- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Invoking Rules on ISE
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-04-2017 11:33 AM
Describe how and when the authorization rules are invoked. Can the system invoke authorization rules:
Automatically, upon meeting the conditions?
Scheduled to run at set times?
On-demand through the system GUI?
Through a web-based API
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-04-2017 12:41 PM
All the above.
ISE guests, posture, and profiling usually invoke re-authentication automatically. So is Rapid Threat Containment (RTC).
ISE endpoint purge policy runs at a fixed time ~ 03:00 server timezone every day and will trigger CoA on the affected endpoints.
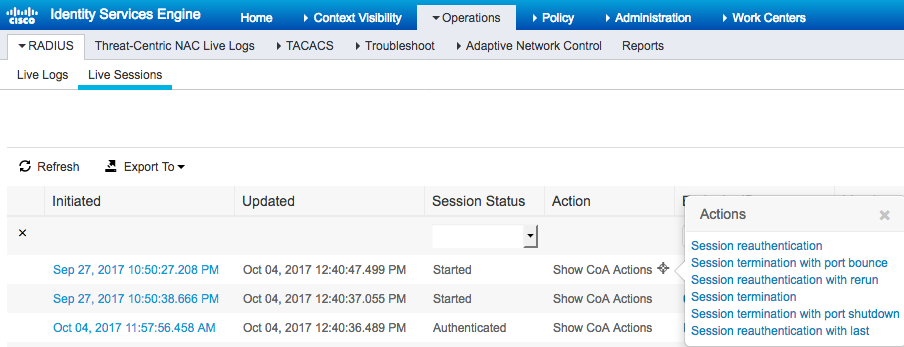
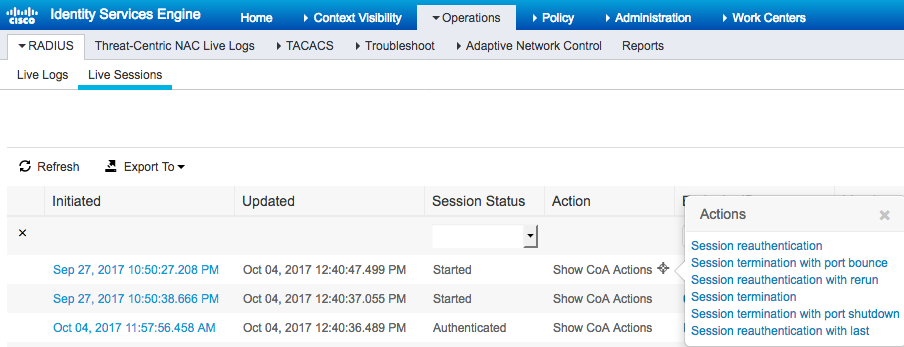
ISE has CoA options @ M&T live session view.
Web-based API is available. Please refer to Using Change of Authorization REST APIs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-04-2017 12:41 PM
All the above.
ISE guests, posture, and profiling usually invoke re-authentication automatically. So is Rapid Threat Containment (RTC).
ISE endpoint purge policy runs at a fixed time ~ 03:00 server timezone every day and will trigger CoA on the affected endpoints.
ISE has CoA options @ M&T live session view.
Web-based API is available. Please refer to Using Change of Authorization REST APIs
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide