- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- Deploying IPv6 in Broadband Access Networks
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 11-18-2010 05:34 AM
Introduction
IPv6 has been deployed in several Service Provider (SP) core networks around the globe due to different reasons such as long term expansion plans and service offering strategies, preparing for new service types, gaining competitive advantage and so forth. Recently IPv6 is being actively deployed in SP broadband access networks.
Cable, Digital Subscriber Line (DSL), Ethernet to the Home (ETTH) and Wireless services are the main broadband technologies that are widely deployed today. As the number of broadband users increases exponentially worldwide, Cable, DSL, ETTH, Wireless and other always-on access technologies along with IPv6’s huge address range, long-lived connections to servers and permanent prefixes for home appliances gives more flexibility to SPs. Specifically the addressing capacity of IPv6 has made it valuable to SPs, most of whom are rolling out IPv6 support in their networks or aggressively evaluating its potential and value for service delivery. Outside the US, IPv6 adoption is being promoted on a national level, and countries such as Japan, Korea, China, India and some European countries have taken lead roles in moving from testing and evaluation to actual deployments in broadband services and applications.
Until recently IPv6-based services were considered only as differentiators that allowed SPs to primarily exploit the large address space available in IPv6 for future growth planning and as a competitive advantage. However as IPv6 has become more popular and familiar, SPs are adopting the protocol not only to offer new services to their customers but also for provisioning and managing large number of network devices and applications. Governmental interest and promotion by means of incentives and favorable legislation is also a major driver for the growing adoption of IPv6 in SP and Enterprise Networks.
IPv6 Deployment Options and Considerations
Several deployment options are available to SP for integrating IPv6 in their networks. Figure 1 below depicts an end-to-end SP network with some of the most commonly deployed Access Broadband technologies, a core network and backend provisioning and network management servers. The access layer of the network features different terminologies for Provider edge (PE) devices in the various access models, however in all cases PE devices function similarly by acting as head-end devices. These head-end devices connect to multiple downstream customer premises devices using different encapsulations techniques, protocols and methodologies.
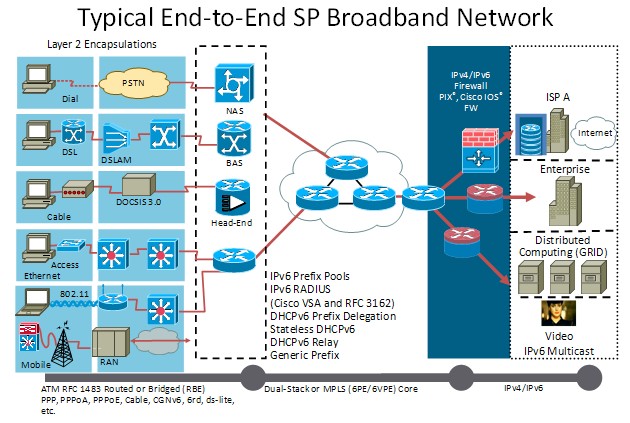
Figure 1
Some of the commonly used techniques for integrating IPv6 in IPv4 Broadband Access networks include:
- Dual-stack IPv4 and IPv6
- Dual-stack with tunneling
- IPv6-only to IPv4-only translation
Dual-stack IPv4 and IPv6
In a dual-stack environment, both IPv4 and IPv6 are enabled on network devices. There are two commonly deployed models in broadband access networks (with the exception of Cable networks):
1. PPP Model
Single or dual PPP sessions are used with dual-stack IPv4/IPv6. Native dual-stack IPv4/IPv6 service on Residential Gateway (RG) LAN side is used and no changes are required in existing Access/Aggregation infrastructure.
In the single PPP session approach, dual-stack IPv4/IPv6 services are supported over a shared PPP session with IPv4 and IPv6 Network Control Protocols (NCPs) running as ships in the night. This approach has limited impact on PPP control plane and Broadband Network Gateway (BNG) data plane.
Figure 2 illustrates the single session PPP model.
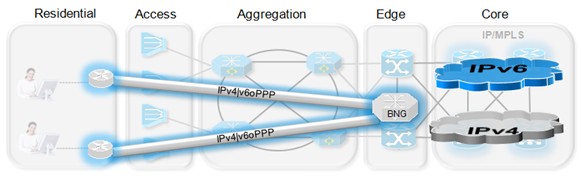
Figure 2
In the dual PPP session approach, one PPP session per Address Family (IPv4 or IPv6) is used. This approach may require twice as many resources on the BNG (states, subscriber plane, memory) as compared to the single PPP session approach, its impact on the network resources should be analyzed in the planning phase of IPv6 deployment strategy.
Figure 3 shows the dual session PPP model.
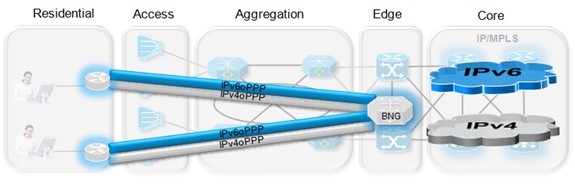
Figure 3
Both approaches use IPCPv6 for Link-Local address assignment and Stateless Address Auto-configuration (SLAAC) or DHCPv6 for Global IPv6 address assignment.
2. IPv6 over Ethernet (IPv6oE) Model
IPv6oE with 1:1 VLANs mapping model is similar to PPPoE models, however it has some differences such as subscriber line-identifier used for 1:1 VLAN mapping (S-TAG, C-TAG). At Layer2, IPv6oE with 1:1 VLANs does resemble PPPoE such as point-point broadcast domain does not require any special Layer2 forwarding constraints on Access Node. However 1:1 VLANs and IPv6oE do require some extra BNG functionality such as IPv6 Neighbour Discovery (ND) support.
Figure 4 illustrates the IPv6oE with 1:1 VLAN Mapping model.
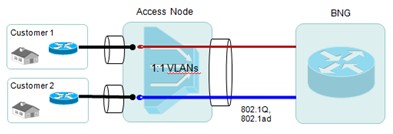
Figure 4
IPv6oE with N:1 VLAN mapping model requires changes in existing Access Node such as support for IPv6 anti-spoofing, RA snooping, DHCPv6 snooping and MLDv2 snooping. Since the VLAN no longer provides a unique subscriber line-identifier, a lightweight DHCP Relay Agent on the Access Node is required to convey subscriber line-identifier information.
Figure 5 illustrates the IPv6oE with N:1 VLAN Mapping model.
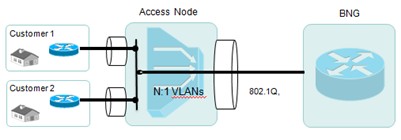
Figure 5
Dual-Stack with Tunneling
There are several tunneling techniques used for integrating IPv6 in existing IPv4 broadband access networks. Some of the key tunneling techniques include:
1. IPv6 over L2TP Softwire Tunnel
This approach requires limited investment and impact on existing infrastructure. Dual-stack IPv4/IPv6 services on RG LAN side are enabled. For PPPoE or IPv4oE, termination is done on IPv4-only BNG. L2TPv2 softwire tunnel is used between RG and IPv6-dedicated L2TP Network Server (LNS) placed in the core network accessing IPv6. This approach has stateful architecture on LNS and offers dynamic control and granular accounting of IPv6 traffic.
Figure 6 shows the IPv6 over L2TP softwire Tunnel model.
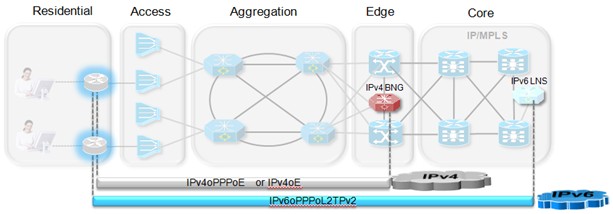
Figure 6
2. IPv6 over IPv4 via 6rd
This tunneling technique is becoming popular among SPs due to limited investment and impact on existing infrastructure and its simple, stateless, automatic IPv6-in-IPv4 encapsulation and de-capsulation functions on 6rd CE (Customer Edge) and 6rd BR (Border Relay). Automatic prefix delegation id done on 6rd CE and IPv6 traffic automatically follows IPv4 routing. A detailed case study of Free ® (largest 6rd deployment) is discussed in our book Deploying IPv6 in Broadband Access Networks.
Figure 7 illustrates the 6rd deployment model.
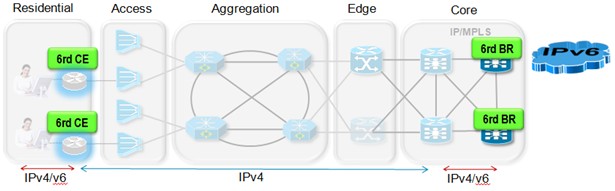
Figure 7
3. IPv4 via IPv6 using Dual-Stack Lite (w/NAT44)
This technique is used when the Access, Aggregation, Edge and Core networks including NMS/OSS/DNS/DHCP services have migrated to IPv6. IPv4 Internet service is available and overlaid on top of IPv6-only network. This approach requires introduction of two components; B4 and AFTR (Address Family Translation Router) where B4 typically sits in the RG and AFTR is located in the Core infrastructure. Key takeaway for this approach is that IPv4 has been phased out and Access/Aggregation network is IPv6-only.
Figure 8 illustrates this model.
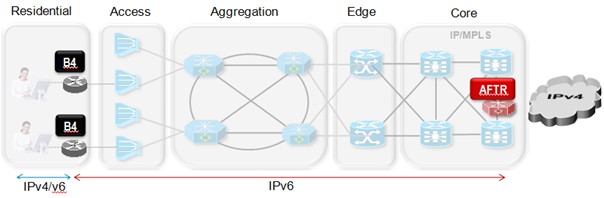
Figure 8
IPv6-Only to IPv4-Only Translation
Connecting IPv4-only with IPv6-only: AFT64 technology is only applicable in cases where there are IPv6-only end-points that need to talk to IPv4-only end-points (AFT64 when initiating from IPv6 to IPv4). The key components of this model include NAT64 and DNS64 while ALG is still required. The key takeaway of this approach is that network infrastructure and services have fully transitioned to IPv6 and IPv4 has been phased out.
Figure 9 illustrates this translation model.
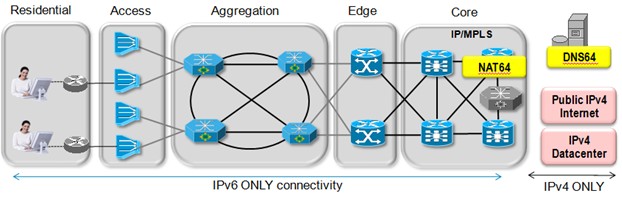
Figure 9
Once the SP has enabled IPv6 in the Access and Core networks, and on backend Provisioning and Management servers, it may consider enabling IPv6 on a per application basis. For example, Cable providers may choose to manage network devices such as Cable Modems (CM) and Multimedia Terminal Adapters (MTA) using IPv6 as a first application.
IPv6 in Cable Networks
Data over Cable Service Interface Specifications (DOCSIS) standard defines the communications and operations support interface requirements for data over cable system. The specification permits high-speed data transmission over an existing Cable TV (CATV) network. It is employed by many Multiple System Operators (MSOs) to provide Internet access over their existing hybrid fiber coaxial (HFC) infrastructure.
DOCSIS 3.0, the latest version of this specification, introduces full support for IPv6, including the provisioning and management of CM with an IPv6 address, and the ability to manage and transport IPv6 traffic over the cable infrastructure. With the changes made to the DOCSIS specification, the Cable Modem Termination System (CMTS) and CM are both IPv6 capable and can natively forward IPv6 traffic. Cable providers may need to upgrade hardware as well as software on their current CMTS and CM in order to natively deploy IPv6 in a DOCSIS 3.0 environment.
Figure 10 illustrates the DOCSIS 3.0 Reference Architecture for IPv6.
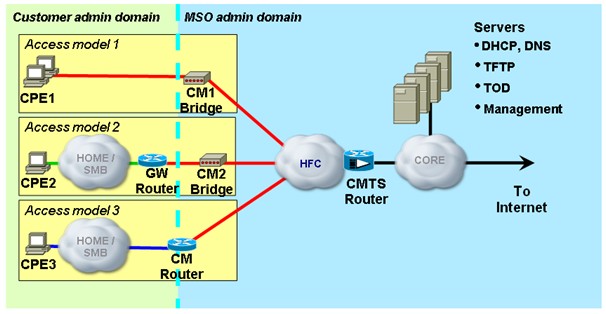
Figure 10
Summary
Deploying IPv6 requires careful planning, a well thought out network design, thorough testing of IPv6 features being deployed to ensure compatibility with existing IPv4 features and services, and a detailed deployment strategy. Depending on the primary drivers for IPv6 deployment and the state of the current IPv4 network, SPs may choose different strategies for integrating IPv6 into their networks.
IPv6 enables SPs to offer new services as well as enhance current services with a focus on servicing end-points. IPv6 services may range from network addressing support for home appliances to peer-to-peer communication, such as Internet gaming, music and video file sharing, IP Telephony and etc. With sufficient address space, in the foreseeable future, for several billion subscribers, appliances and applications; IPv6 is the gateway to the future of Next Generation Internet.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Good whitepaper. Thanks.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Adeel & Salman. Do you think that Dual-Stack Lite is a good alternative?. Some customers are requesting in theirs RFPs Dual-Stack Lite support. I read that Dual-Stack Lite is a promising approach that takes the best of NAT464 while avoiding its problems: It uses IPv6-only links between the provider and the customer, but does not use NAT64 translation.
Regards,
Edward
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: