- Cisco Community
- Technology and Support
- Security
- Email Security
- Cisco ESA Spoof Protection not working correctly
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Cisco ESA Spoof Protection not working correctly
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-13-2019 01:54 AM
Hi all,
we set up Spoof Protection as described here: https://www.cisco.com/c/dam/en/us/products/collateral/security/cloud-email-security/guide-c07-740417.pdf
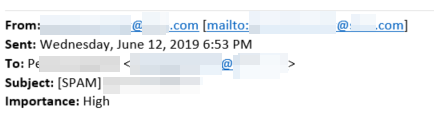
Unfortunately a user received a message from himself.
From: firstname.lastname@domain.tld [mailto:firstname.lastname@domain.tld]
This is the mail header:
Received: from exchange03.domain.tld (x.x.x.x.) by exchange02.domain.tld (10.220.1.102) with Microsoft SMTP Server (TLS) id 14.3.266.1; Thu, 13 Jun 2019 06:42:07 +0200 Received: from ironport.domain.tld (x.x.x.x) by exchange03.domain.tld (10.220.1.103) with Microsoft SMTP Server (TLS) id 14.3.266.1; Thu, 13 Jun 2019 06:42:06 +0200 X-Amp-File-Uploaded: False X-Amp-Original-Verdict: FILE UNKNOWN X-Amp-Result: UNKNOWN X-IronPort-AV: E=Sophos;i="5.63,366,1557180000"; d="jpg'145?scan'145,208,217,145";a="3806876" Subject: [SPAM] firstname.lastname X-IPAS-Result: A0EX/gA6LQFdZBXtipmQeAqqPxiHL0wHCAEDAgKIF7t3jzeJbg X-IronPort-Anti-Spam-Result: =?us-ascii?q?A0EX/gA6LQFdZBXtipmQeAqqPxiHL0w?= =?us-ascii?q?HCAEDAgKIF7t3jzeJbg?= X-IronPort-Anti-Spam-Filtered: true IronPort-PHdr: =?us-ascii?q?9a23=3AenvbohD1SAXwG16cDhYjUyQJPHJ1kqjoPgMT9p?= =?us-ascii?q?ssgq5PdaLmxZn5IUjD/qs13lrAXIHU4ugCkPfNqObrXmlTqY2ZviU6eYdXHw?= =?us-ascii?q?QAld1QmgUhBMCfDkiuMeX3bgQlG95GWAU5oTewNg5XAJ+kNWffqXCz8zMeXy?= =?us-ascii?q?7HG1Uqf7bNE5XJx4Sy3uG29JTJJR5VnyH7arR3fl26qgDYt89ehoUHSO551w?= =?us-ascii?q?DUo1NXfP5SyTk0exSYmFD+/o+88YVi/CJZp/86v5cdCuOjJPR+F+cHSm5/e2?= =?us-ascii?q?kurNXmrxzCUReC6h5+Gi0NnxxEDhKEpBD2U5Htszfr4+902S2UJ8rzHvg/XT?= =?us-ascii?q?Wv6bsuSQe90XpccWdioCeN0ZM21vsIxXDp7wZyyIPVfoyPYf93f6fSdMlcXn?= =?us-ascii?q?daRYBaUCkSZ+H0J4YJEecFOv5V6ofnoF5b5walGAiEG+T1zjMS2iGw1qp80f?= =?us-ascii?q?xrQmSklEQwWskDtnjZtoC/KbwPUMiqy7PMwW+fMbVd3nH/8MKbOgBkqvaKU7?= =?us-ascii?q?VqdMPXwkR6DBvLuVKWrZ22WlHdnvRIqWWQ6PBsEP6+k2Ny4R8kuSChn41/wp?= =?us-ascii?q?mMnI8ezUrIsDl00Jpgb8PtU1Z1OLvGWNNRr33IbtEsBJpkGTo0/n59kOFOuI?= =?us-ascii?q?bnLnFQktJ9l1iGM6fBK8/SvlriTLrDeG0lwis6IPTu3VDqthL8r4+0HsisjA?= =?us-ascii?q?QT83EDy4Oc8CxdkUSUsJTPS+MhrB78gnDWjFCVsLoaZxhzz/CTKoZ9kOdtzd?= =?us-ascii?q?xK7RWFR3Ou3h2x1vXzFA1s+/D0ub26OfO/+s7abtMozFm5aPpmm9TjU71laU?= =?us-ascii?q?5XAzndo73kkuS5rQqjHdAoxrU3ivWL6c2BY51H9+jjWVATisF5tV6+F2v0iY?= =?us-ascii?q?lD2yBbfRQfIkPB18+zZjSsaLj5Favt2gn31m43lracZeSnWtKXcDDCiOuzJO?= =?us-ascii?q?smrRcAmUxplo0Zv9UOVNRjaLryQhOj7YGDSEZlYkrun7ihUJInissfQT7dW/?= =?us-ascii?q?LCdvqP6hnWvKR3ZLPXLI4N5GSkdqNjvqO1yyFj3wFBOvP3uPlfIHGgQqY/fh?= =?us-ascii?q?7fOCe3xIlfVz9N5FR2TfS22gTfCngKOi30Af16vnZhVsqnFduRH9D1xufemn?= =?us-ascii?q?3jRdsOIToZbzLEWXbwK9feAq9KMnnIZJU6w3pcEuL9A445iUP07Va8kuA2aL?= =?us-ascii?q?OIvHVf786rwtFx46eKxEMCsAdsBsHY6FmjCmR9n2cGXTgzhf4tvktnzlvZjf?= =?us-ascii?q?Y+iPseF8QBvv4=3D?= IronPort-SDR: jOsfPEwQtLz8iBcH6oeX/kmebMBcosYA7Uf8266J7rX0CCmf3QzB9GhFtHVLycZCVVx4KzbhCR MkzGaCmJKeji4HD+BvqtT0qZVNYiOr+I5ucEW9kmSAzyjF1KtDWc7eal8Qn5QSki4c0jymYg3k maKxlvIN8gKAhoUAVWXXVzNodqnV3xWRnfMKFUNRWowbjI++T2vX3sj/5AbuSbZ72hZj7lIa2R X9JR/TFmUtZguFKHxqYk+kc0yMErWb1gEHZUvx8c26Ph8p8O1ib4lo0DH0+4CdcEbBOdshY8S5 mkbuXHW06MFdGKGeWkPbgyKa Received-SPF: Pass (ironport.domain.tld: domain of usui@world246.co.jp designates 153.138.237.21 as permitted sender) identity=mailfrom; client-ip=153.138.237.21; receiver=ironport.domain.tld; envelope-from="usui@world246.co.jp"; x-sender="usui@world246.co.jp"; x-conformance=spf_only; x-record-type="v=spf1"; x-record-text="v=spf1 ip4:122.1.234.0/24 ip4:122.28.103.0/24 ip4:125.170.92.0/24 ip4:153.128.48.0/24 ip4:153.138.236.0/22 ip4:153.149.140.0/22 ip4:153.149.144.0/26 ip4:153.149.210.128/25 ip4:153.149.227.0/26 ip4:153.149.229.0/25 ip4:153.149.231.0/26 ip4:153.149.235.0/26 ip4:153.149.246.0/24 ip4:153.153.62.0/23 ip4:153.153.62.64/26 ip4:153.153.66.0/26 ip4:153.153.67.0/26 ip4:180.37.203.0/27 ip4:210.232.239.0/24 ip4:211.129.14.0/24 ~all" Authentication-Results: ironport.domain.tld; spf=Pass smtp.mailfrom=usui@world246.co.jp Received: from oogw1619.ocn.ad.jp ([153.138.237.21]) by ironport.domain.tld with ESMTP; 12 Jun 2019 18:53:00 +0200 Received: from cmn-spm-mts-007c1.ocn.ad.jp (cmn-spm-mts-007c1.ocn.ad.jp [153.153.67.163]) by oogw1619.ocn.ad.jp (Postfix) with ESMTP id ABD78D00632 for <firstname.lastname@domain.tld>; Thu, 13 Jun 2019 01:52:57 +0900 (JST) Received: from mwb-vc-mts-002c1.ocn.ad.jp ([153.138.237.206]) by cmn-spm-mts-007c1.ocn.ad.jp with ESMTP id b6Thh68GSxayib6UbhSYhu; Thu, 13 Jun 2019 01:52:57 +0900 X-BIZ-RELAY: yes Received: from sgs-vcgw117.ocn.ad.jp ([153.149.141.227]) by mwb-vc-mts-002c1.ocn.ad.jp with ESMTP id b6UbhUHD5Pu64b6UbhdCtZ; Thu, 13 Jun 2019 01:52:57 +0900 Received: from world246.co.jp (world246.co.jp [61.126.63.35]) by sgs-vcgw117.ocn.ad.jp (Postfix) with ESMTP id 41EB824027A for <firstname.lastname@domain.tld>; Thu, 13 Jun 2019 01:52:57 +0900 (JST) Received: from [191-37-79-238.cntfiber.net.br] (unknown [191.37.79.6]) (using TLSv1 with cipher DHE-RSA-AES256-SHA (256/256 bits)) (Client did not present a certificate) by world246.co.jp (Postfix) with ESMTPSA id 8981BFA06C4B for <firstname.lastname@domain.tld>; Thu, 13 Jun 2019 01:52:54 +0900 (JST) To: <firstname.lastname@domain.tld> Date: Wed, 12 Jun 2019 18:52:57 +0200 Feedback-ID: 548861:37297860.09834206:c17:gs User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:52.0) Gecko/20100101 Thunderbird/52.0 Errors-To: tlas1q6gl8jndgdjtta@world246.co.jp Content-Type: multipart/related; boundary= "42BA930A9710E9BA89-0359E07F74A1-08C6D57BBB3505A225-4327C8D9E21-F408A" MIME-Version: 1.0 List-Help: <http://www.world246.co.jp/lists/?p=preferences&uid=kxr4k59jfw368nq8x6fnz6162g35qp0c> X-Priority: 1 Message-ID: <v5xc36y-1so7xu-35@world246.co.jp> From: <firstname.lastname@domain.tld> Organization: Iiqvmayafsgw Abuse-Reports-To: <abuse@world246.co.jp> X-Sender: <usui@world246.co.jp> List-ID: <mossojgysy-73822-06857> X-CSA-Complaints: whitelist-complaints@world246.co.jp Return-Path: usui@world246.co.jp
Why did the message pass the Mail Flow Policies? The mail server 153.138.237.21 is not on our whitelist - I just double checked it...
Thanks,
P.
- Labels:
-
Email Security
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-13-2019 10:39 AM
Hello,
The guide you mention seems to instruct you to use the Sender Verification table. This is fine, but, this would only be checking against the Envelope Sender domain. Which, in this case, was usui@world246.co.jp. The From shown in most email clients will not be using the Envelope Sender, but instead the actual From header. Which, in this case, was From: <firstname.lastname@domain.tld>.
The From header and Envelope Sender are completely separate and is the most probable cause as to why the set up in this particular case has failed.
What you can do instead is set up a Message Filter to look for your internal domain in the From header and if the email is not tied to the RELAYED Mail Flow Policy then take appropriate action.
Here is one that I typically provide as an example (of course, this would need to be modified to fit your needs) :
SpoofExample:
if (sendergroup != "RELAYLIST") AND ((header("From") == 'example.com') OR (mail-from == 'example.com'))
{
log-entry ("**********Spoof Message**********");
quarantine('Policy');
}
In short, it says if the Sender Group does NOT equal the RELAYLIST AND the From header contains example.com OR the Envelope Sender contains example.com, then log an entry and send this email to the Policy quarantine.
Thanks!
-Dennis M.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide