- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- How To Cisco DNA Center ISE Integration
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on
07-28-2019
04:45 AM
- edited on
03-20-2023
02:16 PM
by
thomas
![]()
Introduction
Whether you’re beginning your SD-Access journey or are in the process, it's critical to understand the various components that make up the SD-Access solution: Design, Provision, Policy, and Assurance.
Its important to understand that Identity Services Engine (ISE) is a key component with in Cisco DNA Center providing Intent Services like:
- AAA (RADIUS and TACACS+)
- Visibility
- Onboarding
- Security
- Macro and Micro Segmentation
To leverage these services we need to perform Cisco DNA Center ISE Integration to establish trust between the two entities and in the following guide we will provide the steps.
Requirements
For the Cisco DNAC and ISE compatibility versions, see SD-Access Product Compatibility.
Prerequisites
There are 3 main services that need to be enabled and running in order to complete a successful Integrations:
- SSH
- pxGrid
- ERS APIs
Just before you begin check to make sure ISE and Cisco DNA Center can ping each other, This may sound trivial, but many times is overseen and can save some headaches.
SSH
SSH enables the exchange of certificates to establish a trust relationship between ISE and Cisco DNA Center.
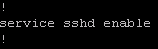
- Verify that SSH is enabled on ISE.
The following entry can be seen on the CLI
Note: Both CLI and GUI Account must have identical passwords.
Validate by performing SSH from Cisco DNA Center to ISE , as well use the same username and password to access ISE GUI ( http://<ISE-Node> )
ERS API
Various ERS API calls are used for the following:
- Certification exchange
- Cisco DNA Center requires knowledge of the ISE deployment infrastructure in order to subscribe to the pxGrid Persona
- pxGrid - subscription to ISE publisher to retrieve contextual date and SGTs
- Update ISE with Cisco DNA Center Orchestrated Group Based Policies (SGTs,Contracts)
In ISE, navigate to Administration > System > Settings > ERS Settings and verify the "Enable ERS for Read/Write" check box is marked.
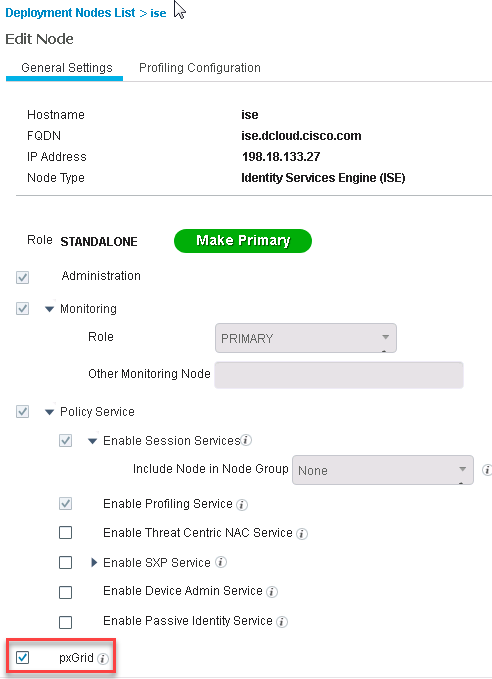
pxGrid
Cisco DNA Center will subscribe to the pxGrid publisher in order to retrieve contextual data as well as the SGTs.When integration is complete the Scalable Groups on the Policy Dashboard in Cisco DNA Center will be updated reflecting the existing list of SGTs on ISE.
Navigate to Administration > System > Deployment and click the node on the right hand side.
Deployment Steps
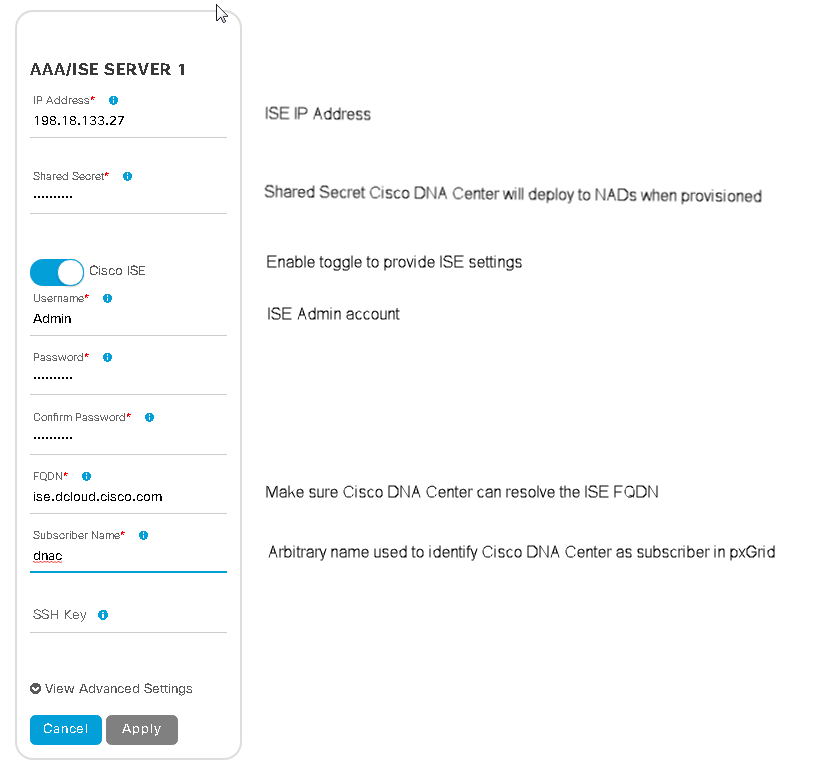
- Navigate on Cisco DNA Center dashboard to the top right and click on the cog icon
and select "System Settings"
- Select "Settings" tab and choose "Authentication and Policy Servers"
- Click on the plus icon
and enter the ISE settings
Once complete click "Apply"
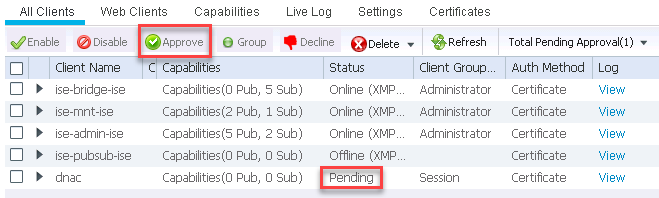
Note: To complete the integration process you may need to log onto your ISE instance and navigate to Administration > pxGrid Services to approve "dnac" Subscriber at which stage the "Pending" Status will change to "Online".
When Integration is completed you will notice on the Cisco DNA Center Policy Dashboard that the "Scalable Groups" value has incremented to the value of the number of SGTs currently on your ISE deployment (the value was null before the integration).What you are witnessing is Cisco DNA Center retrieving the ISE SGTs over API call.
As a sanity check, create an SGT on ISE and see how it increments on the Cisco DNA Center Policy dashboard.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
I had a backend bag problem with my DNAC. After long work by TAC developers, the problem is solved but now DNAC ISE PxGrid integration is down. I tried to delete and add ISE in DNAC again, but it did not allowed me. What is procedure for such cases as mine?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Will I need Cisco DNA premier for intergration with ISE?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi community,
My question is the requirement for PxGrid way to get ISE and Cisco DNA to connect is
Note: The recommended ISE version is 2.3, patch 5 or ISE 2.4 patch 5.
But , my ISE is 2.2 path 9.
So, what is the procedure to get ISE and DNA to connect.
Regards,
Parag
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Please post your queries on our community site:
https://community.cisco.com/t5/software-defined-access-sd/bd-p/discussions-sd-access
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
The answer is no, you do not need DNA Center Premier to integrate ISE. To answer the question posted by Patrick McHenry, which is:
Will I need Cisco DNA premier for intergration with ISE?
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: