- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- Integrating Cisco Identity Services Engine with Cisco Meraki Systems Manager
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on
11-18-2019
10:33 AM
- edited on
05-26-2020
09:59 AM
by
thomas
![]()
Integrating Cisco Identity Services Engine with Cisco Meraki Systems Manager
- Integrating Cisco Identity Services Engine with Cisco Meraki Systems Manager
- Overview
- Components
- Configuration Steps
- Certificate Installation
- Add Meraki Systems Manager as an MDM in ISE.
- ISE Authorization Policy
- MDM Dictionary
- Appendix
Overview
Cisco ISE is a leading, identity-based network access control and policy enforcement system. It is a common policy engine for controlling, endpoint access and network device administration for enterprises. ISE allows an administrator to centrally control access policies for wired, wireless, and VPN endpoints in a network. ISE builds context about the endpoints that include users and groups (Who), device type (What), access time (When), access location (Where), access type (Wired/Wireless/VPN) (How), threats, and vulnerabilities. By sharing vital contextual data with technology partner integrations and the implementation of the group policy for software-defined segmentation, ISE transforms a network from a conduit for data into a security enforcer that accelerates the time-to-detection and time-to-resolution of network threats. This guide will demonstrate the steps necessary to integrate Cisco Meraki Systems Manger as an example MDM and Cisco Identity Services Engine.
Components
Cisco Identity Services Engine 2.6
Cisco Meraki Systems Manager
Configuration Steps
Certificate Installation
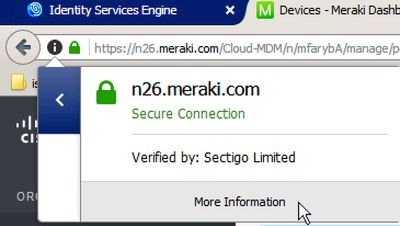
Step 1. Download the SSL certificate from your System Manager dashboard. Firefox users can begin this process by clicking the green lock in the address bar.
Step 2. Click the arrow beside your network URL then select "More Information."
Step 3. Click "View Certificate" then select the "Details" tab.
Step 4. Select "*.meraki.com" then click "Export" at the bottom of the window. Save the certificate to your downloads folder.
Step 5. Close the "Certificate Viewer" window and "Page Info" window.
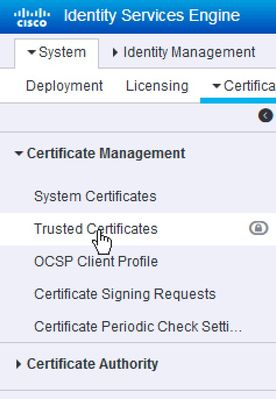
Step 6. Login to the ISE dashboard and navigate to Administration -> System -> Certificates.
Step 7. Click "Trusted Certificates" on the left side menu.
Step 8. Click the "Import" menu button.
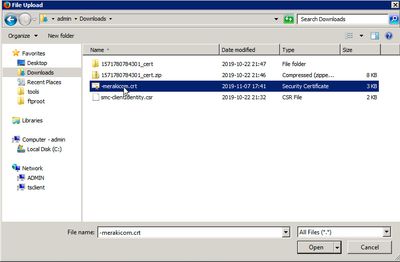
Step 9. Click "Browse" next to *Certificate File.
Step 10. Select the Merkai certificate from your downloads folder, then click "Open."
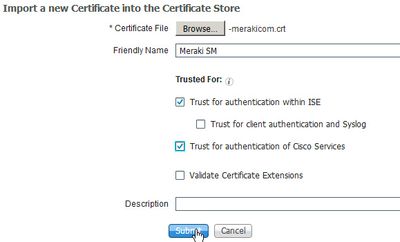
Step 11. In the "Friendly Name" field, enter Meraki SM. This will allow you to easily identify the certificate in the future.
Step 12. Check the box for "Trust for authentication of Cisco Services." This will allow for secure communicate between ISE and Meraki Systems Manager.
Step 13. Click "Submit."
Add Meraki Systems Manager as an MDM in ISE.
Step 1. In the Meraki dashboard for your network, navigate to "Organization" and select "MDM" under "Configuration."
Step 2. Scroll to the bottom of the page to locate the "ISE Settings" section. You will need the username and password information to allow ISE to communicate with Systems Manager.
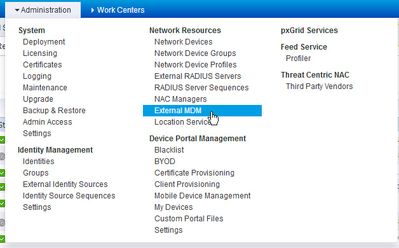
Step 3. In ISE, navigate to Administration -> Network Resources -> External MDM.
Step 4. Click the "+ Add" button.
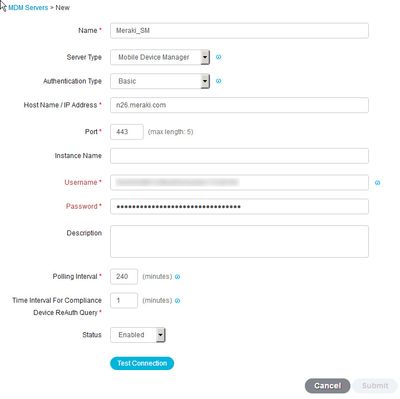
Step 5. Enter the required fields to allow ISE to connect to Systems Manager (Name, Host Name / IP Address, Port, Username and Password). The "Set Up" URL, username and password are obtained from the Meraki Systems Manager dashboard.
Step 6. Click "Test Connection." If you receive an error, it is most likely due to an incorrect username and / or password.
Step 7. If the connection test comes back successful, click the "Submit" button to save the configuration.
ISE Authorization Policy
Now that Meraki Systems Manager is configured in ISE, you will have access to a new attribute dictionary in Authorization Policy. Before you create an authorization rule, a new authorization profile must be created so that devices which are not managed will be redirected for enrollment in Systems Manager. This section relies on the pre-configuration of a wireless LAN controller. Specifically, the ACL that the WLC will use to during the enrollment process. Please see the BYOD Prescriptive Deployment Guide in the appendix for instructions on how to configure the WLC as well as examples for the required redirect ACL to allow for MDM onboarding.
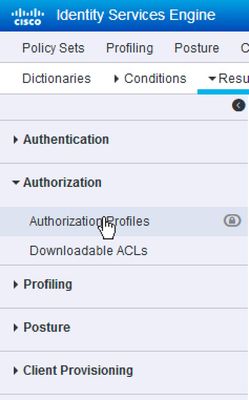
Step 1. In ISE, navigate to Policy -> Policy Elements -> Results.
Step 2. In left side menu, click "Authorization" then "Authorization Profiles."
Step 3. Click the "+ Add" button.
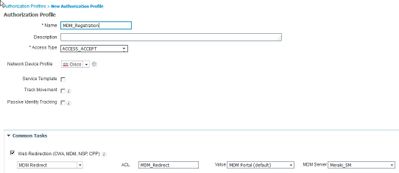
Step 4. Give the profile a name such as MDM Registration and under "Common Tasks," check the box for "Web Redirection (CWA, MDM, NSP, CPP).
Step 5. Fill out the fields for the redirection type, ACL, Value (portal) and MDM Server.
Step 6. Click "Submit." You can now reference this newly created authorization profile in authorization policy.
Step 7. Navigate to Policy -> Policy Sets.
Step 8. Select the Policy Set you would like to use for MDM Onboarding by clicking the black arrow ( > ) on the right side of the UI.
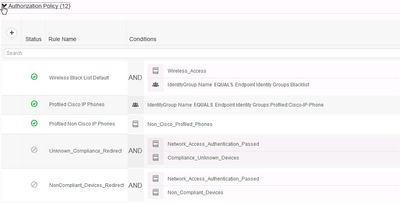
Step 9. Click "Authorization Policy" to expand the list of authorization rules.
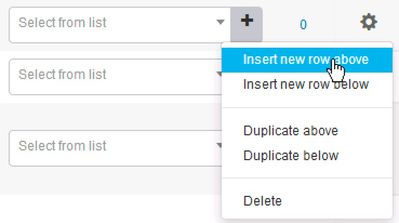
Step 10. Use the gear icon on the right side of the page to create a new authorization rule.
Step 11. Give the new rule a name such as MDM Registration and select the newly created authorization profile from the profiles menu then click the plus ( + ) icon to bring up the condition studio.
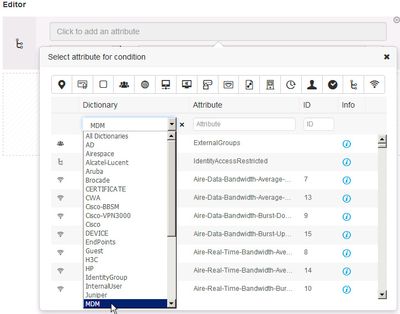
Step 12. Select "Click to add an attribute" in the Editor menu to add a new attribute.
Step 13. Under the Dictionary drop down, select the MDM dictionary.
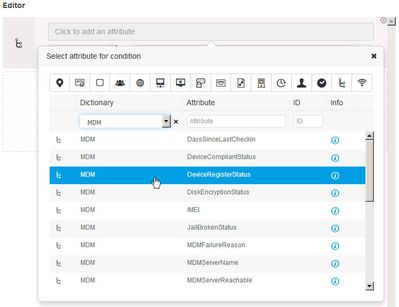
Step 14. Select "DeviceRegisterStatus."
Step 15. Select "UnRegistered" then select "Use" in the lower left corner of the menu then click "Save" to save the new authorization rule.
Step 16. Repeat steps 10 through 15 to create another authorization rule but use an authorization rule name such as "MDM Registered" then use "MDM-DeviceRegisterStatus Equals Registered" for the condition and "PermitAccess" as the authorization result. You should now how two authorization rules for devices that are registered with the MDM and another for devices that are not registered with the MDM.
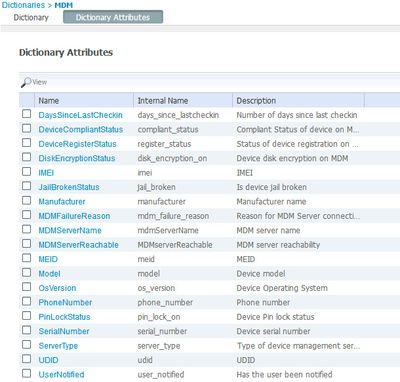
MDM Dictionary
The above example demonstrates the simple process of integrating ISE with Meraki SM and then creating two basic authorization rules that detects if the device connecting to the network is registered or not. The above steps are the same for other MDM vendors as well. Once you integrate the MDM vendor of your choice, you will then have the ability to use the MDM dictionary in authorization policy. Moreover, there additional attributes you will have the ability to use. Some of those attributes are macro in nature such as Compliant or Noncompliant. Other attributes are more granular in nature. Some of attributes include the ability to detect if PIN lock status, Jail-broken status and Disk Encryption status. To view the complete list of dictionary attributes, navigate to Workcenters > Network Access > Dictionaries, then select "System" from the left side menu and chose "MDM."
Appendix
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: