To configure on Demand or other additional mobile settings for Anyconnect clients from the ASA, one can use the profile Editor to configure the settings by following the steps enumerated below:

However, if you are unable to find this option "Addition mobile-only settings" don't get too worried. Most likely what's happened is the version of Anyconnect package installed on the ASA is 2.5.x. While this is understandable since the iphone or ipad AC client version is also only 2.5.x., unforutnately this is also the reason behind you not being able to see the above option. This option was only integrated into the profile editor for AC 3.x packages. So if you were to install a 3.x Anyconnect package on your ASA, everything would work just fine.
Do I need to update clients on all devices then?
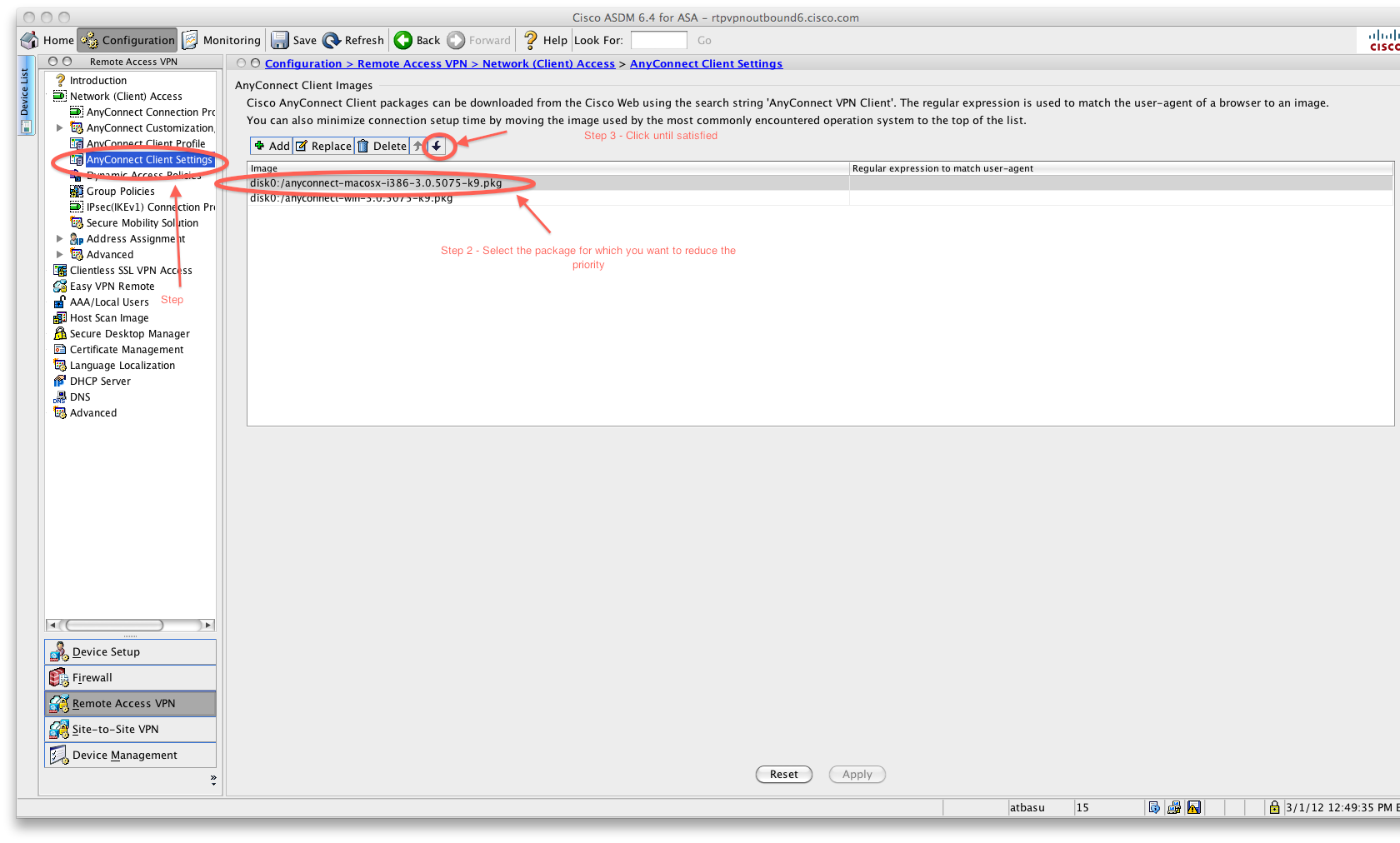
Now, you might be wondering, so does that mean I have to upgrade all my existing non-mobile clients to this version?? NOPE. ASA only requires that a 3.x package be installed in the ASA, not that it be in use by a client. So you can continue to use your existing client version, just add the 3.x client at the bottom of the list, by tweaking the order number in the command:
anyconnect image disk0:/anyconnect-win-3.0.5075-k9.pkg <order_no>
As long as this order no is greater than the other versions installed on the ASA, this version should never be used. You can do the same thing on ASDM by moving the packages up and down in the window shown below:
And voila... you know have the functionality of the 3.x profile editor without having to update your client versions. On a side note, it is definitely a good idea to consider moving to the 3.x code version.
Where do I download Ancyonnect client v 3.x from?
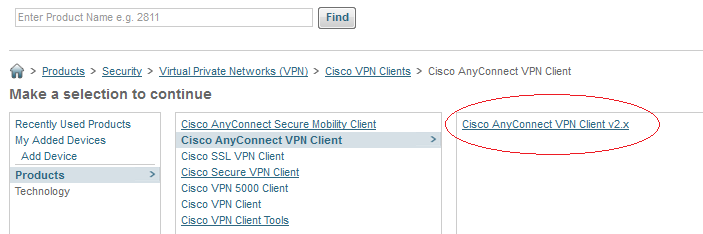
You can get the 3.x client from Cisco.com, however, unlike the 2.x clients, the 3.x client isn't called Anyconnect VPN client, instead it is called Anyconnect Secure Mobility Client: