- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- Does ISE Support My Network Access Device?
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
08-17-2017 05:36 PM - edited 12-19-2023 03:50 PM
Contents
- ISE Supports the RADIUS and TACACS Protocols
- Network Access Device Access Control Capabilities
- What are The Capabilities of My Network Access Devices?
- But I Don't See My Network Device in the Compatibility or Capabilities Guides
- ISE Network Access Device (NAD) Profiles
- Can I use Authentication VLANs?
ISE Supports the RADIUS and TACACS Protocols
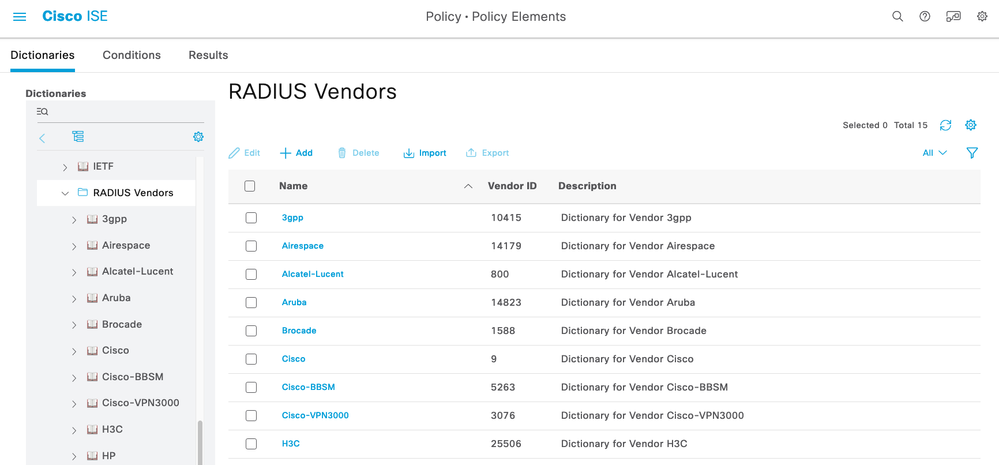
If your network access device can issue access control requests using the standard RADIUS and TACACS protocols then ISE can support it! RADIUS and TACACS protocol support is clearly documented in the ISE Compatibility Guides including the individual RFCs that ISE supports. Some vendors have created RADIUS Vendor Specific Attributes (VSAs) for some of their capabilities - including Cisco - and ISE has the ability to import any additional RADIUS dictionaries that you want. See For download: RADIUS Vendor Dictionaries for 3rd Parties for a long list of VSA dictionaries that you may use with ISE.
Network Access Device Access Control Capabilities
These are modern network access device capabilities and features typically required to implement all of the modern access control scenarios available with the Cisco Identity Services Engine :
| ISE Capability | Network Device Features |
| AAA | 802.1X, MAB, VLAN Assignment, Downloadable ACLs |
| Profiling | RADIUS CoA and Profiling Probes |
| BYOD | RADIUS CoA, URL Redirection + SessionID |
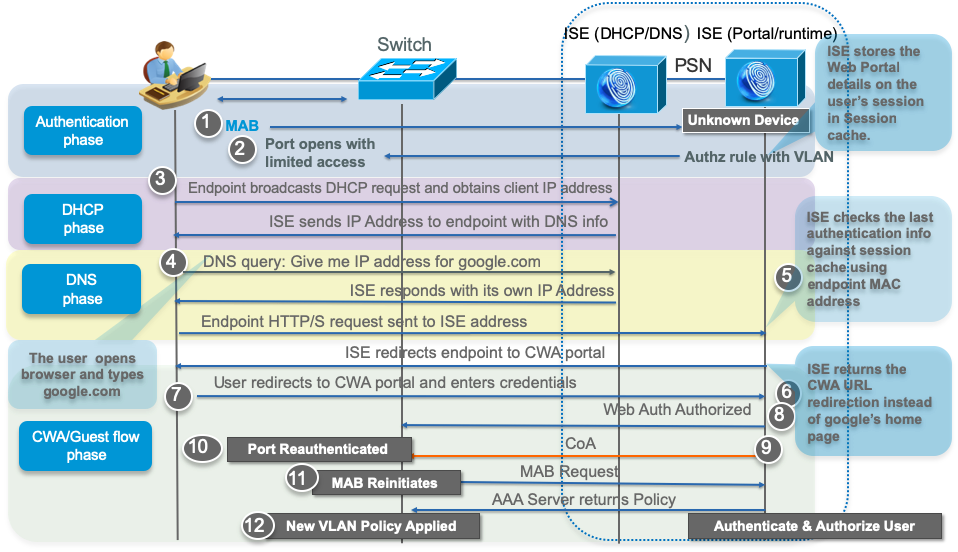
| Guest | RADIUS CoA, URL Redirection + SessionID, Local Web Auth |
| Guest Originating URL | RADIUS CoA, URL Redirection + SessionID, Local Web Auth |
| Posture | RADIUS CoA, URL Redirection + SessionID |
| MDM | RADIUS CoA, URL Redirection + SessionID |
| TrustSec | SGT Classification |
When people ask "Does ISE support my network device?", often what they are really asking "Can ISE give me all of lastest, modern, dynamic access control capabilities and segmentation even with this old, inexpensive switch"? The answer is No. However for these older and less capable switches, ISE offers features like SNMP CoA and Authentication VLAN to provide some rudimentary capabilities for basic Guest, BYOD and Posture flows on older or less capable network access devices.
What are The Capabilities of My Network Access Devices?
We have conveniently documented the Cisco network access device hardware and software capabilities in Network Access Control Capabilities of Network Devices. The absence of a product family, model or software version simply means we have not (yet) validated it. If you do not see a particular hardware family or version listed and would like to suggest it for validation, please submit feedback on Network Access Control Capabilities of Network Devices.
For all others, you will need to research this with the network device vendors' websites, product documentation, forums, etc. Sometimes you may just have to play in your lab to find out what works and what doesn't and create a Network Device Profile for the different combinations of capabilities.
But I Don't See My Network Device in the Compatibility or Capabilities Guides
If your network device supports RADIUS and/or TACACS+ then ISE supports it! The ISE Compatibility Guides clearly states RADIUS and TACACS protocol support :
Cisco ISE supports interoperability with any Cisco or non-Cisco RADIUS client network access device (NAD) that implements common RADIUS behavior (similar to Cisco IOS 12.x) for standards-based authentication.
There are many reasons why both Cisco and non-Cisco devices may not be listed in our guides :
- Our QA team cannot afford to validate every single hardware and software combination with every ISE release
- New hardware platforms must be acquired and tested which usually occurs within 6-9 months after the hardware release
- Every model of a hardware family are not validated - we pick one model and use that to represent the hardware family
- Every software release is not validated - we pick one released platform software version recommended by the platform team a few months before the actual ISE release for QA validation planning
- Older ISE releases will not be validated with newer network device software but still should work per protocol standards.
We always recommend trying your network access device hardware and software in your lab with ISE before deploying to production so you are confident that is will behave as expected. You never know when there may be bugs in your endpoints' software, the network access devices' software, or ISE.
ISE Network Access Device (NAD) Profiles
If you have :
- non-Cisco hardware
- inexpensive, low-end network device hardware
- older network device hardware
- older network device software
then you can use our ISE Third-Party NAD Profiles and Configs or create your own custom NAD profile. Using a NAD profile, you can completely customize how ISE communicates with your network device whether it is on custom ports for RADIUS CoA or if you need to use Authentication VLANs instead of URL Redirection.
Can I use Authentication VLANs?
Yes, but we recommend you upgrade your hardware to modern security capabilities with RADIUS. For more information, see Third-Party Network Device Support in Cisco ISE in the ISE Administrator Guides.
Problems with Using Authentication VLANs
- you must provide temporary access before authentication
- you cannot control multiple devices per port
- traffic filtering is very crude with L2 VLANs - no L3/4 IP/protocol/port control except with a VACL or VRF
- no East/West segmentation within a VLAN means malware is easily spread to other endpoints within VLANs, whether trusted or untrusted
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: