- Cisco Community
- Technology and Support
- Security
- Endpoint Security
- Source IP Address in AMP Device Trajectory to Assist Threat Hunting
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Source IP Address in AMP Device Trajectory to Assist Threat Hunting
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-18-2019 02:47 PM - edited 02-20-2020 09:11 PM
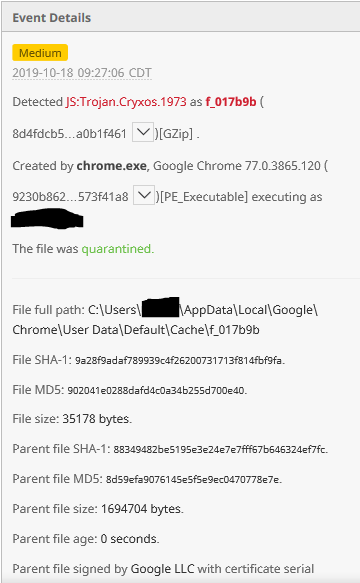
Today I had 6 endpoints within 3 hours all quarantine the following file: 8d4fdcb52b32afbcef4450ca88668def9b245a6f7ab2aa26ec3a4324a0b1f461
When I look what was happening with each endpoint in AMP's Device Trajectory I see this:
The event only indicates that the file was "created by chrome.exe". Why doesn't it indicate the IP address that is the source of the malicious file so we can understand how we are being targeted by malware? That would be valuable.
Even when we open a Threat Response investigation enriched with all of Cisco's threat intelligence data and our Sourcefire and Umbrella environment data we get no additional insight as to the origin of the threat other than which 6 endpoints quarantined the file.
How are we supposed to find out the source of exposure to the malicious file if the only information provided is Chrome. That's basically saying "something on the Internet".
- Labels:
-
AMP for Endpoints
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-18-2019 02:56 PM
That's where all of their stuff gets tied together...
Go to Visibility.amp.cisco.com to get started.
Its free...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-20-2019 02:39 AM
Hello @A.N.Jensen,
the one and only answer for you is not really possible.
- Insights into the AMP connector policy would be interesting. To see if there is any setting which may have an impact on the data shown in DT. Note, an exclusion can have an impact on DT.
- DT should show at least TCP connections for your chrome. AMP does not monitor any TCP connection of any process. This would be too much information and would generated an unmanageable overhead. There are other approaches/products/sensor/intelligences available to cover much more data.
- Without having a complete look into your data shown in DT it is nearly impossible to give you the appropriate answer you are looking for. Maybe there are command line arguments from completely other processes which may trigger chrome.exe.
- DT helps you to understand an Attack/Malicious Szenario. It shows information which helps you getting more insights. This insights can help you to get better insights what is going on. Like every tool, it is important to "understand" the outcome in DT to generate understanding.
- It would also be interesting if AMP generated IOCs for the endpoints.
- Optional: If our e-mail solution is available, it could be integrated into Threat Response, which would give you insights if the file arrived by e-mail.
- You may also take a look in DT, if your e-mail client stored a file in the disk.
- If the enduser has directly opened some attachment, it would be shown in the command line of the appropriate process in DT.
- It would also be interesting to see if the endpoints are showing new unknown files, if there is other activity and so on. Also, take a look if there are any Retrospective alerts in AMP console.
As you see, there are many aspects we cannot directly figure out from a single Screenshot. So it will make sense opening a TAC Case to go through the Event and Monitoring Data in your environment.
Greetings,
Thorsten
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-12-2019 12:47 PM
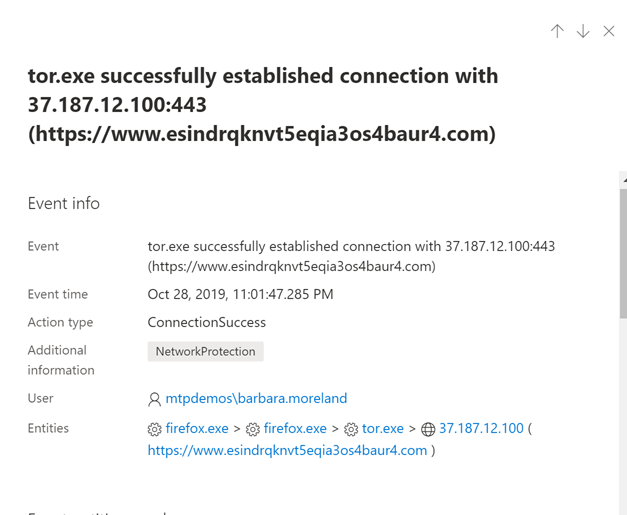
This is the type of data I can see in a demo of Microsoft ATP, this is what I would like to see in AMP events or device trajectory.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide