- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- ASA Phone Proxy LSC Provisioning without secure USB tokens: Config Example
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
09-09-2010 05:38 PM - edited 03-08-2019 06:36 PM
Introduction
This document is meant to assist with configuring LSC provisioning on an Adaptive Security Appliance (ASA) running the Phone Proxy (PP) feature. It is meant specifically for the 7960 or 7940 phones which do not come with a Manufacturer Installed Certificate (MIC) and need to use a Locally Significant Certificate (LSC) to register securely with PP. This also assumes that you are running a nonsecure Cisco Unified Call Manager (CUCM).
Prerequisites
Familiar with the ASA CLI
Familiar with CUCMs’ management interface
ASA and CUCM clocks are set to the correct time.
Requirements
Ensure that you meet these requirements before you attempt this configuration:
- The phone you are using is able to register on the inside of the ASA.
- CUCM 6.x, 7.x, 8.0.x
- ASA 8.0.4 or later with phone proxy configured.
- Secure USB tokens are NOT required.
Configure
The Steps for configuration are outlined below:
1) Configure CUCM to provision a LSC
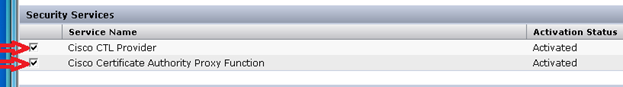
Cisco Unified Serviceability > Tools > Service Activation

Select Cisco CTL Provider
Select Cisco Certificate Authority Proxy Function (CAPF)
2) Copy the CAPF Certificate from the CUCM
Cisco Unified OS Administrator
Security > Certificate Management > Find

Click on CAPF.pem
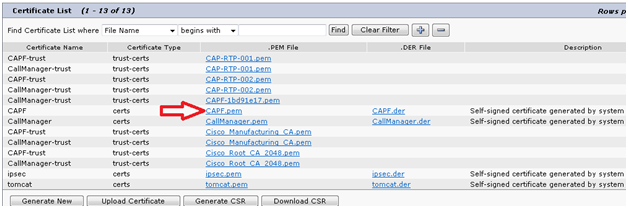
Download the CAPF.pem file

3) Create a trustpoint and import the cert on the ASA
On ASA cli
PhoneProxyASA(config)# crypto ca trustpoint capf_trustpoint
PhoneProxyASA(config-ca-trustpoint)# enrollment terminal
PhoneProxyASA(config-ca-trustpoint)# exit
PhoneProxyASA(config)# cry ca authenticate capf_trustpoint
Enter the base 64 encoded CA certificate.
End with the word "quit" on a line by itself
-----BEGIN CERTIFICATE-----
………………..Certificate Removed…………………….
-----END CERTIFICATE-----
quit
INFO: Certificate has the following attributes:
Fingerprint: 233c8e33 8632ea4e 76d79feb ffb061c6
Do you accept this certificate? [yes/no]: yes
Trustpoint CA certificate accepted.
% Certificate successfully imported
Add an entry in the Cisco Trust List (CTL) file on the ASA
On the ASA cli (note: CTL file cannot be changed while in use.)
PhoneProxyASA(config)# ctl-file ctl_phoneproxy_file
PhoneProxyASA(config-ctl-file)#shutdown
PhoneProxyASA(config-ctl-file)#record entry capf trustpoint capf_trustpoint address 192.168.1.75
PhoneProxyASA(config-ctl-file)#no shut
4) Allow CAPF traffic to the CUCM
Add an entry to the outside acl to allow tcp port 3804
PhoneProxyASA(config)#access-list outside permit tcp any host 192.168.1.75 eq 3804 (needed for the CAPF connection to CUCM)
PhoneProxyASA(config)#access-list outside permit tcp any host 192.168.1.75 eq 2000 (needed for the phone to download instructions on how to get the LSC cert)
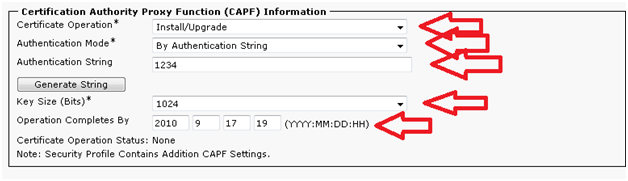
5) Assign the phone instructions to generate a LSC in CUCM
Cisco Unified CM Administration
Device > Phone > Find the PP phone you have configured and select it

Once the phone‘s configuration is shown
Go down to the Certificate Authority Proxy Function (CAPF) Information Section
Make sure to set all settings highlighted
Make sure the operation is set to a date in the future
6) Point the phone to the CUCMs’ mapped ip address
On the phone > Settings > Network Configuration (option 3) > Alternate TFTP (option 32) > **# > Select “Yes” > then “Save”
Go up to “TFTP Server 1”(option 8) in the ‘Network Configuration “ menu and set the mapped ip address of the CUCM(192.168.1.75 in this case).
7) Verify that the CTL-file downloaded
On the phone > Settings > Security Configuration (6) > “CTL File” (5)
8) Update the CTL-file
On the phone go to Settings > Security Configuration (6) > LSC (4)> **# > “update”
Enter authentication string and submit
9) Restart the Phone. Finally you’re done……
Network Diagram
This document uses this network setup:

Configurations
CUCM 7.0.2
7960 running application load “P00308000900.loads”
PhoneProxyASA# sh run
: Saved
:
ASA Version 8.2(2)
!
hostname PhoneProxyASA
domain-name cisco.com
!
interface GigabitEthernet0/0
nameif inside
security-level 100
ip address 172.16.97.1 255.255.255.0
!
interface GigabitEthernet0/1
nameif outside
security-level 0
ip address dhcp setroute
!
clock timezone PDT -8
!
access-list 100 extended permit tcp any host 192.168.1.75 eq 3804
access-list 100 extended permit tcp any host 192.168.1.75 eq 2000
access-list 100 extended permit udp any host 192.168.1.75 eq tftp
!
static (inside,outside) 192.168.1.75 172.16.97.75 netmask 255.255.255.255
!
access-group 100 in interface outside
!
route outside 0.0.0.0 0.0.0.0 192.168.1.1 1
!
crypto ca trustpoint phoneproxy_trustpoint
enrollment self
keypair proxy_key
crl configure
crypto ca trustpoint _internal_ctl_phoneproxy_file_SAST_0
enrollment self
fqdn none
subject-name cn="_internal_ctl_phoneproxy_file_SAST_0";ou="STG";o="Cisco Inc"
keypair _internal_ctl_phoneproxy_file_SAST_0
crl configure
crypto ca trustpoint _internal_ctl_phoneproxy_file_SAST_1
enrollment self
fqdn none
subject-name cn="_internal_ctl_phoneproxy_file_SAST_1";ou="STG";o="Cisco Inc"
keypair _internal_ctl_phoneproxy_file_SAST_1
crl configure
crypto ca trustpoint _internal_PP_ctl_phoneproxy_file
enrollment self
fqdn none
subject-name cn="_internal_PP_ctl_phoneproxy_file";ou="STG";o="Cisco Inc"
keypair _internal_PP_ctl_phoneproxy_file
crl configure
crypto ca trustpoint Cisco_Manufacturing_CA_trustpoint
enrollment terminal
crl configure
crypto ca trustpoint CAP-RTP-001_trustpoint
enrollment terminal
crl configure
crypto ca trustpoint CAP-RTP-002_trustpoint
enrollment terminal
crl configure
crypto ca trustpoint capf_trustpoint
enrollment terminal
crl configure
crypto ca certificate chain phoneproxy_trustpoint
certificate a1f1764a
.....Certificate Removed........
quit
crypto ca certificate chain _internal_ctl_phoneproxy_file_SAST_0
certificate 8275df49
.....Certificate Removed........
quit
crypto ca certificate chain _internal_ctl_phoneproxy_file_SAST_1
certificate 8275df49
.....Certificate Removed........
quit
crypto ca certificate chain _internal_PP_ctl_phoneproxy_file
certificate 8275df49
.....Certificate Removed........
quit
crypto ca certificate chain Cisco_Manufacturing_CA_trustpoint
certificate ca 6a6967b3000000000003
.....Certificate Removed........
quit
crypto ca certificate chain CAP-RTP-001_trustpoint
certificate ca 7612f960153d6f9f4e42202032b72356
.....Certificate Removed........
quit
crypto ca certificate chain CAP-RTP-002_trustpoint
certificate ca 353fb24bd70f14a346c1f3a9ac725675
.....Certificate Removed........
quit
crypto ca certificate chain capf_trustpoint
certificate ca 4d6cfe036a9b89b7
.....Certificate Removed........
quit
!
tls-proxy ASA-tls-proxy
server trust-point _internal_PP_ctl_phoneproxy_file
ctl-file ctl_phoneproxy_file
record-entry cucm-tftp trustpoint phoneproxy_trustpoint address 192.168.1.75
record-entry capf trustpoint capf_trustpoint address 192.168.1.75
no shutdown
!
media-termination mta
address 172.16.97.190 interface inside
address 192.168.1.76 interface outside
!
phone-proxy phone
media-termination mta
tftp-server address cucm70pub interface inside
tls-proxy ASA-tls-proxy
ctl-file ctl_phoneproxy_file
!
class-map sec_sip
match port tcp eq 5061
class-map sec_sccp
match port tcp eq 2443
class-map inspection_default
match default-inspection-traffic
!
!
policy-map global_policy
class inspection_default
inspect tftp
class sec_sccp
inspect skinny phone-proxy phone
class sec_sip
inspect sip phone-proxy phone
!
service-policy global_policy global
PhoneProxyASA#
Process Overview
Step by step registration process with CAPF
1) Phone downloads CTL-file from ASA (phone gets CAPF information)
Settings > Security Configuration (6) >CTL File( 5) to verify
2) Phone downloads config file from CUCM thru ASA
Turn on “debug phone tftp” on ASA cli to verify
3) Phone connects over skinny TCP port 2000
4) On the phone go to Settings > Security Configuration (6) > LSC (4)> **# > “update”
Enter authentication string and submit
5) CAPF connection over TCP port 3804
6) Phone generates LSC
7) Reset phone to begin registration using LSC
8) Phone downloads CTL-file
Phone verifies it matches previous CTL-file
9) Phone downloads config
Turn on “debug phone tftp” on ASA cli to verify
10) Registers over secure skinny using tcp port 2443 and the LSC
“Show phone secure” on ASA shows a non zero port.
Note: if any of these steps fail the phone will not register correctly
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: