- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
06-09-2009 03:47 AM - edited 03-08-2019 05:58 PM
Introduction
What are Access Control Lists?
ACLs are a network filter utilized by routers and some switches to permit and restrict data flows into and out of network interfaces. When an ACL is configured on an interface, the network device analyzes data passing through the interface, compares it to the criteria described in the ACL, and either permits the data to flow or prohibits it.
Why Do We Use Access Control Lists?
There are a variety of reasons we use ACLs. The primary reason is to provide a basic level of security for the network. ACLs are not as complex and in depth of protection as stateful firewalls, but they do provide protection on higher speed interfaces where line rate speed is important and firewalls may be restrictive. ACLs are also used to restrict updates for routing from network peers and can be instrumental in defining flow control for network traffic.
When do we use Access Control Lists?
As I mentioned before, ACLs for routers are not as complex or robust as stateful firewalls, but they do offer a significant amount of firewall capability. As an IT network or security professional, placement of your defenses is critical to protecting the network, its assets and data. ACLs should be placed on external routers to filter traffic against less desirable networks and known vulnerable protocols.
One of the most common methods in this case is to setup a DMZ, or de-militarized buffer zone in your network. This architecture is normally implemented with two separate network devices.

The most exterior router provides access to all outside network connections. This router usually has less restrictive ACLs, but provides larger protection access blocks to areas of the global routing tables that you wish to restrict. This router should also protect against well known protocols that you absolutely do not plan to allow access into or out of your network. In addition, ACLs here should be configured to restrict network peer access and can be used in conjunction with the routing protocols to restrict updates and the extent of routes received from or sent to network peers.
The DMZ is where most IT professionals place systems which need access from the outside. The most common examples of these are web servers, DNS servers, and remote access or VPN systems.
The internal router of a DMZ contains more restrictive ACLs designed to protect the internal network from more defined threats. ACLs here are often configured with explicit permit and deny statements for specific addresses and protocol services.
What does an Access Control List of?
Regardless of what routing platform you utilize, all have a similar profile for defining an access control list. More advanced lists have more distinct control, but the general guidelines are as follows:
- Access control list name (depending on the router it could be numeric or combination of letters and numbers)
- A sequence number or term name for each entry
- A statement of permission or denial for that entry
- A network protocol and associated function or ports
Examples include IP, IPX, ICMP, TCP, UDP, NETBIOS and many others
- Destination and Source targets
These are typically addresses and can be defined as a single discrete address, a range or subnet, or all addresses
- Additional flags or identifiers
These additional statements request additional functions when a match is found for the statement. These flags vary for each protocol but common flag added to statements is the log feature that records any match to the statement into the router log
Types of Access Control Lists:
There are several types of access control lists and most are defined for a distinct purpose or protocol. On Cisco routers, there are two main types: standard and extended. These two types are the most widely used ACLs and the ones I will focus on in this and future articles, but there are some advanced ACLs as well. Some of the advanced ACLs include reflexive ACLs and dynamic ACLs and they are defined as follows. Reflexive ACLs, also known as IP Session ACLs, are triggered from an outbound ACL for traffic initiated from the internal network. The router will identify this new traffic flow and create an entry in a separate ACL for the inbound path. Once the session ends, the entry in the reflexive ACL is removed.
Dynamic ACLs or lock-and-key ACLs are created to allow user access to a specific source/destination host through a user authentication process. Cisco implementations utilize IOS Firewall capabilities and do not hinder existing security restrictions.
Implementation of ACLs on a Router Interface
Placement and understanding of the traffic flow is important to understand up front before you configure an ACL on a router interface. Understanding of the placement and impact of ACLs are frequent questions in CCNA and CCNP exams and mistakes in ACL placement are some of the most common ones network administrators make during security implementation. Trust me, it happens to us all and I am not immune to that one.
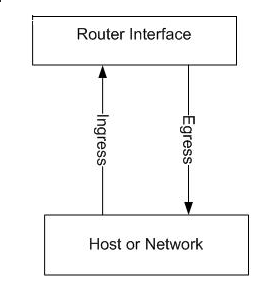
As you can see from this diagram, ingress traffic flows from the network into the interface and egress flows from the interface to the network. IT network and security professionals must pay close attention here. ACLs start with a source address first in their configuration and destination second. As you configure an ACL on the ingress of a network interface it is important to recognize that all local network or hosts should be seen as sources here, and the exact opposite for the egress interface.
What makes this most confusing is the implementation of ACLs on the interface of a router that faces an external network. Look back at Figure 1. In that example, the ingress side is coming from the outside network and those addresses are considered to be sources, while all internal network addresses are destinations. On the egress side, your internal network addresses are now source addresses and the external addresses are now destinations.
As you add ports in extended ACLs, confusion can mount. The best advice I have before any implementation is to document your flows and note your source/destination addresses. We will cover more of these implementations later in ACL configuration articles.
Sample of ACLs:
Numbered access list:
Router(config)# access-list 1 permit 192.168.0.0 0.0.0.255
Router(config)# access-list 1 deny 172.16.0.0 0.0.0.255
Router(config)# access-list 1 permit 10.0.0.0 0.0.0.255
^ source prefix
^ source wildcard mask
Router(config)# access-list 100 permit tcp 192.168.0.0 0.0.0.255 10.0.0.0 0.0.0.255 eq 80
Router(config)# access-list 100 permit udp 192.168.0.0 0.0.0.255 10.0.0.0 0.0.0.255 gt 1023
^ protocol
^ source prefix
^ source wildcard
^ destination prefix
^ destination wildcard
^ protocol specific options
Named access lists:
Router(config)# ip access-list extended FIREWALL-IN
Router(config-acl)# permit tcp 192.168.0.0 0.0.0.255 10.0.0.0 0.0.0.255 eq 80
Router(config-acl)# permit udp 192.168.0.0 0.0.0.255 10.0.0.0 0.0.0.255 gt 1023
Router(config-acl)# deny ip any any log
RFCs
- RFC 1700 - Well known port numbers
- RFC 1918 - Address allocation for private Internets
- RFC 1858 - Security Considerations for IP Fragment Filtering
Also See
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: