WARNING
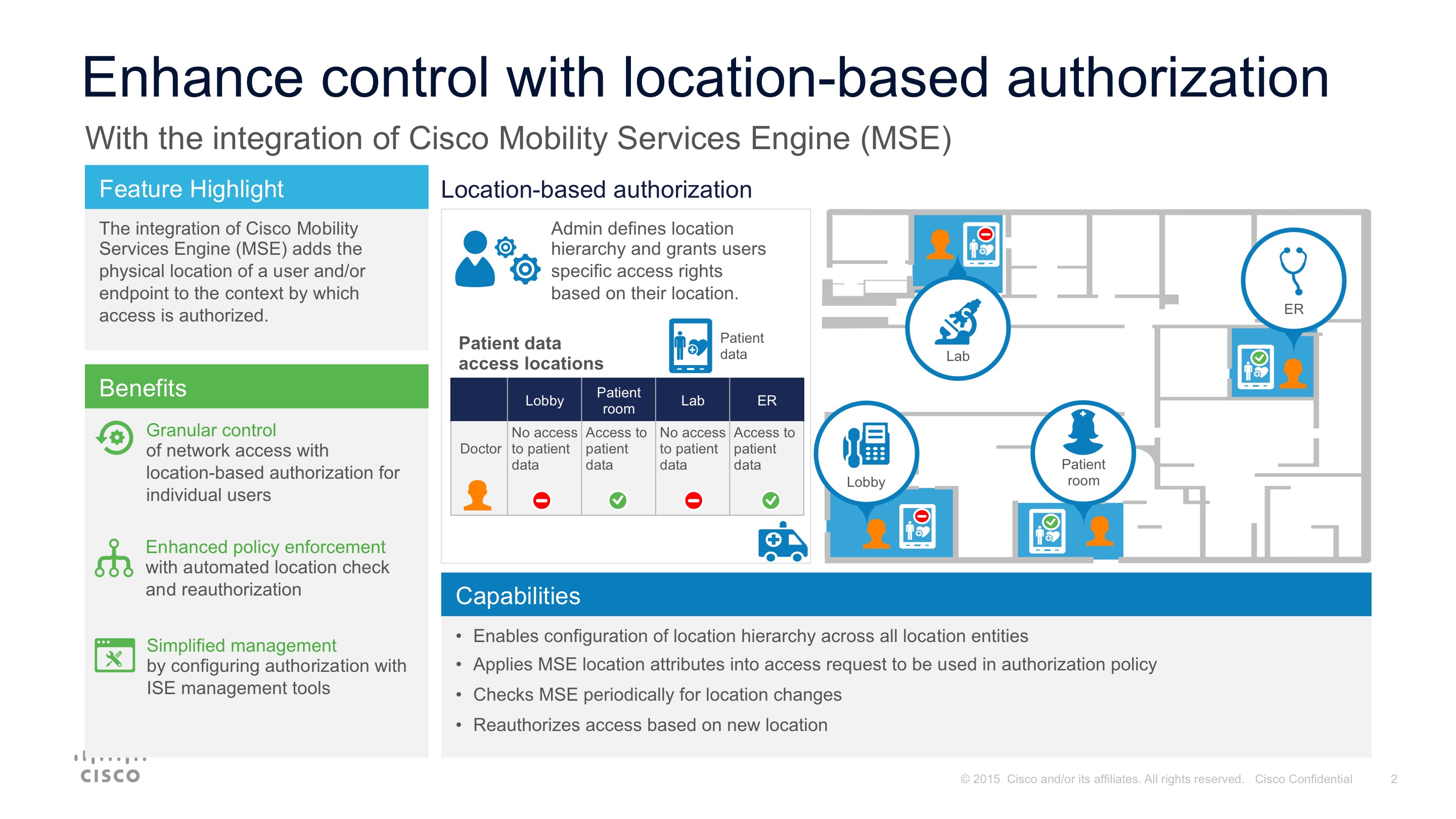
ISE 2.x featured integration with Cisco Mobility Services Engine (MSE) which enables administrators to grant access to users specifically based on their location.
Currently, the definition of a location on a network is very static and is based on the network switch that a user came through to access the network. Location hasn’t been based on the real, geographic, location of a user, who might be moving around, frequently changing location (even location within a specific building). As an example, you might want to grant a doctor in a hospital access to patient records or access to certain applications while in an emergency, but when that doctor moves to the medical lab, maybe they should no longer be able to access those same records or applications.
The location-based authorization enabled by the integration of Cisco Mobility Services Engine (MSE) with ISE 2.0 increases the granular control administrators have and the ability to be more sensitive in their access authorization. MSE will also help administrators enforce location-based policies by periodically checking for location change and automatically reauthorizing the user if a location change is detected. Finally, ISE 2.0 make the configuration of location-based policies with MSE more simple and streamlined—you can define user access policies leveraging the same management tools already available through ISE.
This is currently supported with MSE 8.x, it is not supported with CMX (MSE 10+). Please reach out to sales team to request feature.
![]()
![]()