- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- Cisco Digital Network Architecture Center Modules (Design Module)Part.2
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
11-10-2019 10:24 AM - edited 11-10-2019 10:25 AM
Cisco Digital Network Architecture Center Modules
(Design Module)Part.2
- In this article, we are going to talk about the Cisco Digital Network Architecture Center design Module.
Cisco DNA Center gives us the flexibility and availability to configure multiple fabric sites and manage all of them through DNAC (Centralization Point).
- The continuity of IT operations is the basis of today’s business environment. Almost every single decision made by the business is either based on IT data or done using the IT platform. And so, the Design, security, availability, and performance of the IT infrastructure are the key foundation of a solid business and service environment.
- After we finished the DNAC deployment in the previous article we will start to configure DNAC, We will start by design module as I mentioned in the title.
https://www.linkedin.com/pulse/cisco-digital-network-architecture-center-modules-design-alhenawy/
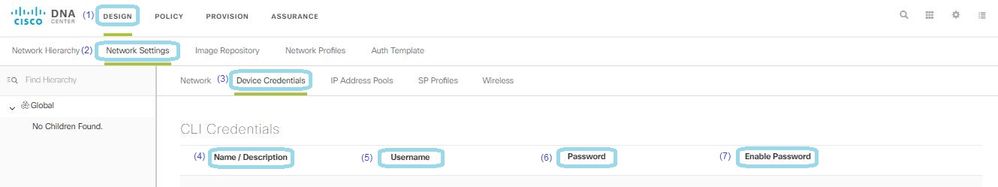
- We are going to write about Device Credentials.
- What is the device credentials Services in the network settings?
The Device credentials are used to log in to the CLI of the devices in your network, Also Snmp Credentials, Https Credentials.
Configure Global CLI Credentials:
Design ----> Network Setting ----> Devices Credentials ----> Click Add ----> Write Name or description ----> Username to login CLI of the Network Devices ----> Password for the username of the CLI ----> Enable Password ----> SAVE.
Configure Global SNMPv2c Credentials: SNMP to manage and monitor the Network devices.
Design--- > Network Setting --- > Devices Credentials --- > SNMP read--- > Click Add --- > Write Name or description--- > read community string password [to read only the information of the network device] --- > SAVE.
Design--- > Network Setting --- > Devices Credentials--- > SNMP Write--- > Click Add --- > Write Name or description--- > Write community string password [ to make the change on the network device ]---- > SAVE.
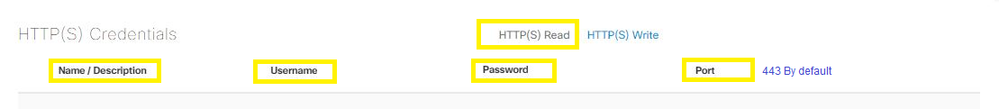
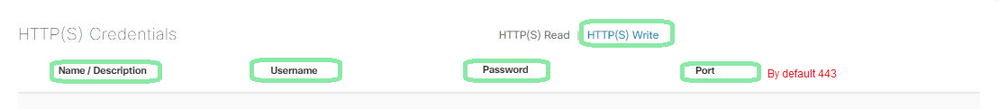
Configure Global HTTPS Credentials:
Design ---> Network Setting --->Devices Credentials--->HTTPs read --->Click Add---> Write Name or description --->Username of Https Auth ---> Password of Https Auth---> Port Number by default is 443--->SAVE.
Design ---> Network Setting --->Devices Credentials--->HTTPs Write--->Click Add --->Write Name or description --->Username of Https Auth--->Password of Https Auth--->Port Number by default is 443--->SAVE.
*** I hope that has been informative for you and thank you ***
Mohamed Alhenawy
CCIE#60453
-
Announcements
-
AppDynamics
-
Assurance and Policy
-
Automation
-
Catalyst 2000
-
Catalyst 4000
-
Catalyst 9000 Switches
-
Catalyst Switch
-
Cisco DNA Automation
-
Cisco DNA Center
-
Cisco ENCS
-
Configuration
-
EEM Scripting
-
LAN
-
LAN Switching
-
Network Management
-
NFVIS
-
Optical Networking
-
Other Routers
-
Other Routing
-
Other Switches
-
Other Switching
-
Routing
-
Routing Protocols
-
SD-Access
-
SD-WAN
-
vEdge Routers
-
WAN
-
Wi-Fi 6
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
*** I hope that has been informative for you and thank you ***
not really, this doesn't answer
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Oh , Long time @Gioacchino
you can check these options --> Instead of using individual user credentials, you can create a dedicated service account with a fixed password on the switches. This service account should have appropriate privileges to perform the necessary operations within Cisco DNA Center. This way, you can configure the CLI credentials on DNA Center using the fixed password of the service account also Consider using RADIUS or TACACS+ authentication for your switches instead of RSA token-based authentication. RADIUS and TACACS+ provide centralized authentication and authorization, allowing you to use fixed credentials for authentication. You can configure the RADIUS or TACACS+ server (e.g., Cisco ISE) to handle the authentication and authorization process for your switches, and then configure DNA Center to use RADIUS or TACACS+ for device authentication.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: