- Create your new custom Active Directory attribute (refer to Microsoft documentation for further detail). For this example, I created a new AD attribute called "SGT".
- Set the value for your custom attribute. For this example, I set SGT="Docs"

- On ISE, navigate to Administration->Identity Management->External Identity Sources->Active Directory<Select your AD server>.
- Select the Attributes tab and click "Add Attribute" to add your custom attribute
- Navigate to Policy->Policy Sets-> <policy set name>->Authorization Policy and select/create an authorization policy.
- Using the condition studio attribute editor, select use your custom attribute as a policy condition

- Set the attribute value.

-
Click Use. Finish configuring the authorization policy and click Save
____________________________________________________________________________________
The solution above uses an attribute value in AD as a condition in authorization rules resulting in assigning an SGT.
As such, multiple authorization rules are required to assign different SGTs.
Use the following method if you would like to dynamically assign the SGT as specified within the AD user attribute.
1) Choose an existing unused attribute in AD user (supporting text) or add a new attribute for this use.
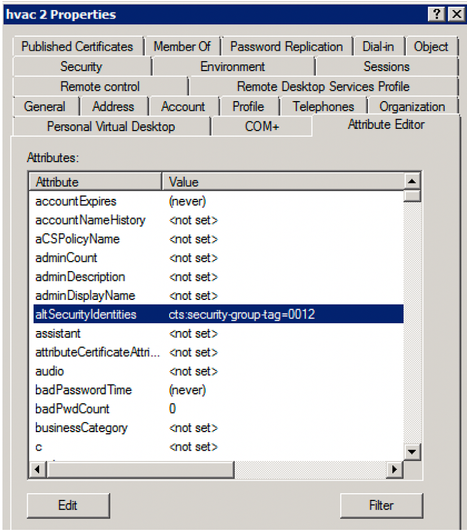
Below I have chosen the existing alt.SecurityIdentities AD attribute.
Edit the value of that user's attribute and enter what ISE would use to assign an SGT within the authorization success AV pair:
Enter "cts:security-group-tag=xxxx" where xxxx is in hex so SGT 18 for HVAC is 12:
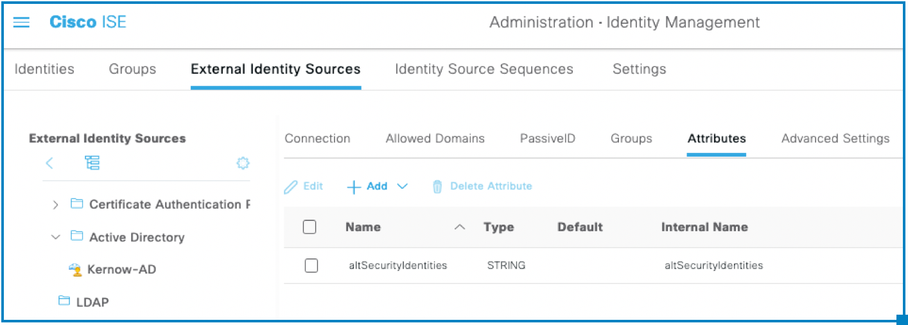
2) In ISE, retrieve that attribute from AD to use in the authorization process:
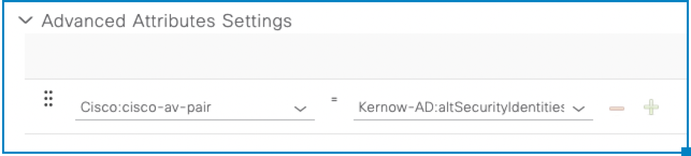
3) In the ISE authorization profile, add a custom attribute as shown below:
4) Now, when that user (hvac2) authenticates, it gets assigned the SGT as configured within the AD attribute.
Attribute shows up in ISE authorization accept:

SGT within auth session for the user:
Kernow-Cat9300-b#sh auth sess int g1/0/1 det
Interface: GigabitEthernet1/0/1
IIF-ID: 0x1D2E8A50
MAC Address: 0050.568f.784f
IPv6 Address: fe80::cc34:7361:cd10:ac53
IPv4 Address: 10.6.5.100
User-Name: hvac2
Device-type: Microsoft-Workstation
Device-name: MSFT 5.0
Status: Authorized
Domain: DATA
Oper host mode: multi-auth
Oper control dir: both
Session timeout: N/A
Acct update timeout: 172800s (local), Remaining: 172759s
Common Session ID: 0219040A0000003718413DB7
Acct Session ID: 0x000000cd
Handle: 0xae00002c
Current Policy: PMAP_DefaultWiredDot1xOpenAuth_1X_MAB
Local Policies:
Server Policies:
Vlan Group: Vlan: 1021
SGT Value: 18
Method status list:
Method State
dot1x Authc Success
Outcome: One ISE authz rule required to assign many different SGTs, based on an attribute within the AD user entry.