- Cisco Community
- Technology and Support
- Collaboration
- Unified Communications Infrastructure
- Weak SSL ciphers on Unity 5.0 server during a security scan
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Weak SSL ciphers on Unity 5.0 server during a security scan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-02-2010 11:01 AM - edited 03-19-2019 01:11 AM
Hello,
We received informaition from our security team when they did a scan on our Unity server...."the remote host supports the use of SSL ciphers that offer weak encryption or no encryption at all" I have found some articles on the web (Microsoft) to edit the registry key so that nothing lower than 128 bit encryption is accepted. I am looking for a Cisco paper to agree or disagree with this...can anyone help?
Thank you.
- Labels:
-
UC Applications
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-06-2010 08:02 PM
So, this isn't an uncommon security alert when you have your system scanned. One thing to keep in mind is the placement of your server and who/what it is accessed for. In any case, you're not likely to find a Cisco doc that references this specifically. Instead, if you really want to move forward with making the appropriate registry changes then you'll want to open a TAC case and find out if this is supported or not. In terms of further info on your issue:
There is a McAfee article about making websites more secure. It is here: http://www.codeproject.com/KB/aspnet/MakeWebsiteMcAfeeSecured.aspx
Your alert is referenced as follows:
Vulnerability Name: Weak Supported SSL Ciphers Suites
Description
The remote host supports the use of SSL ciphers that offer either weak encryption or no encryption at all. This vulnerability is valid for all SSL/TLS sessions that are passing sensitive information.
PCI defines strong cryptography, for secret key based systems, as anything above 80 bit encryption.
Solution
The solution to this is very simple but requires registry tweak again. Following are the steps:
- Click Start, click Run, type regedt32 or type regedit, and then click OK.
- In Registry Editor, locate the following registry key:
HKey_Local_Machine\System\CurrentControlSet\Control\SecurityProviders \SCHANNEL\Ciphers
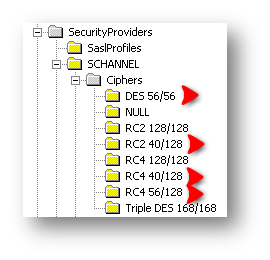
- Under the Cipher key, there are several Ciphers.
- Locate the ciphers which have encryption less than 128 bit.
- Create
DWORDvalues namedEnabledand Value 0 for each of them, just as the previous case. - For convenience, I have marked them with red arrows in the picture above.
- System Restart is NOT required for this.
Now the server is secured.
The above mentioned security issues are the major ones that most of the systems have. However other than this, there may be some easy and minor vulnerabilities like:
- Using robots.txt in the pages. (Generally inserted by Web Marketing team to track user hit).
- Directory Scanner: Common directories are revealed. This can be resolved by URL rewriting and setting “Directory Browsing” off.
Note: For the above vulnerabilities, minor registry tweaks will be necessary. So it is strongly recommended to back up the registry before doing anything. By any chance if something gets messed up, just delete the SCHANNEL key and restart the machine, the key will be auto-generated.
Hailey
Please rate helpful posts!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-22-2011 08:20 PM
Hello,
I am in the same boat, our security team also ran the security scan on Unity connection 7.1(5b)su4 that says..."This host supports the use of SSL Ciphers that offer medium strength encryption, which we currently regards as those with key length 56 bits and less than 112 bits"
I’ll highly appreciate if you can give some pointers of your solution...
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2014 09:58 AM
Same with even Unity 10..
Jeff
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide
