- Cisco Community
- Technology and Support
- Collaboration
- Unified Communications Infrastructure
- VG224 minimum username length issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
VG224 minimum username length issue
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-30-2018 08:04 AM
Our facility uses a well-entrenched NEC DSX key telephone system. The system supports up to 32 VoIP extensions in addition to a few dozen analog and key handsets. I have successfully deployed 18 VoIP extensions using three SPA8000 units with great success. This was required because part of our campus is reachable only by fiber-optic network. We have no copper connectivity to this structure.
I recently purchased a Cisco VG224 unit, expecting to be able to integrate it into the DSX and move all the analog-over-VoIP extensions into one gateway rather than three SPA8000 units.
However:
The VG224 requires usernames for the dial-peer authentication to be a minimum of 4 characters.
The DSX system uses the extension number as the username. Only 3-digit extensions are allowed.
The DSX does not allow the username to be configured in any way, it is always the 3-digit extension number.
The VG224 does not allow 3-digit usernames.
Is there anything I can do on the VG to work around the 4-character minimum username?
For clarity the command I'm issuing is show below, with the system's response to the command:
VG224-01(config-dial-peer)#authentication username 291 password 291291 realm 192.168.75.24
Username MUST be atleast 4 characters
The VG224 is running IOS 15.1(4)M7 [vg224-i6k9s-mz.151-4.M7.bin].
The NEC DSX-80 system is fully up to date with their latest code, version 3.47 GA.
I'm not calling this a bug, but it certainly is a significant mistake in the code as far as I'm concerned.
Thanks in advance.
- Labels:
-
Other Unified Communications
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-31-2018 05:41 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-31-2018 08:49 AM
Essentially I'm trying to replace three Cisco SPA-8000 units with one VG224. Its function is simply an analog to VoIP gateway. No CME or CUCM in this environment. The DSX is the system the VG will connect to.
NEC calls out the SPA-8000 as a compatible unit and offers a configuration guide on how to make them work together. I assumed I could extrapolate the information and adapt it to the VG224. I think I succeeded, if not for this username length issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-31-2018 01:01 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2018 01:08 PM
Since RFC3261 actually uses a three-character username of “bob” in the relevant sections it seems pretty clear this is an assumption made by a developer within Cisco. If you purchased SMARTnet on the VG224 you could open a TAC case and see if you can get it declared a defect.
The only far-fetched workaround idea I can imagine is a voice class sip-profile that modifies the username in the reINVITE that includes the Proxy-Authentication header. I have never tried this though.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-02-2018 03:07 PM
I was able to provision some base model Cisco IP handsets at one point in time and those worked fine with the 3 character username.
I do not currently have SmartNet on the device, if it's not past the sunset date I may add it just to file the bug/defect.
The DSX documentation shows the config for setting up a Cisco SPA8000, and it is able to send the 3 character username with no issues. It seems your take may be right on, it may be the case that the 4 character limitation is in error. I can provide a link to this config example if that's helpful.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-05-2018 07:08 AM
It appears the sunset date for new service attachment on the VG224 is already past, April 23, 2016.
It's extremely unfortunate that I have essentially no option other than to attempt to return the device to the vendor when the issue seems to be very clearly an error in the device code. I suppose this is a risk taken when purchasing equipment without a service contract. However, even in the case of SmartNet coverage, I highly doubt Cisco would write a new firmware image for this outdated, albeit very expensive, device.
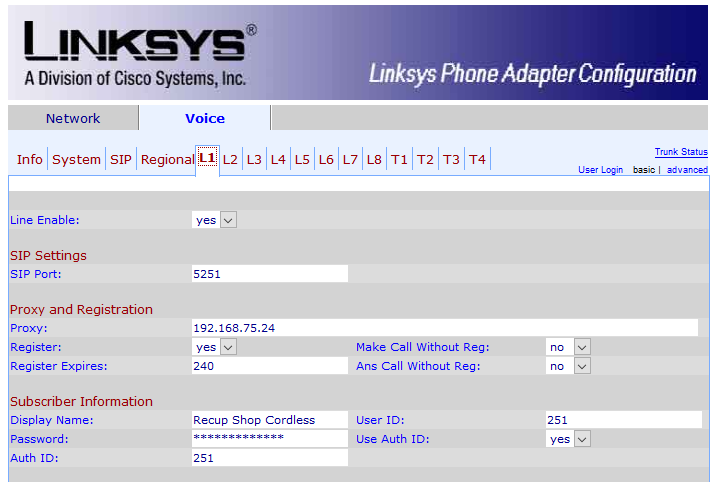
Just a bit of additional information, in the case this may help close the loop or assist somebody else. Here is how the Cisco SPA8000 ATA is configured, per NEC's documentation, to work with my 3rd party key system (NEC DSX-80).
Again, I was able to adapt this information and configured some Cisco 7912 IP handsets and they work very well on the DSX system, using the SIP based firmware on the handset and a simple TFTP server on the LAN for the phones to grab their config files from.
None of this really matters, other than to show clear examples of two other devices (Cisco 7912 handset and Cisco SPA8000 ATA) which happily allow 3-char usernames to be configured for SIP authentication.
SPA8000 example config shown below:
http://www.necdsx.com/docs/sip_ata/sip_ata_installation_notes.html
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide