- Cisco Community
- Technology and Support
- Security
- Network Security
- Certificates in Dynamic Access Policy
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Certificates in Dynamic Access Policy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-08-2020 09:31 AM
Hello everyone,
I am trying to devise a solution to block non company computers from connecting to our Anyconnect VPN. I am thinking about using a self-singed certificate using Dynamic Access policy for this purpose. I have installed Host Scan image 4.9, created and self signed a certificate using my Cisco ASA, exported and imported it into a computer "Trusted Root Certification Authorities" location. How should I develop my DAP to be able to block any computer which does not have the aforementioned certificate installed?
Any help is greatly appreciated.
Thanks,
Ramin
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-21-2021 09:56 AM
Anybody having any idea how to get this to work?
I am thinking to work with the registry value that the installed certificate adds to the computer registry if there is no solution to compare the certificate against Certificate option in Dynamic Access Policies but prefer to use the option available.
Any help is appreciated.
Ramin
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-21-2021 10:15 AM
If using certificate authentication the connecting computer would need a certificate issued by the ASA. Certificate distribution should be controlled, so no one without your company laptop should have a certificate that they can install on a non-company laptop.
Generally when using DAP you can identify a corporate asset to check the registry for the domain value.
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Tcpip\Parameters\Domain Value=domain.name (your company domain name). If the computer connected to the VPN is not joined to your AD domain then they will not be able to connect.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-26-2021 03:49 PM
Hello Rob,
In our case, certificate is the perfect solution since not all the computers are necessarily joined to domain and besides in different windows versions, there are different registry paths.
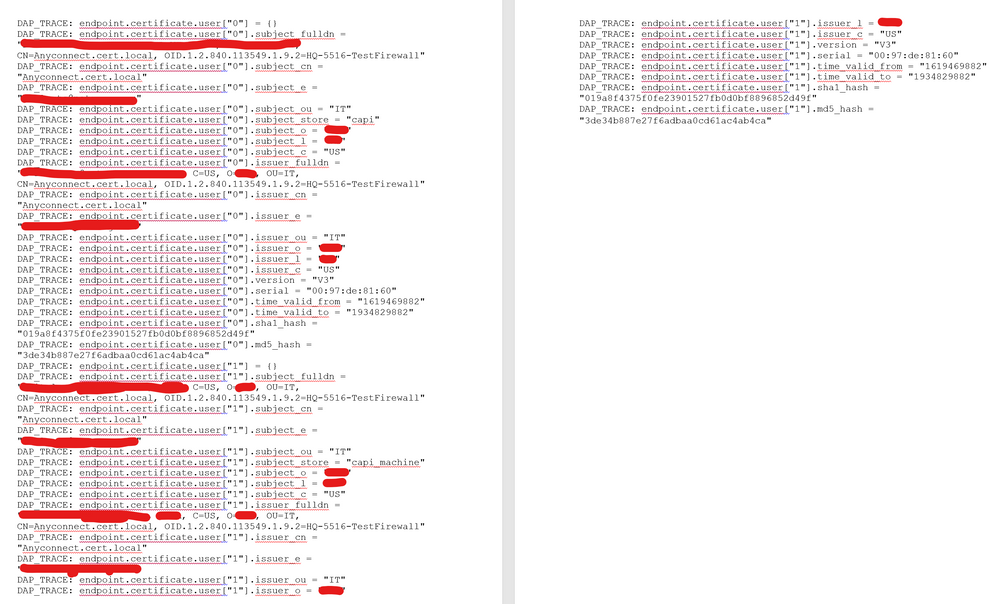
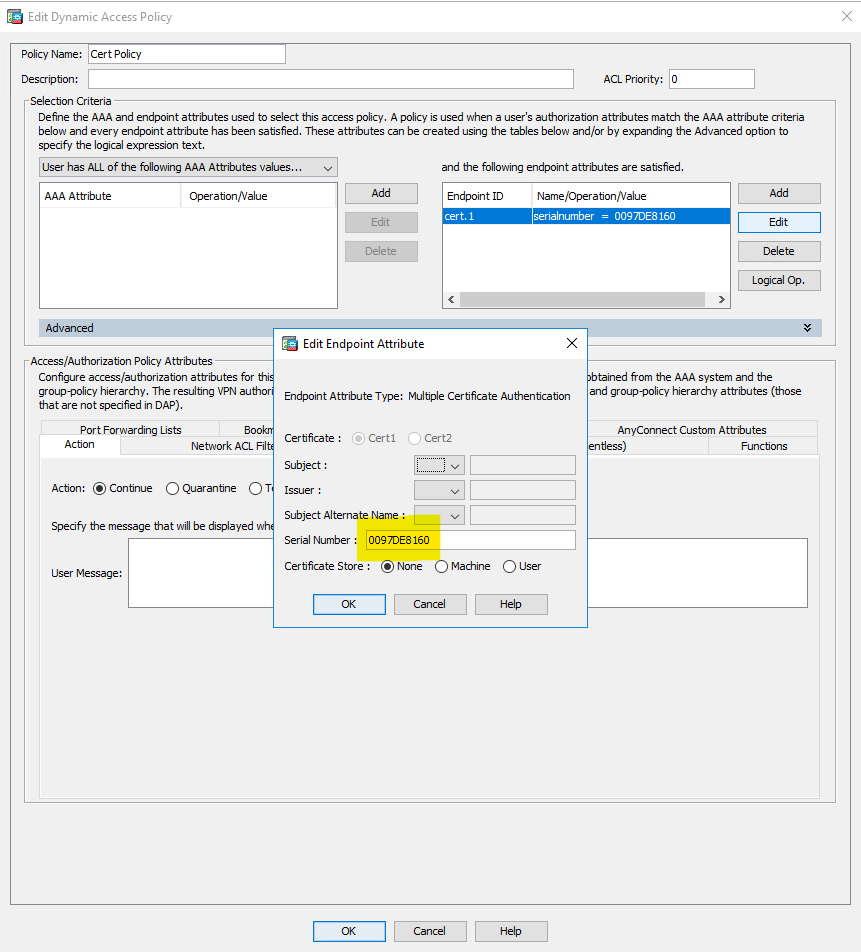
I generated a certificate with a Private Key by ASA and imported it into my computer cert stores (Trusted Root, Trusted Publishers) in both Machine and User stores but unfortunately it did not let me establish VPN. Here is "debug dap trace" output.
Also you can see my DAP configuration below.
Thanks for your help.
Ramin
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide