Hi. I have some queries using the ASA 5506-x in transparent mode. I wish to use the ASA 5506-x within a specific subnet of our network, to isolate 3 devices, not the traditional firewalled, routed, internet access config in most examples I can find online.
The 3 devices will be in their own subnet, connect to a core L3 switch, with the SVI configured. Due to various reasons these 3 devices must be behind a firewall and rules in place to allow specific traffic to a server elsewhere in the network. Not required to use NAT. The ASA will be transparent mode.
I believe if I used routed mode the connection to the core switch will be the trusted 'inside'. The 3 devices will be the untrusted 'outside'. As I will be using transparent mode, does the concept of inside and outside interfaces exist with transparent mode? Please see diagram of required setup.
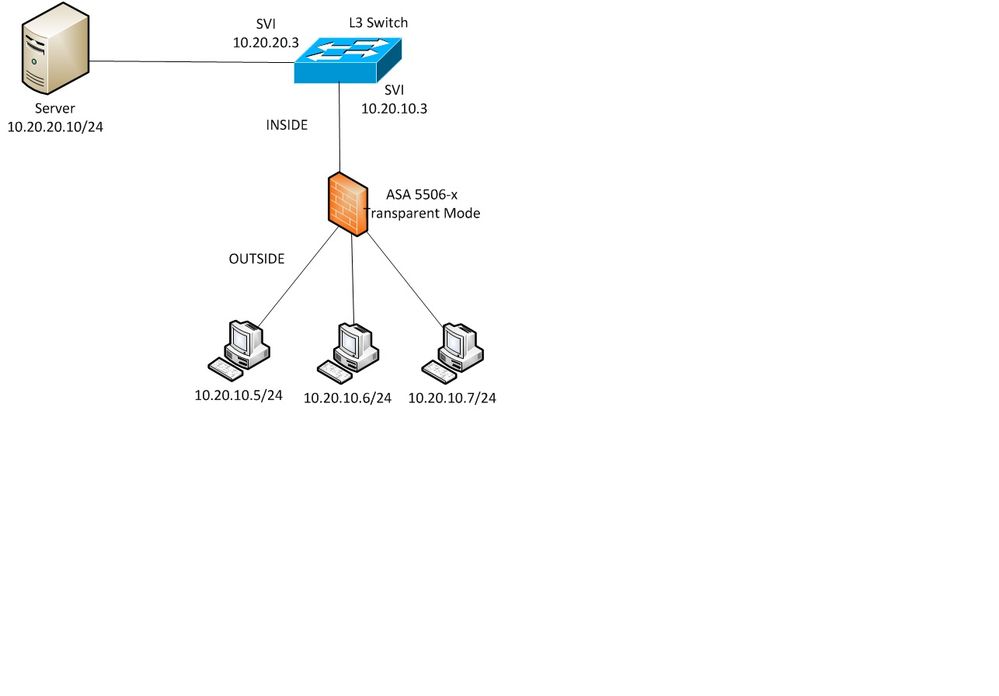
The 3 devices must be able to communicate with each other. I understand interfaces can be bridged to act as switch ports for this purpose.
The 3 devices must be able to communicate with the server - based on specific rules
The server must be able to communicate with each device
Is all this possible using transparent mode?
Do I need to put all interfaces in one bridge group (including the link to the core L3 switch)?
How would I then treat part of this bridge group as outside (containing the 3 devices) and part as inside (link to network) which then allows me to restrict traffic from the 3 devices into the network.
Traffic from server to the 3 devices should be ‘automatically’ allowed due to inside to outside traffic flow – is this possible in transparent mode, can interfaces in the same bridge group then still be named and have the security levels assigned, i.e. 100 for inside, 0 for outside.
Any assistance on configuration would be appreciated.
Thanks