Cisco ISE. Using a compliance and posture check with third party VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-07-2021 02:22 AM
Hello everyone.
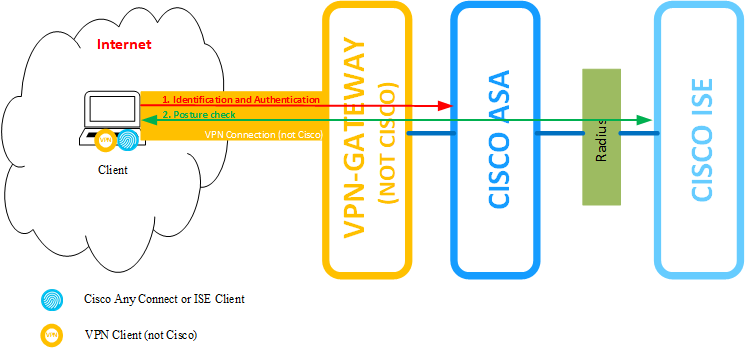
We are going to use Cisco ISE for verify a compliance on clients using a posture check. But we must use a different VPN Gateway (not Cisco and not Cisco Anyconnect) so it is our country legislation requirement.
Please, look at my picture. Can I use posture check NOT to establish Anyconnect VPN connection? Can Anyconnect to connect to cisco ASA without VPN establishing to avoid VPN inside of VPN?
Thank you
- Labels:
-
Integrations
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-08-2021 11:24 AM
I have a couple questions:
Are you using ISE for the non-Cisco VPN authentication?
Can ISE change security results or send CoAs to the non-Cisco device if an endpoint isn't compliant?
Not even getting into the AnyConnect Posture module specifically, what is ISE supposed to do if it's not able to change the non-Cisco VPN session and can't prevent network access anyway?
I believe that it can be done, it would require a little more research, but I'm not sure the value if ISE can't deny or limit access when a device isn't compliant, which would require that ISE be the authentication server for the non-Cisco VPN.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-11-2021 01:20 AM
Hi, ComputerRick
Thank you for you amswer.
<Are you using ISE for the non-Cisco VPN authentication?>
No. Non-Cisco VPN authentication is the first step of authentication. Authentication in ISE - the second.
<Can ISE change security results or send CoAs to the non-Cisco device if an endpoint isn't compliant?>
No. Non Cisco VPN Gateway is not compatible with ISE. I am considering that ISE will send CoAs to Cisco ASA. I see the architecture like next way:
1. Endpoint connect to non-Cisco VPN and authenticate on it using certificate. If success, he got only access to restricted network where he see only ISE server.
2. ISE Agent connect to ISE and ISE authenticate it (maybe user has to click to agent and establish connect and provide login/password)
3. ISE send to agent a command for posture check. If ok, ISE send a CoAs to ASA to apply access list for network acces.
4. If Not, Cisco ISE send non-Cisco VPN Gateway command to disconnect using SSH-commands (I don't sure, that it's possible, need to research)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-11-2021 06:27 AM - edited 10-11-2021 06:29 AM
In your initial question, you asked if there was a way to "connect to cisco ASA without VPN establishing to avoid VPN inside of VPN", to which I would say no. In your response, you then stated "maybe user has to click to agent", which would be needed to establish a tunnel in tunnel. The ASA would then become the headend for your network access and all access control could be done with the ASA and ISE at that point.
I believe that there is any way that ISE could disconnect a session using SSH for the non-Cisco VPN. The non-Cisco VPN could restrict access to the ASA only, in which case it would likely meet your needs and still allow for full access/posture control at the ASA.
I'd really suggest engaging with your Cisco account team or VAR about design on this to ensure that you can meet the legal requirements and still have the security you're seeking.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-13-2021 04:20 AM
Hi, ComputerRick
Thank you for you answer.
On picture I pointed Cisco AnyConnect on client computer. Can we use a Cisco NAC Agent instead?
If yes,
1. Can we authenticate client user/computer using a windows domain belonging?
2. How NAC Agent-to-ISE Server pushing happen to make Agent to start posture check? Does NAC Agent connect immediately without any user actions as It sees a ISE Server? Or Does Cisco ASA see a new divice and send a command to ISE server?2
Thank you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-13-2021 09:39 AM
The NAC agent is going to be for dot1x and I haven't been able to find a way to pass dot1x traffic through any intermediate devices. So, I doubt that using the NAC agent would be an option. Even if you could get it to work, I'd worry about it working consistently.