- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on
06-27-2016
10:08 PM
- edited on
08-03-2020
03:58 PM
by
Jason Kunst
![]()
February 2016
This document is intended for Cisco engineers and customers who are interested in deploying Cisco Firepower Management Center (FMC) 6.0 with Cisco Identity Service Engine (ISE 2.0 or higher) using (platform exchange Grid) pxGrid.
Note: as of Cisco FirePower 6.7, pxGrid 2.0 is supported. It is recommended to use at least ISE 2.4 (please check with Cisco Software on latest recommended release). There is no updated guide on the configuration as of this time, please reach out to the FirePower team
Please note that pxGrid remediation is not supported in Cisco Firepower Management Center FMC 6.0.
Cisco Firepower Management Center (FMC) 6.0 can now enforce an organizations security policy based on ISE session attribute information available through pxGrid. These security policies can be applied to and enforced by the Cisco Firepower to managed NGIPS sensors and/or an ASA with Firepower services. The ASA with Firepower services vsm also manage these policies locally via ASDM.
This document provides the details of configuring Cisco Firepower Management Center (FMC) 6.0 and pxGrid integration with ISE in an ISE Stand-Alone environment using self-signed certificates or using CA (Certificate Authority)- signed certificates.
In this document an ASA with Firepower services will be configured with the ASA Firepower (sfr) module and register with Cisco Firepower Management Center (FMC) 6.0 to use the centrally managed Cisco Firepower Management Center policy. The ASA with Firepower services will also be configured on-box with the Firepower intrusion policy and access control rule independent of the FMC.
The Cisco Firepower Management Center managed security policy and ASA on box Firepower Management policy will consist of an intrusion policy and Employee SGT access control rule for denying access to specific web categories.
- 2.0
- 6.0
- asa
- configuration
- configure
- context
- firepower
- fmc
- how-to
- integration
- ise
- pxGrid
- secure-access
- sxp
- trustsec
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Thomas!
This integration uses pxGrid, so a Plus License is required, but how many licenses I would need and how these will be consumed?
I'll appreciate your help.
Kind regards.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
http://www.cisco.com/c/en/us/td/docs/security/ise/2-2/admin_guide/b_ise_admin_guide_22/b_ise_admin_guide_22_chapter_0101.html#concept_F7FC0B895D284727B8E3DDDBCAD1A23A
pxGrid is used to share context collected by ISE with other products. A Plus license is required to enable pxGrid functionality. There is no session count decrement when context for session is shared. However, to use pxGrid, the number of Plus sessions licensed must be equal to the number of Base sessions licensed. For more information, see Cisco ISE Licenses and Services section in Cisco Identity Services Engine Ordering Guide<http://www.cisco.com/c/dam/en/us/products/collateral/security/identity-services-engine/guide_c07-656177.pdf>.
http://www.cisco.com/c/dam/en/us/products/collateral/security/identity-services-engine/guide_c07-656177.pdf
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thank you Jason.
Just to add, the ordering guide also says "Service is enabled with a valid Plus license. Requires a 1:1 Plus to Base license sessions".
My customer won't like this ![]() .
.
Regards!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Great Very helpful information.
I just have an Cisco FMCv version 6.2.2 and FTDv version 6.2.2, I configured both the machines and FTD registered in FMC. I have a IPS policy but its Security Intelligence feed are not coming in it.
DO you know whats wrong about the miss configuration of FMC policies.
Resolution of IT:
We need to open port 443 from FMC to talk with Talos to get feeds from it. Further more we can also manually get the blacklist ips and stored it to SI policies, Am i correct?
Thanks
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi guys,
I have read from above that we first need base license and to enable PxGrid we need a plus license 1:1 to base license.
will have ISE virtual integrate with FMC and AnyConnect Apex on client machine as to get AMP enabler for AMP Endpoint.
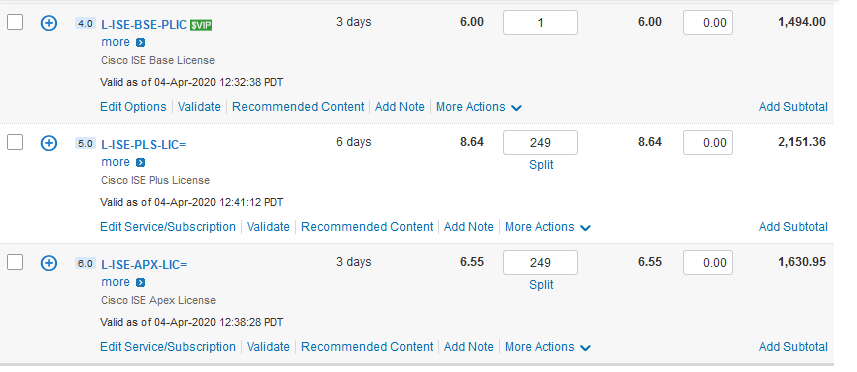
I found plus license more expensive that Apex one, from Cisco portal , question is , does it have to be like this , Base > Plus > Apex, or can it be just Base > Apex, i am a bit confused .
Suppose i need license for 249 users for ISE posture and AMP Endpoint, do i need to get 249 plus license then 249 Apex license ?
Thanks