- Cisco Community
- Technology and Support
- Security
- Endpoint Security
- Re: Cisco AMP and Windows Defender
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Cisco AMP and Windows Defender
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2018 10:10 AM - edited 03-08-2019 05:46 PM
We recently attended a "test drive" class for Cisco AMP where they mentioned that AMP was approved by Microsoft as a 3rd party AV client that should disable windows defender. I've linked the KB below. We have several test machines with AMP deployed that also have windows defender enabled by default in Windows 10. Does anyone have any insight into this?
- Labels:
-
Other AMP Topics
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-27-2018 01:10 AM - edited 02-27-2018 01:23 AM
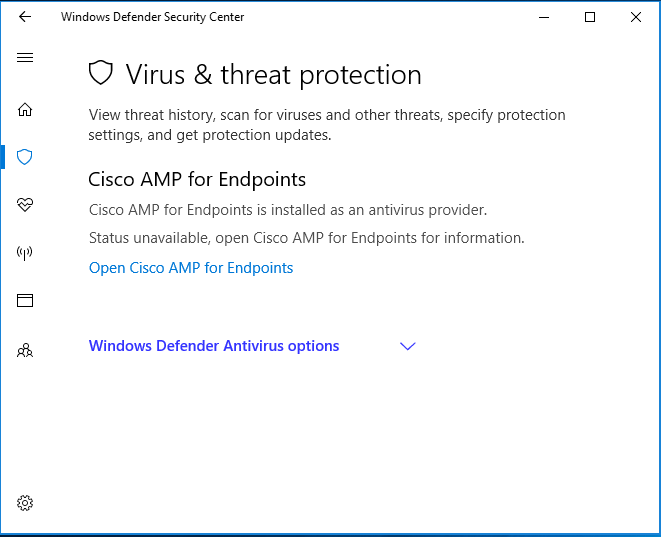
In order to replace Windows defender, the AMP policy for the endpoints must include the optional Tetra engine so that the ClamAV signatures will be downloaded and in effect.
Once you do that, Windows Defender Security Center will indicate that Virus and threat Protection is being provided by Cisco AMP for Endpoints.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-22-2021 01:05 PM
Does this disable Windows Defender completely?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-06-2021 09:49 AM
Should the machine still run Windows Defender firewall?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-06-2021 12:48 PM
Hi,
I use Secure Endpoint (AMP) and Windows Firewall at the same time. And I had not any issue.
M
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2021 07:48 AM
I am finding that on Windows 10 multi-session ( 7.4.5.20701) and on Windows Server 2019 (7.3.9.20091) AMP/Endpoint Security is failing to register with Windows Security Centre - well WSC does not show AMP/Endpoint Security as the active AV, and Defender is still running. This has caused problems where both product ran scheduled scans at the same time. I read in the "Secure Endpoint (formerly AMP for Endpoints) User Guide, Last Updated: July 30, 2021" page 108 "IMPORTANT! Windows Defender cannot be automatically disabled in Windows Server versions 2016 and later. If you want to run TETRA on those operating systems you must disable Windows Defender manually."
So which is true, does 7.4.1 and later register with WSC regardless of Tetra, 7.3.9 depending on Tetra (which is enabled); or on Server 2016 and later, is that really broken? Windows 10 multi-session does report as a server OS in some regards. I am trying to understand if this is not working as expected (so we open a TAC call) or just how it is, bad luck.
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-29-2021 10:53 AM
We're experiencing a similar situation with our Windows 10 workstations; AMP is not registering itself as the primary av provider thus Windows Defender is not getting disabled.
Did your issue resolved, if so could you share?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-19-2021 01:01 AM
Same problem here.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-30-2021 02:14 AM
It is very innovative. Thank you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-22-2021 02:53 AM
It seems that Windows 10 multi-session behaves like a Windows Server build, and also lacks the service that allows Endpoint Security to notify the Windows Security Centre that it is running. There is a Microsoft article about Windows Defender and 3rd party anti-virus product co-existence:
That is helpful but you just have to experiment.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-22-2021 08:04 AM
Hi folks,
with the help of TAC this got resoved quickly. @noc : No, this is only the case for the server version and it was not Tetra-related.
In my case, the following solution worked (quoted from my TAC resolution), removing the registry key was essential:
I already finished to review the logs, It seems there is an issue with CiscoSCMS service:
(529562, +0 ms) Dec 18 21:54:47 [21304]: ERROR: AmpMonitor::ScmInstall: CreateService failed : 1073 : Der angegebene Dienst ist bereits vorhanden.
(529671, +0 ms) Dec 18 21:54:47 [21292]: ERROR: AmpMonitor::ScmProtect: ChangeServiceConfig2 failed : 5 : Zugriff verweigert
(529812, +16 ms) Dec 18 21:54:47 [27392]: ERROR: AmpMonitor::ScmStart: StartService failed : 2 : Das System kann die angegebene Datei nicht finden.
Action Plan
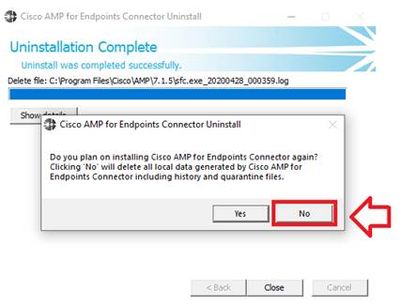
- Manually Uninstall completely the AMP connector
- When this message appears, please select “NO”
- Verify if CiscoSCMS service remained in Windows services and remove the registry key manually using powershell commands with Administrator privlidges:
:\> set-Location HKLM:\system\currentControlSet\Services\
:\> Remove-Item .\CiscoSCMS_7.3.*
- Reboot the endpoint
Perform a full reboot, you can use the following command from CLI: shutdown -r or shutdown /r
- Download a fresh connector installer, install the connector again and verify if the issue persist.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-22-2021 08:13 AM
To clarify... after installing using the new installer, AMP now disabled the Windows Defender on server OS?
Ken
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-22-2021 12:42 PM - edited 12-22-2021 12:48 PM
Hi Ken,
no, I am only talking about Windows 10 notebooks and workstations, not servers! However, you can happily run both, AMP now is the active (primary) one, as ist is supposed to be. Technically defender ist listed as inactive, but you can still let it run scheduled scans in addition. In the perception of defender it switches to inactive, because the main component "real-time protection" is disabled and taken over by AMP.
PS: Don't do that with Kaspersky, Avira or others, leads to all kind of unpredictable effects.
Hope that clarifies matters.
Regards, gernot
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-22-2021 08:19 AM
We were able to resolve this issue by updating Windows Defender to version 4.18.2110.6. Once this was in effect all systems switched over to using AMP as the primary AV provider and disabled Windows Defender.
We did not have to make any registry changes. Hope you are able to find some success with this.
Cheers,
Mark
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-10-2022 07:45 AM
I am also having the same issue.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide