- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- IOS: Auth-proxy with TACACS
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
03-13-2011 04:09 AM - edited 03-08-2019 06:39 PM
Documentation
This configuration example is meant to be interpreted with the aid of the official documentation from the configuration guide located here:
http://www.cisco.com/en/US/docs/ios/12_0t/12_0t5/feature/guide/iosfw2_1.html#wp12282
Prerequisites
For the authentication proxy to work properly, the client browser must be running the following browser software:
- Microsoft Internet Explorer 3.0 or later
- Netscape Navigator 3.0 or later
Goal
The goal is to authenticate the user (192.168.2.10) to R2 (100.110.10.50) via http upon which the tacacs server should add a dynamic access-list to the ACL applied on R1's F0/0 interface and allow the user (192.168.2.10) to ping R2 (100.110.10.50).
Topology
How auth-proxy works
The Cisco IOS Firewall authentication proxy feature allows network administrators to apply specific security policies on a per-user basis.
- auth-proxy intercepts the specified traffic through the router
- forwards to ACS for authentication
- ACS authenticates the user and also pushes allowed access-list to the router
- User is allowed to access the resources based on the dynamic access-lists pushed down to the router by ACS
Assumption
This excercise will assume that all routing is in place and there is proper route from the 192.168.2.0/24 to the 100.110.10.0/24 network. Make sure you can ping end to end.
Step by Step Configuration (R1)
Deny the flow that has to be dynamically allowed by the ACS server inbound on F0/0 on R1
ip access-list extended 153
10 deny icmp host 192.168.1.10 host 100.110.10.50
20 permit ip any any
interface f0/0
ip access-group 153 in
Configure aaa on the router - also protect the console
aaa new-model
aaa authentication login default group tacacs+
aaa authentication login FREE none
aaa authorization auth-proxy default group tacacs+
optional: aaa authentication login AUTH_PROXY group tacacs+
line con 0
login authentication FREE
Configure tacacs server
tacacs-server host 192.168.2.101 key cisco
Enable http server on R1 and configure authentication via aaa
ip http server
ip http authentication aaa
optional: ip http authentication aaa login-authentication AUTH_PROXY
Create auth-proxy instance to intercept interesting traffic
ip access-l ext AUTH-PROXY-ACL
10 permit tcp host 192.168.2.10 host 100.110.10.50 eq www log (log keyword is optional)
ip auth-proxy name AUTHP http list AUTH-PROXY-ACL
Finally apply auth-proxy to the interface (in this case F0/0 on R1)
interface FastEthernet0/0
ip auth-proxy AUTHP
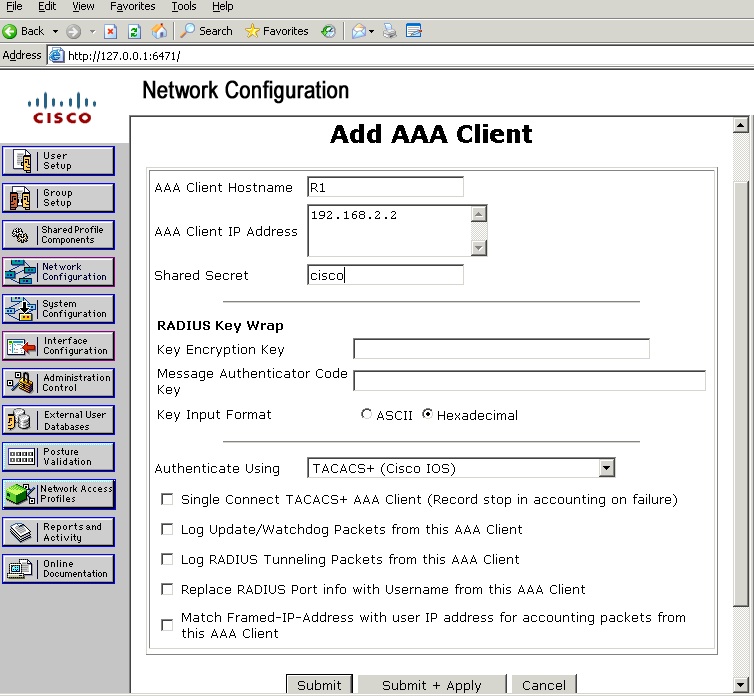
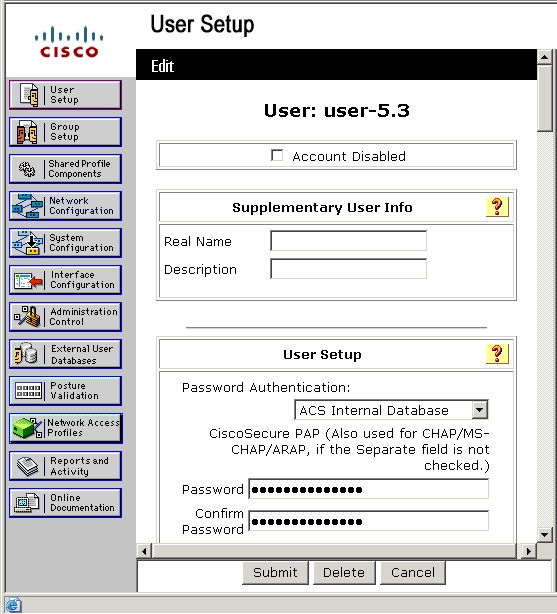
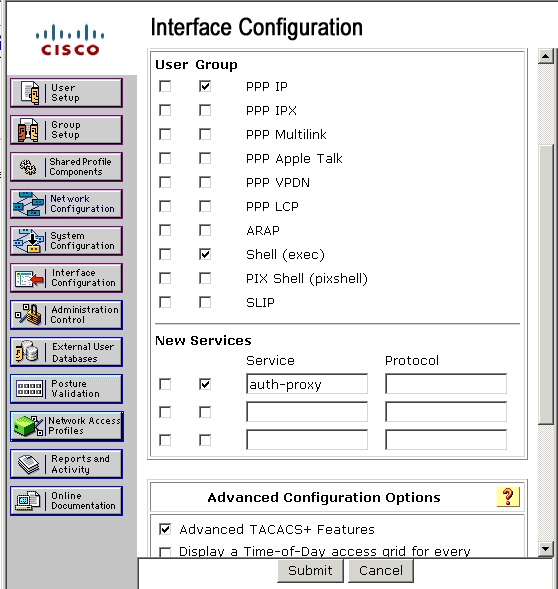
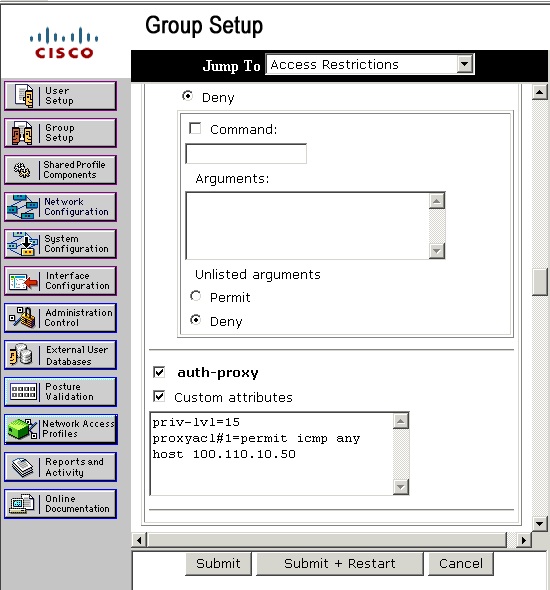
Configure the ACS server
create R1 as a AAA client on the ACS server
create the user
enable auth-proxy service (under the Interface configuration)
configure proxy acl under the group setup for the user (make sure the source is "any")
Test from the Router R1
R1#test aaa group tacacs+ user-5.3 cisco legacy
Attempting authentication test to server-group tacacs+ using tacacs+
User was successfully authenticated.
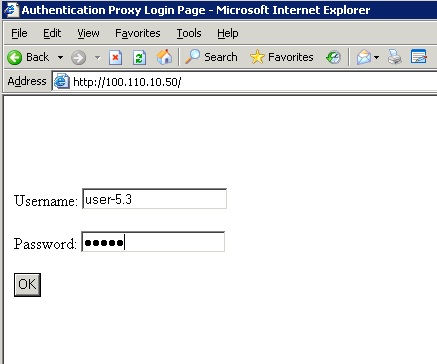
Test from the User PC
Authenticating via the browser
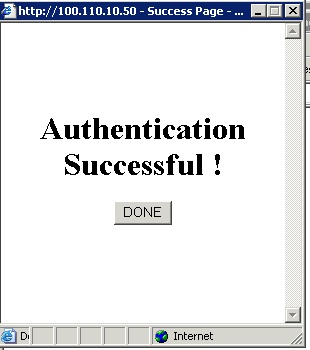
Auth result
Verify the addition of dynamic ACL on the router
R1#sh access-l 153
Extended IP access list 153
permit icmp host 192.168.2.10 host 100.110.10.50 (un-numbered dynamic acl added)
10 deny icmp host 192.168.1.10 host 100.110.10.50 log
20 permit ip any any (15 matches)
Final Configuration Section:
aaa authentication login default group tacacs+
aaa authentication login FREE none
aaa authorization auth-proxy default group tacacs+
!
ip auth-proxy name AUTHP http inactivity-time 60 list AUTH-PROXY-ACL
!
interface FastEthernet0/0
ip address 192.168.2.2 255.255.255.0
ip access-group 153 in
ip auth-proxy AUTHP
!
ip http server
ip http authentication aaa
!
access-list 153 deny icmp host 192.168.2.10 host 100.110.10.50
access-list 153 permit ip any any
!
ip access-list extended AUTH-PROXY-ACL
permit tcp host 192.168.2.10 host 100.110.10.50 eq www log
!
line con 0
login authentication FREE
Debugs and show commands:
debug TACACS+ authentication
debug TACACS+ authorization
debug AAA Authentication
debug AAA Authorization
show access-list 153
show ip auth-proxy cache
clear ip auth-proxy cache *
Here are the outputs
debugs output:
* Mar 13 10:58:49.969: %SEC-6-IPACCESSLOGP: list AUTH-PROXY-ACL permitted tcp 192.168.2.10(3254) -> 100.110.10.50(80), 1 packet
* Mar 13 10:58:49.973: AAA: parse name=FastEthernet0/0 idb type=-1 tty=-1
* Mar 13 10:58:49.973: AAA: name=FastEthernet0/0 flags=0x15 type=14 shelf=0 slot=0 adapter=0 port=0 channel=0
* Mar 13 10:58:49.973: AAA: parse name=<no string> idb type=-1 tty=-1
* Mar 13 10:58:49.973: AAA/MEMORY: create_user (0x49213158) user='NULL' ruser='NULL' ds0=0 port='FastEthernet0/0' rem_addr='192.168.2.10' authen_type=ASCII service=LOGIN priv=0 initial_task_id='0', vrf= (id=0)
* Mar 13 10:58:49.973: AAA/AUTHEN/START (2787625091): port='FastEthernet0/0' list='default' action=LOGIN service=LOGIN
* Mar 13 10:58:49.973: AAA/AUTHEN/START (2787625091): found list default
* Mar 13 10:58:49.973: AAA/AUTHEN/START (2787625091): Method=tacacs+ (tacacs+)
* Mar 13 10:58:49.977: TAC+: send AUTHEN/START packet ver=192 id=-1507342205
* Mar 13 10:58:50.181: TAC+: ver=192 id=-1507342205 received AUTHEN status = GETUSER
* Mar 13 10:58:50.181: AAA/AUTHEN(2787625091): Status=GETUSER
* Mar 13 10:58:50.181: AAA/AUTHEN/CONT (2787625091): continue_login (user='(undef)')
* Mar 13 10:58:50.181: AAA/AUTHEN(2787625091): Status=GETUSE
* Mar 13 10:58:50.181: AAA/AUTHEN(2787625091): Method=tacacs+ (tacacs+)
* Mar 13 10:58:50.181: TAC+: send AUTHEN/CONT packet id=-1507342205
* Mar 13 10:58:50.381: TAC+: ver=192 id=-1507342205 received AUTHEN status = GETPASS
* Mar 13 10:58:50.381: AAA/AUTHEN(2787625091): Status=GETPASS
* Mar 13 10:58:50.381: AAA/AUTHEN/CONT (2787625091): continue_login (user='user-5.3')
* Mar 13 10:58:50.381: AAA/AUTHEN(2787625091): Status=GETPASS
* Mar 13 10:58:50.381: AAA/AUTHEN(2787625091): Method=tacacs+ (tacacs+)
* Mar 13 10:58:50.381: TAC+: send AUTHEN/CONT packet id=-1507342205
* Mar 13 10:58:50.581: TAC+: ver=192 id=-1507342205 received AUTHEN status = PASS
* Mar 13 10:58:50.581: AAA/AUTHEN(2787625091): Status=PASS
* Mar 13 10:58:50.581: FastEthernet0/0 AAA/AUTHOR/HTTP(1387380163): Port='FastEthernet0/0' list='default' service=AUTH-PROXY
* Mar 13 10:58:50.581: AAA/AUTHOR/HTTP: FastEthernet0/0(1387380163) user='user-5.3'Mar 13 10:58:50.581: FastEthernet0/0 AAA/AUTHOR/HTTP(1387380163): send AV service=auth-proxy
* Mar 13 10:58:50.581: FastEthernet0/0 AAA/AUTHOR/HTTP(1387380163): send AV cmd*
* Mar 13 10:58:50.581: FastEthernet0/0 AAA/AUTHOR/HTTP(1387380163): found list "default"
* Mar 13 10:58:50.581: FastEthernet0/0 AAA/AUTHOR/HTTP(1387380163): Method=tacacs+ (tacacs+)
* Mar 13 10:58:50.581: AAA/AUTHOR/TAC+: (1387380163): user=user-5.3
* Mar 13 10:58:50.581: AAA/AUTHOR/TAC+: (1387380163): send AV service=auth-proxy
* Mar 13 10:58:50.581: AAA/AUTHOR/TAC+: (1387380163): send AV cmd*
* Mar 13 10:58:50.785: TAC+: (1387380163): received author response status = PASS_ADD
* Mar 13 10:58:50.785: AAA/AUTHOR (1387380163): Post authorization status = PASS_ADD
show command outputs:
R1#sh ip auth-proxy cache
Authentication Proxy Cache
Client Name user-5.3, Client IP 192.168.2.10, Port 3254, timeout 60, Time Remaining 60, state ESTAB
R1#sh access-l 153
Extended IP access list 153
permit icmp host 192.168.2.10 host 100.110.10.50 (un-numbered dynamic acl added)
10 deny icmp host 192.168.1.10 host 100.110.10.50 log
20 permit ip any any (15 matches)
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: