18045
查看次数
20
有帮助
20
回复
20 条回复20
本帖最后由 ts1110 于 2019-1-25 17:37 编辑
LZ问题也是经常会碰到的,在路由器上要解决这个问题,一般有两种做法
第一种:使用NVI接口做;
第二种:纯粹的NAT+PBR实现;
对于第一种解决方案,需要路由器支持,配置相对来说简单一些,思科网关上就有很多配置范例,LZ可以去查一下!
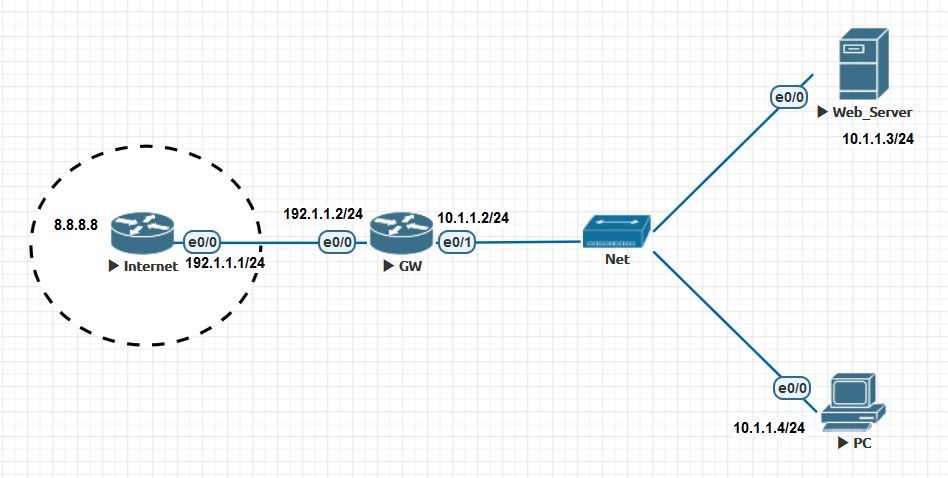
第二种配置要麻烦一下,我这里给你还原了一下环境,LZ可以参考一下,拓扑图如下:
最终需求:
注:我这里拿Telnet来代替HTTP做测试!
网关配置如下:
测试现象:
PC访问Internet:
Internet上的设备通过NAT映射,可以访问到内部的Web服务器:
内部PC可以通过网关的公网地址访问到内部的Web服务器:
LZ问题也是经常会碰到的,在路由器上要解决这个问题,一般有两种做法
第一种:使用NVI接口做;
第二种:纯粹的NAT+PBR实现;
对于第一种解决方案,需要路由器支持,配置相对来说简单一些,思科网关上就有很多配置范例,LZ可以去查一下!
第二种配置要麻烦一下,我这里给你还原了一下环境,LZ可以参考一下,拓扑图如下:
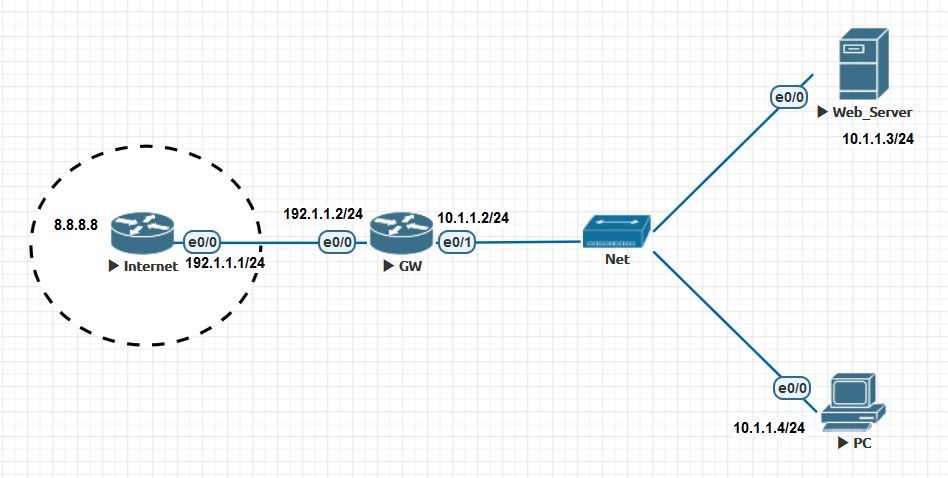
最终需求:
- PC能访问Internet;
- Internet上的设备通过NAT映射,可以访问到内部的Web服务器;
- 内部PC可以通过网关的公网地址访问到内部的Web服务器;
注:我这里拿Telnet来代替HTTP做测试!
网关配置如下:
GW#sh running-config
Building configuration...
Current configuration : 1858 bytes
!
! Last configuration change at 11:08:17 EET Fri Jan 25 2019
!
version 15.7
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname GW
!
boot-start-marker
boot-end-marker
!
!
!
no aaa new-model
!
!
!
clock timezone EET 2 0
mmi polling-interval 60
no mmi auto-configure
no mmi pvc
mmi snmp-timeout 180
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
no ip domain lookup
ip cef
no ipv6 cef
!
multilink bundle-name authenticated
!
!
!
!
!
!
!
!
!
!
redundancy
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
interface Loopback0
ip address 2.2.2.2 255.255.255.255
ip nat inside
ip virtual-reassembly in
!
interface Ethernet0/0
ip address 192.1.1.2 255.255.255.0
ip nat outside
ip virtual-reassembly in
duplex auto
!
interface Ethernet0/1
ip address 10.1.1.2 255.255.255.0
ip nat outside
ip virtual-reassembly in
ip policy route-map LOCAL
duplex auto
!
interface Ethernet0/2
no ip address
shutdown
duplex auto
!
interface Ethernet0/3
no ip address
shutdown
duplex auto
!
ip forward-protocol nd
!
!
no ip http server
no ip http secure-server
ip nat inside source list INTERNET interface Ethernet0/0 overload
ip nat inside source list LOCAL interface Loopback0 overload
ip nat inside source static tcp 10.1.1.3 23 192.1.1.2 23 extendable
ip route 0.0.0.0 0.0.0.0 192.1.1.1
!
ip access-list extended INTERNET
remark WORK FOR LOCAL TO INTERNET
deny ip 10.0.0.0 0.255.255.255 10.0.0.0 0.255.255.255
permit ip 10.1.1.0 0.0.0.255 any
ip access-list extended LOCAL
remark WORK FOR LOCAL TO PUBLIC TO LOCAL
permit ip host 10.1.1.4 host 10.1.1.3
!
ipv6 ioam timestamp
!
route-map LOCAL permit 10
set interface Loopback0
!
!
!
control-plane
!
!
!
!
!
!
!
!
line con 0
exec-timeout 0 0
logging synchronous
line aux 0
line vty 0 4
exec-timeout 0 0
privilege level 15
no login
transport input none
!
!
end
测试现象:
PC访问Internet:
PC#ping 8.8.8.8
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 8.8.8.8, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 1/1/1 ms
Internet上的设备通过NAT映射,可以访问到内部的Web服务器:
Internet#telnet 192.1.1.2
Trying 192.1.1.2 ... Open
Web_Server#
Web_Server#
内部PC可以通过网关的公网地址访问到内部的Web服务器:
PC#telnet 192.1.1.2
Trying 192.1.1.2 ... Open
Web_Server#
Web_Server#
ts1110 发表于 2019-1-25 17:26
LZ问题也是经常会碰到的,在路由器上要解决这个问题,一般有两种做法
第一种:使用NVI接口做;
e0/0 和 e0/1 都是 ip nat outside ?
loopback 0 是 ip nat inside ?
!
route-map LOCAL permit 10
set interface Loopback0
!
interface Ethernet0/1
ip policy route-map LOCAL
!
大概意思能明白,能详细解释一下原理吗?
ts1110 发表于 2019-1-25 17:26
LZ问题也是经常会碰到的,在路由器上要解决这个问题,一般有两种做法
第一种:使用NVI接口做;
ip nat inside source list LOCAL interface Loopback0 overload
!
ip access-list extended LOCAL
remark WORK FOR LOCAL TO PUBLIC TO LOCAL
permit ip host 10.1.1.4 host 10.1.1.3
!
ip access-list extended INTERNET
remark WORK FOR LOCAL TO INTERNET
deny ip 10.0.0.0 0.255.255.255 10.0.0.0 0.255.255.255
permit ip 10.1.1.0 0.0.0.255 any
!
发现不做红色这些也可以实现,但不是转换为2.2.2.2,而是外网接口地址



