- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- RSA Adaptive Authentication with ASA Clientless SSLVPN
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
05-23-2011 12:04 PM - edited 08-28-2017 02:31 AM
Introduction
What is RSA AA?
•PCI compliance requires a high level of assurance for authenticating users.
•Adaptive Authentication offers multi-factor authentication method without the need for user certificates or fobs.
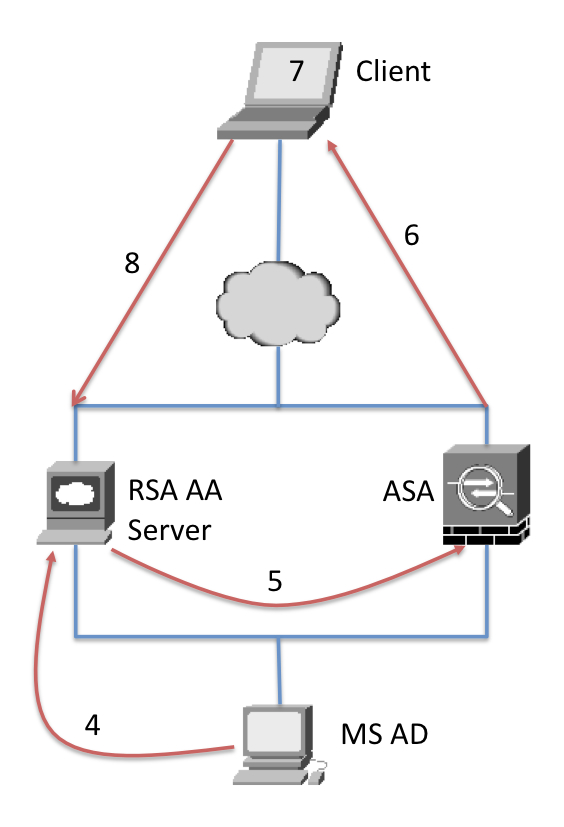
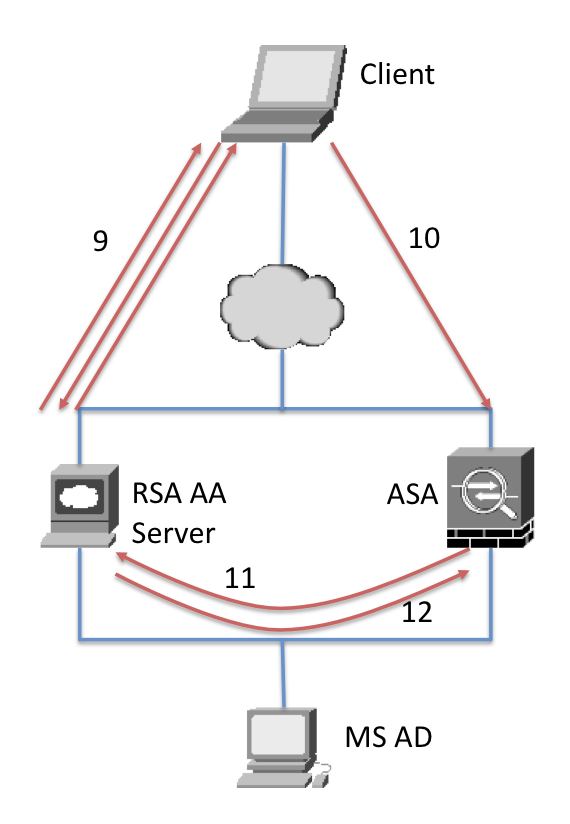
How does it work: Overview
How does it work: details
1) Client visits ASA webpage and puts in username/password.
2) ASA sends the user/pass via RADIUS to RSA AA server on it’s inside interface.
3) RSA AA server forwards the user/pass to MS AD for authentication (either via ldap or radius)
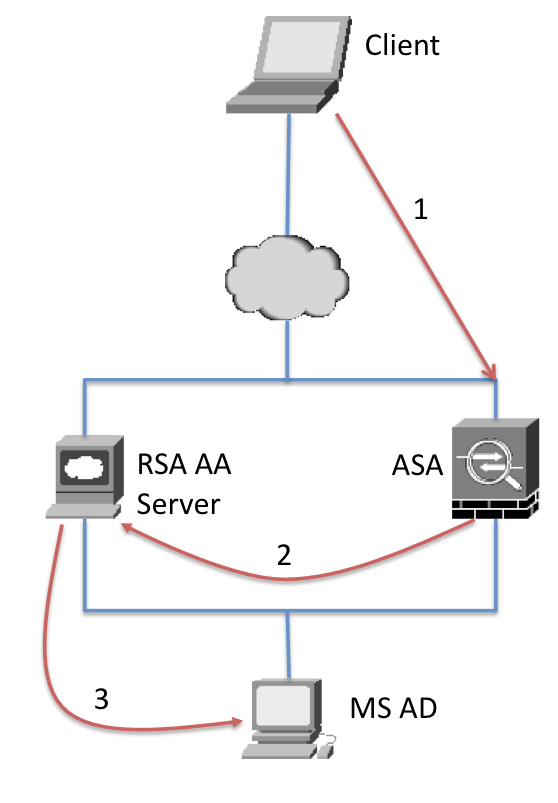
4) If the user/pass is correct then the MS AD authorizes the user and sends back an ‘Ok’ message to the RSA AA server. So at this point the RSA AA server has completed 1 factor authentication.
5) RSA AA server then sends a ‘Radius-Challenge’ message with a message that contains a string value X
6) ASA displays the message X and prompts for a response.
7) The Javascript running in the client browser reads the page the ASA returned and extracts value X.
8) The Javascript takes the value X and sends it towards the public facing RSA AA interface.
This document is complementary for "Adpative Authentication Integration
Guide for Cisco SSL-VPN.pdf" available from RSA Security, Inc. Please contact RSA Security, Inc. for detailed installation guides.
Basic installation steps:
1) Extract the "adapters-sslvpn-products-cisco-asa.zip" file to your computer
2) Edit the aa_config.js file to point to your RSA AA server url
3) Configure the ASA to use Radius for authentication under the tunnel-group. Configure the ASA to use the RSA AA server as the Radius server.
4) Import the contents of the zip file to the ASA as 'web-content'. Make sure to select "No" for 'Require authentication to access its content?'
5) Create a customization and add the following into the "copyright panel"
<script src="/+CSCOU+/aa_config.js"></script><script src="/+CSCOU+/challenge.js"></script>
6) Assign the customization to the tunnel-group that you are connecting to.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Where do you get the file:
adapters-sslvpn-products-cisco-asa.zip
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
lucchejj,
That file is provided by RSA when you purchase the Adaptive Authentication product. You will need to contact RSA for further information. This document is really just an informal guide on how to integrate these products from the ASA side.
-Jay
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello Jay
is there any specific hardware or software requirement for ASA- RSA intergration as stated above, we have ASA5540 with Ver 8.4(7) and are facing multiple issues. Client successfully authenticates but is again prompted the Login page.
We are following integration guide that is provided by RSA, but they tested this feature with ASA 9.3.x Code.
Any reference in this regard.
Thanks
Ahad
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: