- Cisco Community
- Technology and Support
- Online Tools and Resources
- Cisco Bug Discussions
- Re: CSCvf96814 - Key Reinstallation attacks against WPA protocol
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-17-2017 01:05 AM - edited 03-20-2019 09:37 PM
Hello.
Have you an idea of when an security update for WAP371 will be available?
Thanks.
Solved! Go to Solution.
- Labels:
-
Cisco Bugs
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-17-2017 01:11 AM - edited 10-20-2017 04:59 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-17-2017 01:11 AM - edited 10-20-2017 04:59 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2017 12:07 PM
The "answer" is not helpful in this case. Still waiting for patch of WAP371
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2017 05:22 AM
Where can i find the fix?
or there is no fix yet?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-23-2017 01:20 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-23-2017 01:42 AM
Hello,
How about security update for WAP371 firmware? Any idea when it will be available?
These AP's work without WLC.
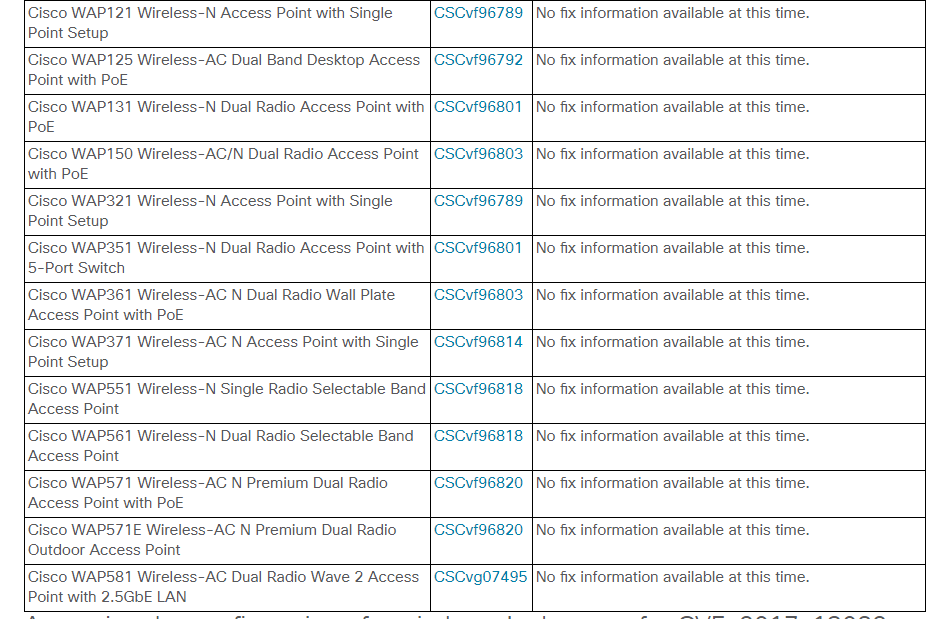
Last firmware release for these is from February 2017 and Cisco lists these as vulnerable:
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20171016-wpa
Best regards,
Maciek
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-27-2017 01:58 AM
I fully understand that rolling out updates for access points with WLC gets priority. But it would be great to get some advice on these vulnerabilities in the WAP371 firmware. Can you reduce the risk by temporary disable certain functions until a fix is available? What should be disabled:
enterprise security with radius authentication?
pre-authentication?
WDS bridge?
Workgroup bridge?
Single point setup?
others?
regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-27-2017 12:44 PM
It would be greatly appreciated if Cisco, prior to releasing new firmware for the 371 ap, could post measures by means of settings change to mitigate vulnerability changes. Best would be to have the firmware the soonest though.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-27-2017 04:24 PM - edited 10-27-2017 04:26 PM
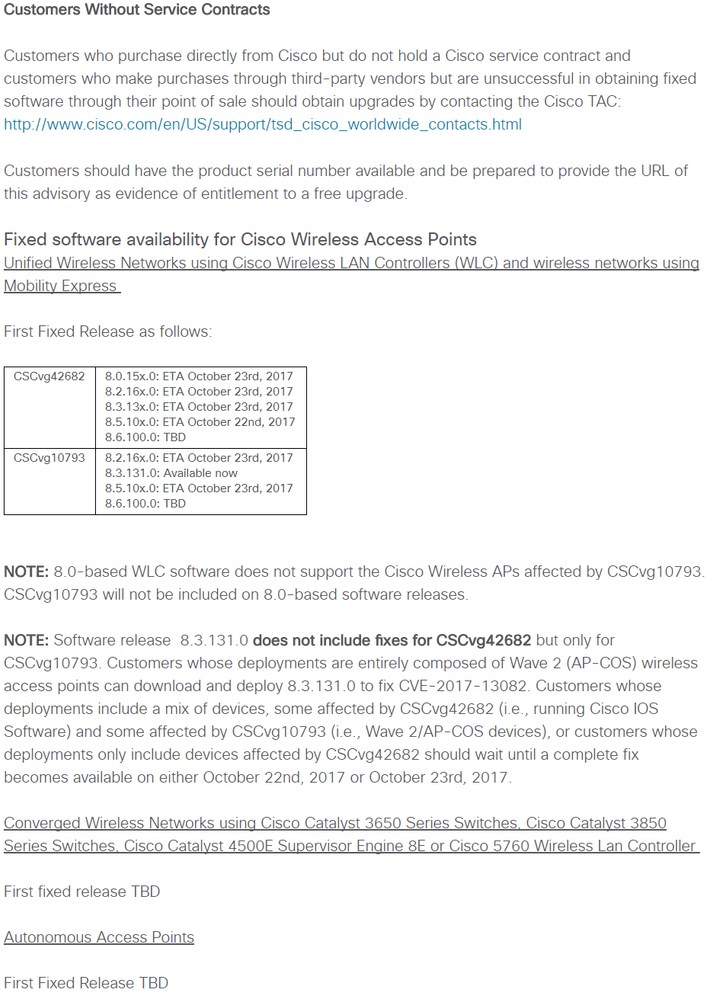
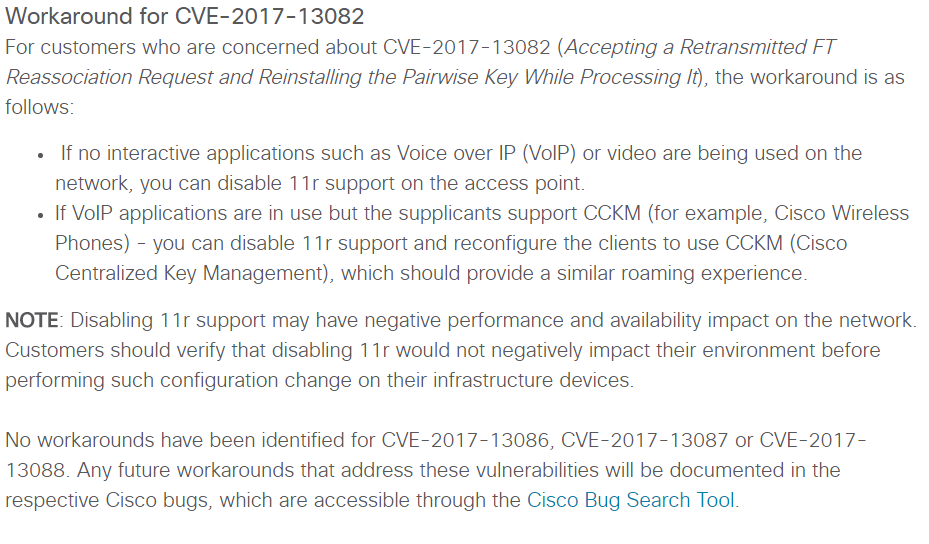
KRACK exploit involves up to ten (10) vulnerabilities. Patching the client will fix 9 out of 10 vulnerabilities (except CVE-2017-13082) because those are client-facing vulnerabilities.
(This means that even if the APs are patched for CVE-2017-13082, but if the clients aren't patched then they could be vulnerable to any of the nine attack vectors.)
For CVE-2017-13082, if your APs support 802.11r (aka Fast Transition or FR), then the fix is to disable this feature. If APs don't support 802.11r, then it's all fine.
WARNING: Please understand what 802.11r can/can't do to the wireless network before undertaking the workaround.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-17-2017 01:50 AM
Hello All,
Month after publicly announcing the vulnerability, two months from when CISCO was notified about it, there is still no promised fix for WAP371 access points...
That is very damaging to the brand and I will think twice before purchasing or recommending CISCO Small Business line products to clients.
If we have to replace hardware to fix the vulnerability, we will also have to go for a different brand this time. Pitty, as WAP3xx line was very affordable way for small businesses to get robust and scalable wireless network...
Also, this thread was marked as answered, although there is still no answer to the original question.
Very disappointing...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-10-2017 08:39 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-14-2017 12:58 PM
This is unacceptable and embarrassing. When will the fix be released? This isn't "solved"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-20-2017 07:28 AM
Guys,
KRAK finally patched on WAP 3XX access points:
https://bst.cloudapps.cisco.com/bugsearch/bug/CSCvf96814
Best regards,
Maciek
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide