- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- Router Security: DNS-layer Security - Step by Step Configuration
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
06-13-2018 12:38 PM - edited 06-05-2022 01:03 PM
- Goal
- Documentation
- Image Download Links
- Supported Platforms
- Limitations/Restrictions
- Topology
- How DNS-layer security works
- Step by Step Configuration
- Import CA certificate to the trust pool
- Get the token to register the device
- Configure local domains (optional)
- Configure the token
- Enable Umbrella Out
- Enable Umbrella in
- Verification
- Final Relevant Config
- Show commands
- Debugs
- Troubleshooting
Goal
To configure DNS-layer security on routers that run IOS-XE such that it redirects all the DNS traffic except local domain traffic to the Umbrella Cloud for resolution.
Documentation
Umbrella DNS-Layer Security Documentation: https://docs.umbrella.com/hardware-integrations/docs/integration-for-isr-4k-and-isr-1100-security-configuration-guide
Umbrella DNS-Layer Security Troubleshooting guide: https://support.umbrella.com/hc/en-us/articles/115005154526-Cisco-Umbrella-ISR4k-integration-troubleshooting-guide-
Cisco Documentation: http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_data_utd/configuration/xe-16/sec-data-umbrella-branch-xe-16-book.html
Image Download Links
Catalyst 8500 - https://software.cisco.com/download/home/286324574/type
Catalyst 8300 - https://software.cisco.com/download/home/286324476/type
Catalyst 8200 - https://software.cisco.com/download/home/286324472/type
Catalyst 8000V - https://software.cisco.com/download/home/286327102/type
ISR - https://software.cisco.com/download/home/284389362/type
CSR - https://software.cisco.com/download/home/284364978/type
ISRv - https://software.cisco.com/download/home/286308693/type
Supported Platforms
All branch and aggregation edge routing platforms running IOS-XE 16.3 and above.
Limitations/Restrictions
DNS-Layer security will not have any effect on the following if configured. Meaning traffic will not be filtered based on Umbrella policies configured on the portal.
- Loading a page using IP address
- Using a proxy on the browser
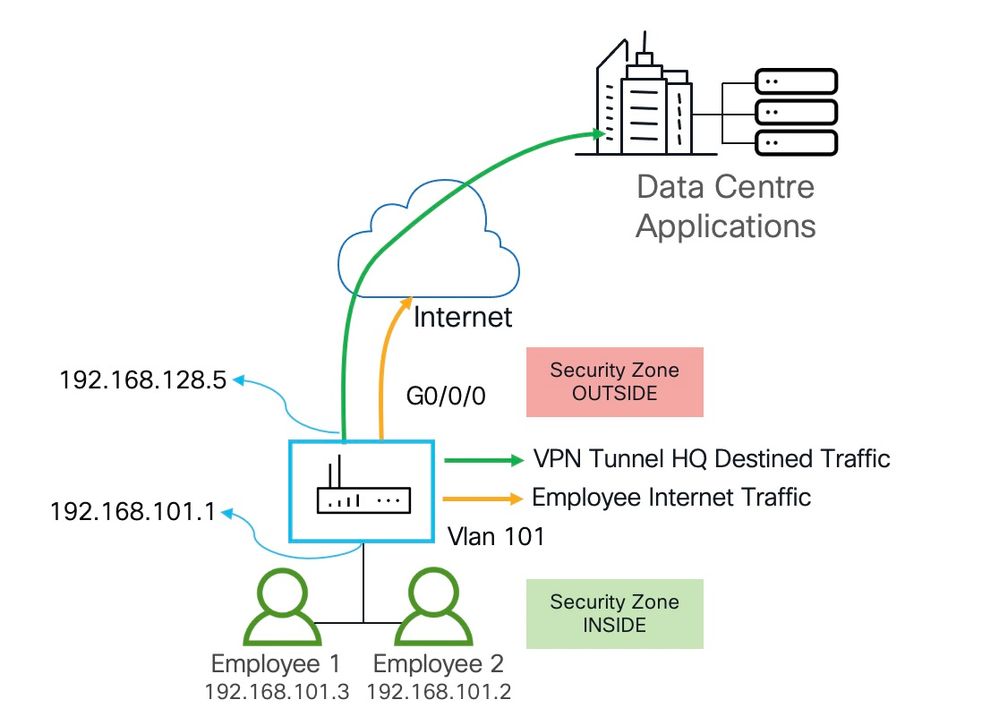
Topology
How DNS-layer security works
- All DNS traffic is intercepted by the ISR; if it is a local domain query, then the DNS packet will not be changed and forwarded to Umbrella DNS resolvers, otherwise the ISR will add ENDS records to the query and forward it to Umbrella cloud.
- Based on the policies configured on the Umbrella portal if the HTTP client is trying to browse to a page that is blocked or malicious, then Umbrella sends their blocked page IP address as DNS response.
- HTTP client will send HTTP request to Umbrella cloud IP address and Umbrella provides the reason for blocking the content in the HTTP response.
Step by Step Configuration
Import CA certificate to the trust pool
Communication for device registration to the Umbrella server is via HTTPs. This requires Umbrella's root certificate to be installed on the router.
crypto pki trustpool import url http://www.cisco.com/security/pki/trs/ios.p7b
If you see any errors like this below, then the best thing to do is to download the manually download "ios.p7b" cert bundle via curl and copy to the Router's flash > Clear existing certificate from pool > Import "ios.p7b" cert bundle from flash:
% Error: failed to open file. % No certificates imported from http://www.cisco.com/security/pki/trs/ios.p7b.
Here are the steps to cleanup the trust pool and import the trust bundle ios.p7b.
1. Go to http://www.cisco.com/security/pki/trs/ios.p7b and download the ios.p7b
2. Tftp, FTP or SCP the file to the router's flash
3. Clean the trustpool with the command provided below
4. And import the trust bundle to the trust pool
crypto pki trustpool clean crypto pki trustpool import url flash:ios.p7b Reading file from bootflash:ios.p7b % PEM files import succeeded.
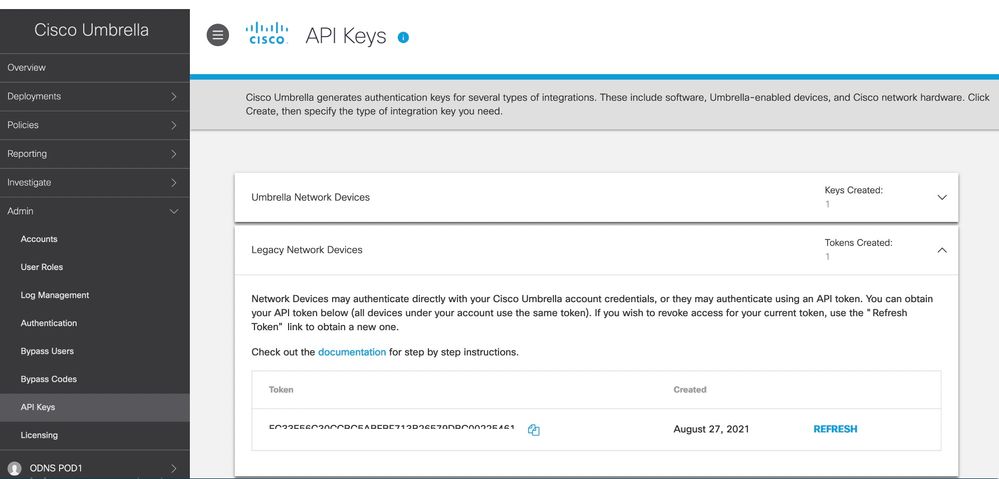
Get the token to register the device
Log into the Umbrella portal https://login.umbrella.com/
Navigate on the left to Admin >> API Keys >> Legacy Network Devices and copy the Token. We need this to configure the router for Umbrella.
Configure local domains (optional)
DNS queries destined to local domain will remain untouched and will not be redirected to OpenDNS cloud.
parameter-map type regex dns_bypass pattern www.cisco.com pattern .*eisg.cisco.*
Configure the token
Configure the token that you got from the OpenDNS portal and add the optional local domain configured in the above step.
parameter-map type umbrella global
token EC33E56C30CCBC5ABEBB26579DBC00225461
local-domain dns_bypass
dnscrypt
udp-timeout 5
Enable Umbrella Out
interface GigabitEthernet0/0/0
ip address dhcp
ip nat outside
umbrella out
negotiation auto
end
Enable Umbrella in
Enable Umbrella in on all the interfaces that are interested in redirecting DNS traffic to the Umbrella cloud. Each interface should include a "tag" so you can configure policies based on the "tag" on the Umbrella portal. In this case we have used the "tag" as "inside-network"
interface Vlan101
description WIRED
ip address 192.168.101.1 255.255.255.0
ip nat inside
umbrella in Wired-clients
end
Verification
Once all the configuration is in. You should see that the the router received the device-id for the inside networks from umbrella.
kusankar-1121X#show umbrella deviceid Device registration details Interface Name Tag Status Device-id Vlan101 Wired-clients 200 SUCCESS 010a94405f77eb93
Final Relevant Config
parameter-map type regex dns_bypass pattern www.cisco.com pattern .*eisg.cisco.*
parameter-map type umbrella global token EC33E56C30CCBC5ABEBB26579DBC00225461 local-domain dns_bypass dnscrypt udp-timeout 5
interface Vlan101 description WIRED ip address 192.168.101.1 255.255.255.0 ip nat inside umbrella in Wired-clients interface GigabitEthernet0/0/0 description Connected to Meraki Z3 ip address dhcp ip nat outside umbrella out negotiation auto
Show commands
show umbrella dnscrypt show umbrella config show umbrella deviceid
Debugs
debug umbrella device-registration
The below debugs clearly indicate there is a problem with the certificate.
*Apr 6 02:58:28.938: OPENDNS-DEV-REG:opendns_dev_reg_process_start
*Apr 6 02:58:28.938: OPENDNS-DEV-REG:Found channel
*Apr 6 02:58:28.938: OPENDNS-DEV-REG:dev reg to be sent for interface :GigabitEthernet0/0/1 status :REQ QUEUED
*Apr 6 02:58:28.938: OPENDNS-DEV-REG: Dev reg interface details interface name: GigabitEthernet0/0/1 tag: inside-network, status :1
*Apr 6 02:58:28.938: OPENDNS-DEV-REG:Found channel
*Apr 6 02:58:28.940: OPENDNS-DEV-REG:DNS match found for api.opendns.com is 67.215.92.210
*Apr 6 02:58:28.940: OPENDNS-DEV-REG:channel connect : resolved OOB server ip:67.215.92.210
*Apr 6 02:58:28.940: OPENDNS-DEV-REG:channel: IDB name GigabitEthernet0/0/1:
*Apr 6 02:58:28.940: OPENDNS-DEV-REG:channel: Connecting to 67.215.92.210(443) from src 0.0.0.0: socket 6: status -1: errno 265 channel status0
*Apr 6 02:58:28.940: OPENDNS-DEV-REG:channel: Error in socket_connect: status -1: sock_fd 6
*Apr 6 02:58:28.940: OPENDNS-DEV-REG:Cleaning up the channel
*Apr 6 02:58:28.940: OPENDNS-DEV-REG: Could not connect device reg channel
*Apr 6 02:58:28.940: OPENDNS-DEV-REG:cleanup and reconnect
*Apr 6 02:58:28.940: OPENDNS-DEV-REG:Cleaning up the channel
Please import the certificate and make sure the cert the is still there. If not import it to trustpool again.
ISR-4321-OpenDNS#sh cry pki trustpool
ISR-4321-OpenDNS#sh cry pki trustpool
CA Certificate
Status: Available
Certificate Serial Number (hex): 01FDA3EB6ECA75C888438B724BCFBC91
Certificate Usage: Signature
Issuer:
cn=DigiCert Global Root CA
o=DigiCert Inc
c=US
Subject:
cn=DigiCert SHA2 Secure Server CA
o=DigiCert Inc
c=US
CRL Distribution Points:
http://crl3.digicert.com/DigiCertGlobalRootCA.crl
http://crl4.digicert.com/DigiCertGlobalRootCA.crl
Validity Date:
start date: 12:00:00 UTC Mar 8 2013
end date: 12:00:00 UTC Mar 8 2023
Associated Trustpoints: Trustpool
Trustpool: Downloaded
debug opendns config
debug opendns split-dns
Troubleshooting
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
New Stuff to me, Thanks
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Kureli,
Really useful post. Can i check what was the DNS server given to the client 10.10.20.2 via dhcp was it pointing to the gateway or some internal DNS server or umbrella.
Thanks
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
It looks like the C8500 image link is pointing to an 8500L image, just checking is it typo?
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: