- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- How To: Cisco ISE Captive Portals with Aruba Wireless
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
06-22-2022 06:23 PM - edited 05-21-2024 07:33 AM
How To: Cisco ISE Captive Portals with Aruba Wireless
Authors: Adam Hollifield, Brad Johnson
- Introduction
- Prerequisites
- Minimum Requirements
- Components Used
- Configuration
- Aruba Wireless Controller
- WLAN Creation
- Authentication Configuration
- Role & Policy Configuration
- Cisco ISE
- Aruba RADIUS Dictionary Addition
- Aruba Network Device Profile
- Aruba Authorization Profiles
- Authentication Allowed Protocols Configuration
- Policy Set Configuration
- Verification
- ISE RADIUS Live Logs
- Aruba Mobility Controller
Introduction
Previous configurations for integrating Cisco ISE portals and Aruba Wireless used a static external captive portal URL to redirect clients to an ISE portal. This required the use of multiple authorization profiles and authorization rules per PSN. Aruba AOS 8.4 added support for the Aruba-Captive-Portal-URL Vendor Specific Attribute (VSA) which allows for dynamic URL redirection similar to what we see when configuring portal rules with Cisco network access devices (NADs). This will enable additional scale, posture flows, and ease of configuration when integrating Aruba wireless with Cisco Identity Services Engine.
Prerequisites
Minimum Requirements
The minimum software requirements for this configuration:
- Aruba AOS 8.4 or later (NOTE: based on various community feedback this configuration does not work with Aruba Instant Mode APs. Aruba Instant Mode does not have support for the Aruba-Captive-Portal-URL VSA)
- Cisco ISE 2.4 or later
Components Used
The information in this document is based on these software versions:
- Aruba Wireless Controller with AOS 8.10.0.1
- Cisco ISE 3.1 with Patch 3
Configuration
Aruba Wireless Controller
WLAN Creation
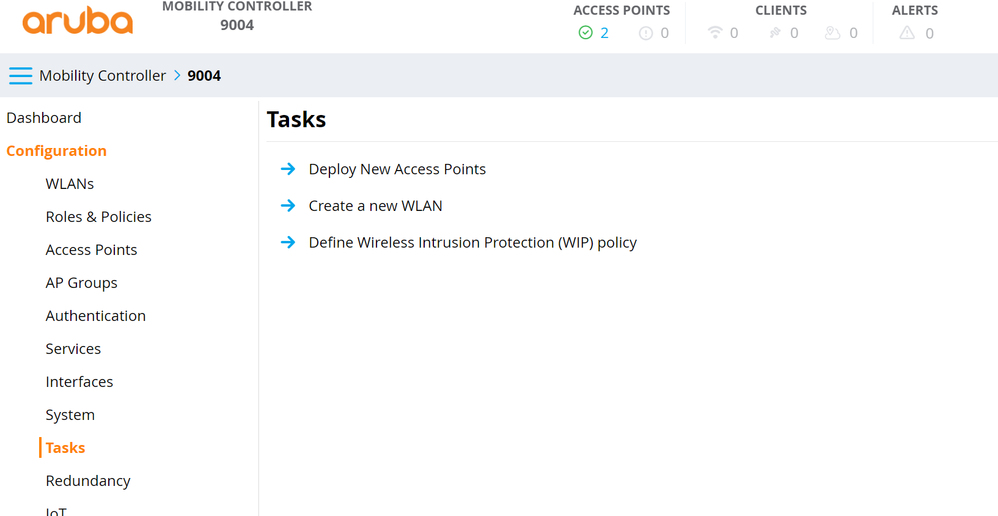
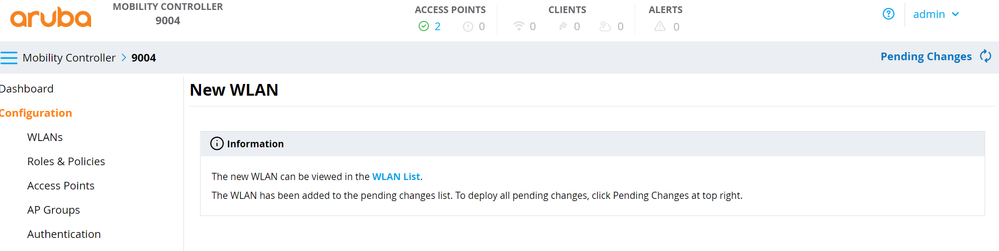
- Navigate to Configuration > Tasks > Create a new WLAN.
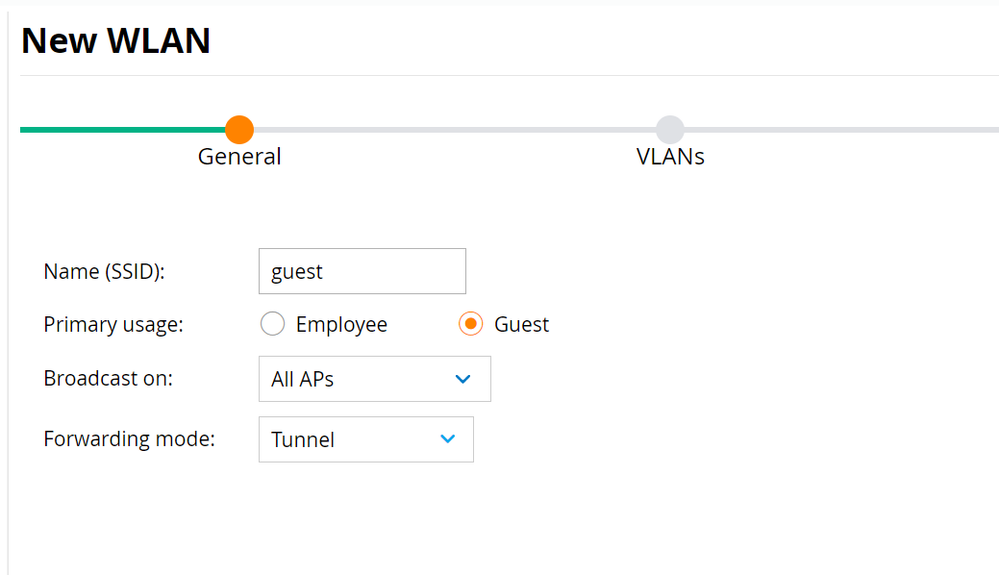
- Fill in the SSID and select Guest as Primary usage. Select AP groups and Forwarding mode as required by the wireless deployment. Click Next.
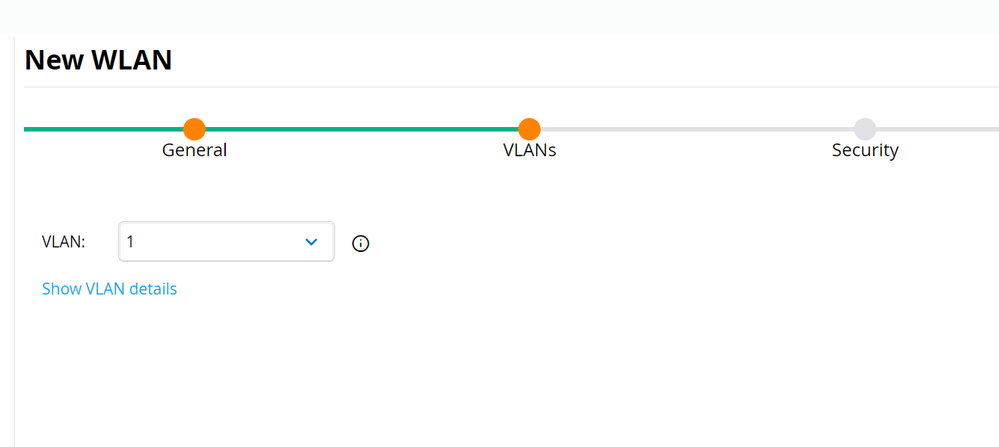
NOTE: it is best practice to broadcast WLANs only on specified AP groups and not use the default group. - Select the VLAN and click Next.
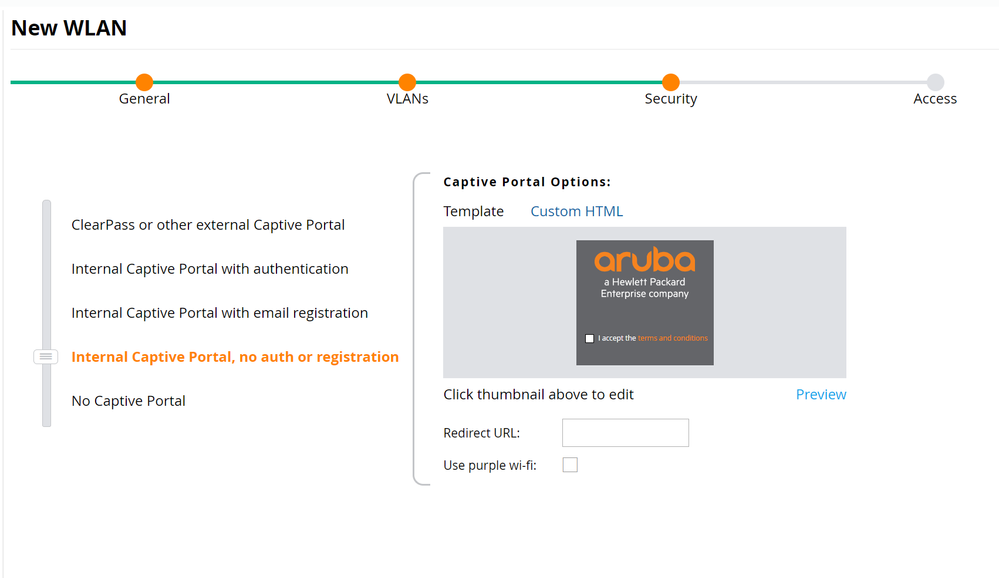
- Set Security to Internal Captive Portal, no auth or registration and click Next.
The Internal Captive Portal will not be used here and will be overridden by the captive portal URL supplied by ISE through the Aruba-Captive-Portal-URL VSA. However, the Aruba Mobility Controller requires some form of Captive Portal to be enabled on the WLAN to successfully redirect clients. - Click Next and Finish.
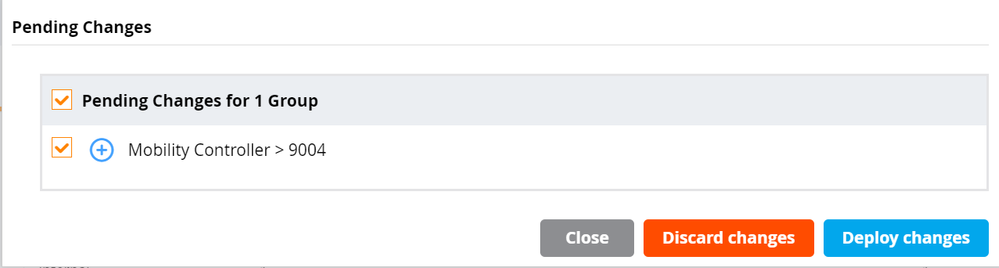
- Click Pending Changes in the top right and click Deploy changes to deploy the configuration to the Mobility Controller.
Authentication Configuration
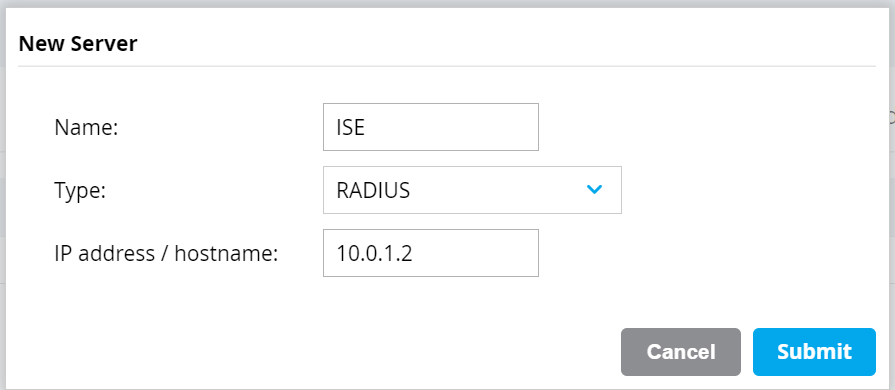
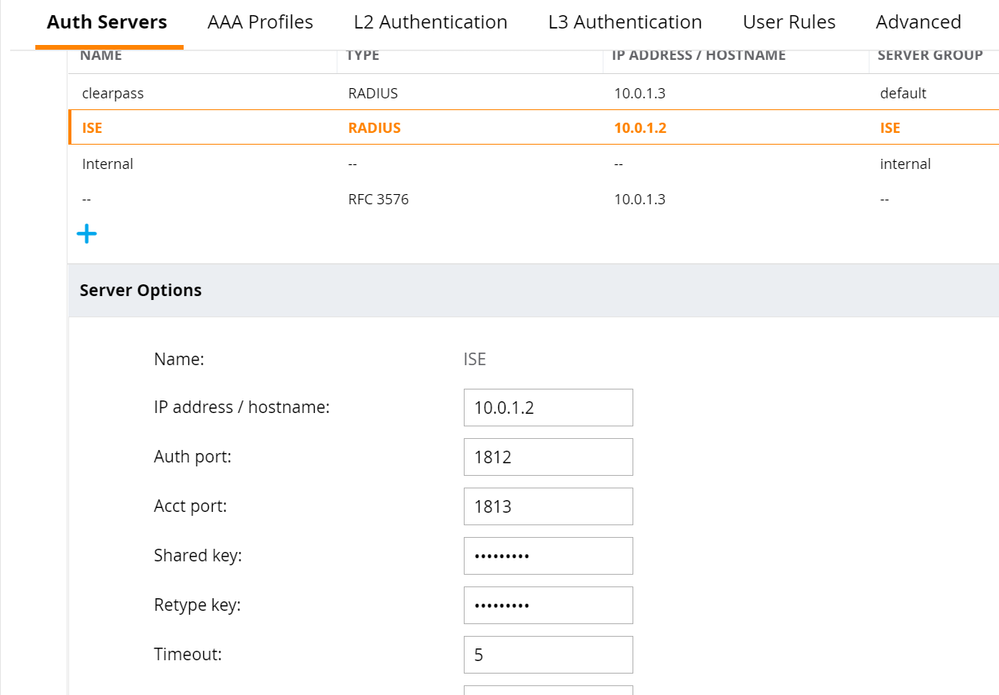
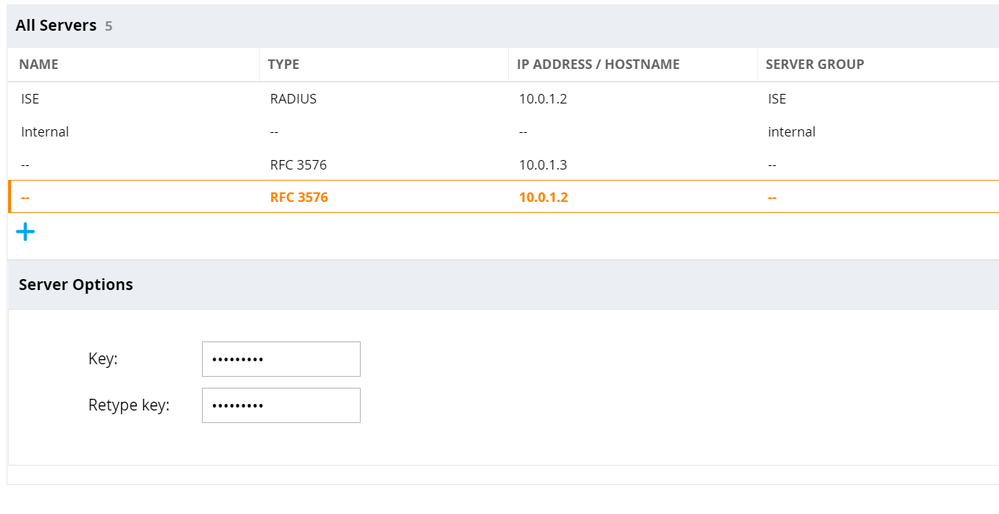
- Navigate to Configuration > Authentication > Auth Servers. Click the + button under All Servers. Fill in name, select type as RADIUS, and fill in the IP address/hostname of the ISE PSN. Click Submit. Repeat for each of the ISE PSNs.
- Select the newly created RADIUS Server definition. Enter the Shared Key and click Submit. Repeat for each of the ISE PSN RADIUS Server definitions.
- Click the + button under All Servers. Change type to Dynamic Authorization and enter the IP address of the ISE PSN. Click Submit. Repeat for each of the ISE PSNs.
- Select the newly created RFC 3576 definition and enter the Key. Click Submit. Repeat for each of the ISE PSN RFC 3576 definitions.
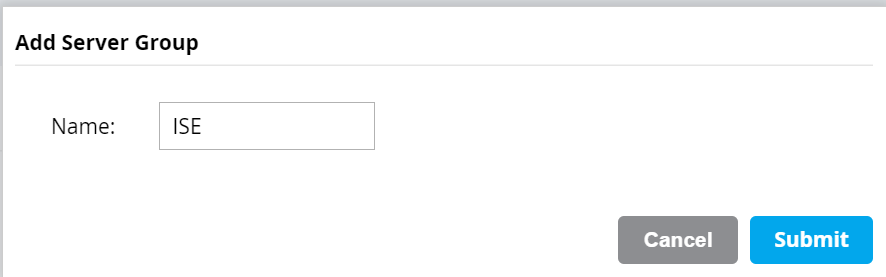
- Click the + button under Server Groups. Enter a name. Click Submit.
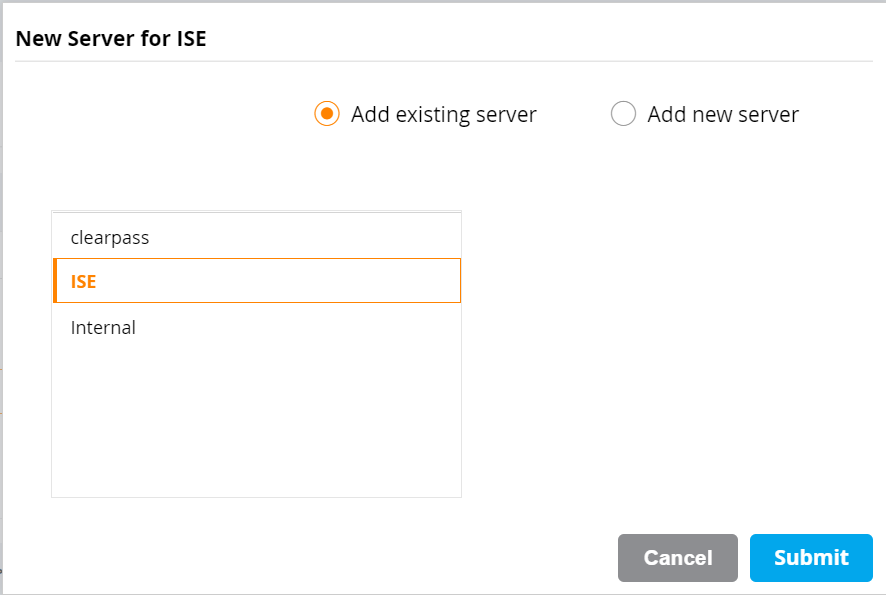
- Select the newly created Server Group and click the + button. Choose Add existing server and select the ISE PSN RADIUS Server definition. Click Submit. Repeat for the rest of the ISE PSN RADIUS Server definitions.
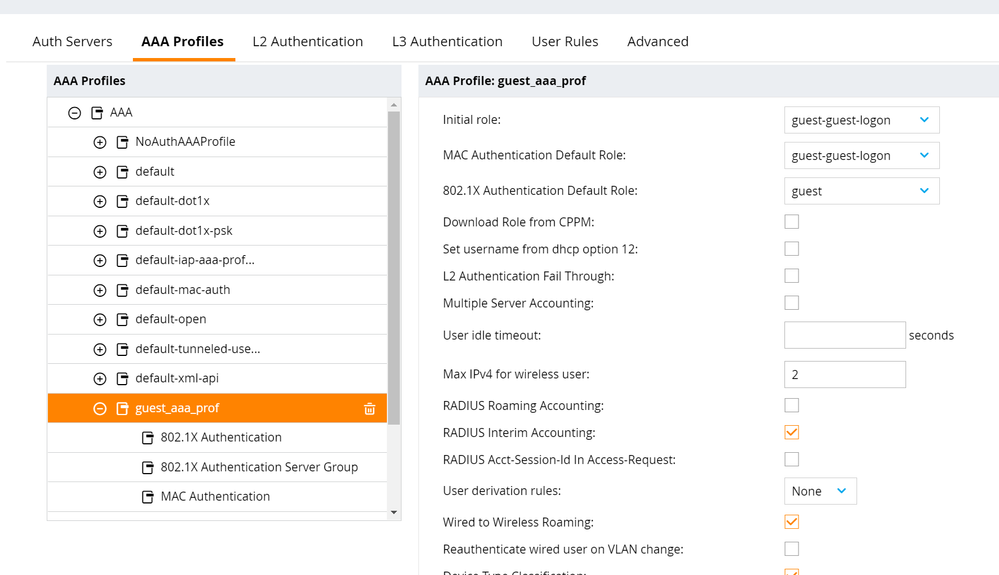
- Navigate to Configuration > Authentication > AAA Profiles. Select the AAA profile for the newly created WLAN, [SSID]_aaa_prof. Enable RADIUS Interim Accounting. Click Submit.
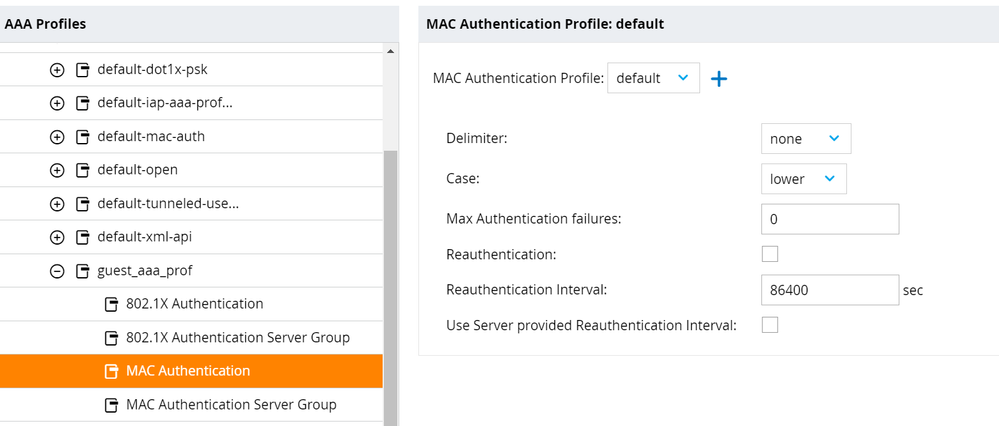
- Select MAC Authentication. Change MAC Authentication Profile to Default. Click Submit.
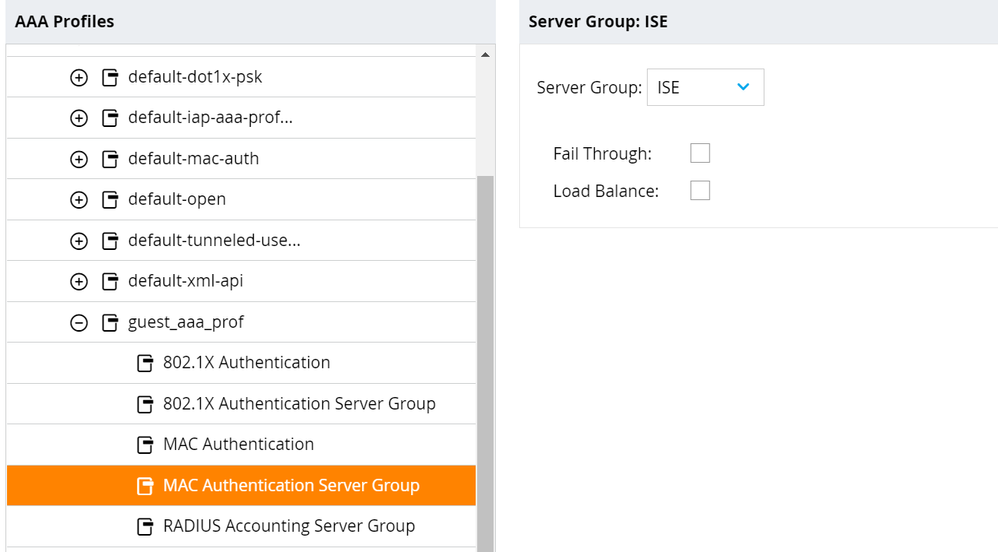
- Select MAC Authentication Server Group. Change Server Group to the ISE Server Group created previously. Click Submit.
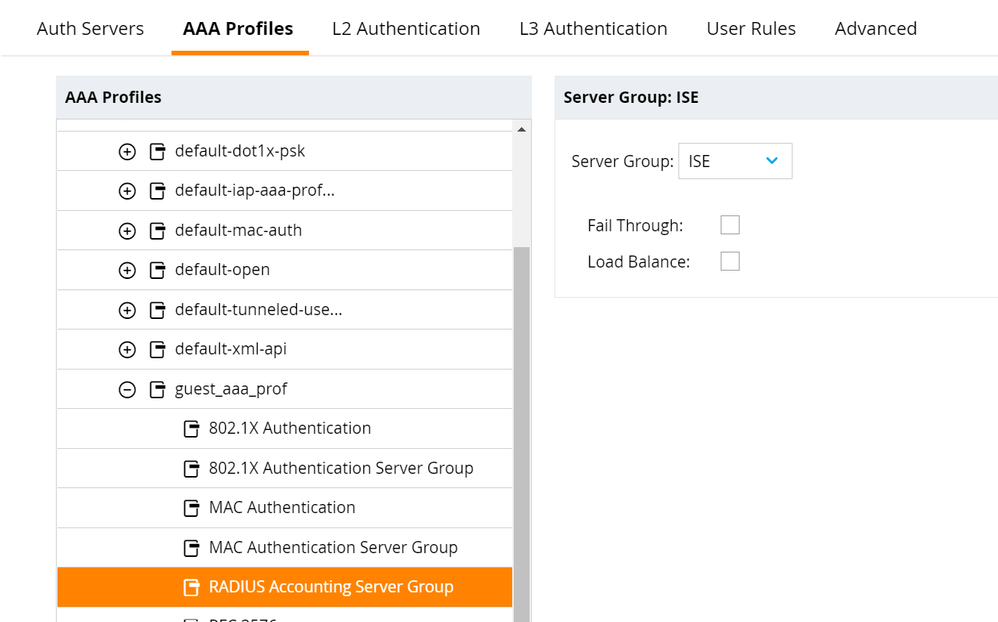
- Select RADIUS Accounting Server Group. Change Server Group to the ISE Server Group created previously. Click Submit.
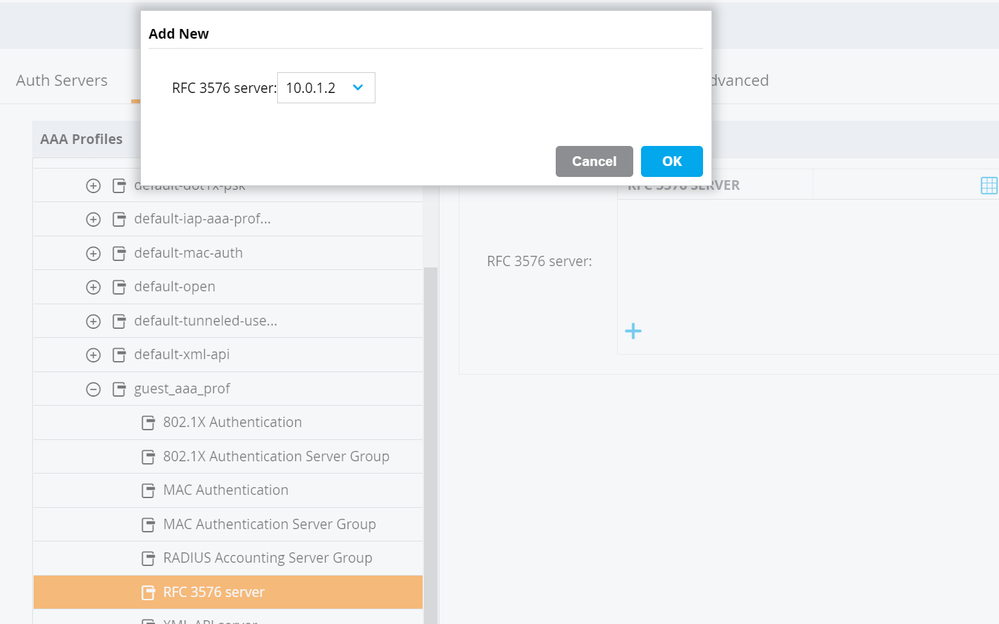
- Select RFC 3576 Server. Click the + button and select the ISE PSN from the drop down. Click Submit. Repeat for each of the ISE PSN RFC 3576 server definitions.
- Click Pending Changes in the top right and click Deploy changes to deploy the configuration to the Mobility Controller.
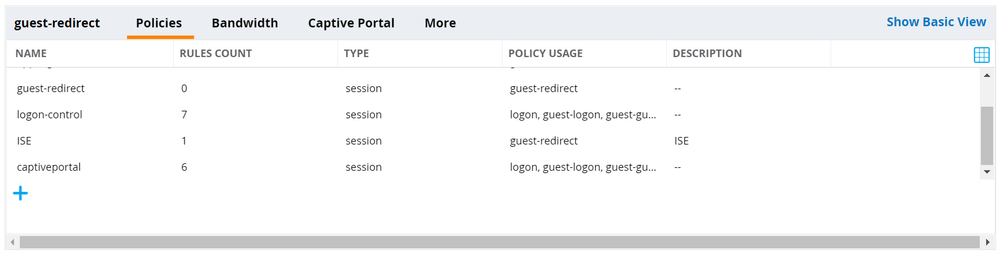
Role & Policy Configuration
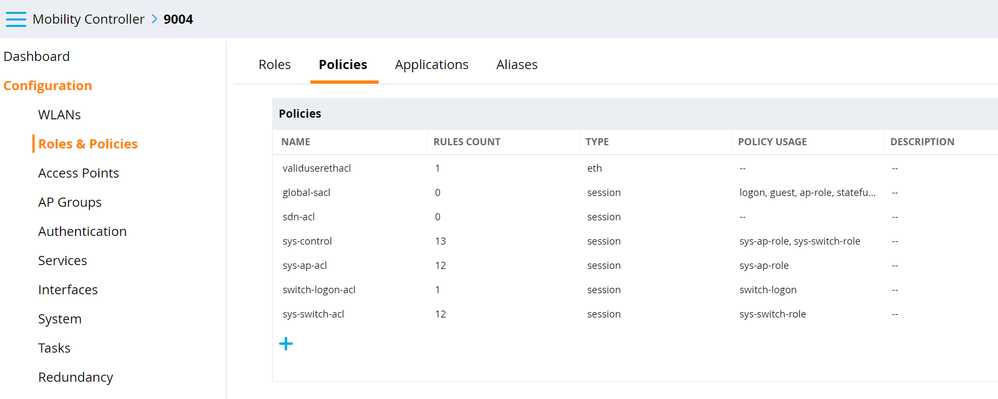
- Navigate to Configuration > Roles & Policies > Policies and click the + button.
- Set Policy Type to Session, enter a Policy Name, and an optional description. Click Submit.
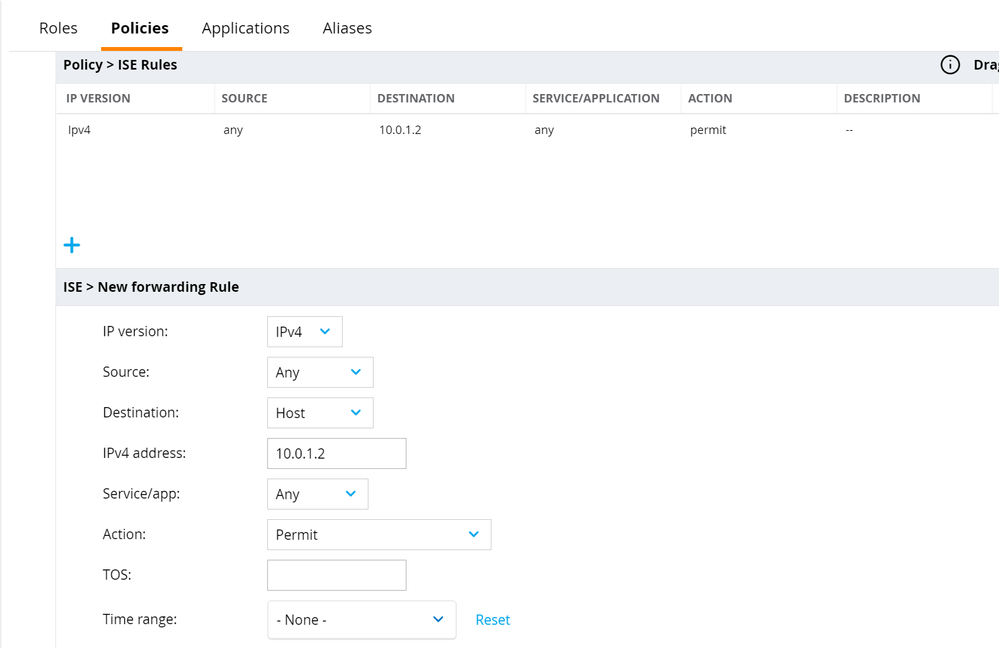
- Select the newly created policy and click the + button. Select Access Control and click OK. Create a new forwarding rule allowing captive portal traffic to the ISE PSNs. Click Submit.
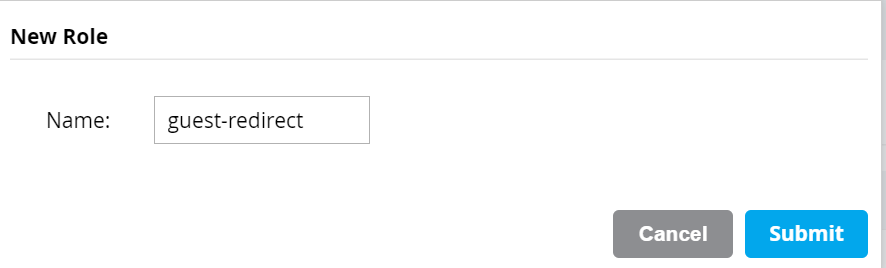
NOTE: This Policy enforces what traffic from the guest WLAN will be allowed BEFORE the guest authenticates to the portal. This Policy can and should be customized for the individual network environment and security requirements. At a minimum, the captive portal ports (typically 8443) must be allowed from the guest users to the ISE PSNs during the redirect phase. - Navigate to Configuration > Roles & Policies > Roles and click the + button to create a new role. Give the Role a Name and click Submit.
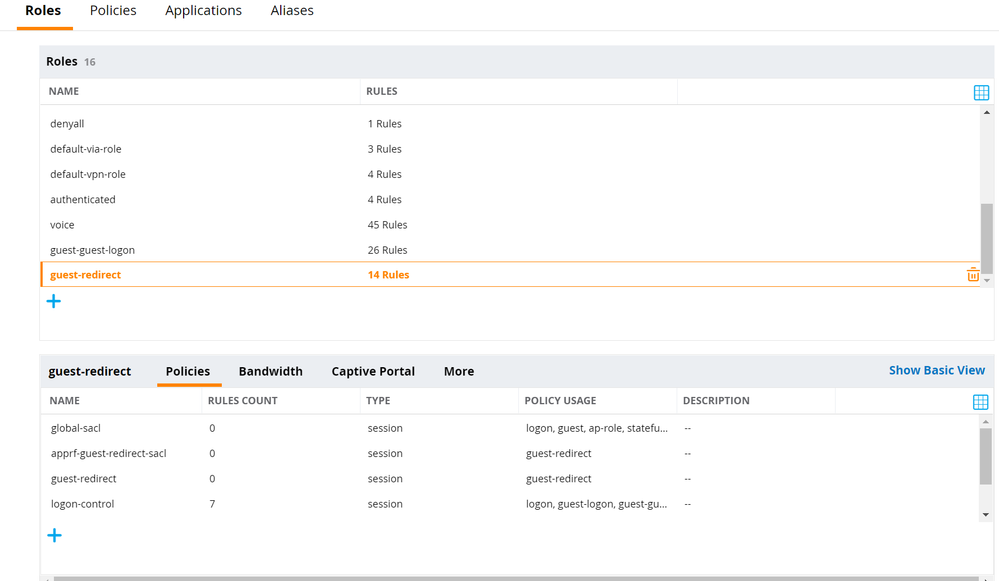
- Select the newly created Role from the list. Click Show Advanced View.
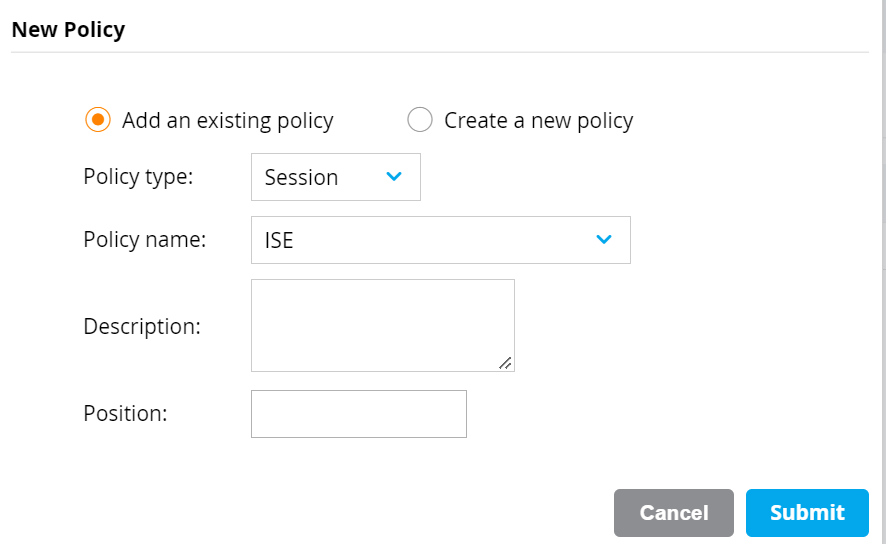
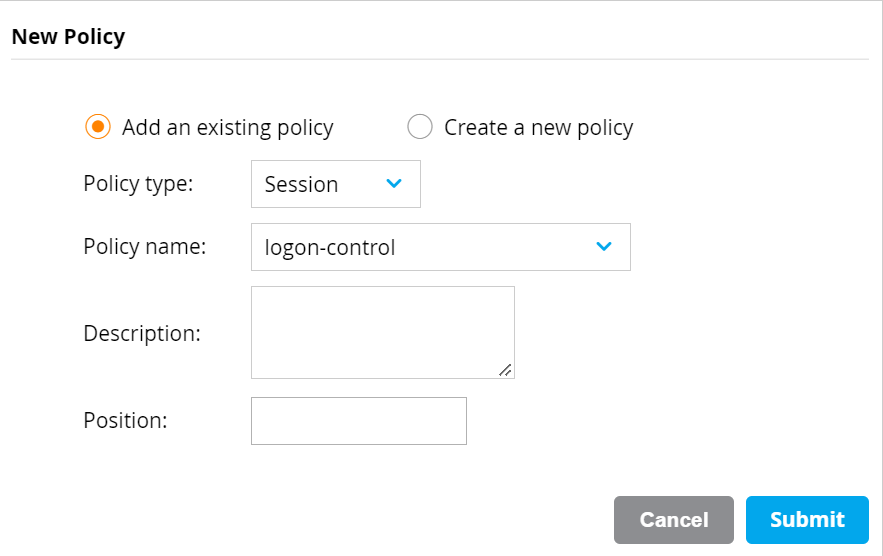
- Click the + button within Policies. Select Add an existing policy. Select type Session and select the policy created in the previous step. Click Submit.
- Repeat this procedure again adding the logon-control and captiveportal Policies to this Role.
- Re-order the policies so that the Policy created previously is listed between logon-control and captiveportal.
- Select the Captive Portal tab. Move slider to Internal Captive Portal, no auth or registration.
The Internal Captive Portal will not be used here and will be overridden by the captive portal URL supplied by ISE through the Aruba-Captive-Portal-URL VSA. However, the Aruba Mobility Controller requires some form of Captive Portal to be enabled on the Role to successfully redirect clients.
- Click Submit.
- Click Pending Changes in the top right and click Deploy changes to deploy the configuration to the Mobility Controller.
You may also wish to create a custom role for the guest users once the user successfully authenticates to the Captive Portal. In this example, the Aruba default guest Role is used for this purpose.
Cisco ISE
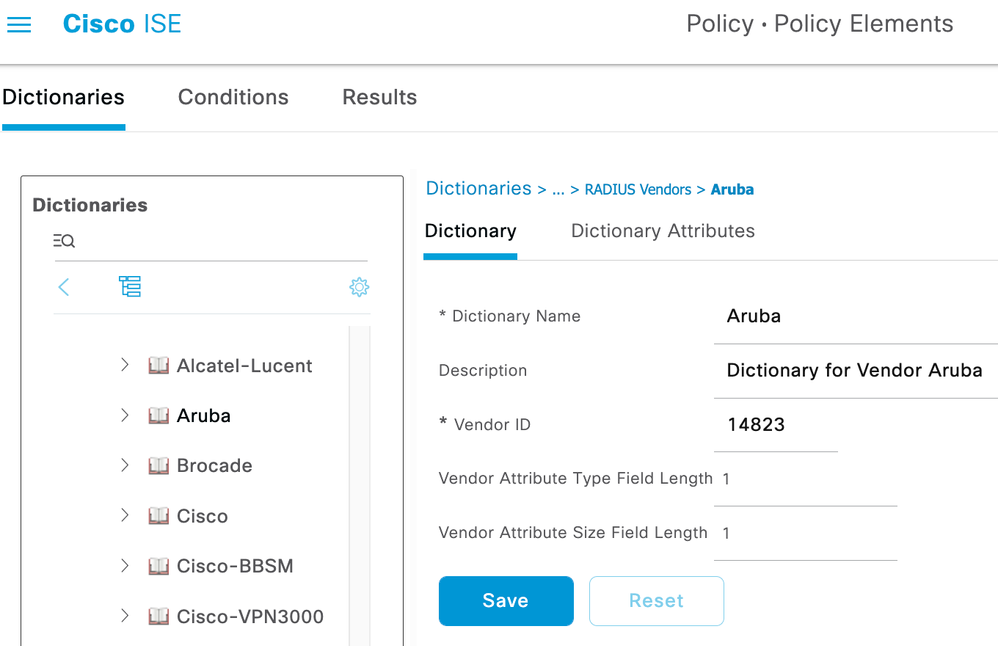
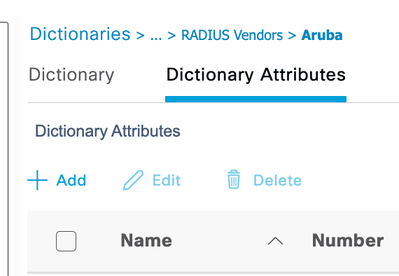
Aruba RADIUS Dictionary Addition
The default Aruba RADIUS dictionary in Cisco ISE does not contain the RADIUS VSA Aruba-Captive-Portal-URL. This must be manually created before configuring the network device profile.
- Navigate to Policy > Policy Elements > Dictionaries.
- Expand System > RADIUS > RADIUS Vendors and click on the Aruba entry.
- Click Dictionary Attributes and then Add.
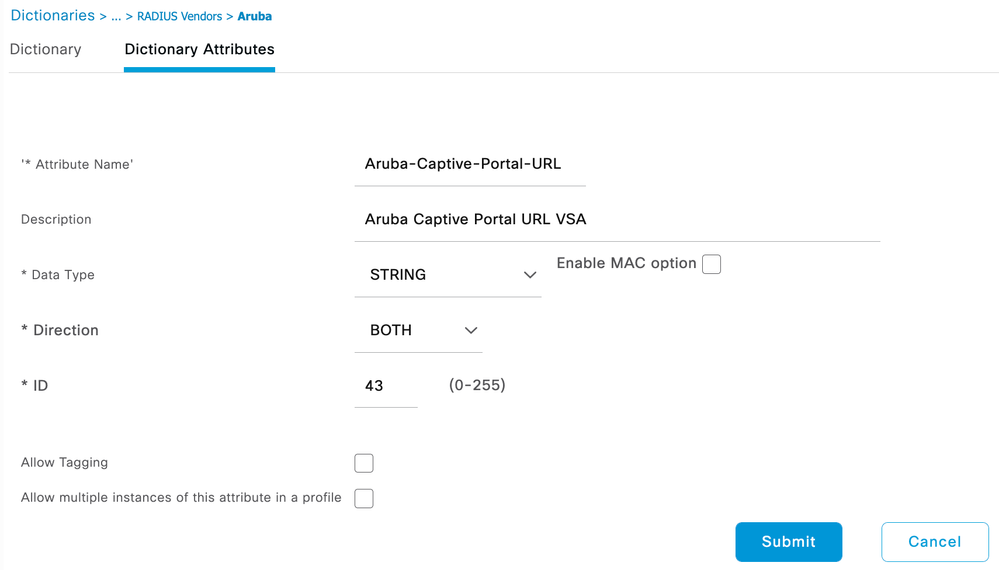
- Fill in the information as follows:
Attribute Name: Aruba-Captive-Portal-URL
Description: [optional]
Data Type: STRING
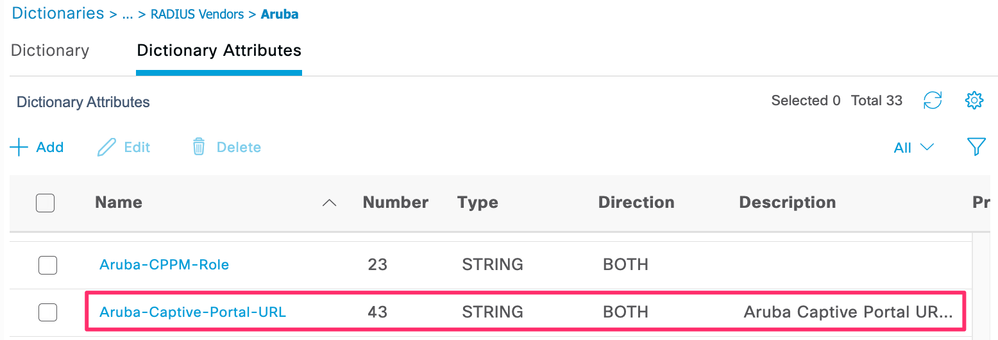
ID: 43 - Click Submit and verify the new attribute shows up under the Dictionary Attributes menu.
Aruba Network Device Profile
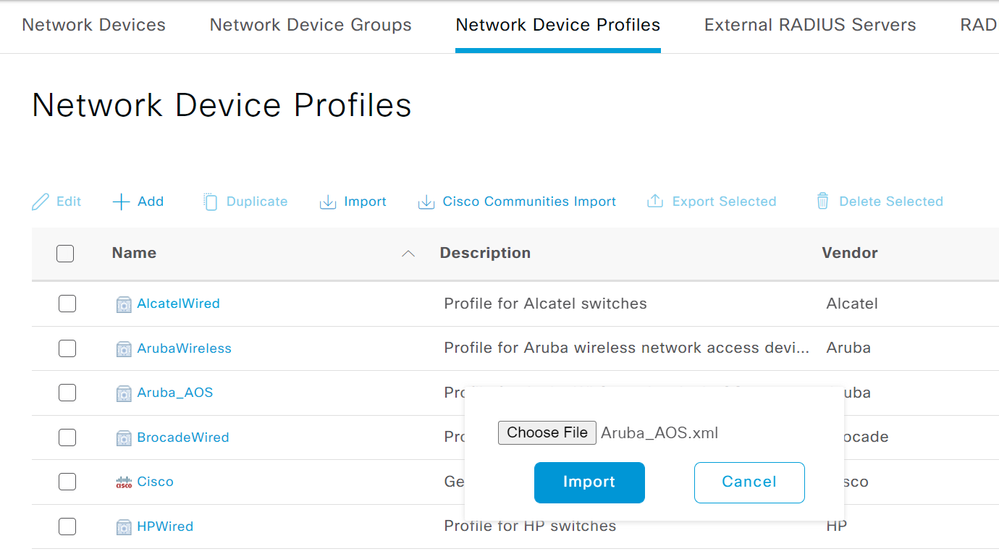
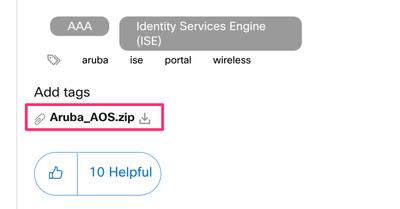
The default Aruba Network Device Profile in Cisco ISE does not support URL redirection via RADIUS VSA. A custom Network Device Profile for Aruba AOS controllers has been created and is attached to this article.
- Navigate to Administration > Network Resources > Network Device Profiles. Click the Import button. Browse the Aruba_AOS.xml file and click Import.
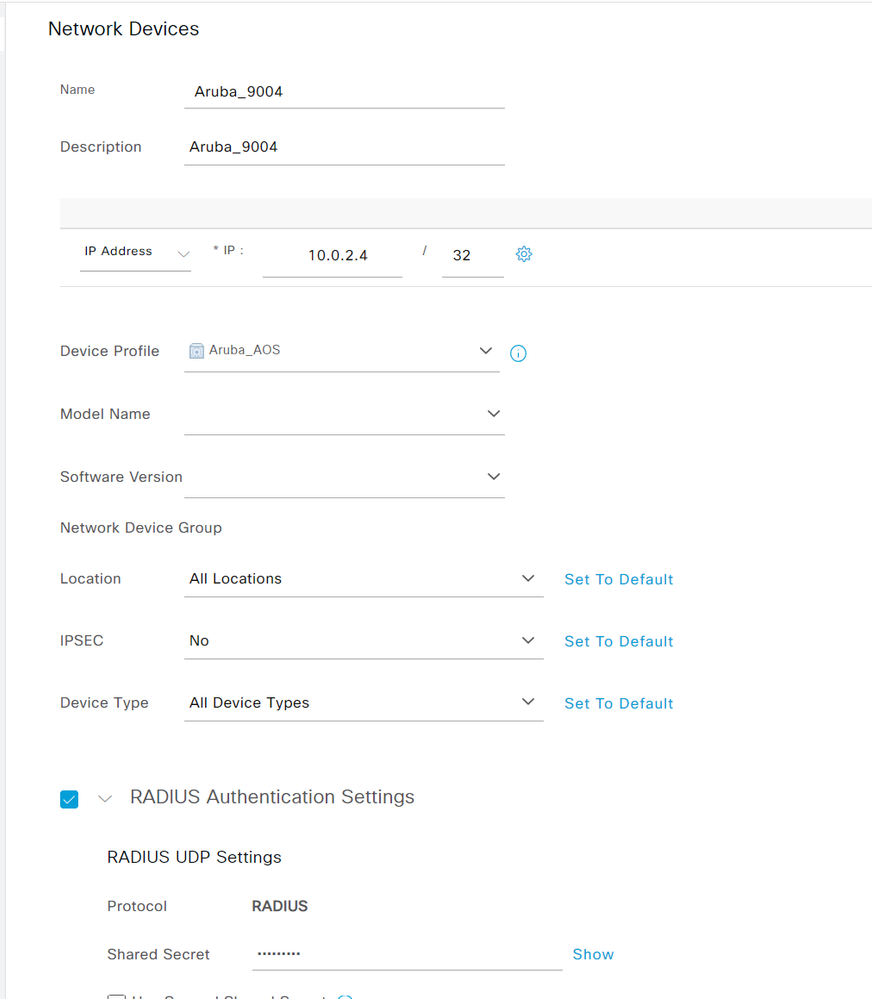
- Navigate to Administration > Network Resources > Network Devices and click the +Add button.
- Add an entry for the Aruba Mobility Controller ensuring to select the custom Aruba_AOS Network Device Profile imported in the previous step. Specify the IP Address of the Mobility Controller and the RADIUS Shared Secret.
- Click Save.
Aruba Authorization Profiles
- Navigate to Policy > Policy Elements > Results > Authorization > Authorization Profiles.
- Click the +Add button.
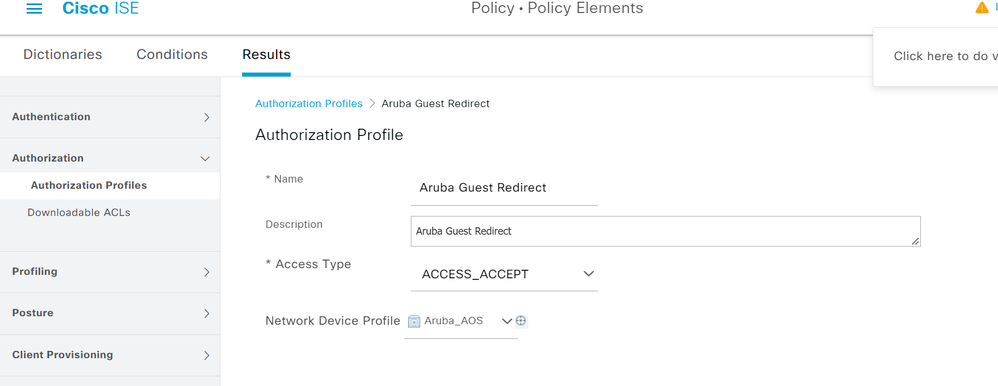
- This authorization (authz) profile will be for redirecting the unknown guest user.
- Give the authz profile a name, select Aruba_AOS as the Network Device Profile.
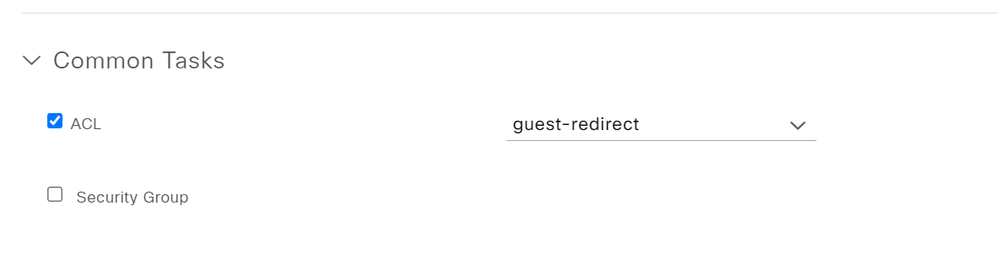
- Within Common Tasks click the checkbox for ACL and specify the name of the Role created for the redirect on the Aruba Mobility Controller. NOTE: these names much match exactly.
- Check the box for Web Redirection and specify the corresponding portal type and portal. Click Save.
This guide does not cover the creation of a portal on ISE. For this example, the Default Hostspot Guest Portal is used.
- Click the +Add button again.
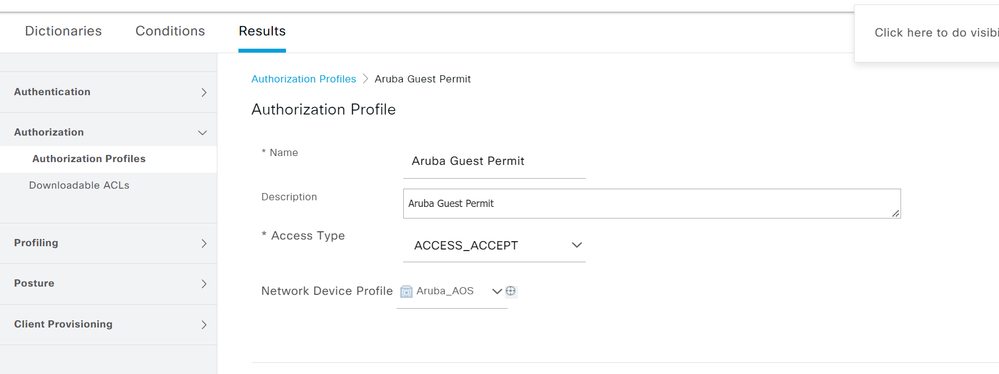
- This authorization profile is for the authenticated guest.
- Give the authz profile a name, select Aruba_AOS as the Network Device Profile.
- Within Common Tasks click the checkbox for ACL and specify the name of the Role for the guest users on the Aruba Mobility Controller.
NOTE: these names much match exactly. You may also wish to create a custom role for the guest users once the user successfully authenticates to the Captive Portal. In this example, the Aruba default guest role is used for this purpose.
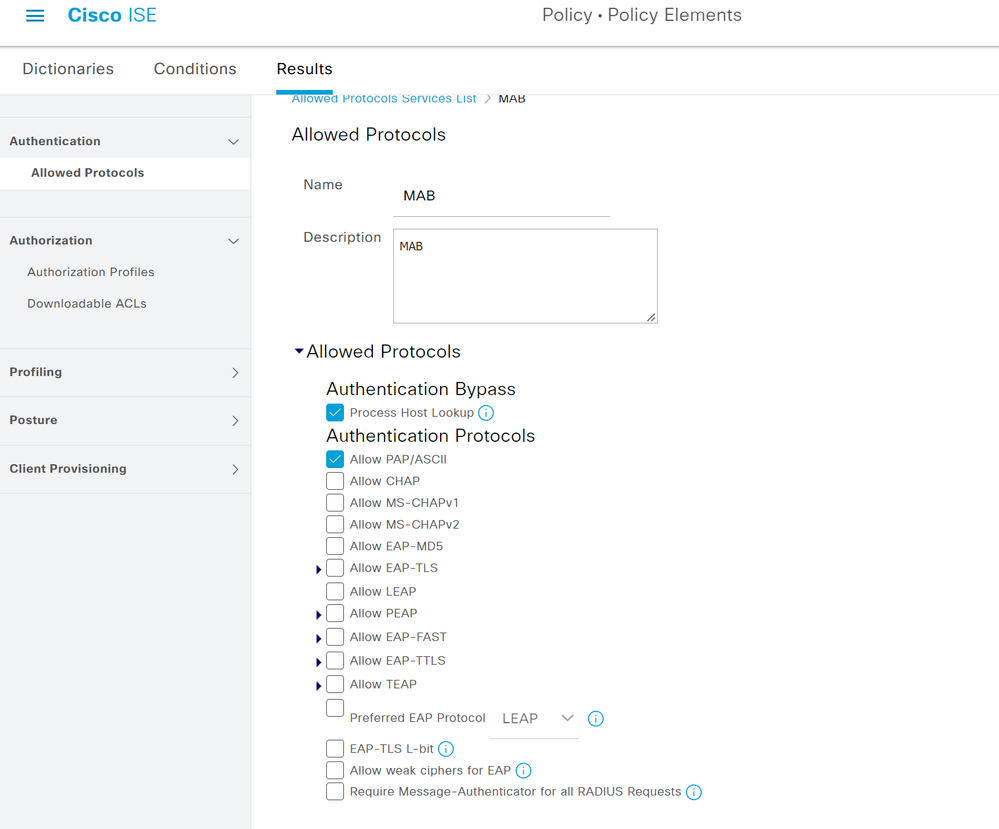
Authentication Allowed Protocols Configuration
- Navigate to Policy > Policy Elements > Results > Authentication > Allowed Protocols. Click the +Add button to create a new Allowed Protocols Service.
- Give the Allowed Protocols Service a name and optional description. Disable all other protocols except for Process Host Lookup and PAP/ASCII. Click Save.
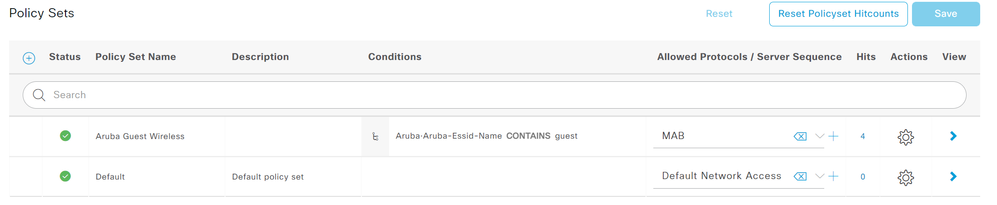
Policy Set Configuration
- Navigate to Policy > Policy Sets and click the + button to create a new policy set.
- Give the policy set a name and within conditions, specify Aruba-Aruba-Essid-Name CONTAINS [SSID].
- Replace [SSID] with the name of the SSID configured on the Mobility Controller.
- Replace [SSID] with the name of the SSID configured on the Mobility Controller.
- For Allowed Protocols/Server Sequence, select the MAB allowed protocols created in the previous section.
- Click Save and then click the greater than sign (>) on the far right of the policy set to open the new Policy Set.
- Expand Authentication Policy and specify Internal Endpoints in the Use column of the Default authc policy.
- Change If User not found within Options to Continue.
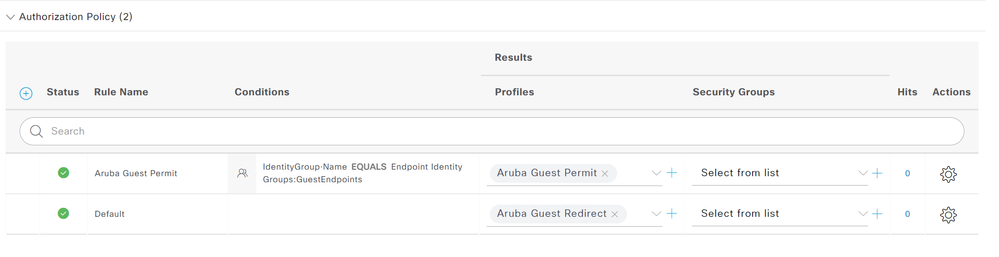
- Expand Authorization Policy and click the plus (+) button to create a new authz policy.
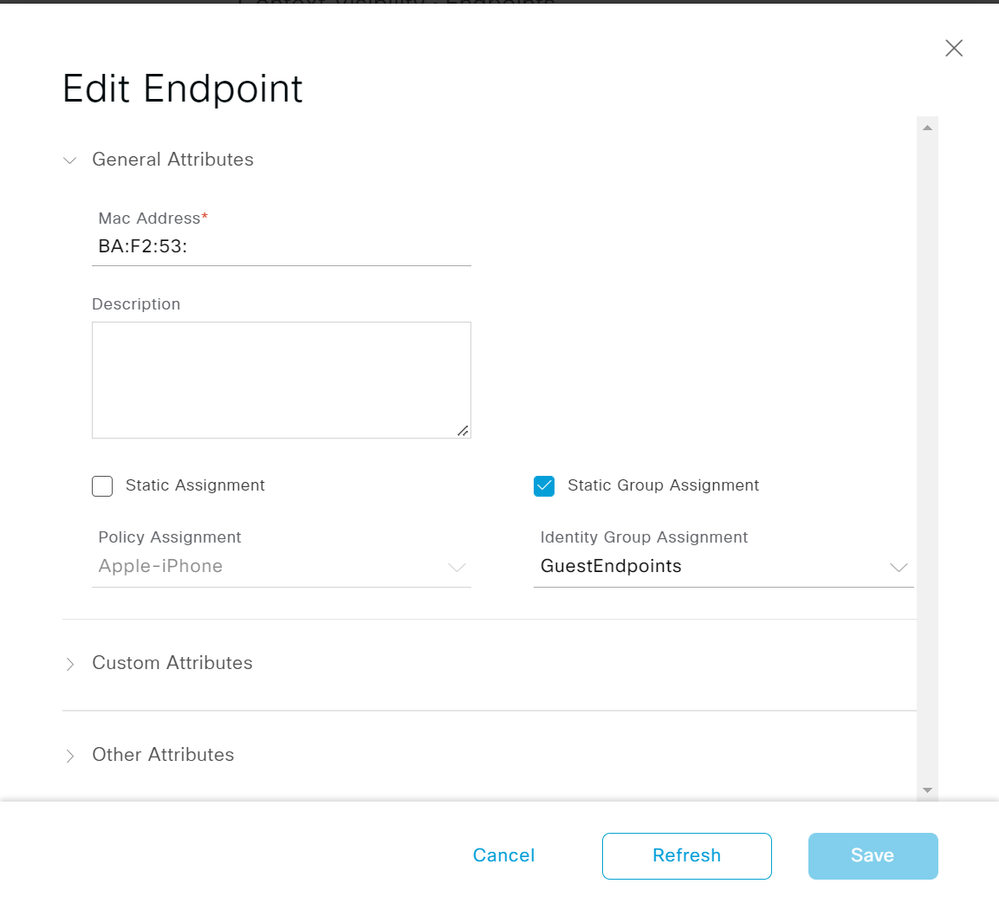
- Specify a name for the policy and for Conditions specify IdentityGroup-Name EQUALS Endpoint Identity Groups:GuestEndpoints.
- This guide is using the Remember Me guest flow so if the endpoint MAC address exists in the specified endpoint group they will automatically be granted guest access.
- Specify the Aruba Guest Permit authorization profile in the Results column.
- Specify the Aruba Guest Redirect authorization profile in the Results column for the Default authz policy.
- Click Save.
Verification
ISE RADIUS Live Logs
Navigate to Operations > RADIUS > Live Logs. From bottom to top in the screenshot below, the Live Logs should first show the Aruba Guest Redirect authz profile. Followed by the Change of Authorization (CoA) once the user logs into the captive portal. Finally, the endpoint re-authenticating to the wireless network and receiving the Aruba Guest Permit authz profile.
The endpoint should also be a member of the GuestEndpoints Group within Context Visibility > Endpoints after logging into the captive portal.
Aruba Mobility Controller
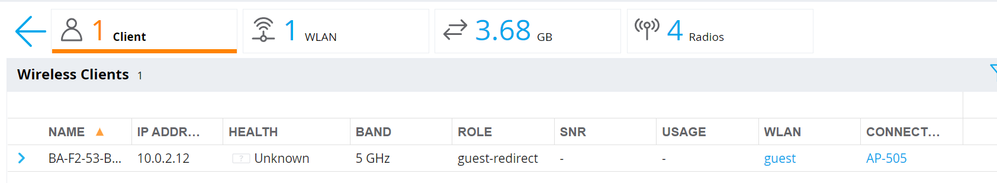
Navigate to Dashboard > Overview and click on the clients view. Before authentication to the captive portal, the client should be assigned the guest-redirect role.
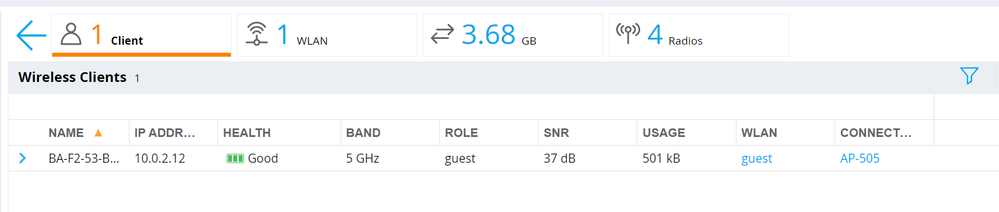
After authentication to the captive portal, the client should be assigned the guest role.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Do you have this in PDF form, please?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
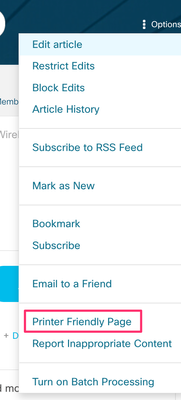
You can generate a printer friendly version by going to the top-right of the page, click Options > Printer Friendly Page.
From there you can print to PDF.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks, @bradjohnson.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi,
Is it possibile to make setup like this but using built-in "Guest_Flow" condition instead of relying on GuestEndpoints group?
Will ISE recognize "Guest_Flow" for third party NAD like Aruba?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Dear,
May I know where to download "Aruba_AOS.XML" file?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks @bradjohnson
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi,
First, thank you for the sharing. But I have a quesiton for you.
For the "initial role" and "mac authentication defaul role" in "guest_aaa_prof", it's "guest-guest-logon".But the user role defined is "guest-redirect". May I confirm with you if the "initial role" and "mac authentication defaul role" is "guest-redirect" in "guest_aaa_prof" ?
Looking forward to your early reply.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks for your reply. May I know whether the defined user role "guest-redirect" will be associated with aaa profile ?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
It does not. The role just must be defined on the controller and the name must match EXACTLY with what is pushed in the VSA from ISE.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thank you. I completed the configuratin and met the issue that the redirect URL didn't work on the client side. From the tcpdump packet, the attribute "Aruba-Captive-Portal-URL" was shown unknon attribute in the radius. Do you have any idea of this ?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Did you import the XML Network Device Profile into your ISE deployment? Did you assign that Network Device Profile to the definition for your Mobility Controller? What version of AOS?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Yes, the XML was imported and associated to network devices (Aruba Controllers). The AOS is version 8.6.0.9. I am not sure if the XLM file can support AOS 8.6.0.9 ? I saw the testing environment is running on AOS 8.10.0.1.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
That shouldn't matter as the RADIUS VSA Aruba-Captive-Portal-URL was added to ArubaOS 8.4. That's why we noted in the XML that it was for ArubaOS 8.4+. On your wireless controller, is it showing the VSA as unknown and rejected or rejecting because it contains invalid information?
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: