- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- Two-Factor Authentication for Cisco Digital Network Architecture (Cisco DNA) center Using Cisco ACS
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on
06-18-2019
11:54 AM
- edited on
06-18-2019
03:46 PM
by
thomas
![]()
Contents
Introduction
This Document shows how we can set up 2 Factor authentication using RSA SecurID token with one time token based on a PIN to login to the Cisco DNAC Web interface.
Two factor authentication provides two or more authentication factors to gain access into a secured system. This also increases security by requiring a pin and use a device we have such as laptop ,mobile ,hardware .By using One-time password which is only valid for one login session, we overcome organizational security concerns of using only a static password.
The 2-factor authentication is supported only for Cisco DNAC configured to authenticate the user against an external authentication server over RADIUS protocol.
Cisco ACS supports the RSA SecurID server as external database and RSA SecurID two-factor authentication consists of users PIN and individually registered RSA SecurID token that generates single use token codes.
RSA server validates this code and each RSA SecurID token is unique . When the correct token code is supplied together with a PIN, user is authenticated and thus RSA SecurID servers provide reliable authentication mechanism compared to already set passwords
Prerequisite
- Cisco DNAC Appliance
- An authentication server such as ACS, ISE, or other RADIUS servers that is able to return cisco-av-pairs to convey the RBAC role authorization of the authenticated Cisco DNAC users
- A 2-factor token server such as RSA Secure ID that can function as backend of ACS/ISE or support the RADIUS protocol above.
- Token card or RSA Secur ID application on client PC/Mac that generates the login token
Devices Used
- Cisco DNAC
- Cisco Secure Access Control System (ACS) 5.8
- RSA SecurID Token Server ( RSA Authentication Manager-7.2 )
- RSA SecurID Token Client
Configuration
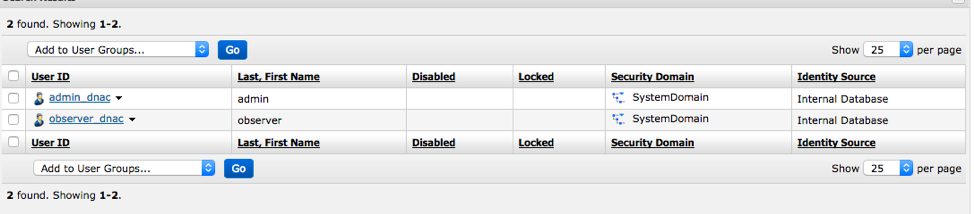
We created two users in RSA SecurID AM as admin_dnac and observer_dnac
First Integrate RSA- Authentication manager with Cisco ACS
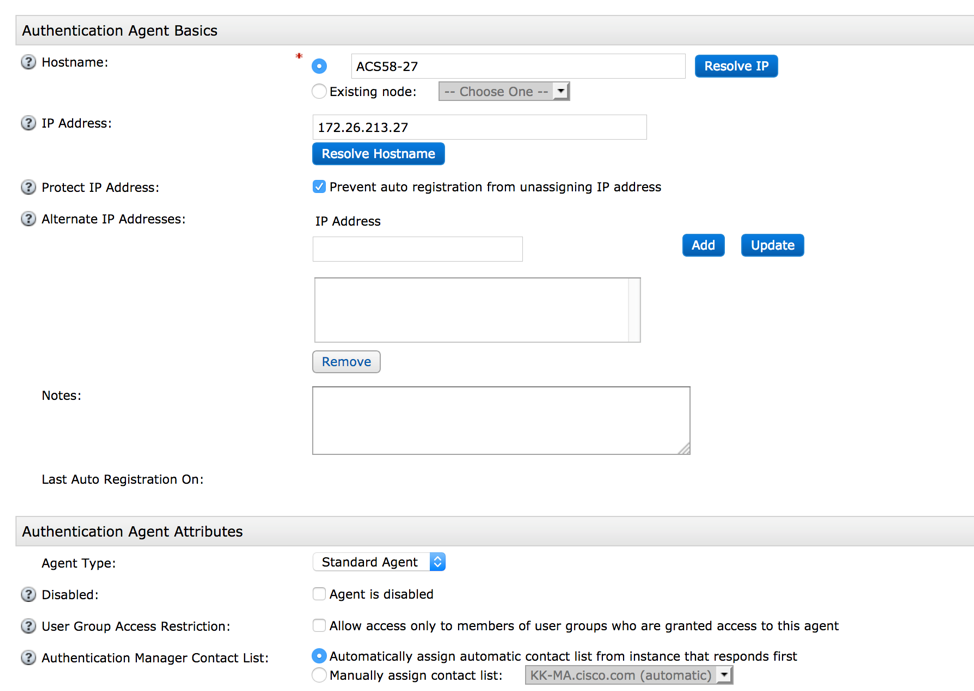
Create a new Authentication Agent pointing to Cisco ACS with its details.
This is done under Access > Authentication Agents > Add New:
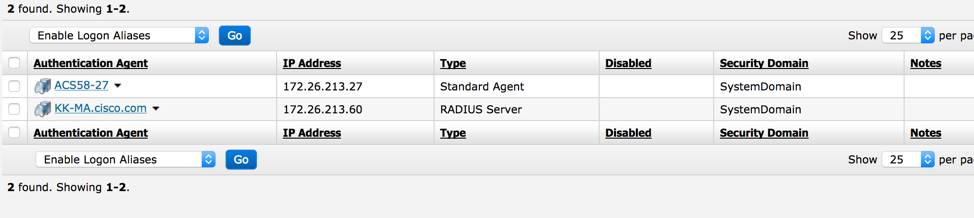
After you added, it shows up like this
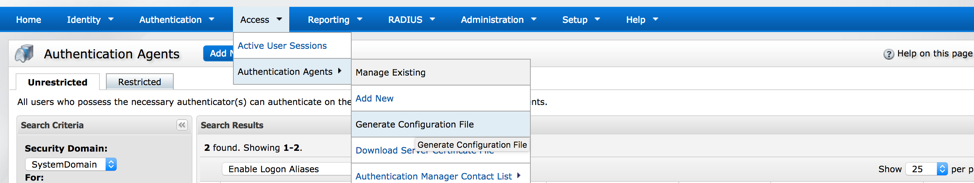
Now from , RSA Security Console, navigate to Access > Authentication Agents > Generate Configuration File in order to generate the sdconf.rec configuration file:
Use the default values for Maximum Retries and Maximum Time Between Each Retry:
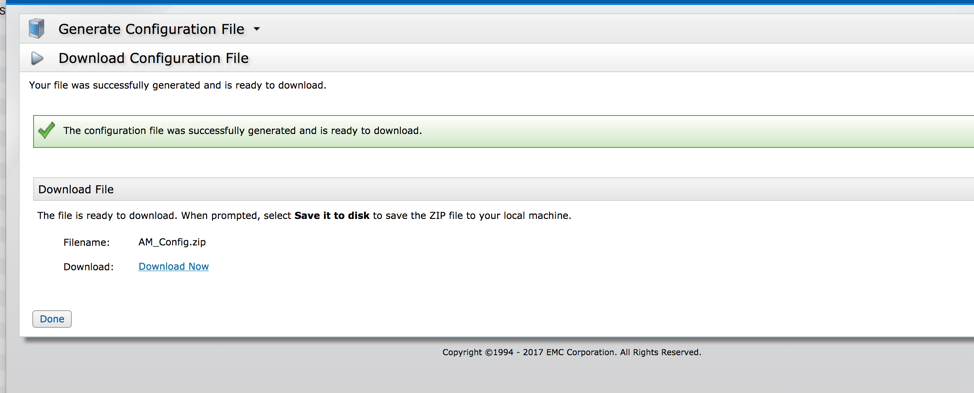
Download the configuration File
The .zip file contains the actual configuration sdconf.rec file, which the ACS administrator needs in order to complete configuration tasks.
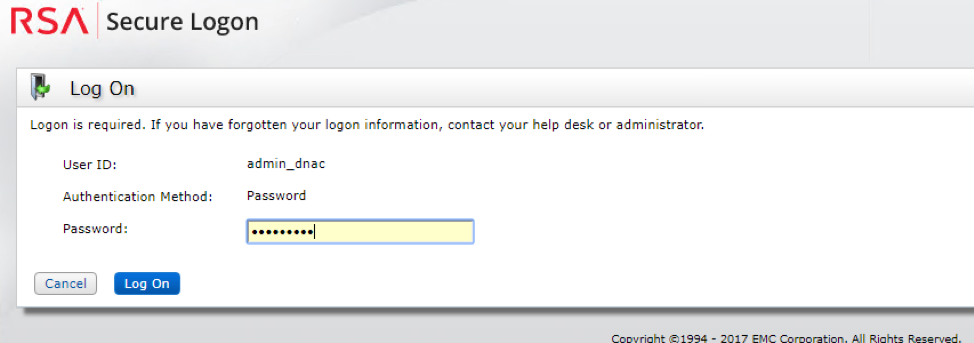
As a first part of authentication, we have to generate PIN for each username in RSA-AM
Log into the RSA-AM Console-self service using
Screenshot below , we logged in as admin_dnac and there we will have the option to set/change PIN for each username.
Now Go to the Cisco ACS Server
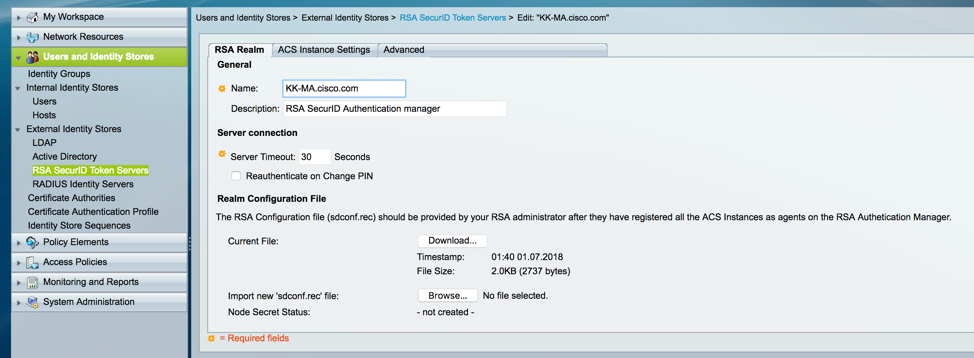
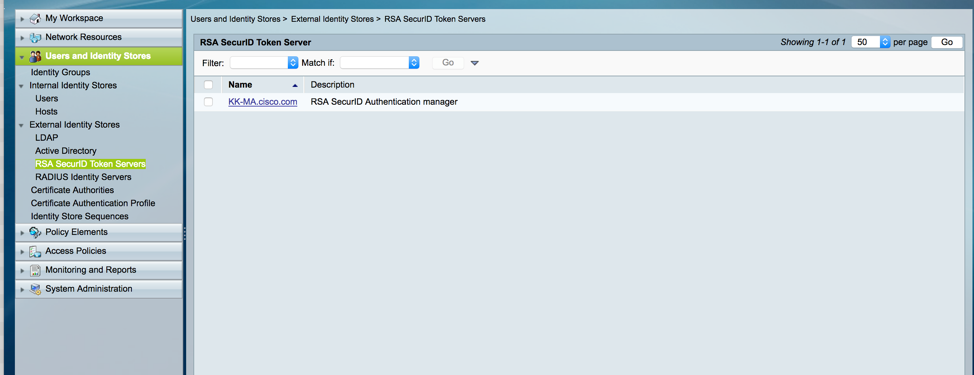
In the Cisco Secure ACS Version 5.x console, navigate to Users and Identity Stores > External Identity Stores > RSA SecurID Token Servers, and click Create:
Enter the name of the RSA server, and browse to the sdconf.rec file that was downloaded from the RSA server:
Which shows up like this
Now the Cisco ACS and RSA – AM are successfully integrated
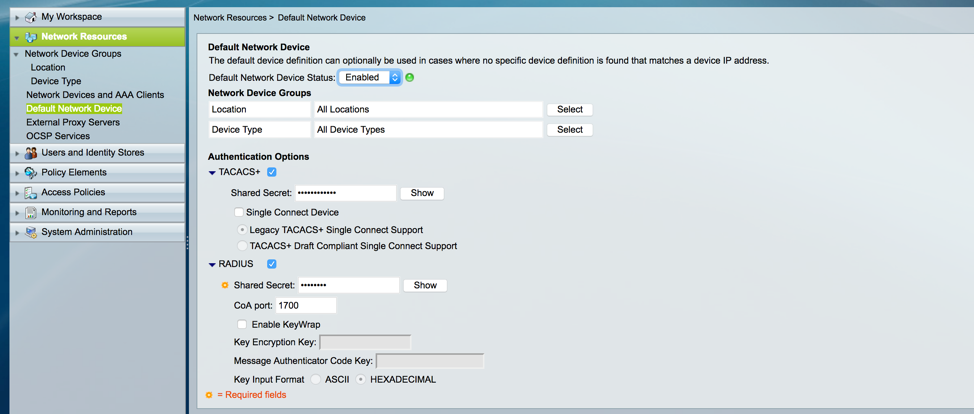
Now Make sure you have a Shared Secret for RADIUS Under Network Resources > Default network Device
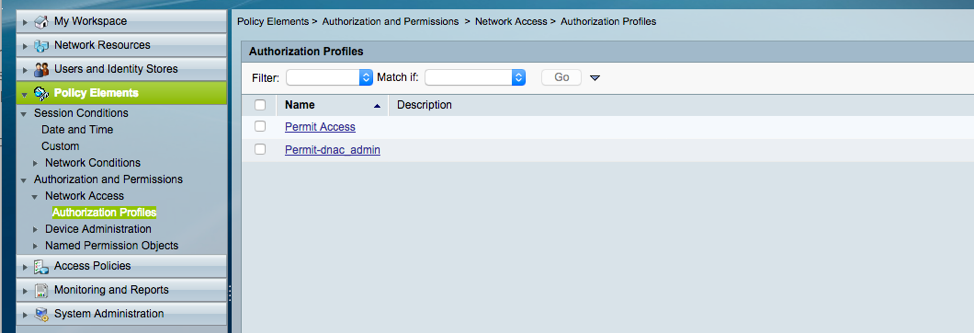
Now, Create a Authorization Profile under Policy Elements > Authorization and Permissions > Network Access > Authorization Profiles
Create a Profile
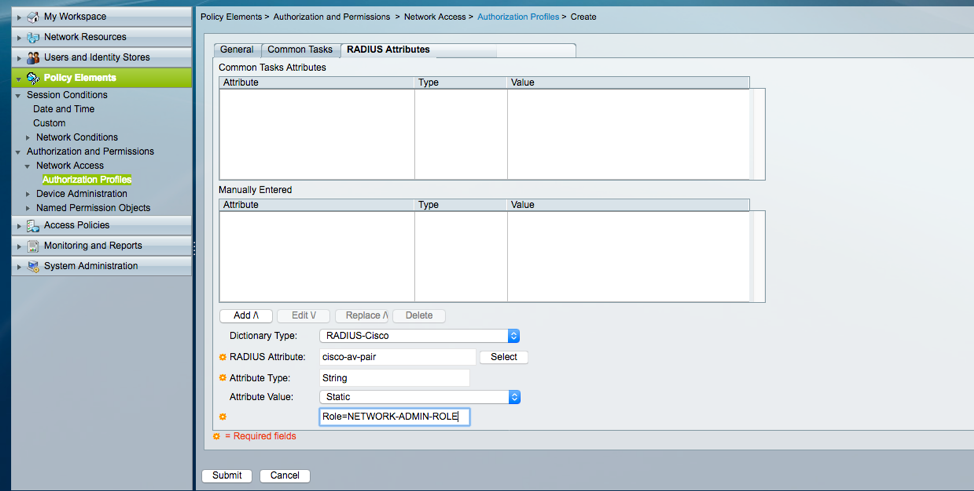
Edit this profile in such a way that it returns cisco-av-pair with role NETWORK-ADMIN-ROLE
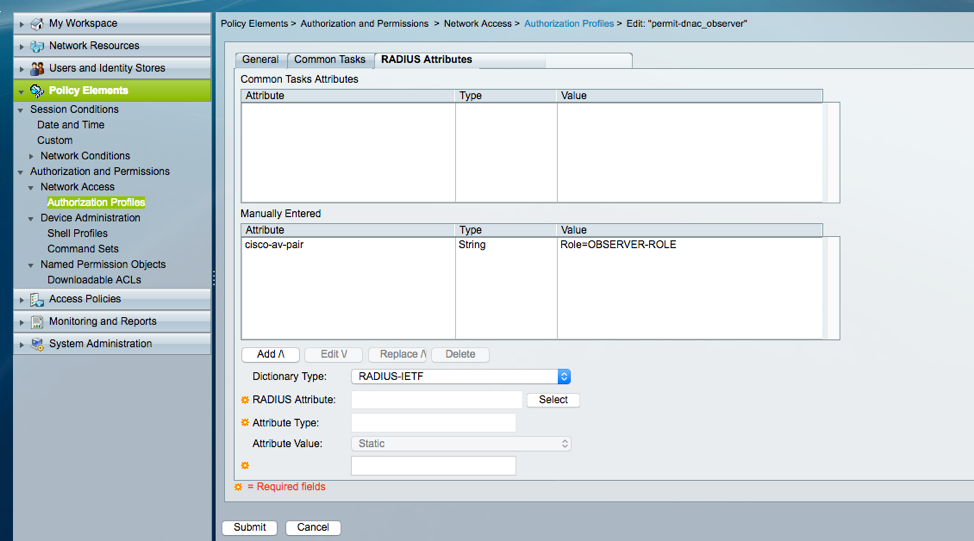
Create similarly for Observer as well
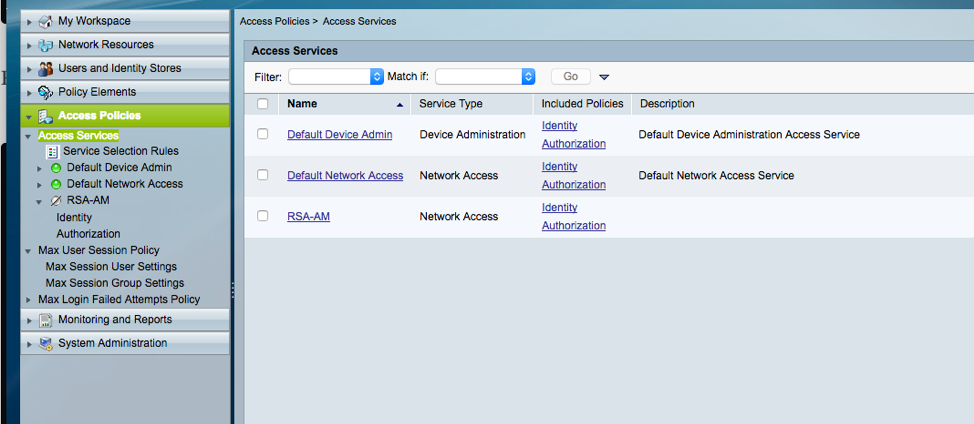
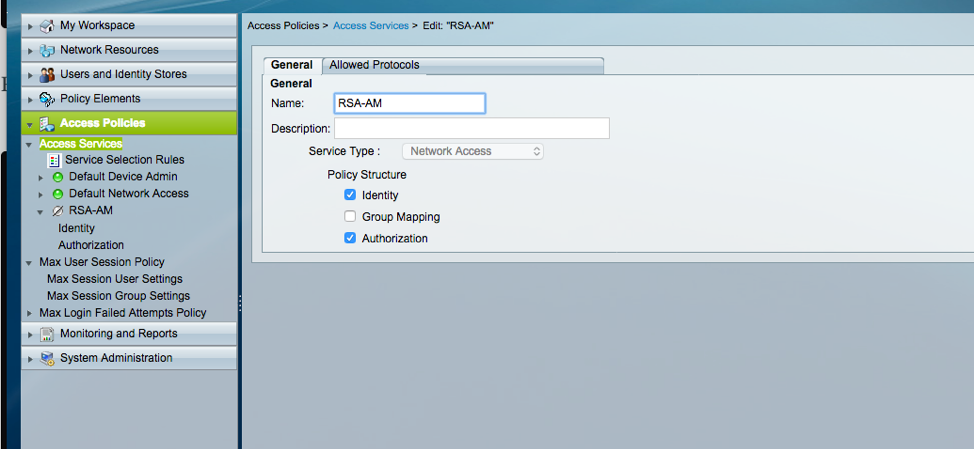
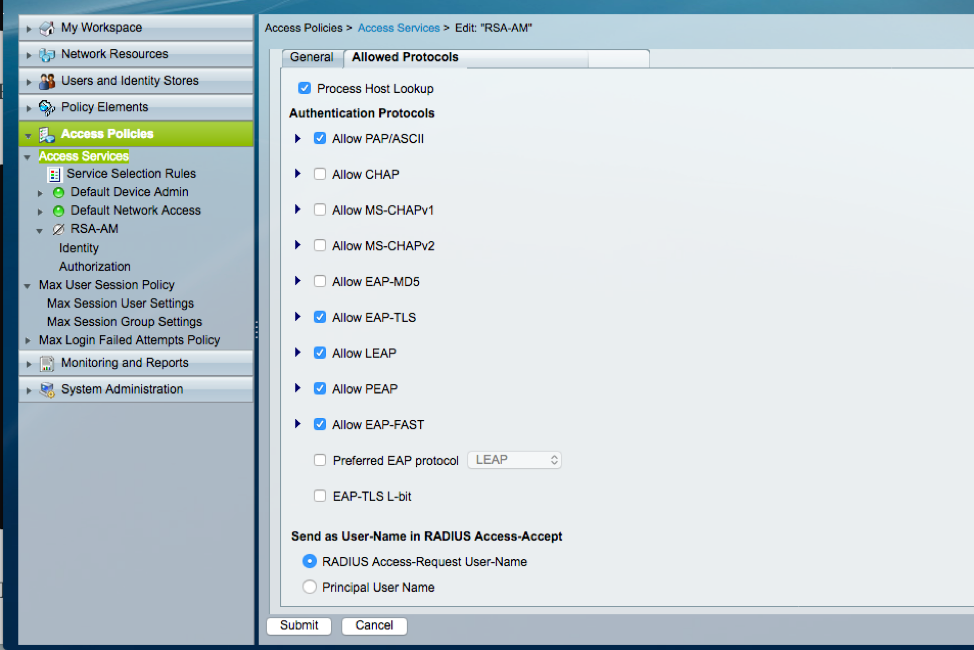
Create Access Service
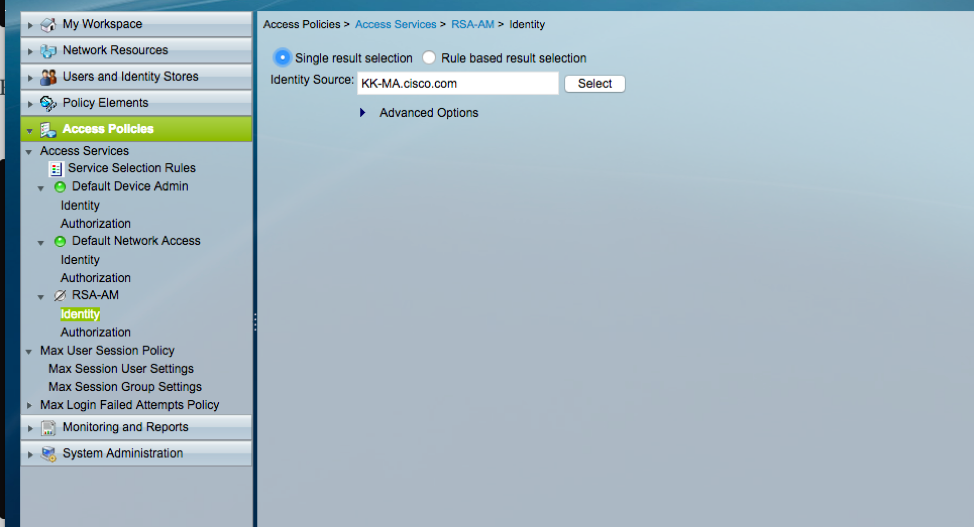
Add RSA- AM as Identity
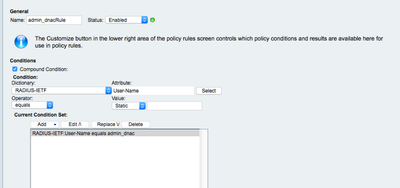
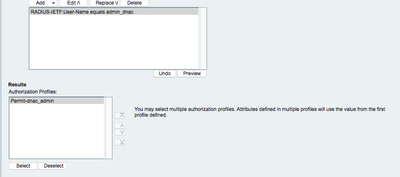
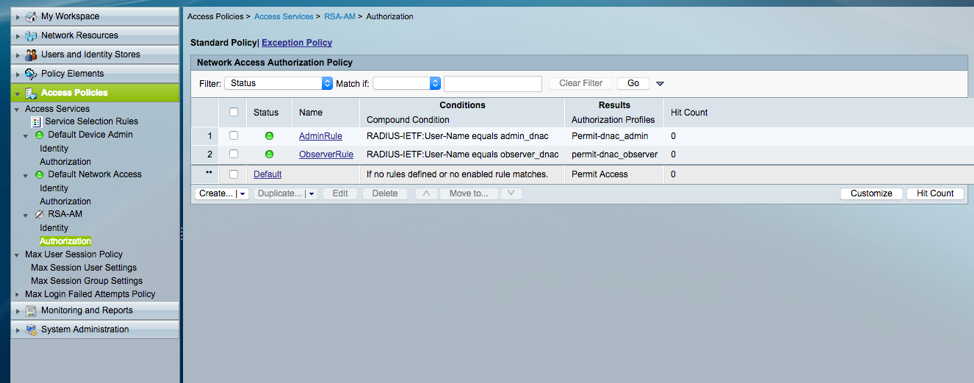
On ACS, create authorization policy rule to return the Authorization Profile corresponds to the different users or user group. In this paper our rule is based on the User-Name as an illustration.
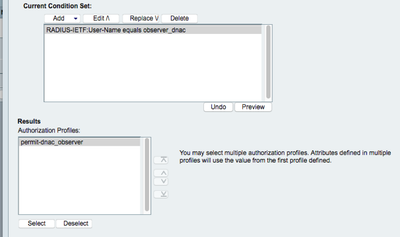
The AdminRule match the admin_dnac and returns the admin authorization, and the ObserverRule match the observer_dnac and returns the read only authorization.
After Creating, it looks like this
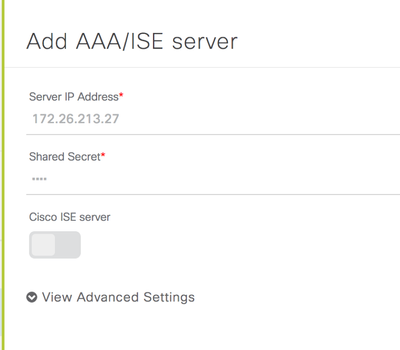
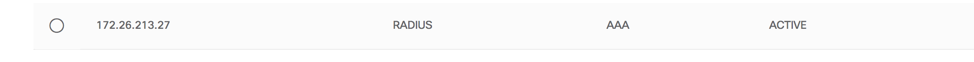
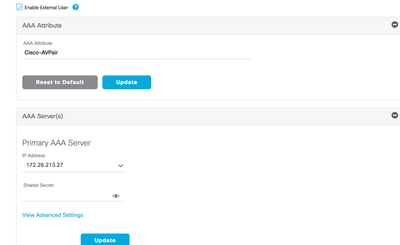
Once the profiles are created, make sure you have tokens for each users under RSA Security Console. Then, Integrate ACS into Cisco DNAC under Settings > Authentication and Policy Servers and enable External Authentication under Settings > Users > External Authentication and point to ACS Server.
Once the Integration is done, register the RSA Token with RSA token server, this ensures that only user in procession of the token is able to use token
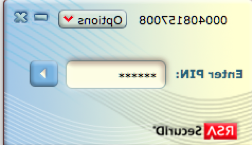
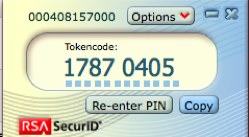
Open the RSA SecurID Token client and enter the pre-set PIN in the RSA SecurID Token client as a first factor of authentication
Which in turn gives you one time token as below which you enter while authentication with the username
Enter the username and one time token on the Cisco DNAC login page. User passed authentication is allowed access.
This is how 2 factor authentication is achieved with a combination of PIN + One time token.
Authentication Workflow
- User generates PIN using RSA SecurID client to get RSA SecureID token
- On the Cisco DNAC Login page user enters username and RSA SecureID token
- Cisco DNAC will send the username/Passcode request to ACS over RADIUS Protocol
- ACS in turn sends it to the RSA AM
- RSA AM sends it to acs that authentication is successful
- ACS matches the authenticated user to the configured authorization profile
- ACS returns the cisco-av-pair with role=NETWORK-ADMIN-ROLE of the authorization profile
- Cisco DNAC use the RBAC role to give the user access to relevant features and pages
Verification
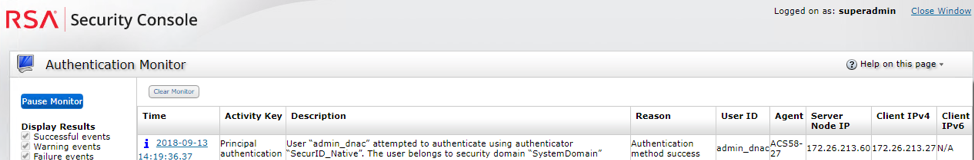
We can verify the login from the live logs from Cisco ACS and RSA-AM
- On RSA-AM Authentication Monitor Dashboard, we can see that dnac_admin was able to successfully log in
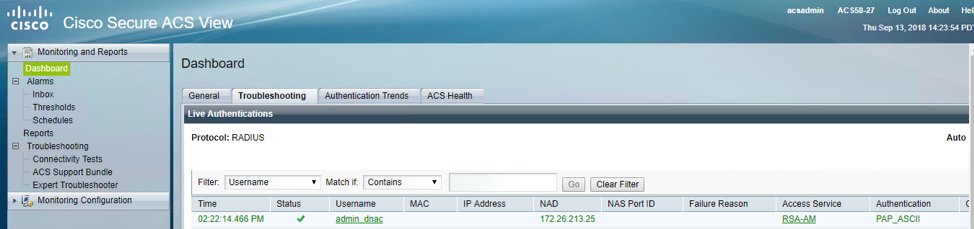
- Under ACS Monitoring and Reports > Launch Monitoring and Report Viewer
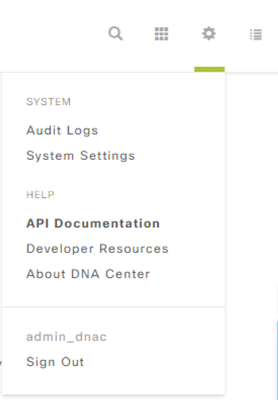
- We can also see that we were able to successfully log in to the Cisco DNAC via admin_dnac
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: