The purpose of this document is to highlight some of the new changes in Cisco DNA Center 1.3 with relation to SD-Access Fabric. The objective of this document is to provide a quick glance at the Fabric Provisioning tasks with screenshots. The assumption is that the readers are already familiar with deploying SD-Access using 1.2.X and prior versions.
The document is showing an example here where there is already an existing Fabric site and below are the steps that are required when we are adding a new Fabric site, and must not be misunderstood with actual Implementation Guide. This is only a reference.
Follow the best practices that you would normally take in your environments and test out first in the lab or during maintenance window before making any changes.
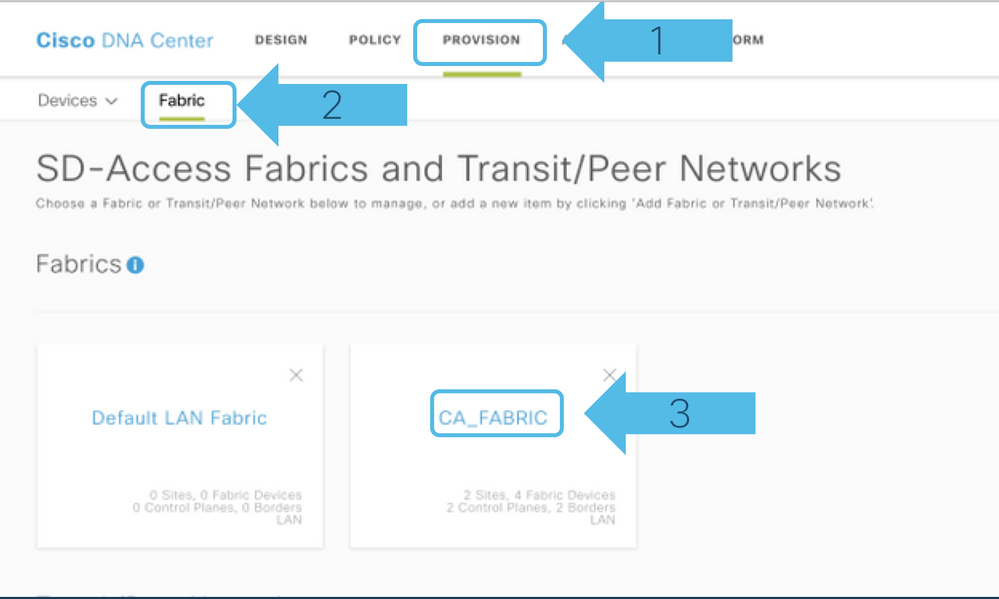
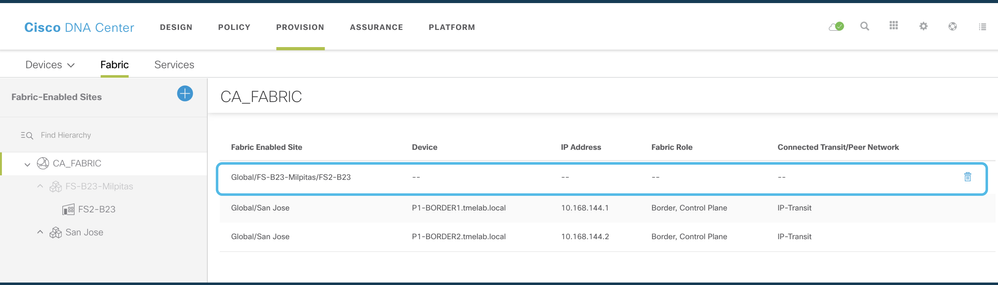
Step1: Go to Provision -> Fabric
Click on CA_FABRIC
Step2: Click on the Plus sign to add new Fabric Site, and then select the location from the popup where you want this Fabric (carried over from Hierarchy created on Design Page) to be enabled and click Next as shown below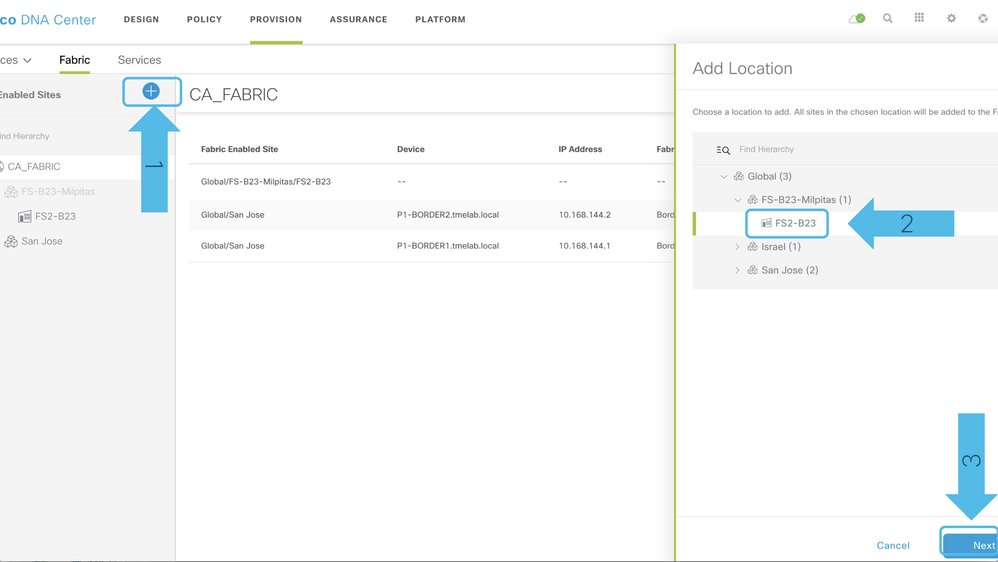
Step3: Next, you would be presented with a list of VNs that would need to be used later in the Fabric. By default, INFRA_VN and DEFAULT_VN are selected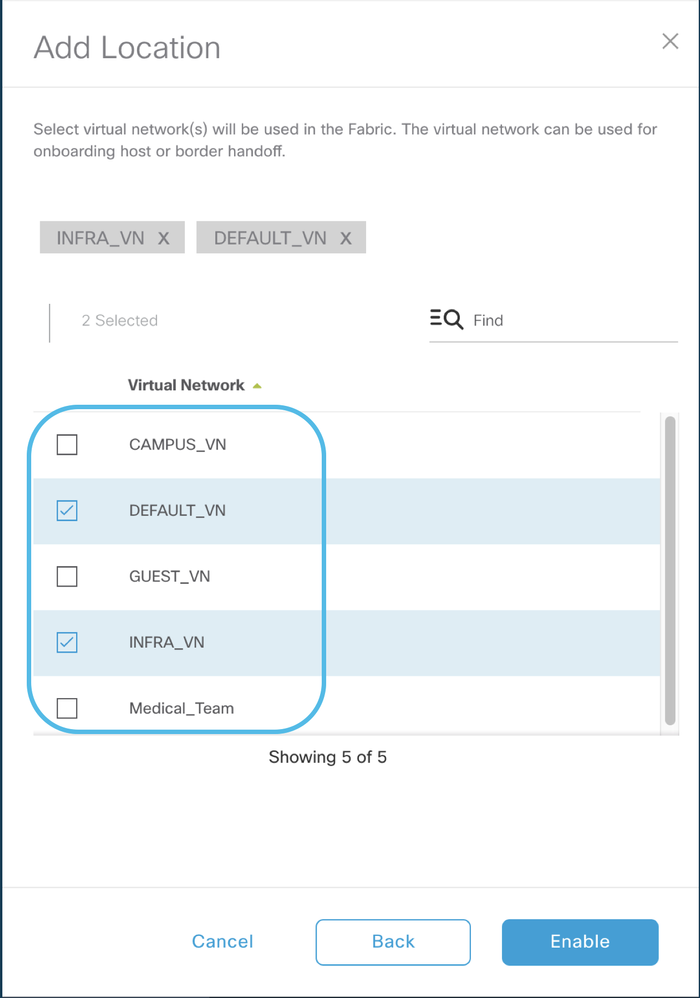
Step4: Select the CAMPUS_VN and GUEST_VN in addition to the default ones shown above for the new Fabric Site and select Enable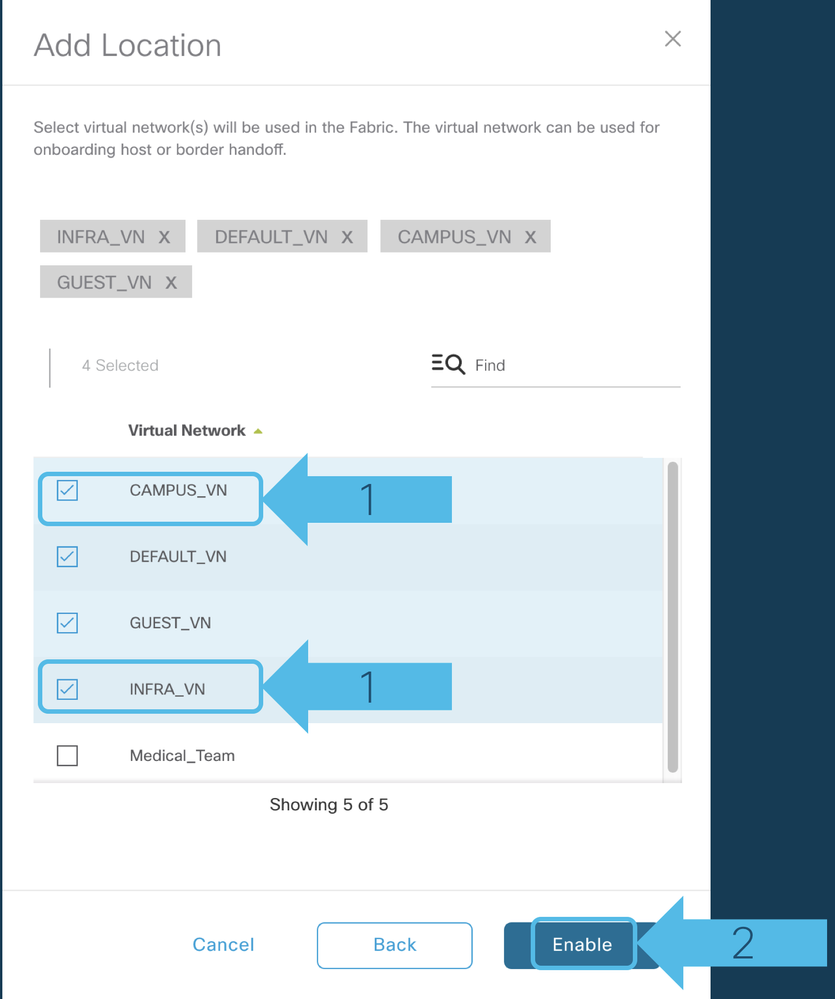
Step5a: There will be a new Fabric Site appearing under "Fabric Enabled Site";
Step5b: Then click on the new Fabric site on the extreme left side as shown below to start provisioning the devices into the Fabric
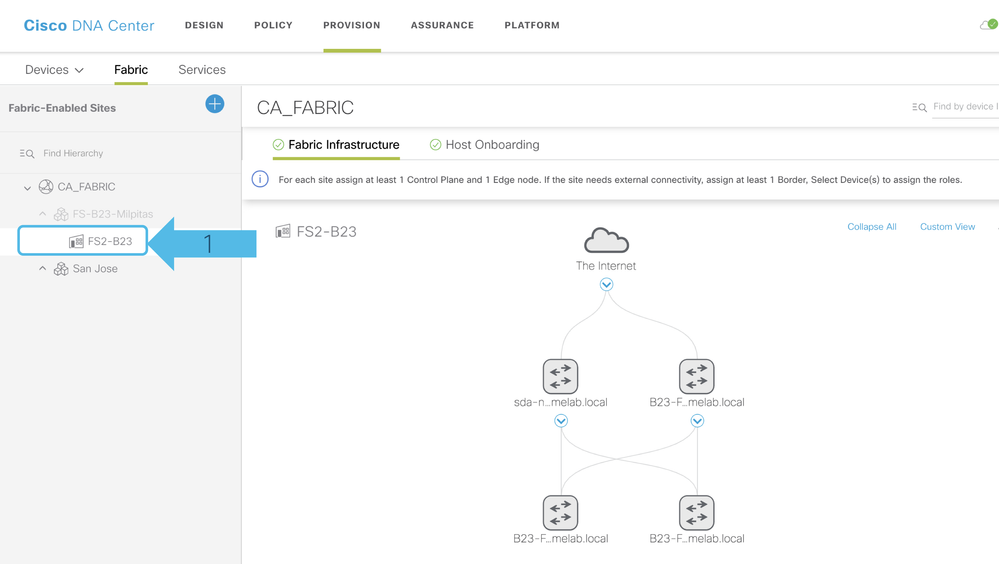
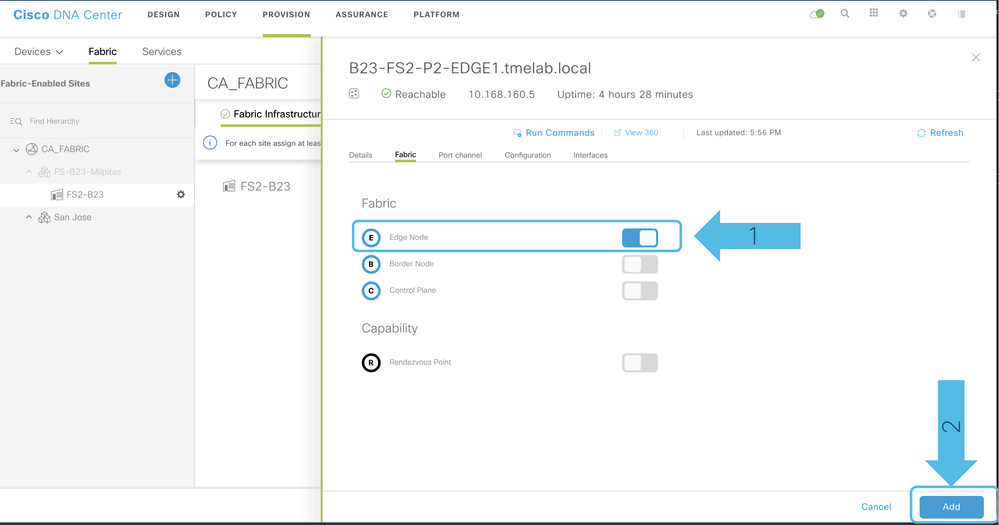
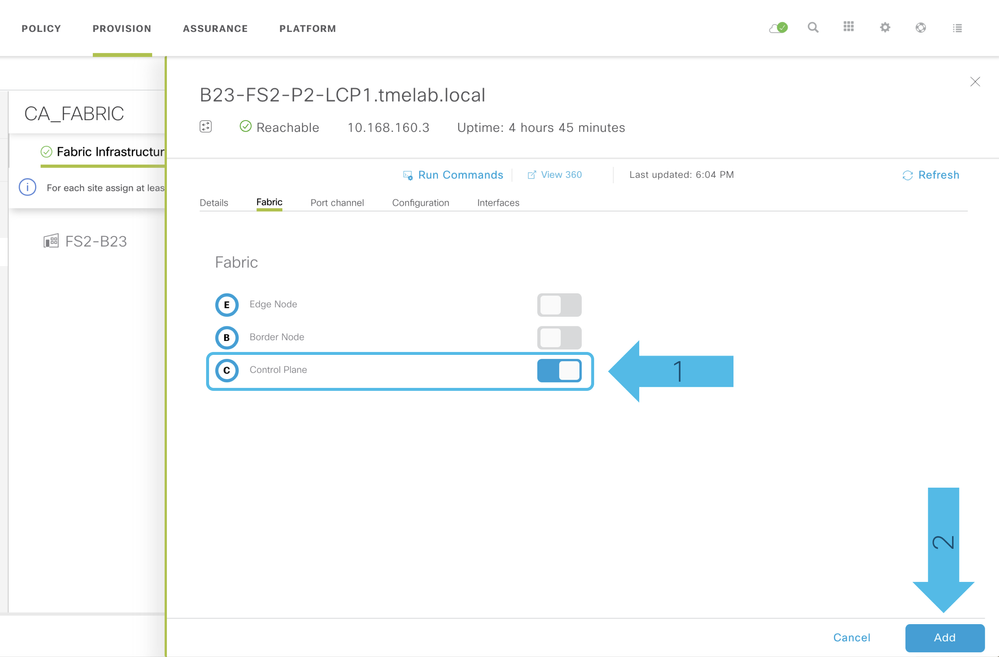
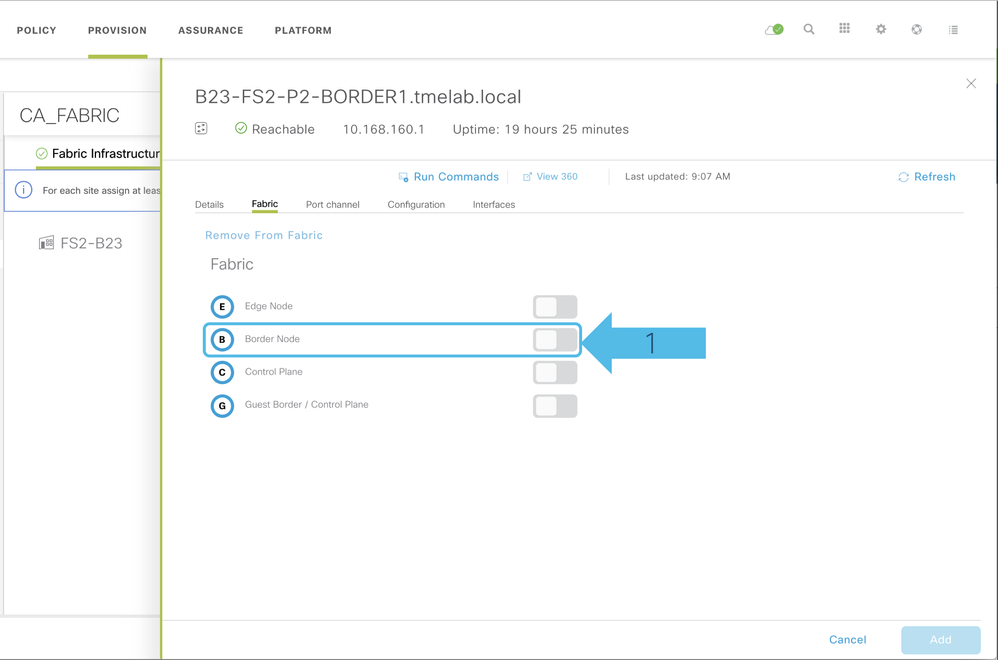
Step6a: Click on the Nodes and a pop up will appear to your right and select the Fabric Roles
Step6b: Enable Fabric Edge Role and click at the bottom option Add
Step6c: Enable Control Plane Node Role
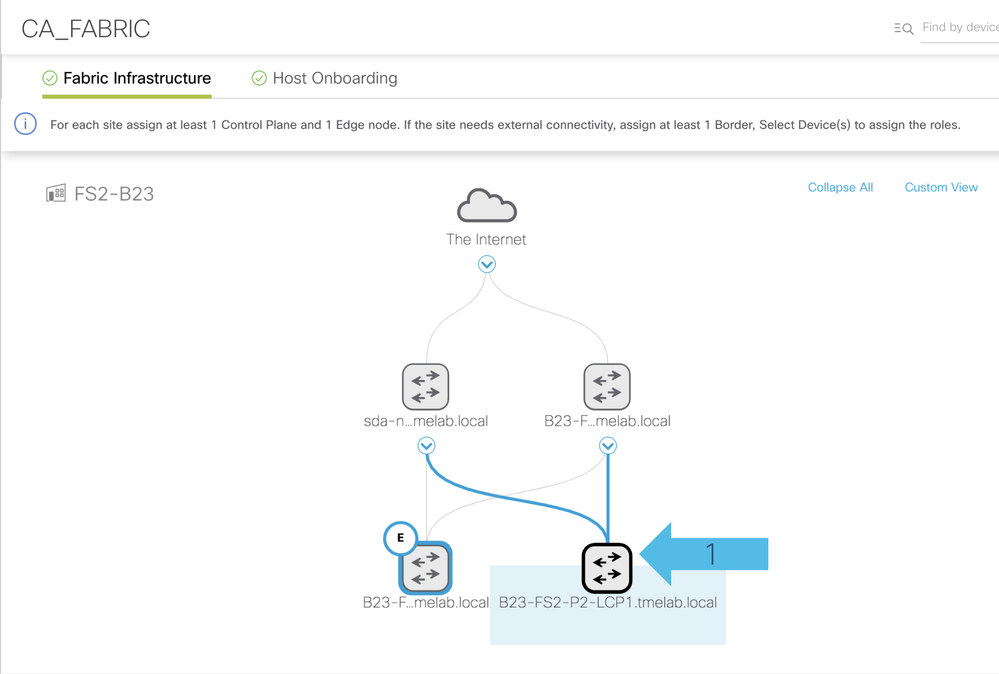
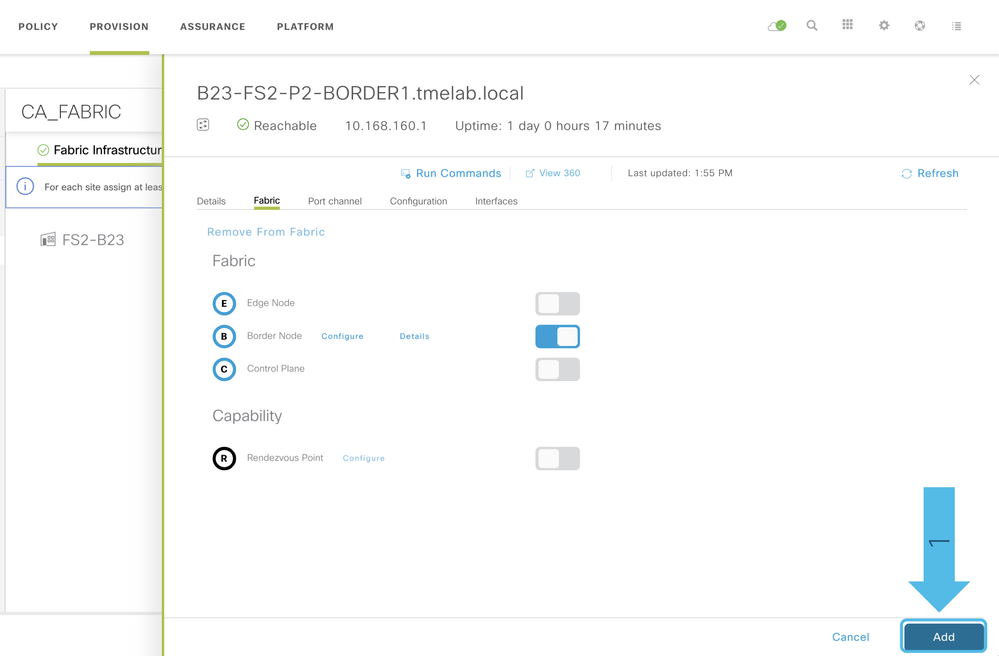
Step6d: Enable Fabric Border Role; Click on the Border as highlighted below

Step6e: Then, you would be presented with a pop-up and click on the Border tab which would give another screen

Step7a: Next step is to complete connectivity to the peer / external network. Fill out the BGP AS number, select the Border Pool (Dropdown list will be showing all the IP pools associated with this Fabric Site).
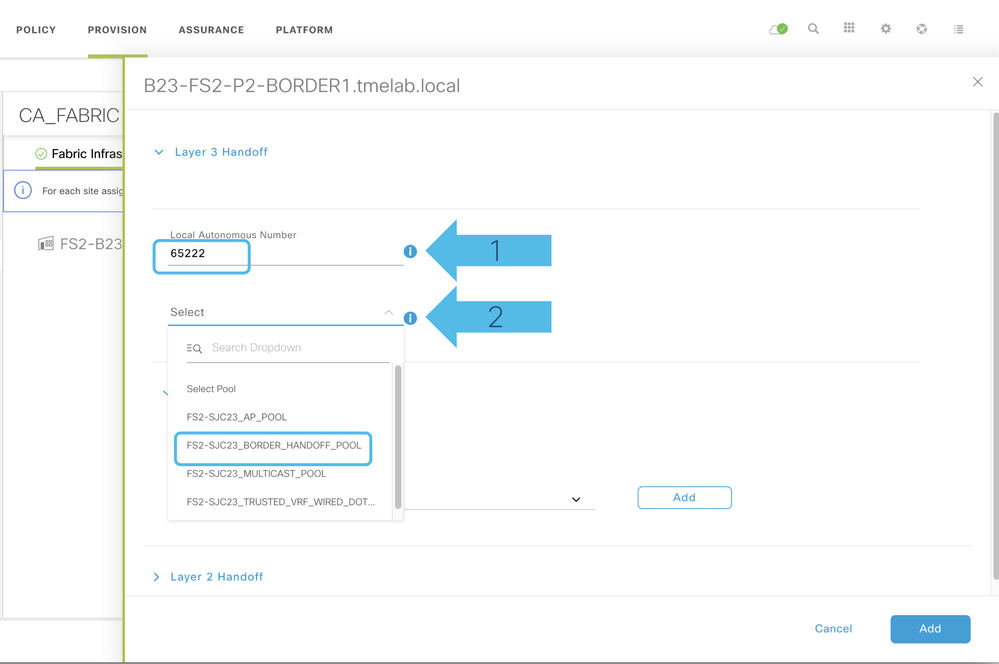
Step7b: Select the Border option and Transit type as shown below
For more information about Border Roles refer to this article https://community.cisco.com/t5/networking-documents/guide-to-choosing-sda-border-roles-in-cisco-dnac-1-3/ta-p/3889472
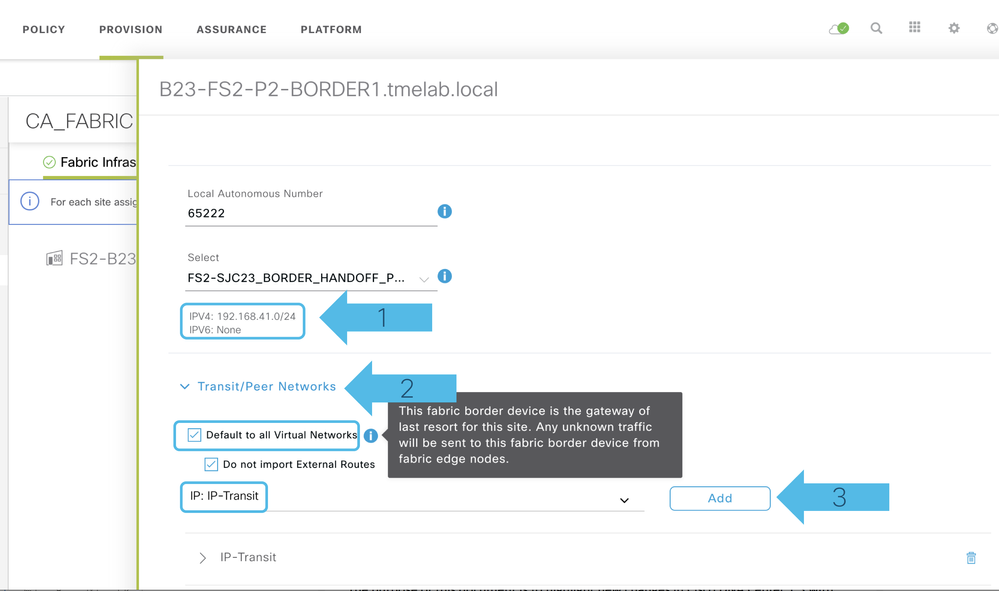
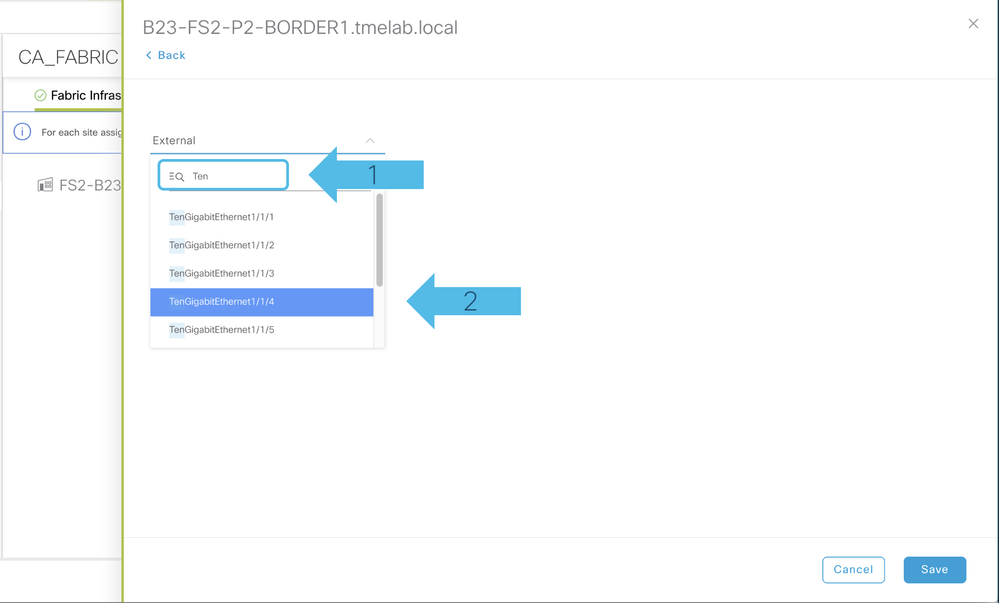
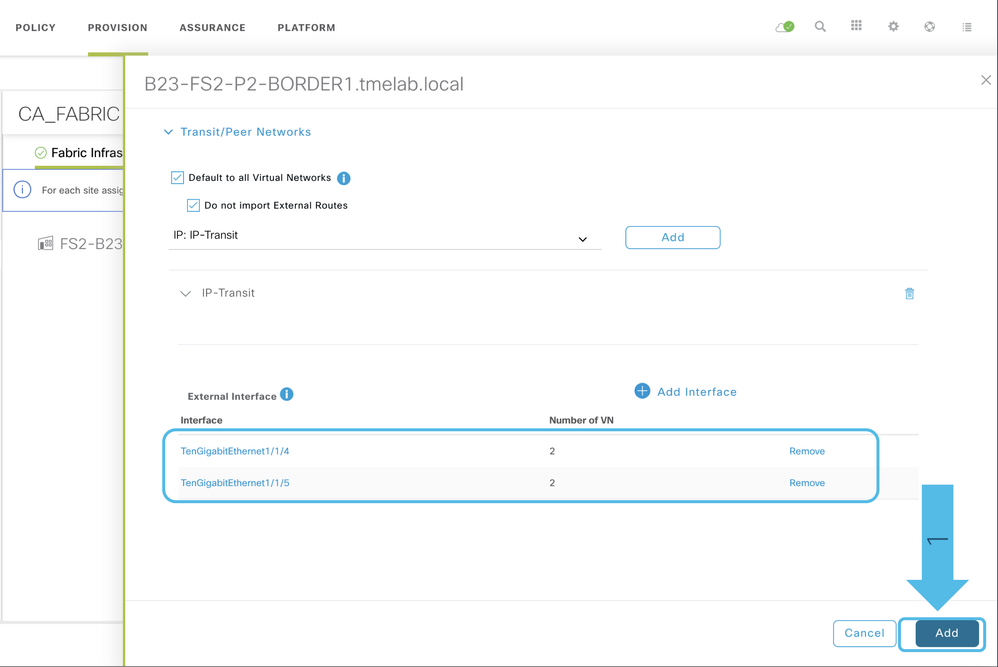
Step7c: Expand the IP-Transit option and select the external interfaces for Border Handoff to Peer Network

Step7d: Once you select the Add Interface option above, search for the external interface Te1/1/4 and click on Save
Step7e: Select the VNs for Border Handoff and then click Save, repeat the same procedure for additional interfaces
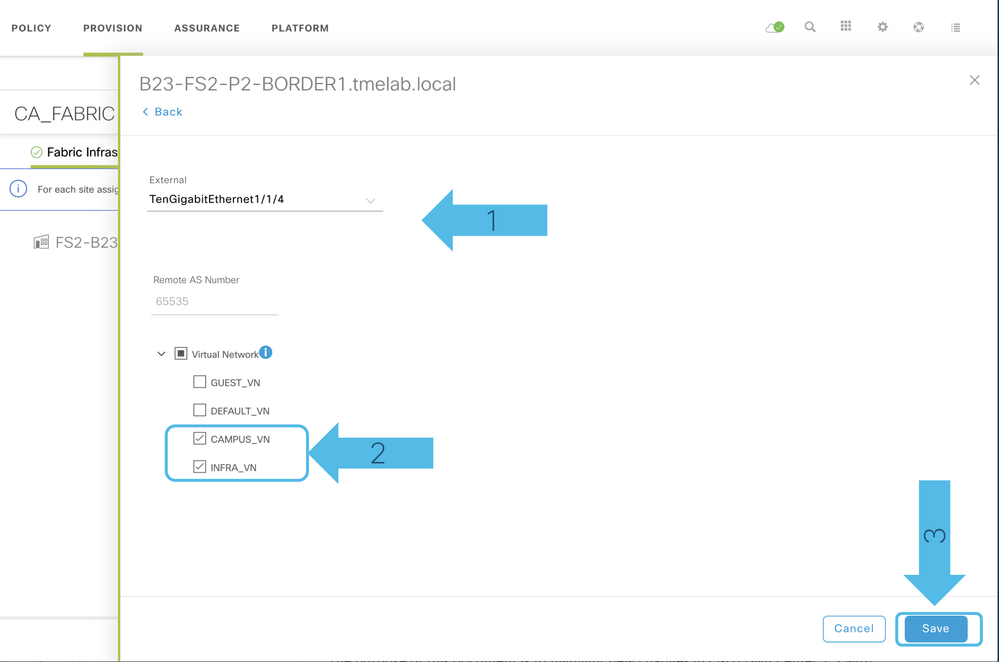
Step7f: Click on Add and then you will be going to the original screen and then click again Add
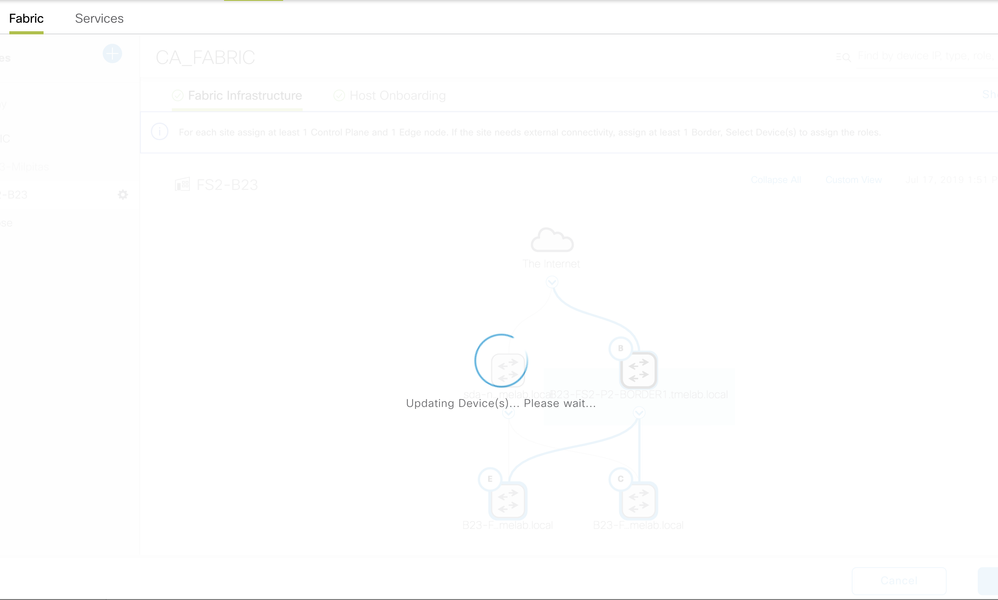
Step7g: Click on Save and then Apply. You would see the below screens while the switches are provisioned into the SD-Access Fabric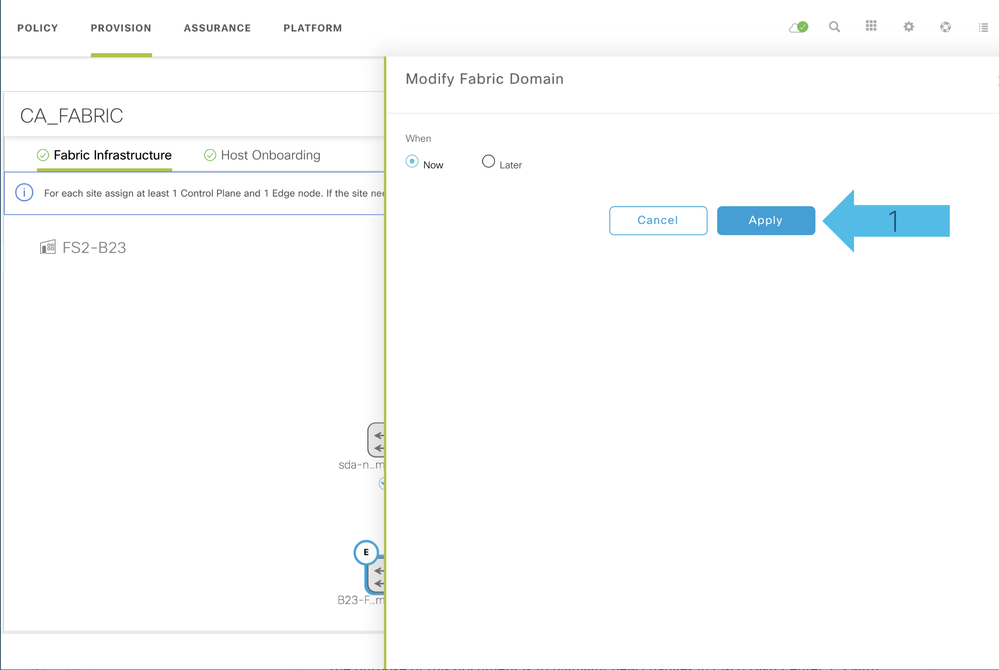
This completes the Fabric Provisioning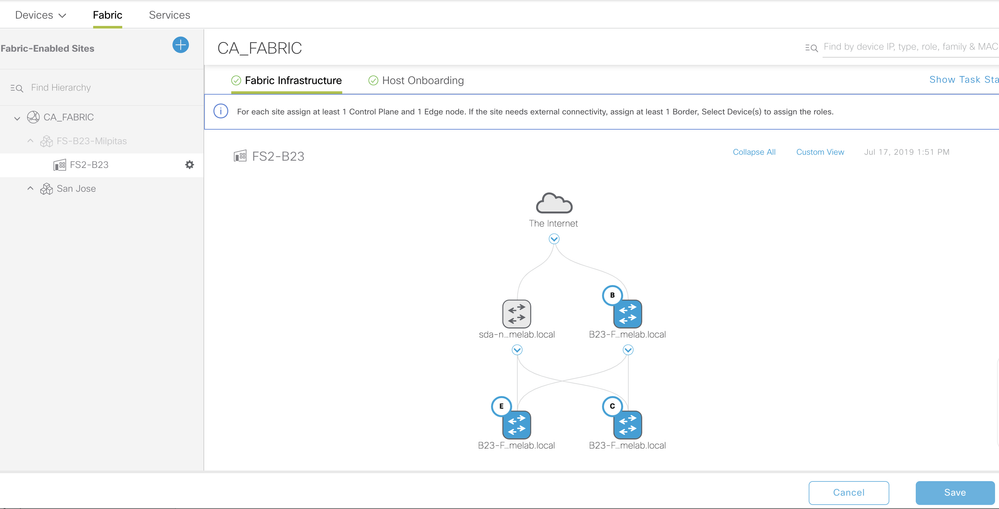
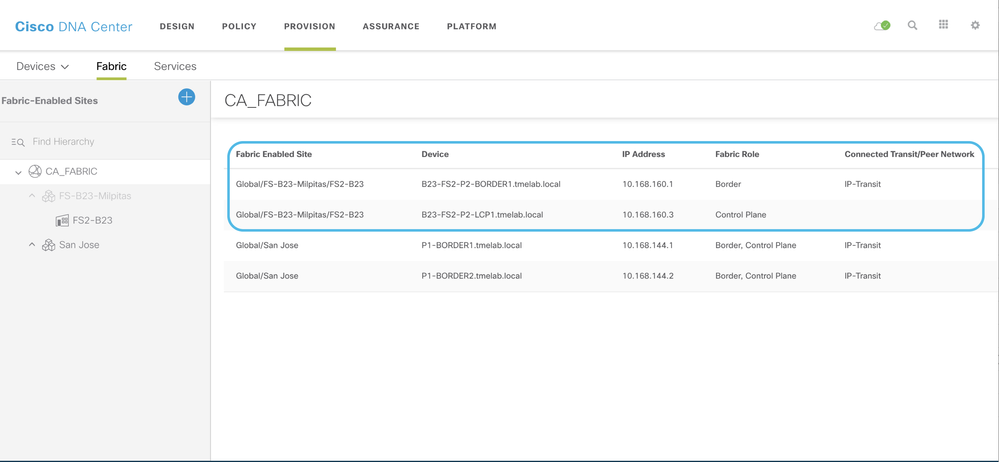
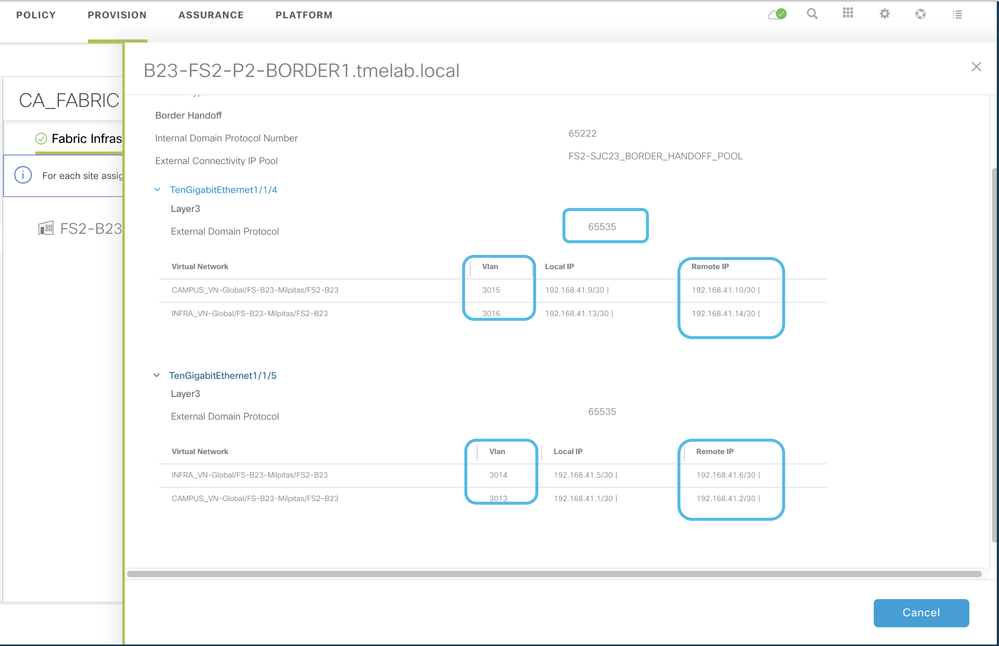
Repeat this procedure on the other Border as well and complete the configuration on the peer Network Devices to enable end-to-end Network Connectivity. Click on Border details to see the Vlans and IP addresses needed on the peer Network Devices.
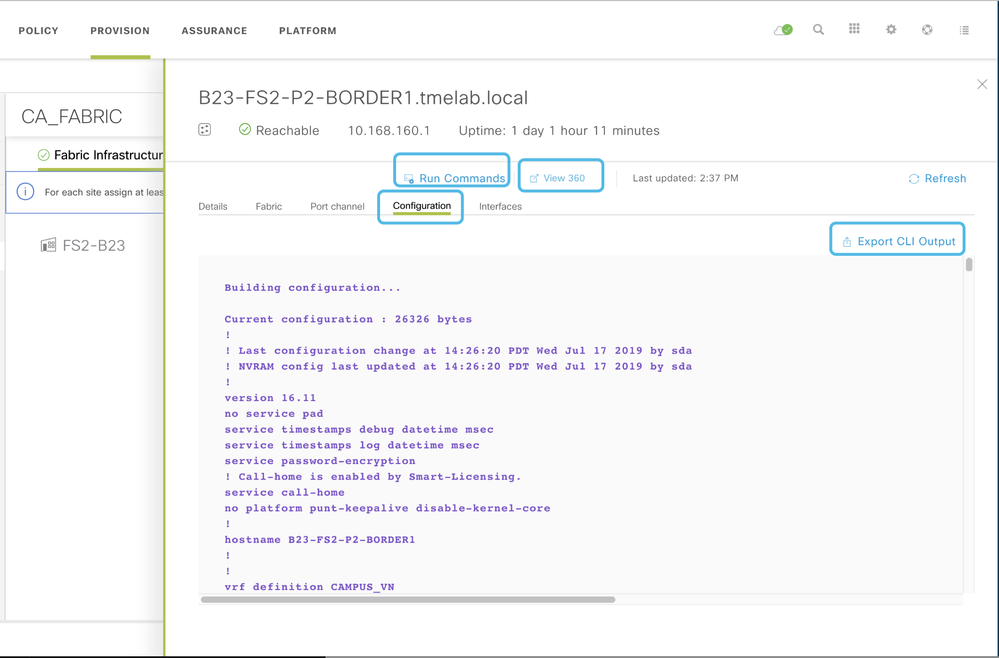
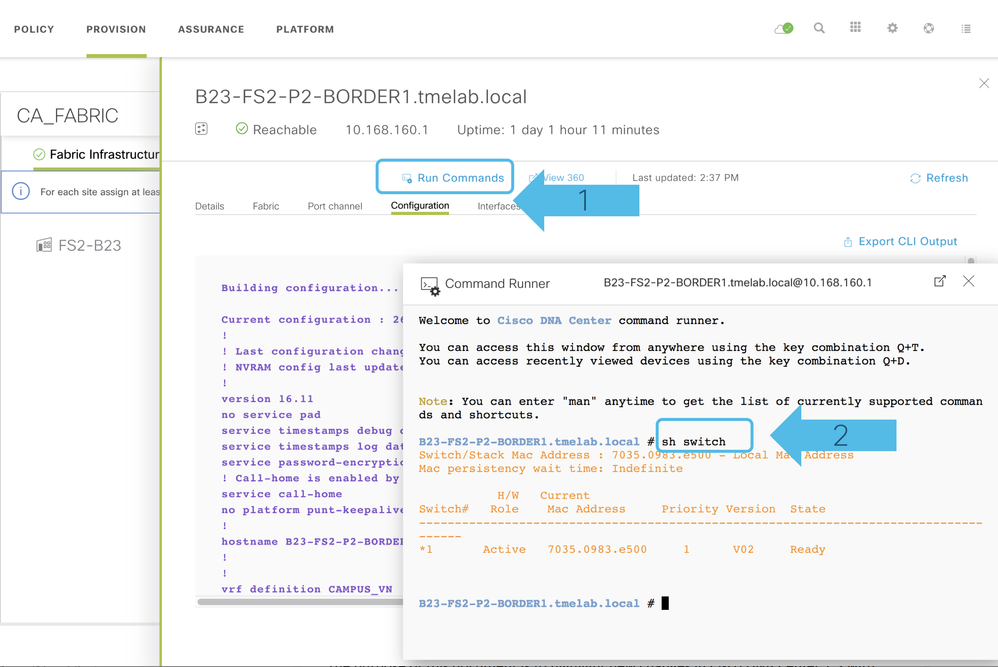
To Look for Configuration and to Run Commands, go to Device360 and to Export CLI Output ... all is merged now in the Provision Fabric page ... when you click on the Fabric Nodes you will have all those above options. See below
What else?
There are many more cool features with Cisco DNA Center 1.3!!! Start exploring your journey towards SD-Access!