- Cisco Community
- Technology and Support
- DevNet
- General DevNet Topics
- DevNet General Discussions
- Re: IOSXE RestAPI auth failing
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
IOSXE RestAPI auth failing
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-09-2018 01:53 AM - edited 03-01-2019 02:59 AM
Hello Team,
CSR1k 16.9.1.
I have enabled rest:
aaa authentication login HTTP local username rest privilege 15 password 0 Krakow123 ip http server ip http authentication aaa login-authentication HTTP ip http secure-server restconf
(i have also tested ip http authentication local or without that command)
Then my curls results are the following:
$ curl -v -X POST https://192.168.1.116/api/v1/auth/token-services -H "Accept:application/json" -u "rest:Krakow123" -d "" --insecure ....... HTTP/1.1 411 Length Required
Why ?
(i've set content-length to 0 in the request but that did not change anything)
I have also tried classic rest API without token and got:
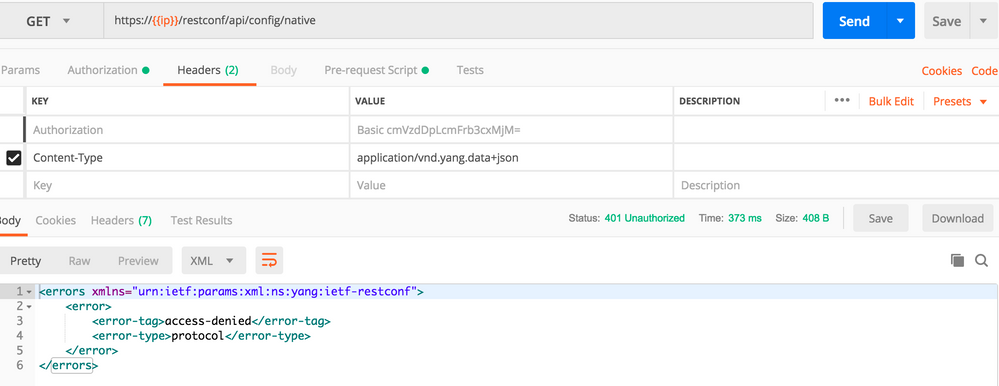
https://{{ip}}/restconf/api/config/native
Response 401:
<errors xmlns="urn:ietf:params:xml:ns:yang:ietf-restconf">
<error>
<error-tag>access-denied</error-tag>
<error-type>protocol</error-type>
</error>
</errors>
Debugs on CSR:
%DMI-5-AUTHENTICATION_FAILED: R0/0: dmiauthd: Authentication failure from 192.168.1.124:0 for rest over http.
Why failing ?
Thanks,
- Labels:
-
General
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-09-2018 03:03 AM
OK, i've just found a solution for authentication failure (not for 411 error!)
I had exactly same issue with netconf:
To get restconf or netconf working we need to be sure the user is not only in priv15 lvl but also exec mode authorization is enabled via: aaa authorization exec default local (which puts ssh user directly in enable mode).
It would be good to update documentation to reflect that.
I am still troubleshooting my last problem - why when requesting for auth token i got 411 length required.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2019 07:45 AM
I have added all these commands (netconf-yang + priv 15 + aaa authorization exec default group (...))
and still have this error:
%DMI-5-AUTHENTICATION_FAILED: R0/0: dmiauthd: Authentication failure from (...) for netconf over ssh.
in python script i have error:
ncclient.transport.errors.AuthenticationError: AuthenticationException('Authentication failed.',)
while credentials 100% correct
any ideas? soft: 16.8 IOS XE
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-18-2020 08:09 PM
Hi,
I have the same issue. I fix it by performing the following steps:
aaa authentication login default group ISE-GROUP local
aaa authorization exec default group ISE-GROUP local
aaa authentication login NOAUTH none
line console 0
login authentication NOAUTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-18-2020 04:20 AM
double check the line vty 0
i had enabled - due to copy error - no exec.
So the ssh session arrives first via line 0 that serves as a kind of template. Replacing with <exec> solved some issues 🙂 BUT NOT ALL
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-18-2020 11:55 AM
I was getting the same error with "Basic Authorization":
%DMI-5-AUTHENTICATION_FAILED: R0/0: dmiauthd: Authentication failure from 10.1.1.1:0 for rest over http
after enabling exec mode authorization it worked: # aaa authorization exec default local
%DMI-5-AUTH_PASSED: R0/0: dmiauthd: User 'devnet' authenticated successfully from 10.1.1.1:0 and was authorized for rest over http. External groups: PRIV15
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-18-2020 10:41 PM
And furthermore, I'm currently working on 4K ISR routers.
Apparently they where 'defaulting' with:
ip http secure-active-session-modules HTTPS
ip http timeout-policy idle 600 life 86400 requests 1000
ip http session-module-list HTTP ITS_LOCDIR,CME_EM_LOGIN,CME_SERVICE_URL,CME_AUTH_SRV_LOGIN
ip http session-module-list HTTPS ITS,WEB_EXEC,HOME_PAGE
ip http active-session-modules HTTP
This configuration did not accept the API request. Disabling this, allowed API request to the router. But - I guess this should be enabled, although I do not know today how to enable the 'API-service'. Also, I do not know that putting in the 'ip http secure-server' to enable restoconf/netconf, created the above configurations.
Good luck in your development and experimentation.
B
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2021 04:58 PM
I have fixed my RESTCONF issue by just re-adjusting the privilege level of my user account.
I was using:
#ip http secure-server
#ip http authentication local
on the router, with a username that was created following:
#username admin secret cisco
It turns out that the error I was getting "authorization error" in my API call was related to the privilege level o the user
To fix it:
#username admin privilege 15
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2021 10:25 PM
Indeed, good to read you have found the issue.
Maybe look at this video: it is a good start and that basic configuration works like you have found already:
https://youtu.be/qeanMXpcHIk?t=177
2:57
Not that I like the sound of his voice or video's 🙂
Another good reading are the DevNet labs. Different tracks available. My tip: start small and go get information from your devices.
Start with getting accustomed.
Good luck in your journey.
Bart
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide