server_host_key_algorithms: (2) | ssh-rsa | ecdsa-sha2-nistp256 | encryption_algorithms: (3) | aes128-ctr | aes192-ctr | aes256-ctr | mac_algorithms: (2) | hmac-sha2-256 | hmac-sha2-512 | compression_algorithms: (3) | none | zlib |_ zlib@openssh.com Nmap done: 1 IP address (1 host up) scanned in 0.99 seconds
一時的な Compatibility Mode への切り戻し
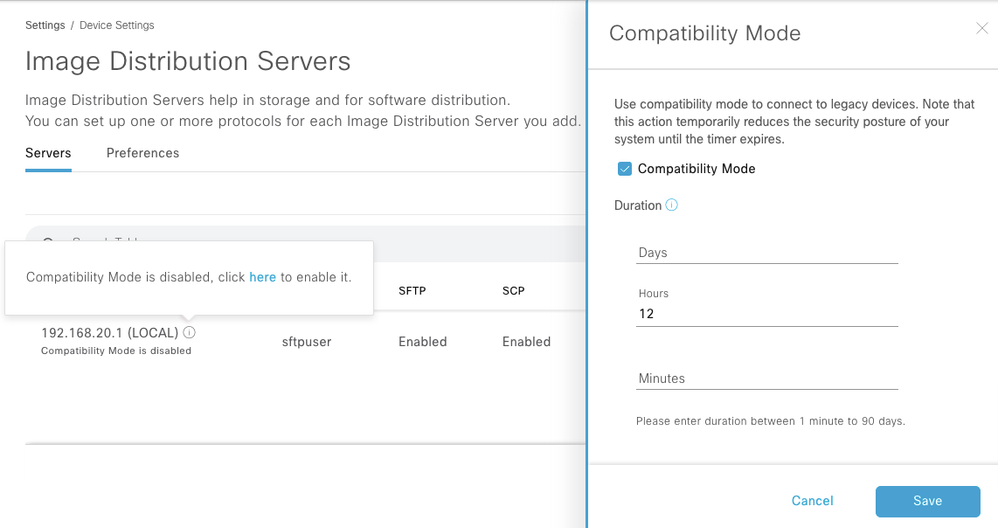
古い AireOS WLC のバージョンアップ等で一時的に Compatibility Mode に戻す場合は click here をクリックして有効期限を設定を行い、Save します。
有効期限は最大 90 日です。一度 Compatibility Mode を無効にすると無期限に有効化することはできません。
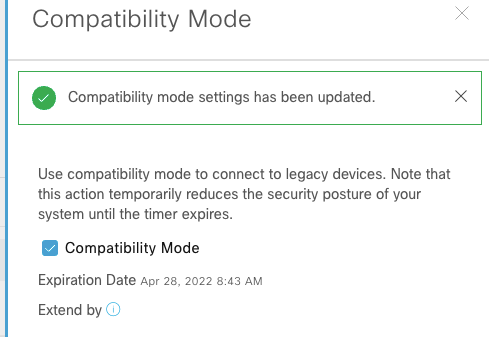
設定を保存すると有効期限が表示されます。
備考
% nmap -p 2222 --script ssh2-enum-algos <DNA Center IP> Starting Nmap 7.92 ( https://nmap.org ) at 2022-04-27 20:55 JST Nmap scan report for <DNA Center IP> Host is up (0.13s latency). PORT STATE SERVICE 2222/tcp open EtherNetIP-1 | ssh2-enum-algos: | kex_algorithms: (6) | curve25519-sha256@libssh.org | ecdh-sha2-nistp256 | ecdh-sha2-nistp384 | ecdh-sha2-nistp521 | diffie-hellman-group14-sha1 | diffie-hellman-group14-sha256 | server_host_key_algorithms: (2) | ecdsa-sha2-nistp256 | ssh-ed25519 | encryption_algorithms: (5) | aes128-gcm@openssh.com | chacha20-poly1305@openssh.com | aes256-gcm@openssh.com | aes128-ctr | aes256-ctr | mac_algorithms: (4) | hmac-sha2-512-etm@openssh.com | hmac-sha2-256-etm@openssh.com | hmac-sha2-512 | hmac-sha2-256 | compression_algorithms: (2) | none |_ zlib@openssh.com Nmap done: 1 IP address (1 host up) scanned in 0.97 seconds $ sudo cat /etc/ssh/sshd_config | grep -e Port -e Cipher -e MACs Port 2222 Ciphers aes128-gcm@openssh.com,chacha20-poly1305@openssh.com,aes256-gcm@openssh.com,aes128-ctr,aes256-ctr MACs hmac-sha2-512-etm@openssh.com,hmac-sha2-256-etm@openssh.com,hmac-sha2-512,hmac-sha2-256
SFTP サーバ (tcp/22) は前述のように NodePort の Kubernets Service である sftp-service-ext としてクライアントに公開され、外部からの通信は tcp/2222 に DNAT されて sftp-service Pod に転送されます。
$ kubectl get svc -n fusion | grep -e PORT -e sftp NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE sftp-service ClusterIP 169.254.55.70 19999/TCP 205d sftp-service-ext NodePort 169.254.57.91 2222:22/TCP 205d $ kubectl get pods -n fusion -o wide | grep -e NAME -e sftp NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES sftp-service-7c7fcb4555-phvc6 1/1 Running 0 21d 169.254.45.115 192.0.2.32 $ sudo iptables-save | grep -e sftp-service-ext -e 169.254.45.115 -A KUBE-NODEPORTS -p tcp -m comment --comment "fusion/sftp-service-ext:default" -m tcp --dport 22 -j KUBE-MARK-MASQ -A KUBE-NODEPORTS -p tcp -m comment --comment "fusion/sftp-service-ext:default" -m tcp --dport 22 -j KUBE-SVC-N5ER6YXVSC55OTBD -A KUBE-SEP-7QHHIP5CQNCIXRPL -s 169.254.45.115/32 -j KUBE-MARK-MASQ -A KUBE-SEP-7QHHIP5CQNCIXRPL -p tcp -m tcp -j DNAT --to-destination 169.254.45.115:19999 -A KUBE-SEP-NJYDUNWX3YVEROBY -s 169.254.45.115/32 -j KUBE-MARK-MASQ -A KUBE-SEP-NJYDUNWX3YVEROBY -p tcp -m tcp -j DNAT --to-destination 169.254.45.115:2222 -A KUBE-SERVICES ! -s 169.254.32.0/20 -d 169.254.57.91/32 -p tcp -m comment --comment "fusion/sftp-service-ext:default cluster IP" -m tcp --dport 2222 -j KUBE-MARK-MASQ -A KUBE-SERVICES -d 169.254.57.91/32 -p tcp -m comment --comment "fusion/sftp-service-ext:default cluster IP" -m tcp --dport 2222 -j KUBE-SVC-N5ER6YXVSC55OTBD $ sudo iptables -t nat -L KUBE-SEP-NJYDUNWX3YVEROBY Chain KUBE-SEP-NJYDUNWX3YVEROBY (1 references) target prot opt source destination KUBE-MARK-MASQ all -- 169-254-45-115.sftp-service.fusion.svc.cluster.local anywhere DNAT tcp -- anywhere anywhere tcp to:169.254.45.115:2222
ラベル:
Getting Started
検索バーにキーワード、フレーズ、または質問を入力し、お探しのものを見つけましょう
シスコ コミュニティをいち早く使いこなしていただけるよう役立つリンクをまとめました。みなさんのジャーニーがより良いものとなるようお手伝いします
Quick Links
下記より関連するコンテンツにアクセスできます
Customers Also Viewed These Support Documents