- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- Managing CISCO IOS IPS with Syslog or SDEE and Troubleshooting
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
11-19-2012 10:30 PM - edited 03-08-2019 06:47 PM
- Introduction:
- What is IPS?
- Understanding SDEE:
- Storing SDEE events in Buffer:
- Steps for Configuration:
- TROUBLESHOOTING:
- Understanding IPS system messages:
Introduction:
In this document you would see:
1.) How to manage CISCO IPS with help of SDEE
2.) Basic Troubleshooting
What is IPS?
Intrusion prevention systems (IPS), also known as intrusion detection and prevention systems (IDPS), are network security appliances that monitor network and/or system activities for malicious activity. The main functions of intrusion prevention systems are to identify malicious activity, log information about said activity, attempt to block/stop activity, and report activity.
Intrusion prevention systems are considered extensions of intrusion detection systems because they both monitor network traffic and/or system activities for malicious activity. The main differences are, unlike intrusion detection systems, intrusion prevention systems are placed in-line and are able to actively prevent/block intrusions that are detected.More specifically, IPS can take such actions as sending an alarm, dropping the malicious packets, resetting the connection and/or blocking the traffic from the offending IP address. An IPS can also correct Cyclic Redundancy Check (CRC) errors, unfragment packet streams, prevent TCP sequencing issues, and clean up unwanted transport and network layer options.
Understanding SDEE:
- It is a protocol which is used at application level for exchange of messages between IPS server and IPS client.
- SDEE is always running, but it does not receive and process events from IPS unless SDEE notification is enabled.
- If in case it is not enabled and a client sends a request, SDEE will send a fault response message, indicating that notification is not enabled.
Storing SDEE events in Buffer:
When SDEE notification is enabled 200 hundred events can be automatically stored in buffer. When SDEE notification is disabled, all stored events are lost. A new buffer is allocated when the notifications are reenabled.
While specifying the size of an events buffer, we need to take care of following functionality:
- Circular: When buffer is reached to end, the buffer will start overwriting the earliest stored events. (If overwritten events have not yet been reported, you will receive a buffer overflow notice.)
- If a new, smaller buffer is requested, all events that are stored in the previous buffer will be lost.
- If a new, larger buffer is requested, all existing events will be saved.
Steps for Configuration:
STEP 1: Enables privliged EXEC mode
router>enable
STEP 2: Enter in to Global Configuration Mode.
router#conf t
STEP 3: Enable SDEE event notification
router(config)#ip ips notify sdee
STEP 4: Setting number of events that could be stired in Buffer
router(config)#ip sdee events <events number>
deafult:200
maximum:1000
STEP 5: Setting simultaneous subscriptions
router(config)#ip sdee subscriptions <range>
range:between 1 to 3
TROUBLESHOOTING:
To print sdee alerts on the console:
debug ip sdee
To clear event buffer
clear ip sdee
Understanding IPS system messages:
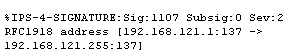
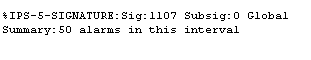
1.) ALARM MESSAGES
Triggering of IPS signature
Flooding of a specific signature
In below mentioned error we can see that signature no:1107 has been flooded to a count of 50.
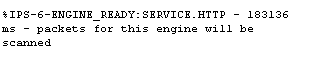
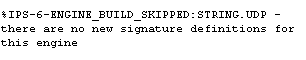
2.) STATUS MESSAGES
IPS signature engine is built and ready to scan packet.
No signature definitions or changes to the existing signature definitions and the engine does not need to be rebuilt.
Packets are being dropped because IPS module is not functioning and "ip ips fail closed" command is configured.
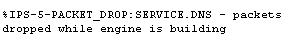
Packets are passing but are not being scanned because IPS module is not functioning and the "ip ips fail closed" command is not configured.
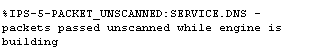
An SDF(Signature definition file) is successfully loaded from a given location.
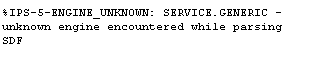
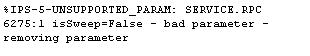
3.) ERROR MESSAGES
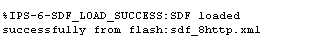
One of these three messages can be seen when IPS loads the built-in signatures.
The router has encountered an unknown and unsupported signature engine while parsing the SDF.
Note To prevent this message from being generated again, ensure that the SDF being loaded on the router does not contain any engines that are not supported by IPS.
The router has encountered an unsupported parameter while parsing the SDF.
- The signature is deleted if the unsupported parameter is required for the signature.
- The parameter is removed from the signature if it is not required.
Note: To prevent this message from being generated again, ensure that the SDF being loaded on the router does not contain any parameters that are not supported by IPS.
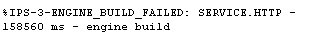
One of the signature engines fails to build after an SDF is loaded. A message is sent for each engine that fails.
- An engine typically fails to build because of low memory, so increasing router memory can alleviate the problem. Also, try to load the SDF immediately after a route reboots, which is when system resources are available.
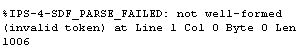
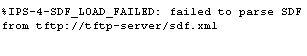
SDF has not parsed correctly, SDF might have been corrupted.
An SDF fails to load.This may occur because of following reasons:
- Fails to load if it resides on a network server that cannot be reached
- Does not have the correct read permissions
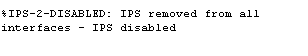
IPS has been disabled and why it is disabled.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: