- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- Cisco Remote Workforce Solution-Wireless
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
08-24-2020 09:28 AM - edited 07-02-2021 09:41 PM
Table of Contents
Use Case: Teleworker with Wireless Devices
Cisco Wireless LAN Controllers
Cisco Teleworker Access Points
Cisco AP (Teleworker) Workflow
Steps Required to Configure Teleworker AP
Configure Flex-Profile for Teleworker AP
Configure AP Join Profile for DTLS encryption
Configure Site Tag for Teleworker AP
Cisco Network Plug and Play (PnP) for Teleworker Deployment
Cloud Plug and Play Connect redirect to WLC
Cloud Plug and Play Device Provisioning
Create a Controller Profile
Adding Cisco Access Point to the Devices List
Adding WLANs/RLANs to a Policy Tag
Split Tunneling for Teleworker AP
Assigning the Split ACL on Flex Profile
Assign the ACL as the Split mac ACL on policy profile
Cisco Catalyst C9105W as Teleworker Access Point
Connecting Cisco Teleworker Access point
Teleworker Assurance from Cisco DNA Center
Technology Use Case
Providing employees access to corporate network and services from a remote environment poses challenges for both the end user and IT operations. For the home-based teleworker, it is critical that access to business services be reliable, consistent and secure, providing an experience that is as similar as office in the organization's facility. In addition, the solution must also support a wide range of teleworking employees who have varying skill sets, making it critical to have a streamlined and simplified way to implement the teleworker solution.
Cisco Teleworker Access Point provides secure communications from a controller to an access point at a remote location, seamlessly extending the corporate WLAN over the Internet to an employee's residence. The user's experience at the remote location is the same as it would be at the corporate office. Datagram Transport Layer Security (DTLS) encryption between the access point and the controller ensures that all communications have the highest level of security. Users may also need access to Cloud Applications (for e.g. Office365, AWS etc.) so it's important to also have a direct access to cloud with Teleworker AP (split tunneling) option.
Use Case: Teleworker with Wireless Devices
Teleworkers require always-on secure access to networked business services from a remote home office. Wireless access provides easy mobility and setup within the home office, and consistent device configuration allows for easy mobility between the home office and on site at the corporate location.
This design guide enables the following network capabilities:
-
Common wireless device configuration for onsite and teleworker wireless access
-
Authentication through IEEE 802.1X for employees and encryption for all information sent and received to the organization’s main location
-
Simplified IT provisioning for the home office, which reduces setup time and supports varying levels of end-user skills
-
Mobility and flexibility for voice endpoints at the teleworker location
Design Overview
The Cisco Teleworker solution is based on Cisco OEAP (OfficeExtend AP) feature which is specifically designed for a teleworker, who primarily uses wireless devices. The solution consists of the following components:
Cisco Aironet Access Point
All 11ac wave2 (indoor) - OEAP1810, 1810W,1815T/W/I, 1830,1840,1850 Series 2800/3800/4800 Series AP
Cisco Catalyst Access Points
All Cisco Catalyst C9100 Series APs
Cisco C9800 Wireless LAN Controller
C9800-CL (Private Cloud), C9800-L, C9800-40, C9800-80
Recommended Software 17.3 release
Cisco AireOS Wireless LAN Controller
CT-3504, 5520, 8540
Recommended Software 8.10MR3 release
Deployment Components
The Teleworker deployment is built around three main components: Cisco wireless LAN Controllers, Cisco Access Points and Corporate Firewall
Cisco Wireless LAN Controllers
Cisco wireless LAN controllers are responsible for system-wide WLAN functions, such as security policies, intrusion prevention, RF management, quality of service (QoS), and mobility. They work in conjunction with Cisco Teleworker Access Points to support business-critical wireless applications for teleworkers. Cisco wireless LAN controllers provide the control, scalability, security, and reliability that network managers need to build a secure, scalable teleworker environment.
To allow users to connect their corporate devices to the organization's on-site wireless network, the Cisco teleworker solution offers the same wireless Secure Set Identifiers (SSIDs) at teleworker's home as those that support data and voice inside the organization.
Cisco Teleworker Access Points
Cisco has dedicated Teleworker APs like OEAP1810 and 1815T but mostly all Cisco APs can run the teleworker/OEAP functionality. Teleworker APs require a centralized Wireless LAN Controller, as the Access Point communicates with the WLC resources, it will download its configuration and synchronize its software/firmware image, if required. Cisco Access Points establishes a secure Datagram Transport Layer Security (DTLS) connection to the controller to offer remote WLAN connectivity using the same profile as at the corporate office. Secure tunneling allows all traffic to be validated against centralized security policies and minimizes the management overhead associated with home-based firewalls.
Cisco Teleworker access points delivers full 802.11ac and 802.11ax wireless performance and avoids congestion caused by residential devices because it operates simultaneously in the 2.4-GHz and the 5-GHz radio frequency bands. Cisco Teleworker Access Points usually connected to a NATed home-router environment, provides wired and wireless segmentation of home and corporate traffic, which allows for home device connectivity without introducing security risks to corporate policy.
Corporate Firewall
The Wireless LAN Controller and Access Points communicate through CAPWAP protocol and when a WLC is placed in a DMZ behind a corporate firewall then it must allow CAPWAP Control and CAPWAP Data traffic through the firewall to the Wireless LAN Controller in order to establish the communication.
Note: The CAPWAP control port (UDP 5246 ) and CAPWAP data port (UDP 5247) needs to be opened on the firewall for communication between the Wireless LAN controller and the Cisco Teleworker Access Points.
Design Models
For the most flexible and secure deployment of Cisco Teleworker solution deploy a dedicated controller using Cisco Catalyst 9800 Series Controllers or Cisco AireOS Wireless Controllers. In the dedicated design model, the controller is directly connected to the Internet edge demilitarized zone (DMZ) and traffic from the Internet is terminated in the DMZ versus on the internal network, while client traffic is still directly connected to the internal network.
Figure 1. Cisco Teleworker Design Model
Cisco AP (Teleworker) Workflow
The following steps describe the workflow carried out by the admin and teleworker to connect the Teleworker Access Point to the corporate Wireless LAN Controller:
-
Admin acquires the AP inventory recorded before shipping to employee.
-
Admin can utilize Cisco Network Plug & Play from software.cisco.com to provision the access points with WLC IP address.
-
Admin can provide teleworker with an Access Point primed with the IP address of the corporate Wireless LAN controller. Alternatively, the teleworker/employee can prime the Access Point by entering the IP address of the Wireless LAN Controller in the local configuration screen of the Access Point.
-
The teleworker connects the WAN port (on OEAP1810 & 1815T Models) dedicated Teleworker Access Point or PoE LAN port (on other AP models) to one of the home internet router LAN interfaces.
-
The Access Point will obtain an IP address from the home internet router and will initiate a join request to the corporate Wireless LAN Controller
-
After the Access Point joins the corporate Wireless LAN Controller, it can advertise the corporate SSID, extending the same security methods and services across the WAN to the teleworker’s remote home location.
-
If Remote LAN (RLAN) is configured on Wired LAN ports of the Supported Access Points (OEAP1810,1815T,1815W,1850,2800, 3800 and C9105W) then the devices can be connected to the corporate network via the Wired LAN ports
-
Teleworker can additionally configure a Personal SSID on the Access Point for home wireless network. This personal SSID is strictly private and is not monitored by the network admin. The Personal SSID can be used as home network SSID for connecting devices.
Steps Required to Configure Teleworker AP
-
Configure WLC C9800 for NAT
-
Configure Flex-Profile for Teleworker AP – to enable OEAP option
-
Configure AP Join Profile – For DTLS encryption and Priming AP
-
Configure Site Tag for Teleworker AP
-
Tag the AP before AP Joins
-
Setup Cisco Network Plug and Play (PnP) for ease of deployment.
Configure WLC C9800 for NAT
If the WLC management IP is configured with a Public IP address then NAT is not required. But the Internet edge firewall usually works as a Network Address Translation (NAT) device and translates the IP address of the WLC management interface in the DMZ to a publicly reachable IP address so Teleworker Access Point at employee location can reach the WLC. However, in order for the Access Point to communicate with the WLC, the publicly reachable address must also be configured on the WLC management interface. It is required to use 1:1 NAT mapping for the WLC’s IP address, meaning that the WLC’s private IP is mapped statically to a single public IP (no Port Address Translation is possible).
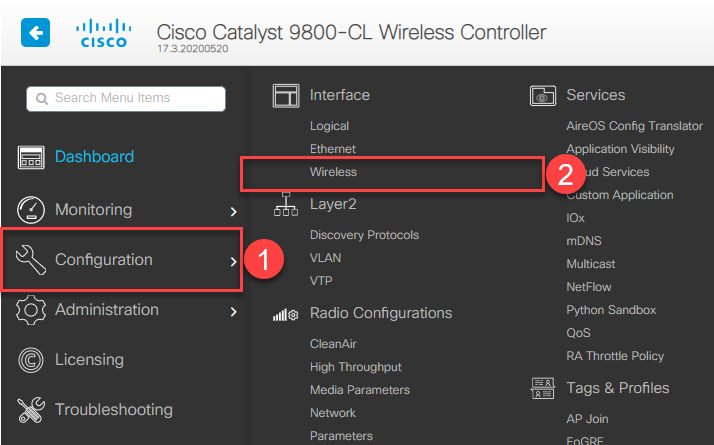
To configure the WLC for NAT, perform the following steps:
Step 1: On the C9800 WLC GUI navigate to Configuration → Interface→ Wireless
Step 2: Click on the Management interface to open the Edit Management Interface dialog box
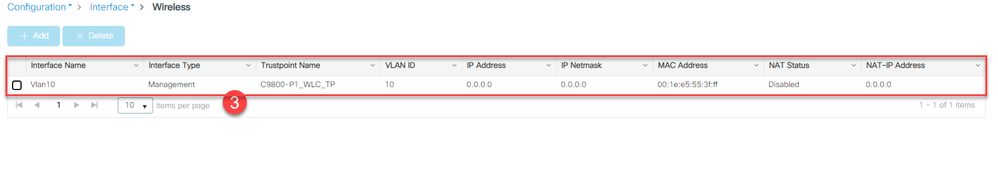
This opens the IP address box, to assign the Public NAT IP.
Step 4: Fill the Public IP of the WLC and From CAPWAP Discovery option select Private, Public or both
Private – This Includes private IP in CAPWAP Discovery Response. For Example: If WLC mgmt. IP is 10.10.10.3 and APs on corporate network can discover and join WLC through this management IP address.
Public – Includes public IP in CAPWAP Discovery Response. The public option allows WLC to advertise external IP and allows AP’s on Public network discover and join on Public IP of WLC.
Both options can be enabled as well. For WLC behind NAT make sure the Public IP is enabled.
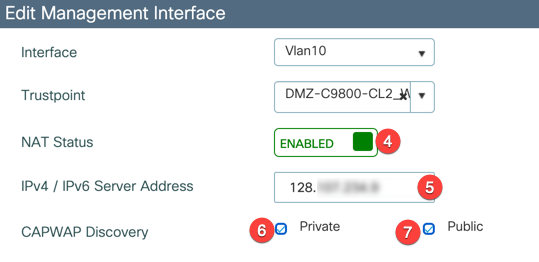
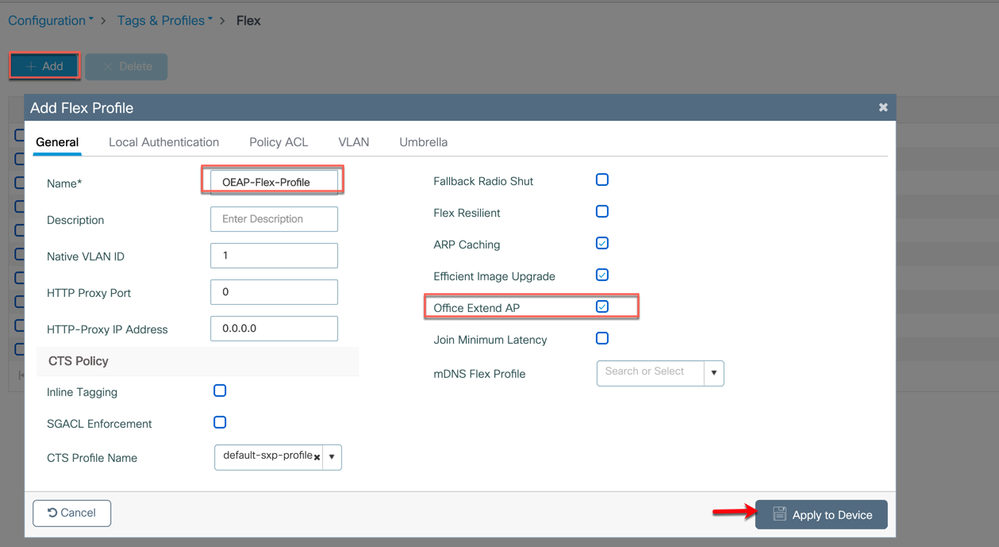
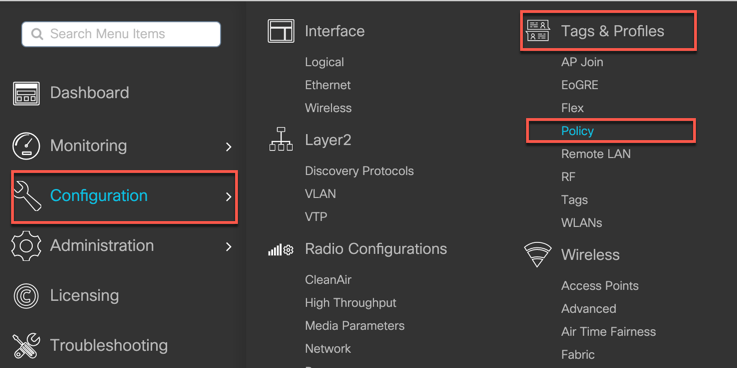
Configure Flex-Profile for Teleworker AP
The Office Extend configuration is part of flex profile so user either needs to create a custom flex profile or can use the default-flex-profile to enable it. This function will convert the APs to OEAP
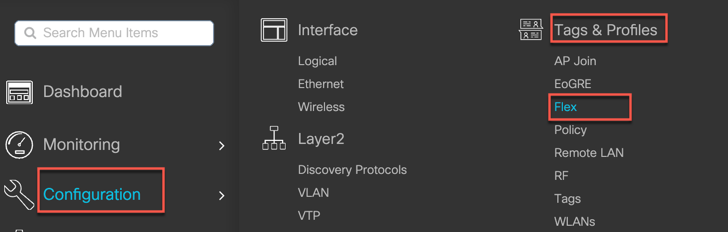
Step 5: Navigate to Configuration → Tags & Profiles → Flex and modify the default-flex-profile (or create a custom one by clicking +Add then Name the Flex Profile and then enable Office Extend AP by checking the box then click Apply
Note: The Access Point will reboot and after reboot, it will operate as a Teleworker/OfficeExtend Access Point.
Configure AP Join Profile for DTLS encryption
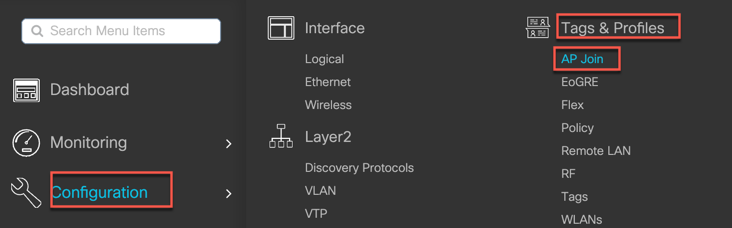
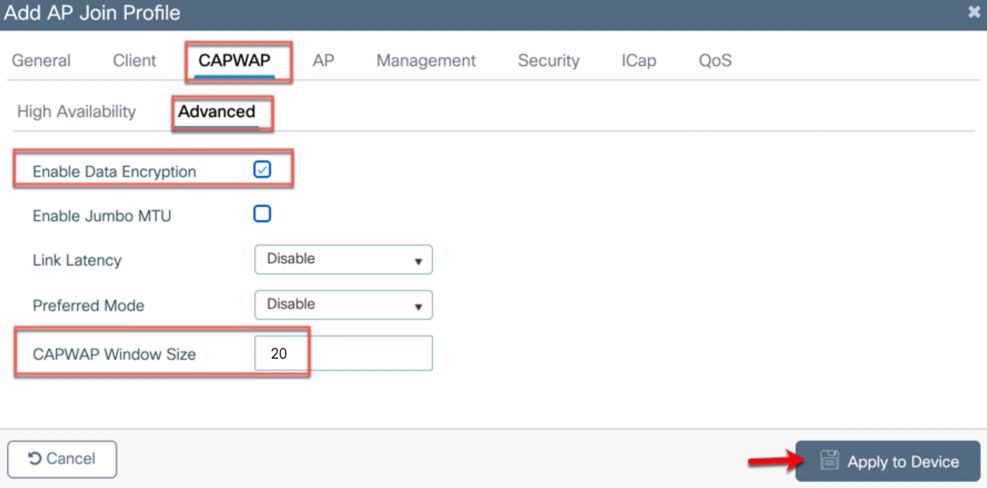
Step 6: Go to Configuration → Tags & Profiles → AP Join
Now create a new AP join profile specific for OEAP by clicking +Add, name the profile and go to tab CAPWAP> High Availability>Primary Controller configure the Name and IP Address of WLC.
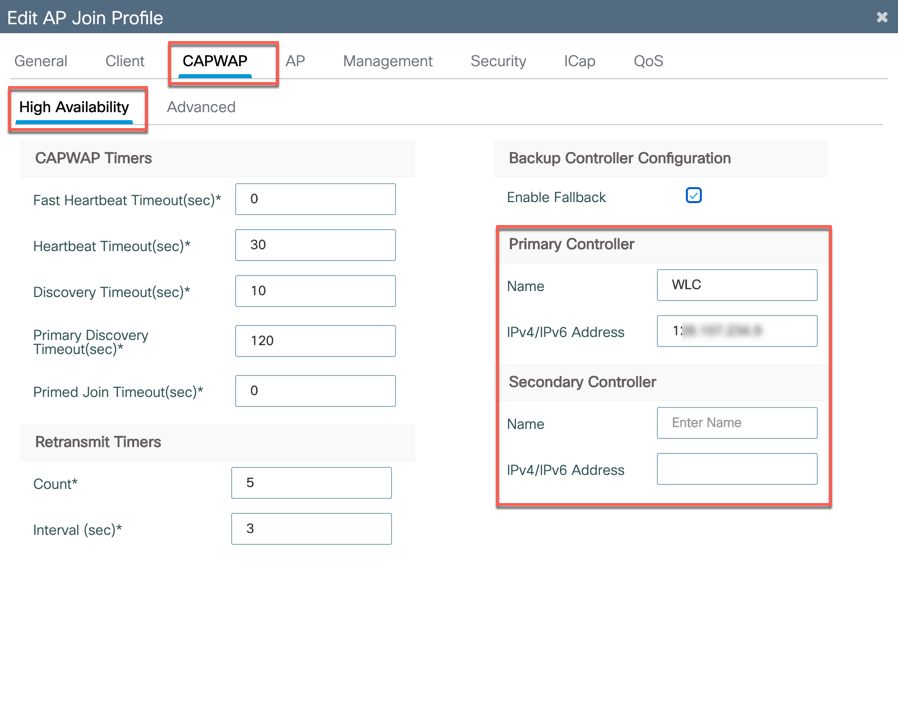
Go to Advanced tab and Enable Data Encryption by checking the box and then click Apply. This is to secure the traffic traversing the internet is encrypted.
Admin can also configure the CAPWAP Windows Size option which gives a high-performance boost for CAPWAP control in high latency links. Max value possible is 50 and the recommended value is 20
For example: It increases the AP image download time by at least 10 times
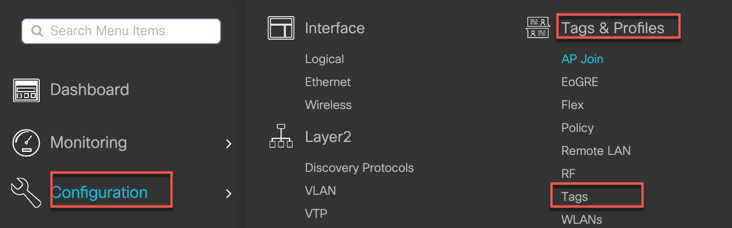
Configure Site Tag for Teleworker AP
OEAP mode is part of Flex profile and AP needs to be in flex connect mode for enabling the OEAP functionality, in order to do that the site tag needs to be configured for remote site.
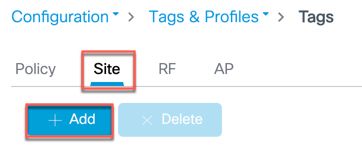
Step 7: Go to Configuration → Tags & Profiles → Tags → Site and click +Add a new Site tag for OEAP that is to be mapped to the Flex Profile from the previous step.
Make sure that Enable Local Site box is unchecked (this will convert the APs to FlexConnect when they inherit this tag). Then Name the site tag and select the AP Join Profile and Flex Profile then click Apply.
Tag the AP before AP Joins
Now the APs need to be tagged with the appropriate policy-tag, site-tag and rf-tag, once the APs join the WLC they can inherit those tags. There are multiple ways to associate tags to APs
Option 1: Admin can add the AP MAC manually along with the TAG names
Note: The AP MAC is the Ethernet MAC which is available on the AP label
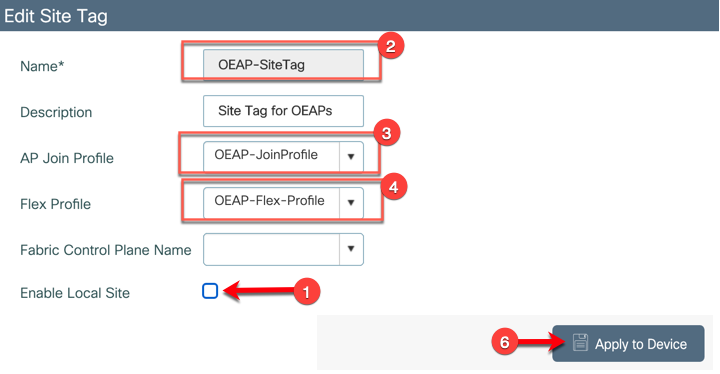
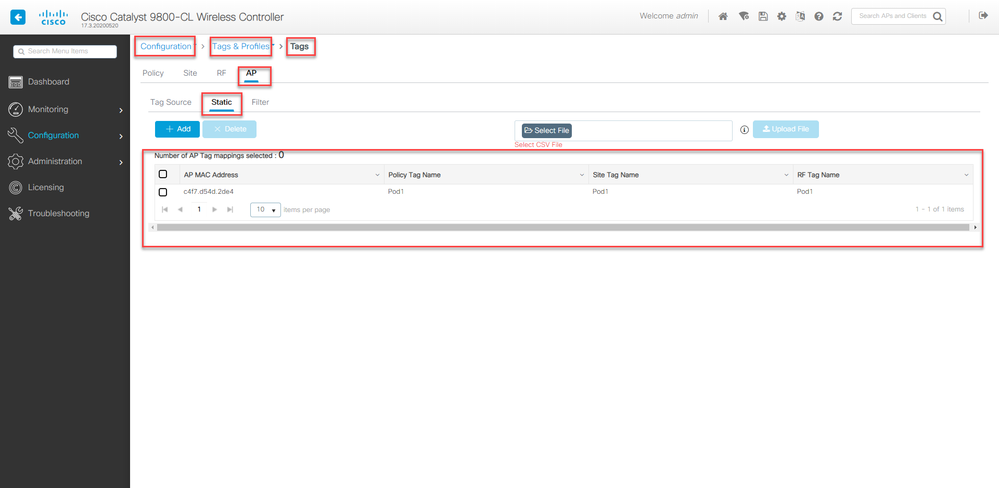
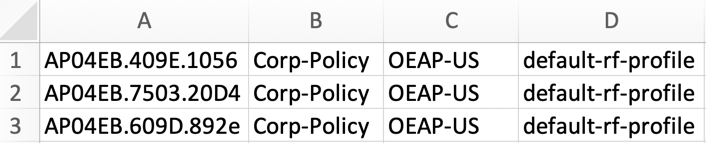
Step 8a: From WLC navigate to Configuration > Tags & Profiles > Tags >AP > Static click on +Add and add the AP MAC Manually along with the TAG names
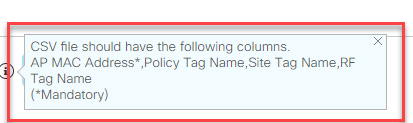
Option 2: Admin can also import the CSV file with AP MAC and Tags. Sample CSV shown below
Step 8b: From WLC navigate to Configuration > Tags & Profiles > Tags >AP > Static click on the Select File to upload the CSV file
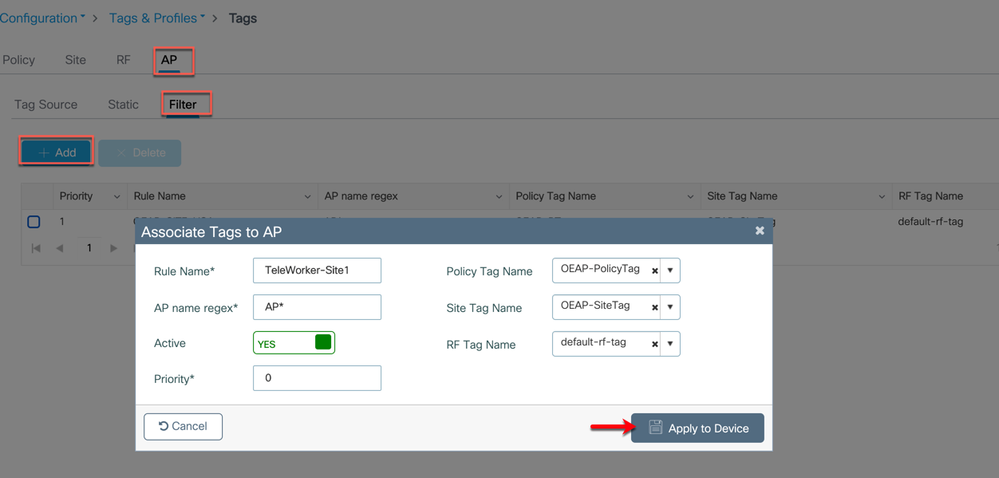
Option 3: Admin can also tag the APs through Filter Rule
Step 8c: From WLC navigate to Configuration > Tags & Profiles > Tags >AP > Filter click on +Add and enter the following then click Apply to Device
Rule Name: Admin configured name
AP name regex: The regular expression is to identify APs name (in the example AP* is used so any AP joining WLC with the name AP in it will inherit the respective tags)
Active: Yes/No
Priority: From 0-1023 with 0 being the highest
Policy Tag Name: Select the policy tag from the drop-down list
Site tag Name: Select the site tag from the drop-down list
RF tag Name: Select the site tag from the drop-down list
Cisco Network Plug and Play (PnP) for Teleworker Deployment
Cisco Network Plug and Play solution provides a simple, secure, unified, and integrated offering for enterprise network customers to ease new site rollouts for provisioning Cisco Access points. This solution allows use of Cloud Redirection service, which provide a unified approach to provision enterprise networks comprised of Cisco Access Points, Cisco routers, switches, with a near zero touch deployment experience.
You can use the Cisco Network Plug and Play portal to pre-provision the site and add Cisco access points to the site. This includes entering access point information to the device list and setting a controller profile (which contains WLC info like WLC public IP address)
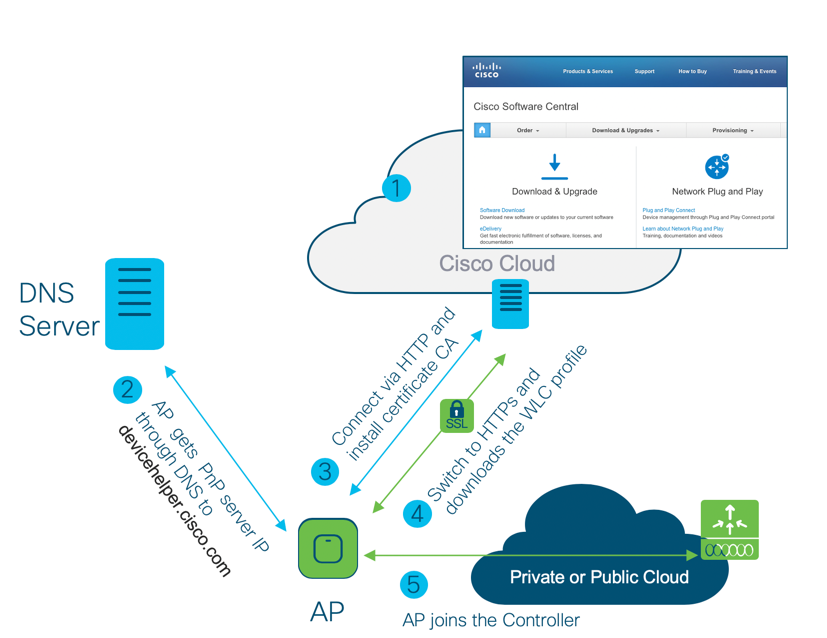
When a teleworker /employee is provided with the teleworker AP and he powers up the access point, it auto-discovers the Cloud PNP server by using the DNS /cloud redirection service through devicehelper.cisco.com.
After the auto-discovery process is complete, the AP gets the WLC IP information from the controller profile on the Cloud PNP and then try to join the WLC.
Figure 2. Cloud PnP Workflow
Prerequisites
-
Cisco Smart account registration to access Cisco Network Plug and Play
-
Access Points–Cisco 802.11ac Wave 2 (indoor) and 11ax access out-of-box or factory reset to defaults. (APs should not have the previous WLC joined information otherwise PnP agent would not start)
-
AP should have the recommended code running 17.3.1 or 8.10.MR3
-
Controller Configuration–WLC public IP address to be uploaded on Network PnP portal https://software.cisco.com/
-
AP should be configured with DNS server information through the local DHCP and be able to resolve and connect to devicehelper.cisco.com
Cloud Plug and Play Connect redirect to WLC
Cloud re-direction service uses Cisco Cloud PnP to re-direct Cisco access points to Cisco WLC. The minimal requirement is that the Access Points network have DHCP, DNS, and connectivity reachable to Cisco Cloud PnP.
Cloud Plug and Play Device Provisioning
This section describes the steps to redirect Cisco Access Points to Cisco WLC using Cloud Plug and Play Connect service.
To configure cloud Plug and Play connect redirect service, perform the following steps:
-
Create a Smart Account
-
Create Controller Profile
-
Adding Access Point to the devices list
-
Associate Access Point to Controller profile
Create a Smart Account
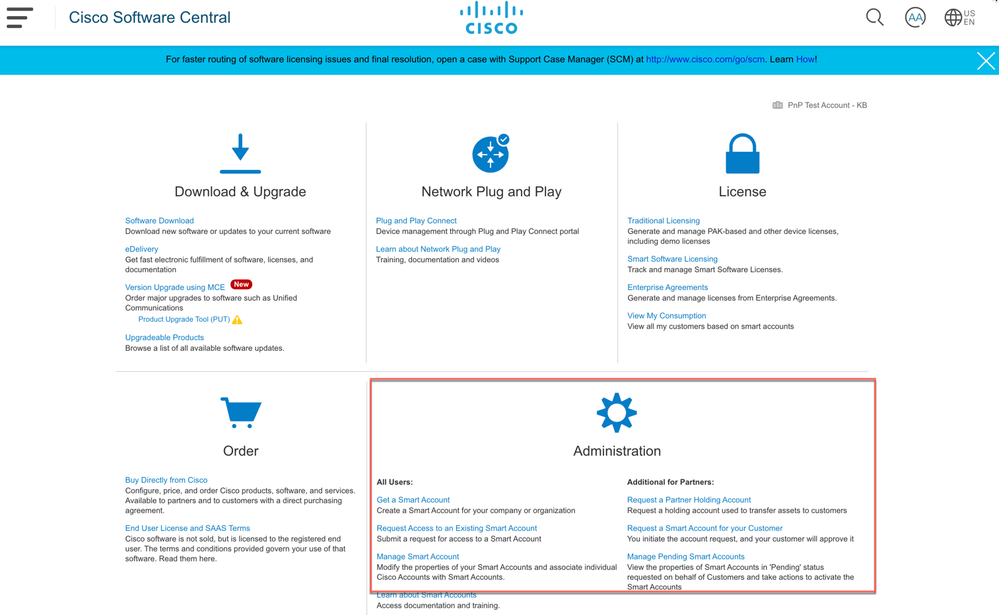
Step 1: Go to http://software.cisco.com
Step 2: Request a Smart Account or Log In (existing Smart Account holders)
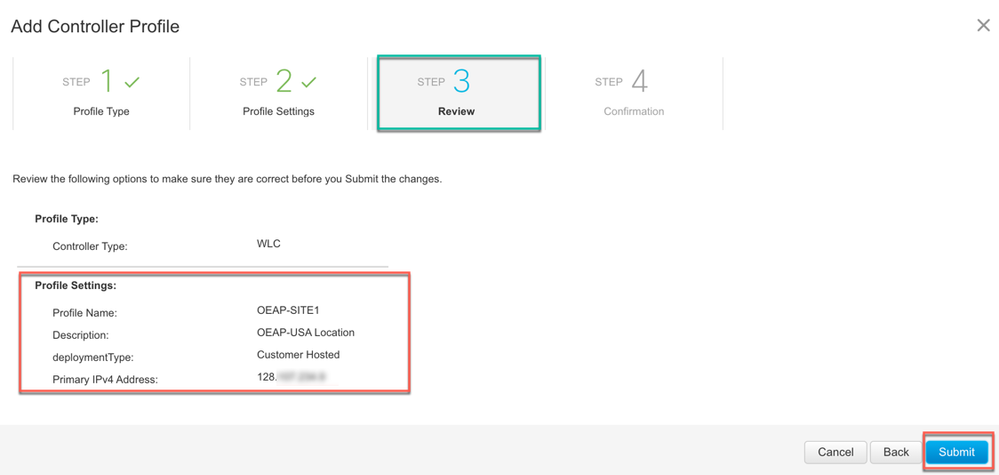
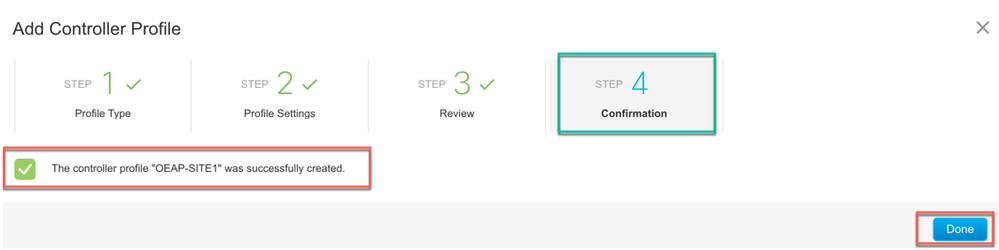
Create a Controller Profile
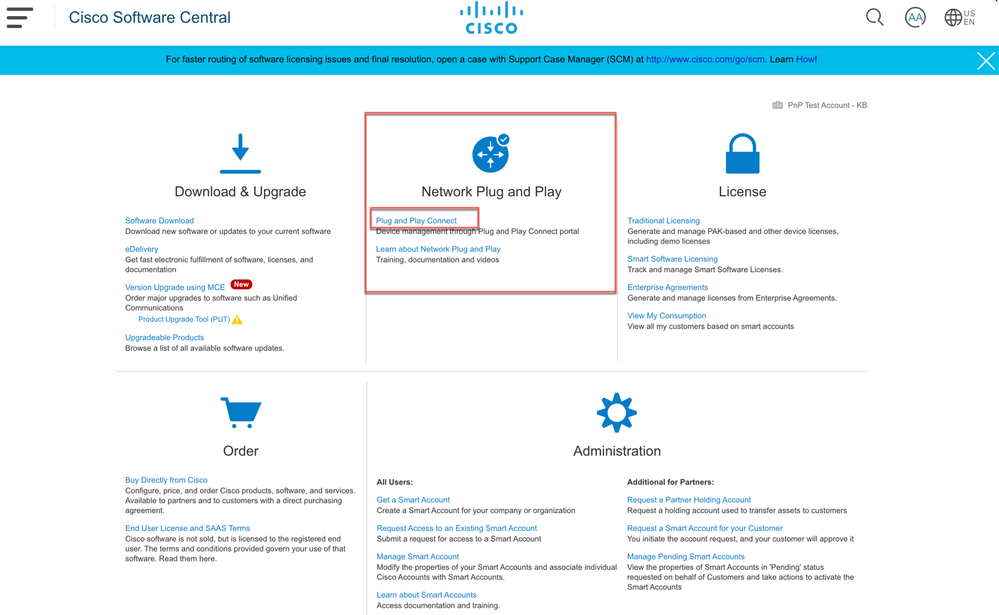
Step 1: Go to http://software.cisco.com and login via cisco.com account
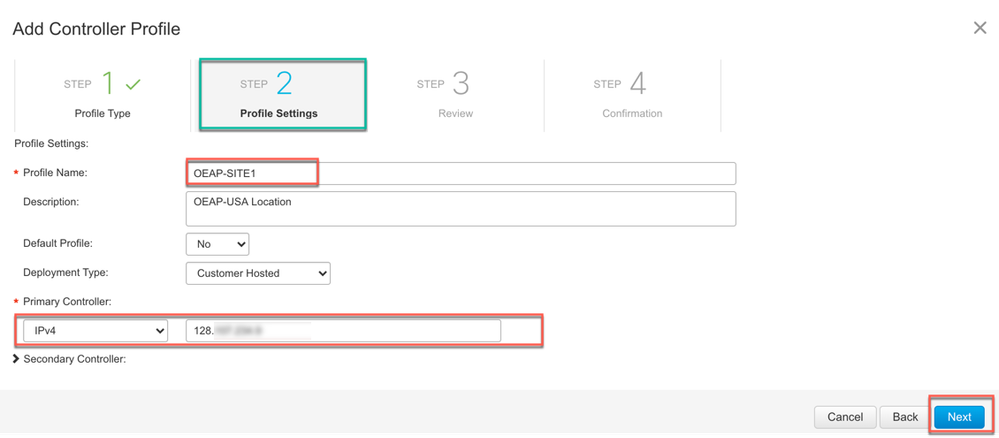
Step 2: Navigate to Network Plug and Play > Plug and Play Connect
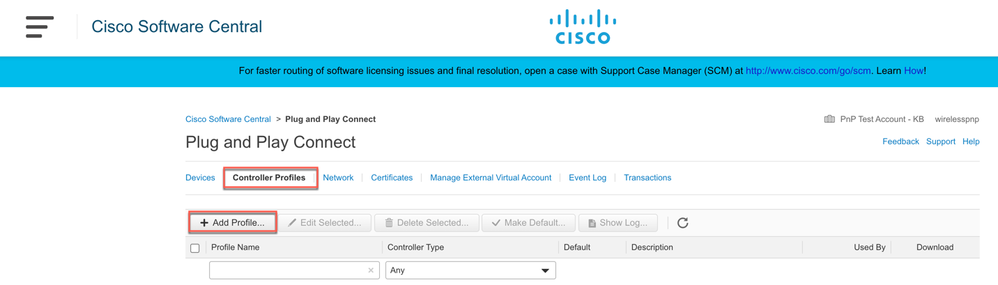
Step 3: Then click on Controller Profiles> + Add Profile to create a new controller profile
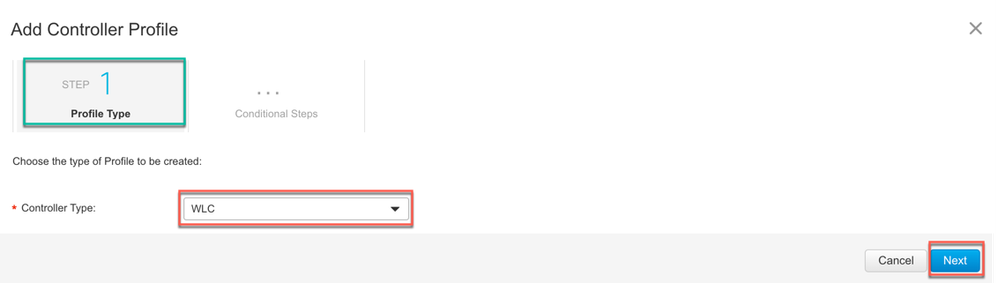
Step 4: Select Controller Type as WLC (IOS-XE or AireOS) from the drop-down list and click on Next.
Step 5: Enter the following and click Next.
Profile Name: Admin configured name
Description (optional): Admin configured description
Primary Controller: Select primary controller IPv4/IPv6 and enter the Public IP address of the primary WLC. Hostname/FQDN or URL is not supported.
Secondary Controller (Optional): Select secondary controller IPv4/IPv6 and enter the Public IP address of the secondary WLC
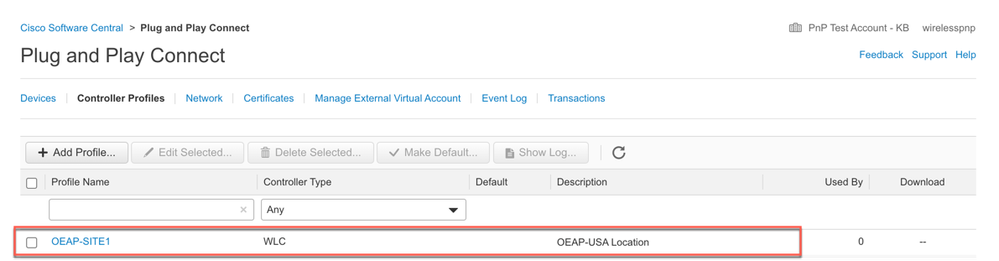
Step 6: Review the entries and click on Submit button to add the Controller Profile and finally the confirmation message will appear that the controller profile was successfully created then click Done.
The created profile will appear in the Controller Profile list.
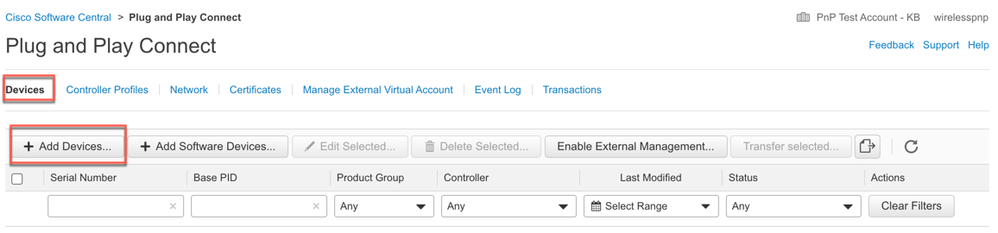
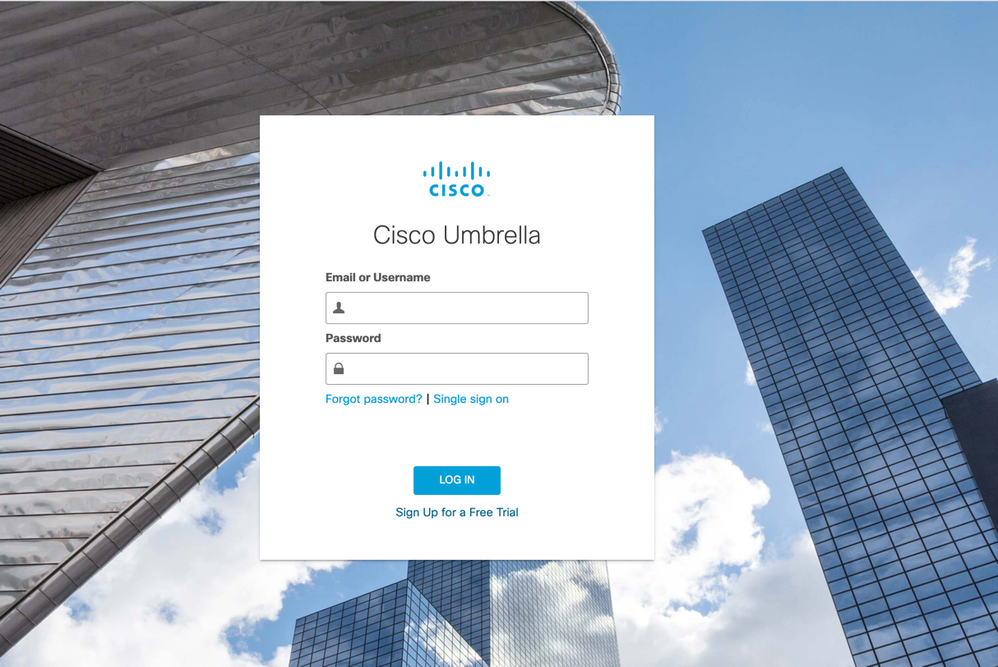
Adding Cisco Access Point to the Devices List
Step 1: Navigate to Plug and Play Connect then click on Devices tab.
Step 2: Click on +Add Devices button to add a new device
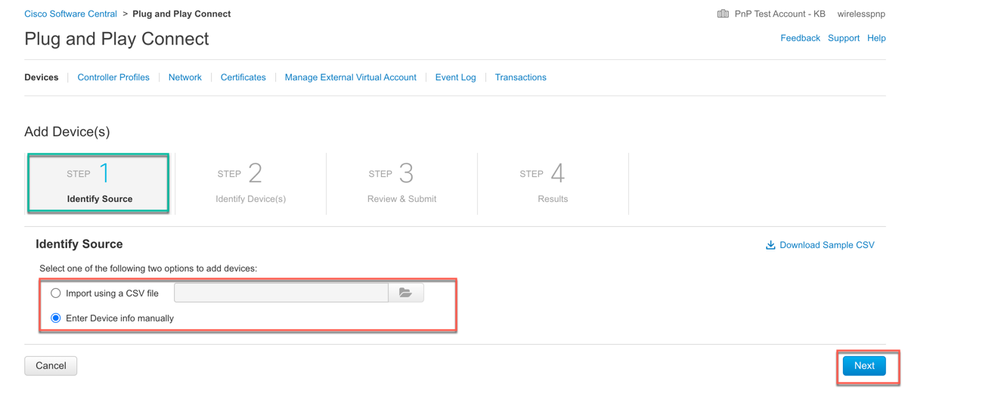
Step 3: Import a CSV file with the Device info or select Enter Device info manually option. Click Next. User can download a sample csv file to enter the devices info.
Note: In CCW there is a default option that will add the device in PNP Cloud automatically, unless the user disables it.
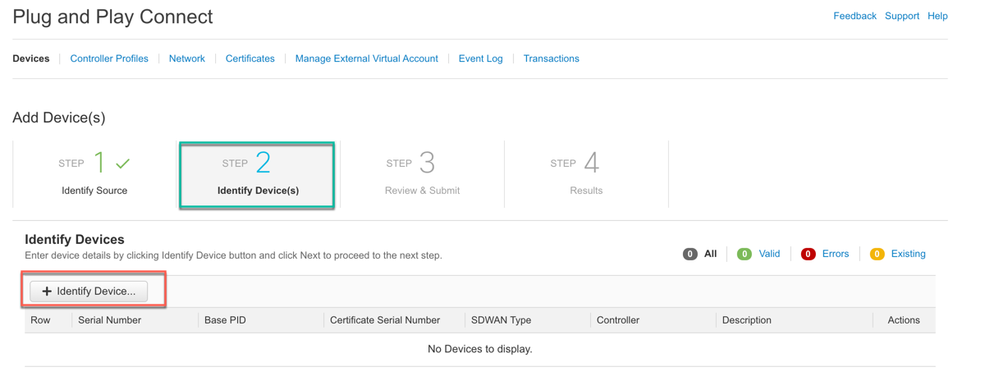
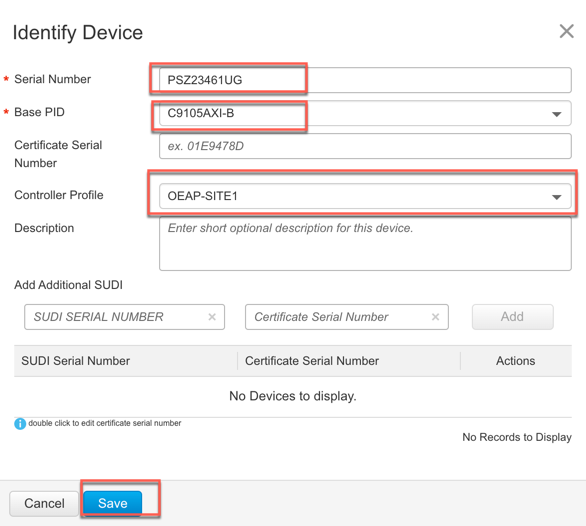
Step 4: Click on +Identify Device button. The Identify Device window will pop up.
Enter Serial Number, select Base PID from the drop-down list, and Controller Profile (created earlier) or from previously created profiles.
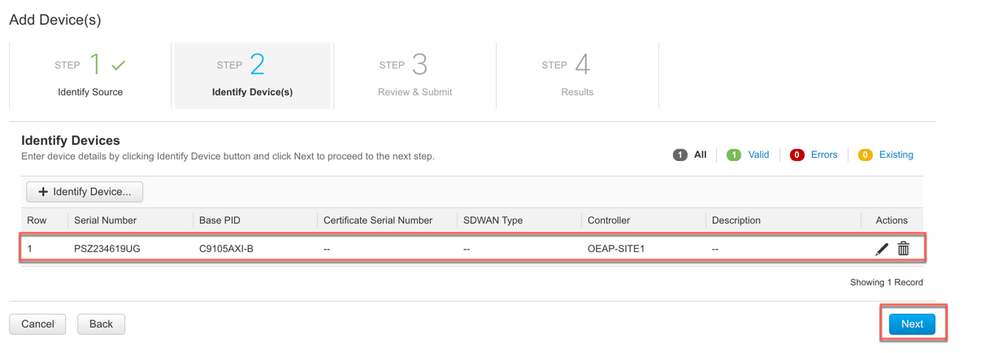
Click on the Save button followed by Next button.
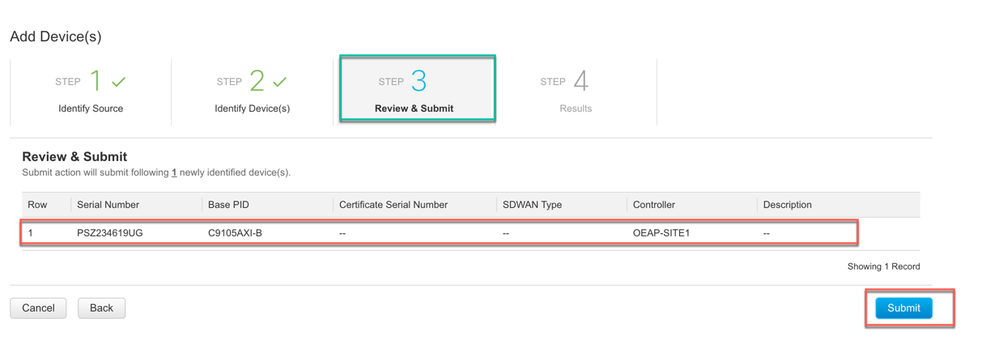
Step 5: Review the entries and click on Submit button to add the Device.
Step 6: Once the device is successfully added then click Done.
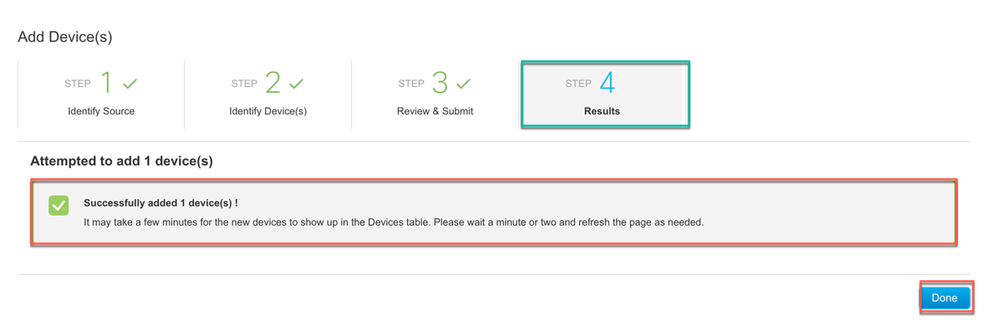
Step 7: Verify that the Device has been added and the status is “Pending (Redirection)” in orange. When the device redirection is successful the status will show “Redirect Successful”
Once the the AP is online it will get the WLC information from Cisco PnP Connect and will then join the respective WLC.
Umbrella for Teleworker WLAN
Cisco Umbrella is a Cloud delivered network security service, which gives insights to protect devices from malware and breach protection in real time. It uses evolving big data and data mining methods to proactively predict attacks also do category-based filtering. This is not specific to Teleworker but can be you utilized to have an added protection of the corporate clients.
Prerequisites:
-
Cisco Umbrella provisioning involves creating a user account on Cisco Umbrella cloud. Subscription is per account and Cisco Umbrella offers 14-day obligation free trial license.
-
Permanent License is covered under DNA Advantage license Subscription.
-
WLC direct reachability to the Internet or through the proxy server.
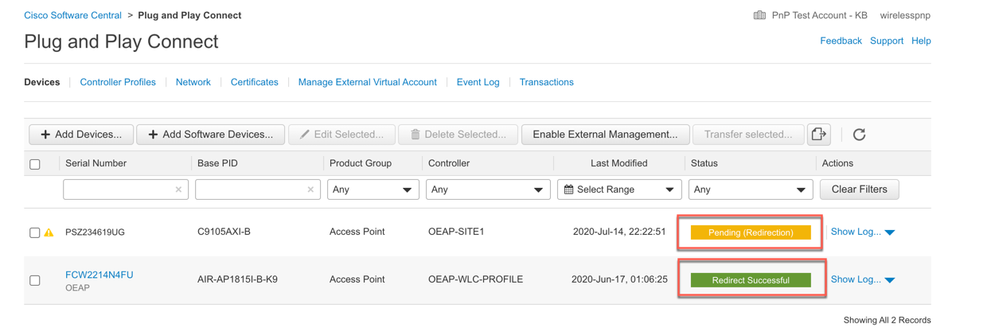
Step 1: Login to your account at https://login.umbrella.com/
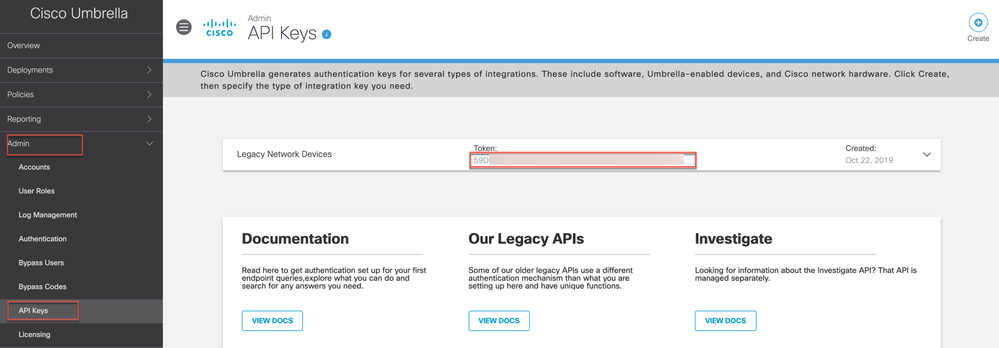
Step 2: From Cisco Umbrella main dashboard landing page, go to Admin>API on copy the API TOKEN as shown below.
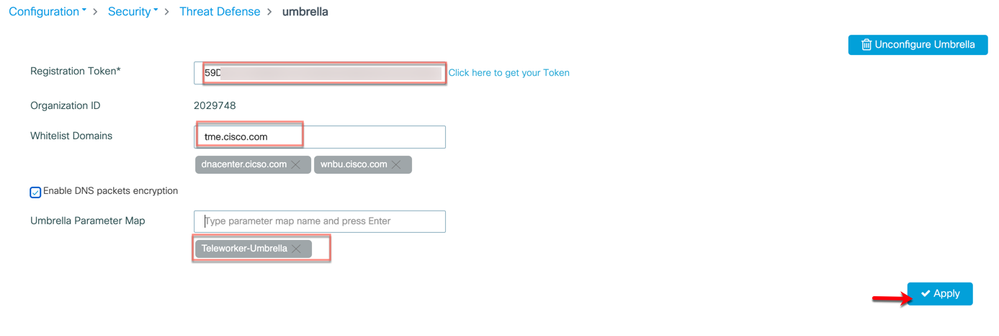
Step 3: From WLC navigate to Configuration>Security> Threat Defense> Umbrella. Enter Umbrella API Token to register
Admin can also define the corporate internal sites or list the domains for DNS splitting.
In Whitelist Domains add the domain names or a regex name which needs to be internally split and hit Enter key.
By default, Umbrella Parameter Map is set to ‘global’ but admin can define custom umbrella parameter map by assigning a name and hit Enter key. Then click Apply
Note: Refresh the page to verify the Organization ID is not stating ‘None’ if it is this means that the device did not register to Umbrella cloud.
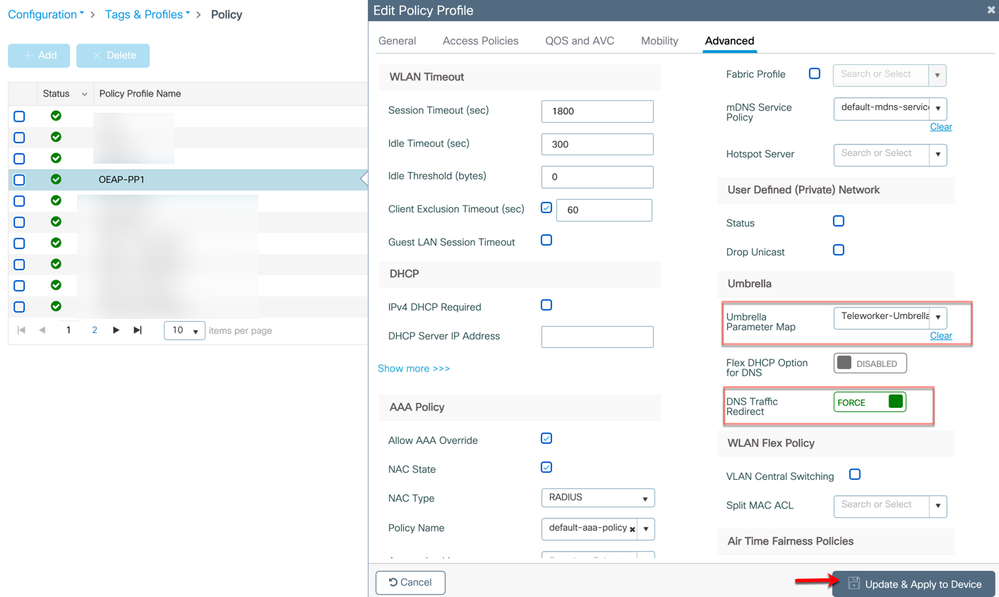
Step 4: Now go to Configuration>Tags & Profiles>Policy and click on policy profile name on which admin wants to configure umbrella parameter map and then go to Advanced tab
Select the Umbrella Parameter Map from the drop-down list.
DNS traffic redirect state to Force (even if user try to change the device DNS manually on the client it would always use Umbrella DNS)
Then click “Update & Apply to Device” button
Note: Admin can also configure QoS & AVC policies for a particular Policy Profile.
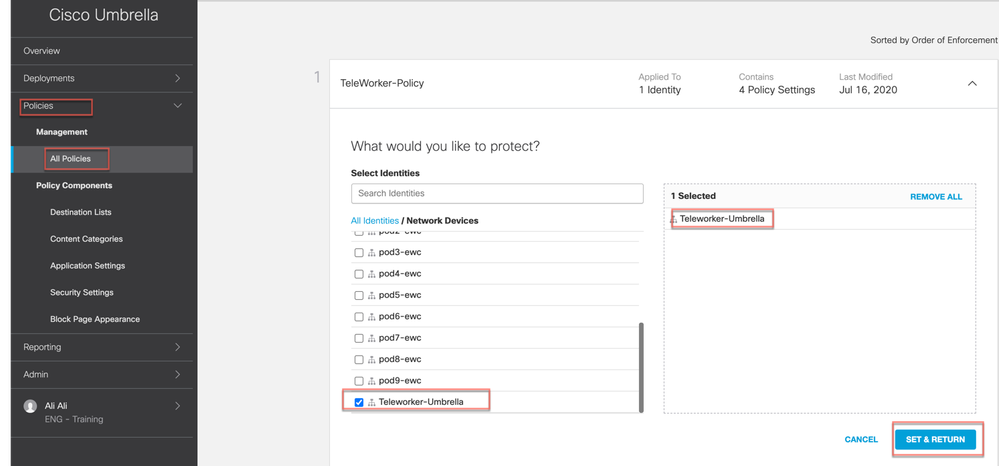
On Cisco Umbrella admin can attach this Parameter Map profile to the Umbrella Cloud policies to do category-based filtering on sites and domains to allow, deny or just monitor the devices accessing the internet
For Umbrella Policies creation and configuration please visit the umbrella docs
https://docs.umbrella.com/deployment-umbrella/docs).
https://docs.umbrella.com/deployment-umbrella/docs/create-and-apply-policies
Configuring the Remote LAN (RLAN)
A remote LAN (RLAN) is similar to a WLAN except it is mapped to one of the Ethernet ports on the back of the Cisco Access Point.
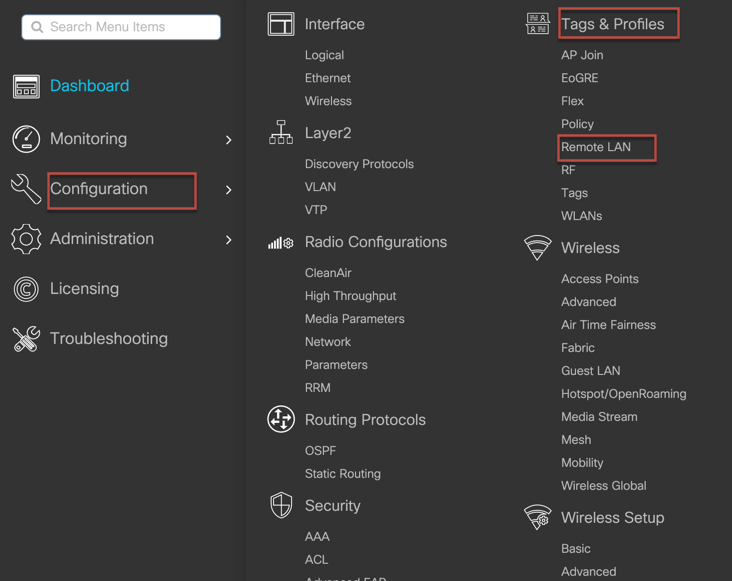
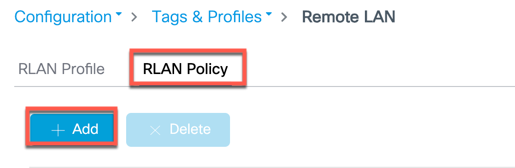
Step 1: Login to your C9800 WLC and go to Configuration>Tags & Profiles> Remote LAN
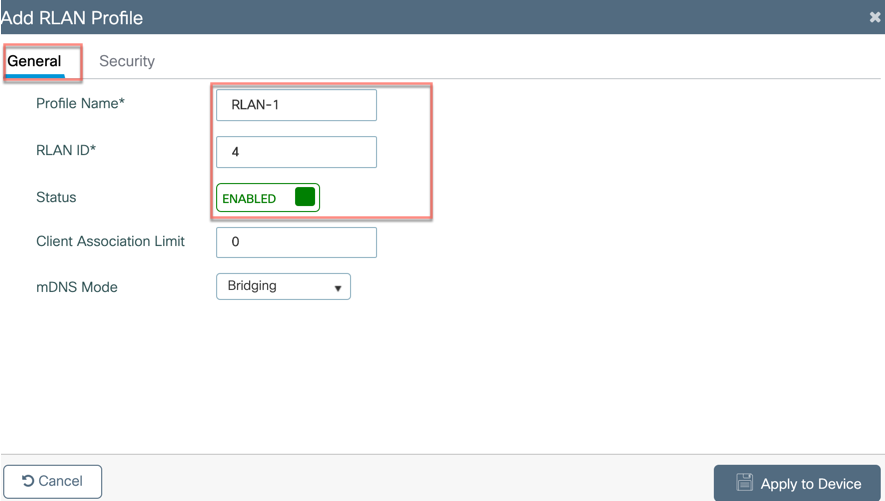
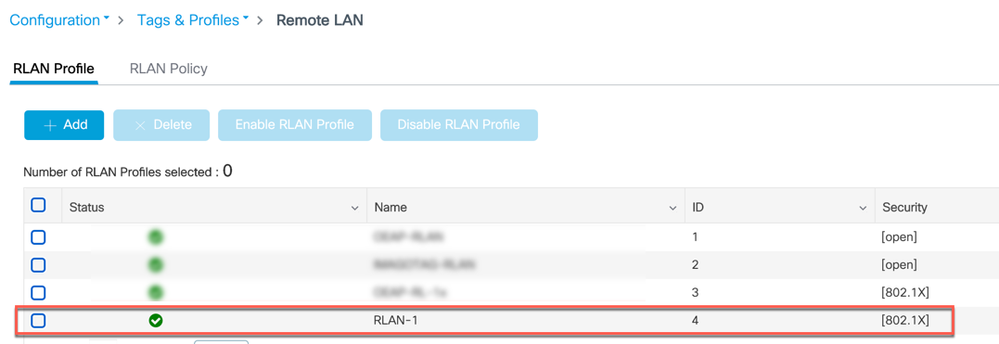
Step 2: From RLAN Profile tab click on +Add and then from General tab configure the RLAN Profile Name, RLAN ID and enable the Status
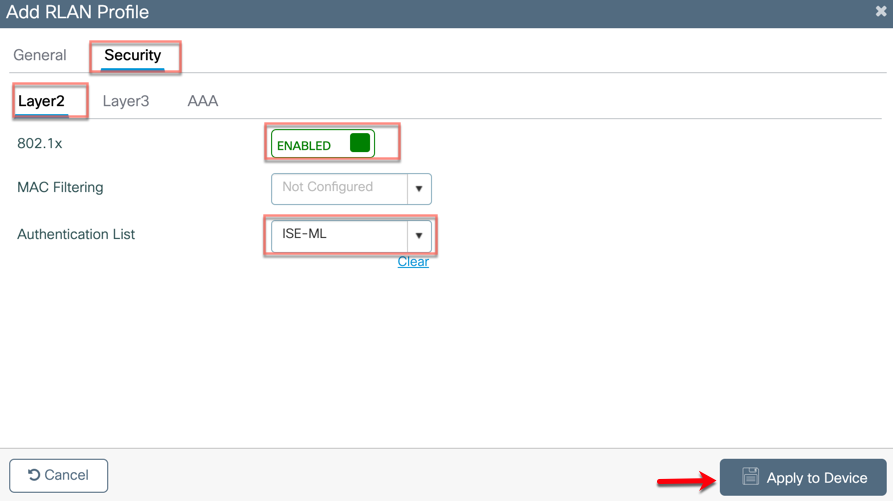
Step 3: Go to the Security>layer2 user can Enable 802.1X or if kept disabled its in open state with no authentication. User can also configure RLAN for web-auth from Layer3 tab. In this example we are using 802.1X.
From the Authentication List select the Radius server and click “Apply to Device”.
Note: The Radius server needs to be configured first if not already configured.
For Radius/AAA configuration on C9800 please refer to the following document
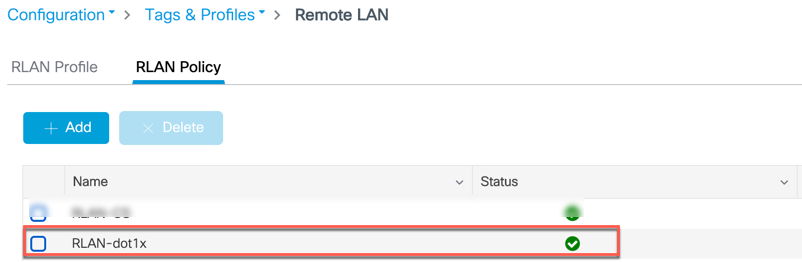
Configure Remote LAN Policy
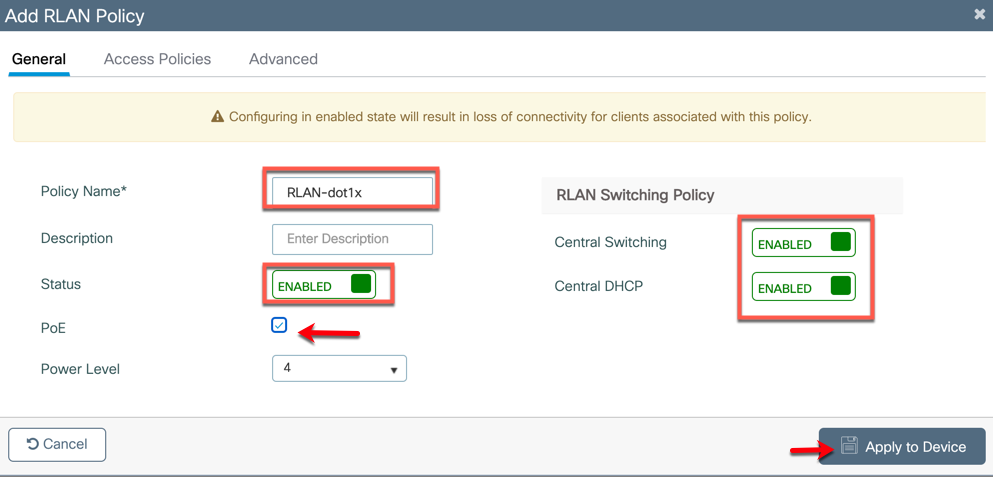
Step 1: Select RLAN Policy tab and click +Add to configure RLAN policy.
Step 2: From General tab configure the following
Policy Name: User define name
Status: User can enable to disable the policy. Enable the Status
PoE: Enables or disables PoE -If user want to enable PoE on RLAN port1 (PSE-LAN1) then check PoE box.
Enable Central Switching and DHCP and then click “Apply to Device”.
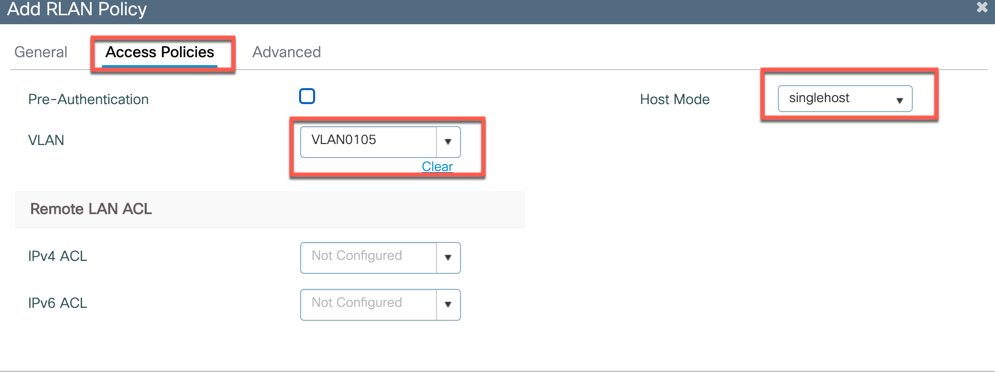
Step 3: From Access Policies tab configure the following:
Select the VLAN: This VLAN will be used as egress point of Teleworker user’s Corporate Network access. i.e. wired clients connecting to this RLAN will be assigned the VLAN centrally from the 9800.
Select the Host mode: admin can choose the mode as singlehost, multihost or multidomain
Single-Host Mode—Is the default host mode. In this mode, the switch port allows only a single host to be authenticated and passes traffic one by one.
Multi-Host Mode—The first device to authenticate opens up to the switch port, so that all other devices can use the port. You need not authenticate other devices independently, if the authenticated device becomes authorized the switch port is closed.
Multi-Domain Mode—The authenticator allows one host from the data domain and another from the voice domain. This is a typical configuration on switch ports with IP phones connected.
Note: Multi-Domain Mode is not supported in the 17.3 release
Note: For a RLAN profile with open-auth configuration, you must map the RLAN-policy with single host mode. Mapping RLAN-policy with multi-host or multi-domain mode is not supported. If the RLAN is used for IP phone the voice VLAN can be tied to the RLAN policy.
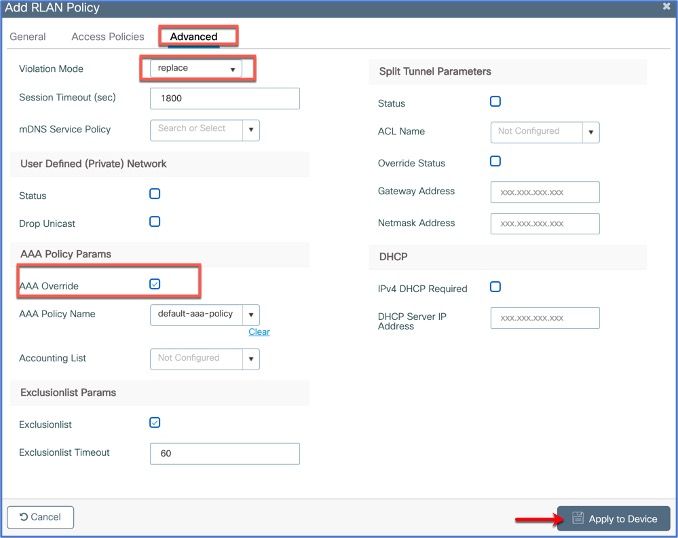
Step 4: From Advanced tab configure the following
Violation Mode: It is a port security method and replace is a default behavior.
Replace—Removes the current session and initiates authentication for the new host.
Protect—Drops packets with unexpected MAC addresses without generating a system message.
Shutdown—Disables the port
Check AAA Override if using Radius to send and attributes to override.
Click ‘Apply to Device’
Adding WLANs/RLANs to a Policy Tag
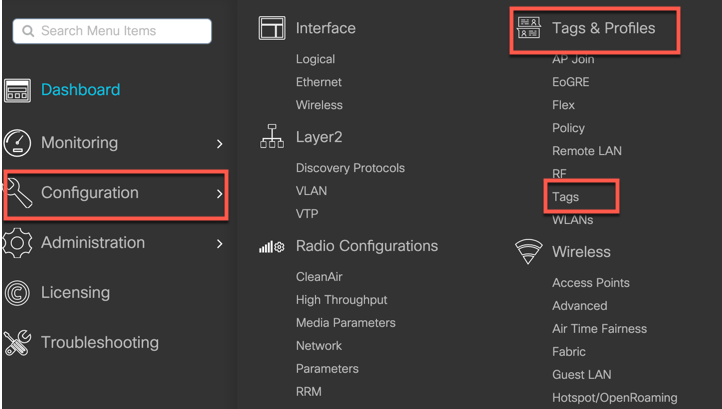
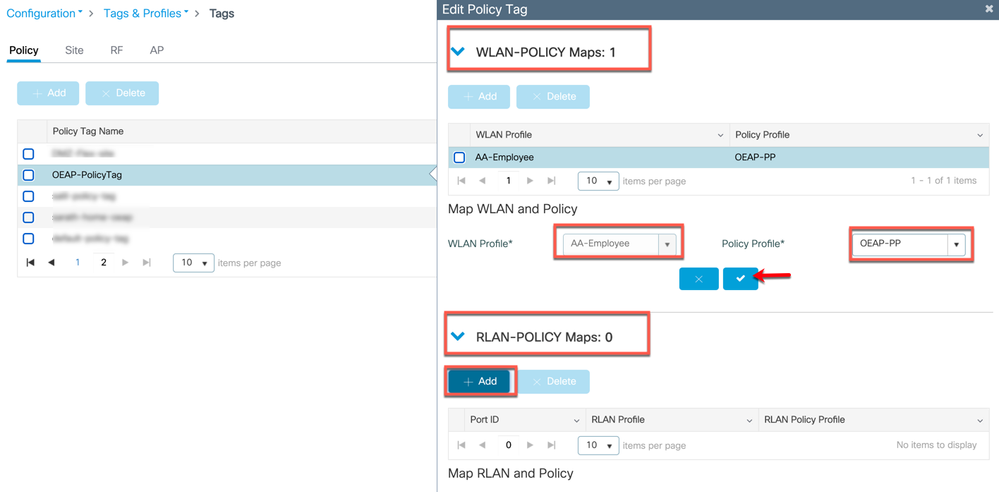
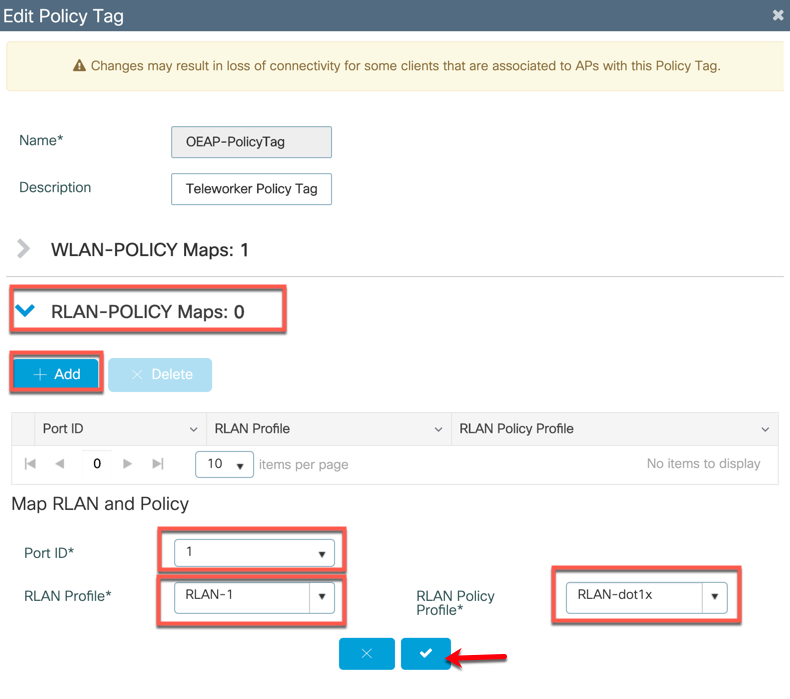
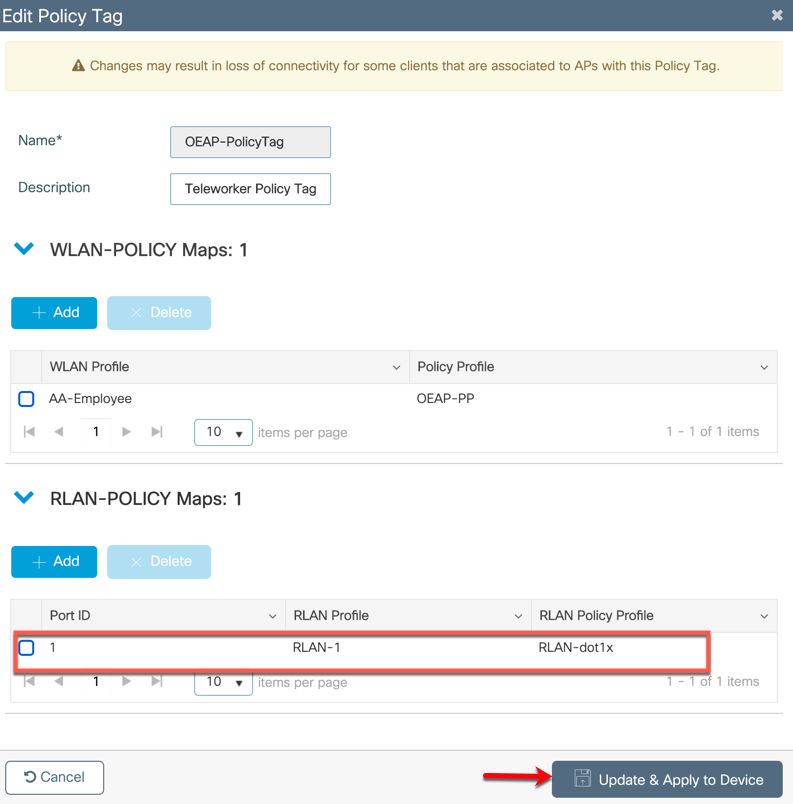
Step 1: Go to Configuration> Tags & Profiles> Tags
Policy Tag helps in mapping the WLAN/RLAN profiles to the particular policy profile. Admin can create a new policy tag or use the already configured ones to add WLANs and RLANs.
Step 2: From the option WLAN-POLICY Maps user can use +Add to configure a new WLAN or apply pre-configured WLANs to policy profiles mapping.
Similarly, from RLAN-POLICY Maps click +Add and select the Port ID on which user want to apply the RLAN profile and also select the RLAN policy.
Note: Ports 1 and 2 are used as RLAN ports, Port 3 is a dedicated local port on C9105W and 1815T/W. User can connect their laptop to Port 3 to access the local Teleworker AP configurations.
Then click on the "checkmark" to add the RLAN-Policy MAP
Note: RLAN is supported in APs that have more than one Ethernet port. For e.g. C9105W, OEAP1810/1810W/1815T/1815W/1850/2800/3800) AP4800 AUX port does not support RLAN.
Step 3: Apply it by clicking “Apply to Device”
The configured RLAN Policy will the configured RLAN Policy status.
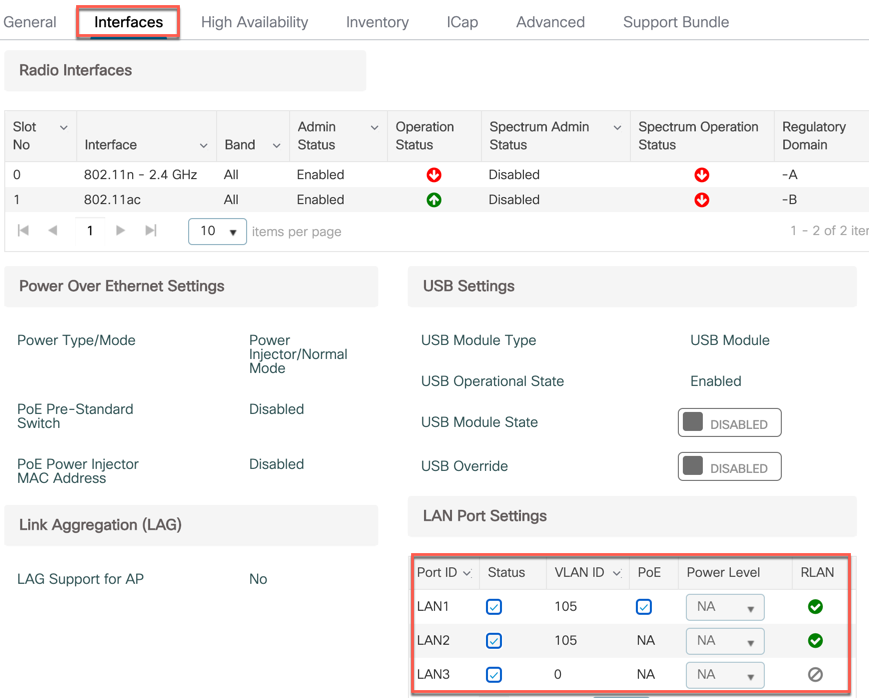
Step4: To enable the port on APs admin can go to the Configuration>Wireless>Access Points and select the Teleworker AP with the RLAN port then go to Interfaces>LAN Port Settings then select or check the Status of the LAN Ports
Split Tunneling for Teleworker AP
Split Tunneling introduces a mechanism by which the traffic sent by the client will be classified, based on packet content, using ACLs. Matching packets are switched locally from Teleworker AP and the rest of the packets are centrally switched over CAPWAP.
Use Case 1: Local device access while connected to corporate network
The Split Tunneling functionality is an added advantage for Teleworker setup where clients on a Corporate SSID can talk to devices on a local network (printers, wired machine on a Remote LAN Port, or wireless devices on a Personal SSID) directly without consuming WAN bandwidth by sending packets over CAPWAP.
Use Case 2: CAPWAP data tunnel Optimization
Applications like webex-meetings, SharePoint, Office365, box, dropbox etc. all live in the cloud as a SAAS applications. Teleworkers use these daily as part of their work, to access these the traffic do not need to go all the way to the Corporate HQ network in the tunnel which can cause extra latency, to avoid this admin can use split-tunneling feature on WLC.
The way it can be achieved is by applying the split-tunnel to send only the corporate IP addresses centrally and switch all other traffic locally. The split-ACL supported is a five tuple IP ACL (which can take IP, protocols and ports as part of ACL rules)
While crafting this ACL admin can make sure all the DNS traffic is centrally switched so that it gets the benefit of Umbrella security even for the traffic that is getting locally switched due to split ACL.
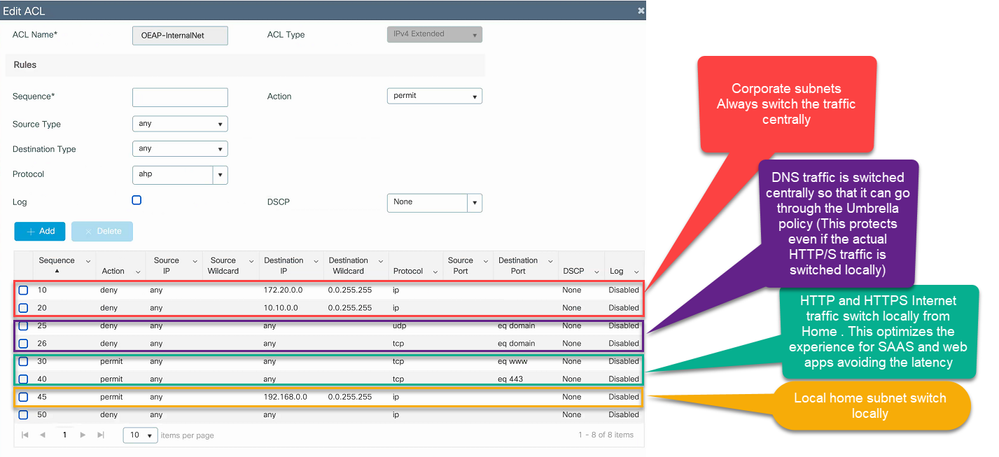
Creating Split-ACL
Navigate to Configuration > Security > ACL
Click Add to create a new ACL of type IPv4 extended.
Note: when creating the ACL, a deny statement means “not splitting the traffic” so it’s traffic that is sent in the CAPWAP tunnel. A permit statement means permit the “splitting of that traffic” and hence the traffic exits locally at the AP. Therefore, admin can create a ‘Deny rule’ for centrally switched traffic and create a ‘Permit rule’ for locally switched traffic.
Create a deny rule for the centrally switched traffic- Corporate networks, DNS, TCP/UDP
Create a permit rule for the locally switched traffic -home network) and HTTP/HTTPs
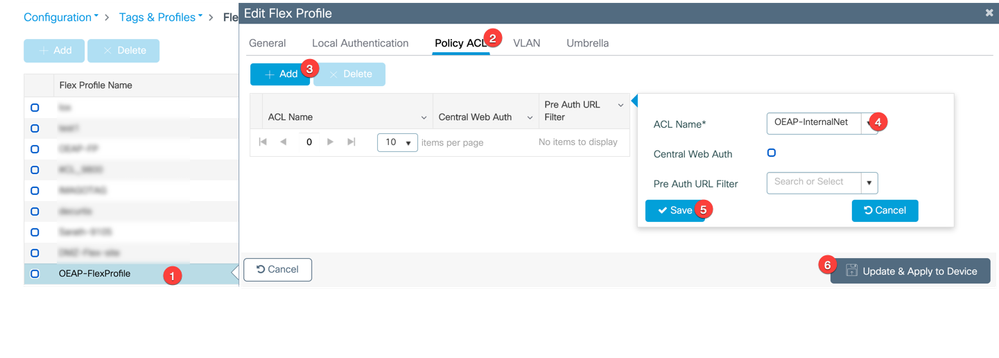
Assigning the Split ACL on Flex Profile
Step 1: Navigate to Configuration > Tags & Profile > Flex
Step 2: Click on the flex profile on which user want to apply the ACL to edit Flex Profile configuration
Navigate to Policy ACL >+Add the select the ACL Name from the drop-down list
click Save and Update and Apply
This is to make the ACLs to be downloaded on to the AP’s.
Assign the ACL as the Split mac ACL on policy profile
To apply the Split ACL we need to map it to the Policy-Profile
Step 1: Navigate to Configuration > Tags & Profile > Policy
Step 2: Click on the Policy Profile Name on which admin/user wants to configure Split ACL.
In the Edit Policy Profile window navigate to Advanced tab.
Under WLAN Flex Policy >Split MAC ACL select the Split ACL (which admin created) from the drop-down list.
Then click Update and Apply to Device
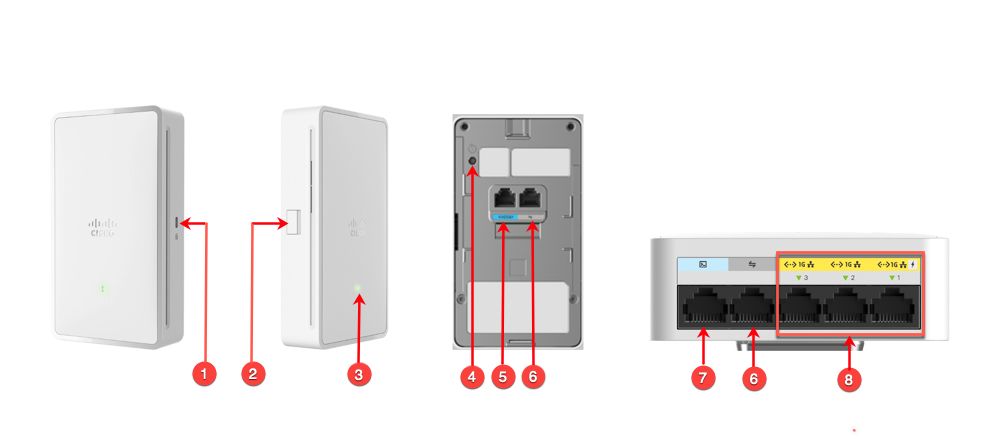
Cisco Catalyst C9105W as Teleworker Access Point
The Cisco Catalyst C9105W Series Access Point offer a compact, wall plate-mountable access point, ideal for hospitality, cruise ships, residential halls or other multi-dwelling-unit deployments. The C9105W Series combines 802.11ax wireless and MultiGigabit Ethernet wired connectivity into a sleek device, built to take advantage of existing cabling infrastructure. This combination provides best in class performance while reducing total cost of ownership.
Cisco C9105W Access Point can be also used as dedicated Teleworker AP and supports a number of features:
Interfaces
1x 100/1000/2500 Multigigabit Ethernet (RJ-45)
3 x 100/1000 Gig Ethernet (RJ-45) – Port 1-2 (RLAN ports) & Port 3 (dedicated Local LAN port)
1 x Pass-through port
Management console port (RJ-45)
USB 2.0
DTLS
Control–DTLS is enabled for Control
Data–DTLS is enabled for client traffic tunneled back to the corporate Wireless LAN Controller
Authentication and Security
Advanced Encryption Standard (AES) for Wi-Fi Protected Access (WPA2/WPA3)
802.1X, RADIUS authentication, authorization and accounting (AAA) on WLAN and RLAN
802.11i
MAC filtering
Rogue and WIPs
Personal SSID support
Personal SSID support for local home networking
LAN 3 is a dedicated local port for local AP access
WLAN and RLAN
A total of 8 WLANs and 2 RLANs are supported on Cisco Teleworker APs. One can have more than 8 WLANs associated on the Site-Tag(C9800) / AP group (AireOS) but only the first 8 WLANs would be usable.
| Interfaces in Figure |
Interfaces as shown on C9105W |
Description |
|---|---|---|
| 1 | Security | Kensington Security Slot |
| 2 | USB | USB 2.0 |
| 3 | LED | Multi-color LED Status indicator. Colors supported are Red, Green, Amber |
| 4 | Mode | When pressed for more than 20s, it will reset the AP to factory defaults |
| 5 | mGig PoE Port  |
2.5 MultiGig Port to power the AP and for Up-link connectivity to the internet. |
| 6 | Pass-Through Port  |
Pass through port on the AP |
| 7 | Console Port  |
For Console access of the AP RJ-45 |
| 8 |
PSE-LAN1, LAN2, LAN3
|
LAN Ethernet Ports, PSE-LAN1 and LAN2 can be tunneled back to WLC. LAN 3 is a dedicated LAN port for accessing local UI of C9105W |
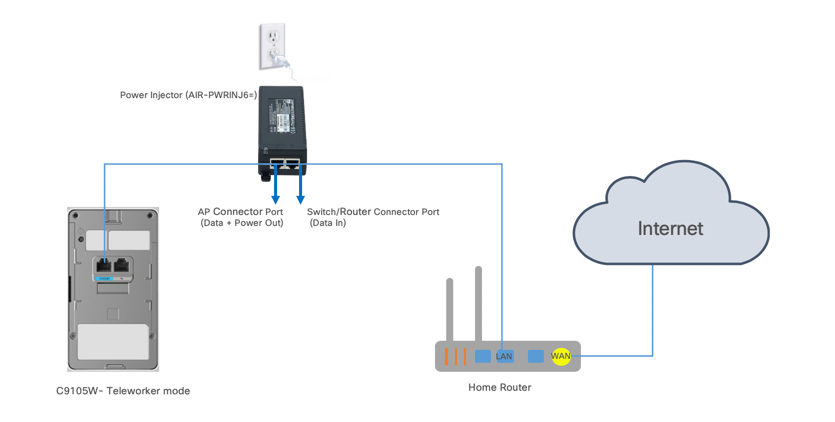
Connecting Cisco Teleworker Access point
The Cisco (Teleworker) APs requires minimal configuration by the end user. For environments where zero-touch end user deployments are required, the corporate IT department or network-integration partner should pre–configure the Cisco Teleworker AP with the address of the corporate Wireless LAN controller, as described in previous sections of this document.
Step 1: Connect the PoE port marked on the back of the Cisco Teleworker Access Point to your home router/gateway PoE port or have a power injector to power the AP. The Cisco C9105W Access Point gets an IP address from the home router/ gateway.
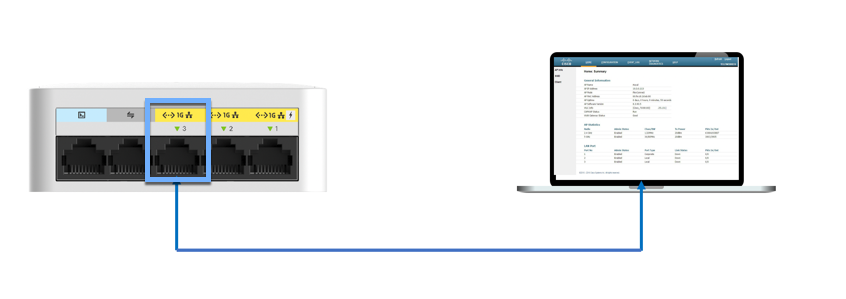
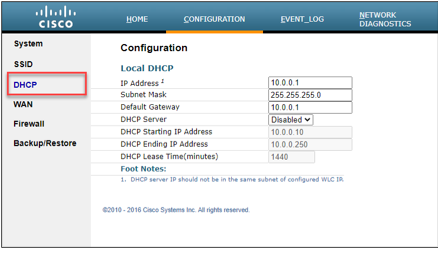
Step 2: After the Cisco C9105W (Teleworker)Access Point has booted up, connect a computer to the port labeled as 3. The computer gets an IP address from the default DHCP address pool of 10.0.0.0/24 ( Teleworker AP has NAT enabled for client connecting to the local LAN port 3 or on Personal SSID )
Step 3: Open a browser and navigate to the Access Point by using its default IP address: http://10.0.0.1/
Note: For the other APs models which do not have additional LAN ports or Port3. User need to get the Teleworker AP IP by going to the home router’s ‘Client List’
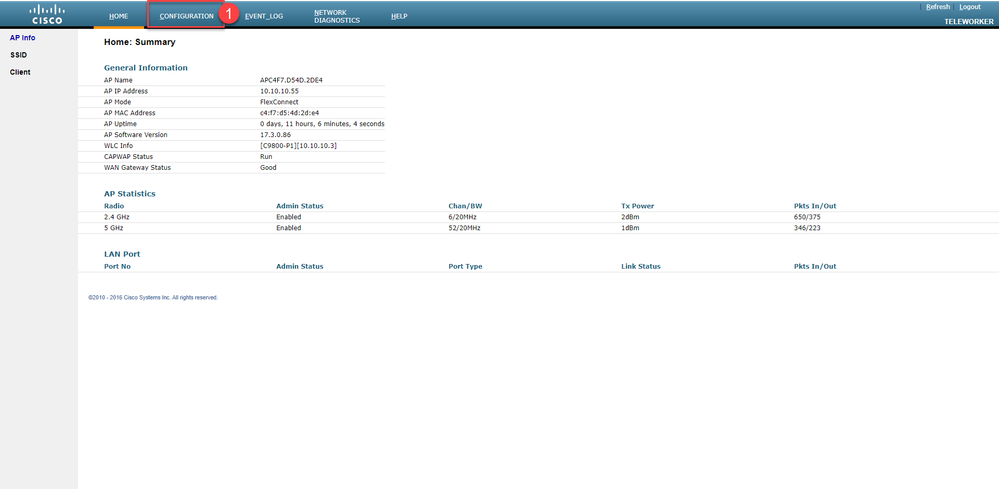
Step 4: Log in to the Administration page by using the default credentials admin/admin. The default credentials can be changed later configuration tab. The summary page appears. From top menu go to CONFIGURATION
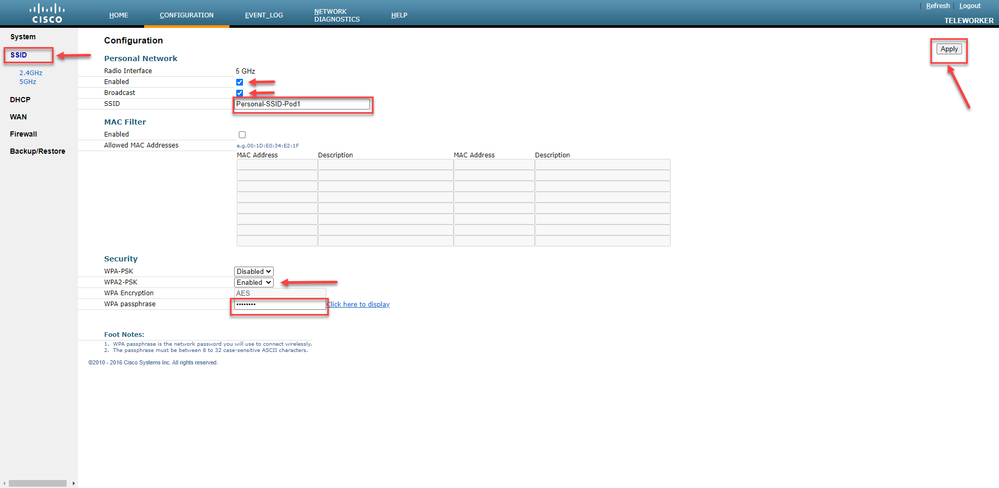
Step 5: click on the SSID and select the 2.4 GHz or 5 GHZ Radios. Enable the radio and configure the personal SSID and Passphrase and click Apply
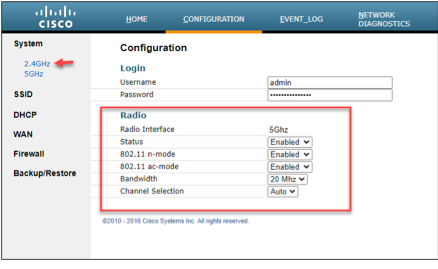
Radio Settings: User can also change the radio settings if required from CONFIGURATION>System> <2.4GHz/5GHz>
Local DHCP Server: User can also configure or change DHCP server settings if required from CONFIGURATION>DHCP
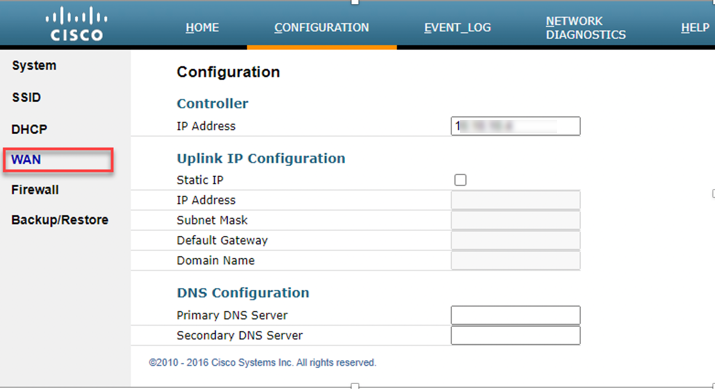
WLC IP configuration: From CONFIGURATION>WAN
User can verify Controller IP Address or if required can enter the Public IP address of the primary WLC, and then click Apply.
Clearing Personal SSID
The admin can clear the personal SSID config on the Teleworker access point if required.
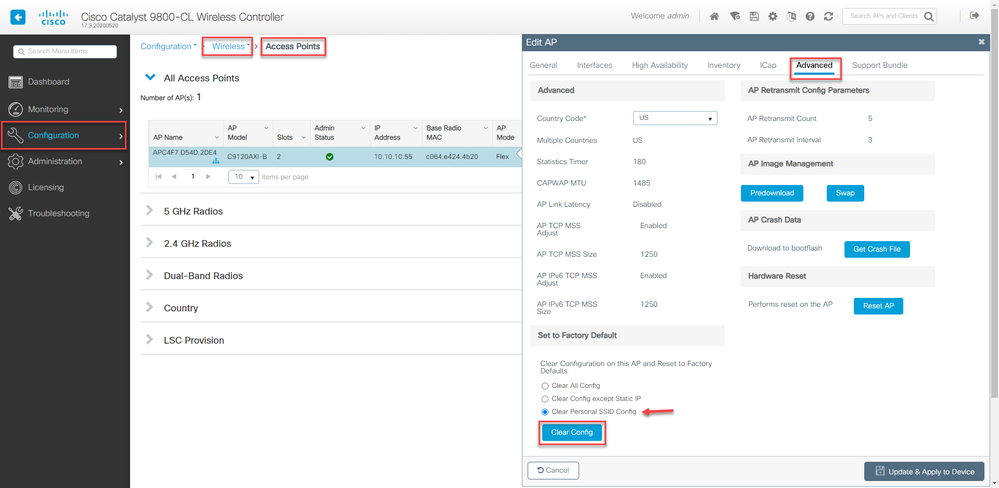
Step 1: Navigate to Configuration>Wireless>Access Points
Step 2: Click on the Access point on which admin wants to clear personal SSID the and Navigate to Advanced tab
Step 3: Select the Clear Personal SSID Config and press Clear Config button
This will clear the personal SSID config on the Teleworker access point
Limitations and Restrictions
-
Teleworker solution is not supported on Cisco Mobility Express or Embedded Wireless Controllers.
-
8 WLANs and 2 RLANs are supported on Teleworker APs.
-
A switch connected to any RLAN/LAN port on AP it supports 4 clients connected to it.
-
Multicast and mDNS is not supported in split tunnel scenario.
Teleworker Assurance from Cisco DNA Center
Cisco DNA Center is the foundational controller and analytics platform at the heart of Cisco’s intent-based networking solution. The software platform offers a centralized, intuitive management system that makes it fast and easy to design, provision, and apply policies across your network environment. The Cisco DNA Center UI provides intuitive, end-to-end network visibility and uses network insights to optimize network performance and deliver the best user and application experience.
In this section of the guide we are just going to walk through the DNA Center Assurance (2.1.1) with respect to wireless components specifically wireless clients and access points health and Cisco Intelligent Capture (icap) for teleworker deployment use-case. Please refer to DNA Center installation and deployment guide for device setup and details.
Cisco DNA Assurance User Guide, Release 2.1.1
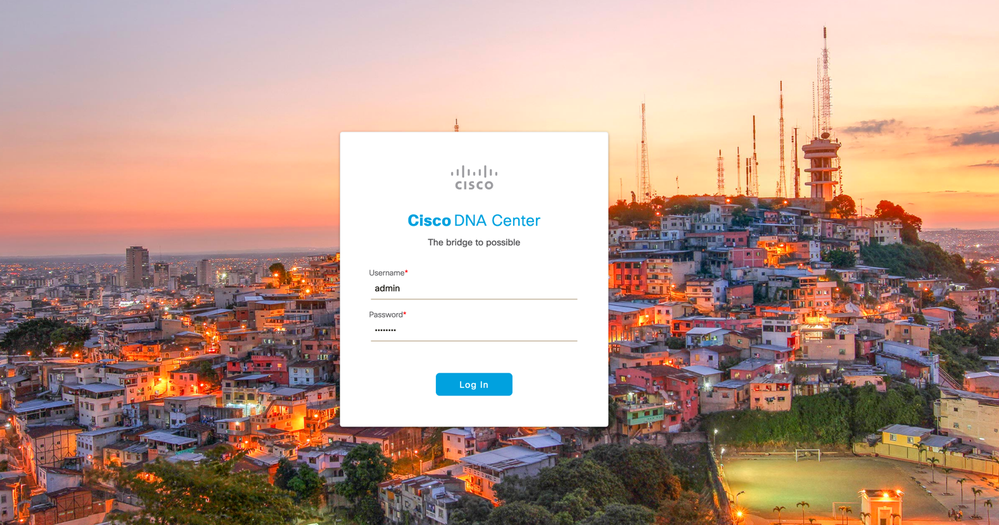
In this teleworker document we assume that user has already configured Cisco DNA Center for Assurance
Note: Teleworker Personal WLAN will not be monitored by WLC or Cisco DNA Center Assurance for privacy protection.
Login to the DNA Center with configured credentials
Cisco DNA Center (2.1.1) GUI, introduces a hamburger menu.
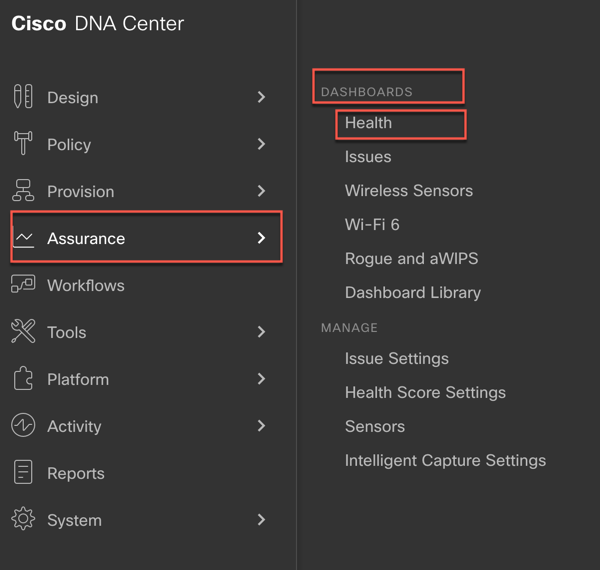
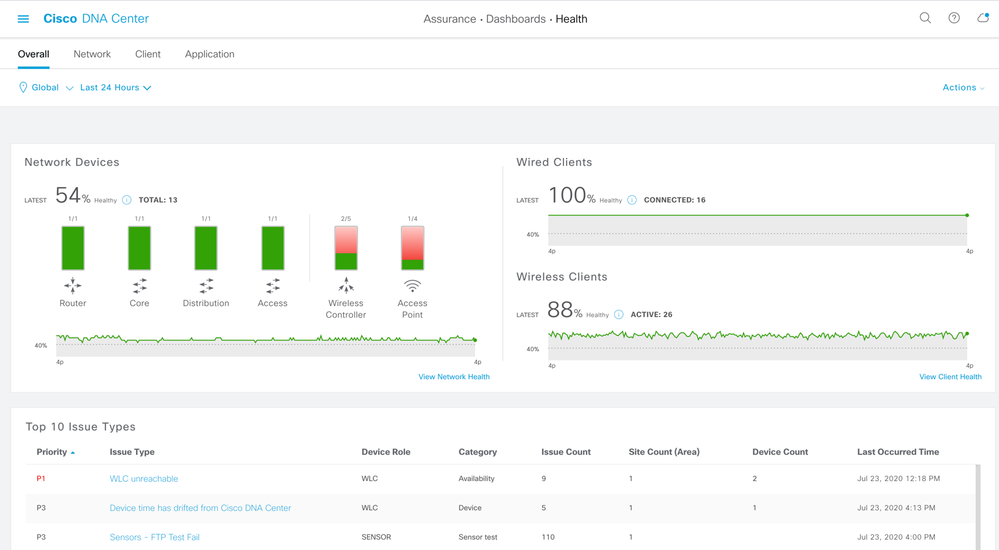
Step 1: Click the Menu icon and choose Assurance > Health. The Overall health dashboard appears
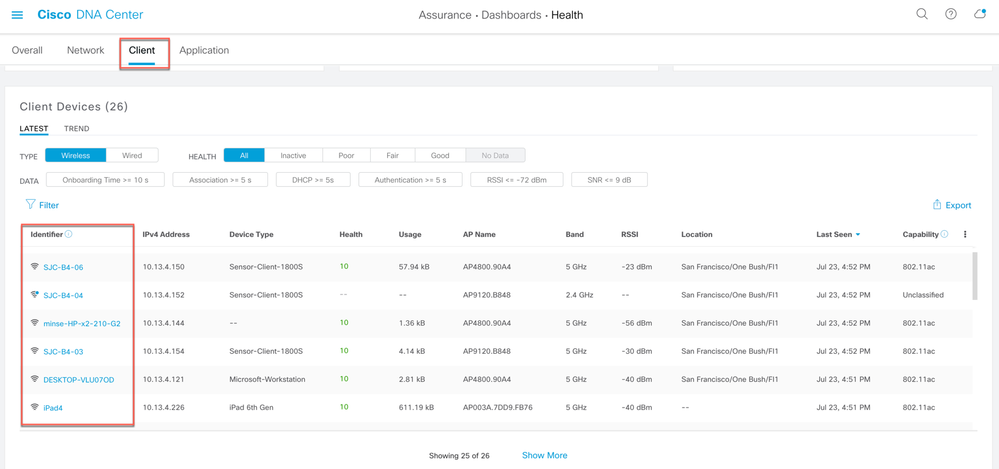
Step 2: Click the Client tab to navigate to the Client Health page. Scroll down to the client devices table and click the client user want to view the client 360 page.
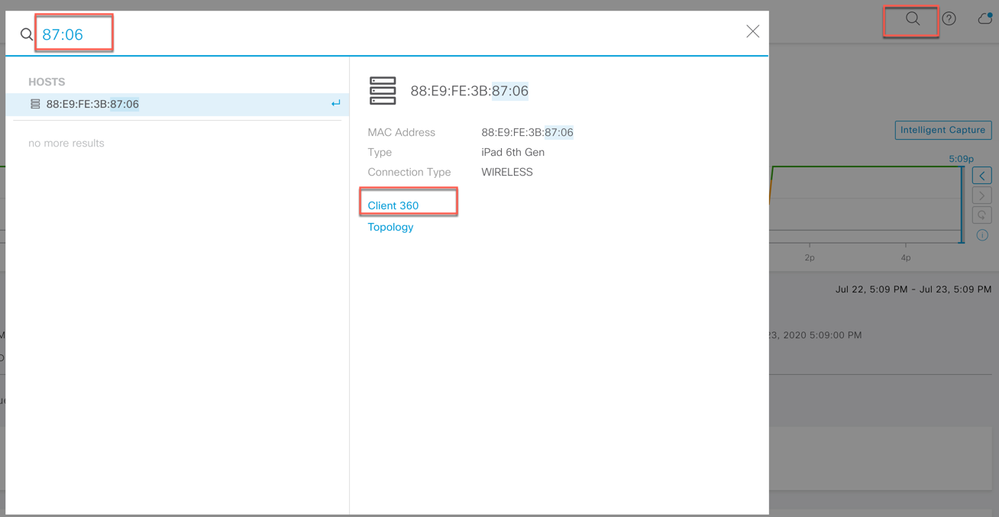
User can also click on the magnifying glass in the top right corner of DNA Center page to search the client. Enter either the client MAC address, the IP address, or the username the client used to join an 802.1X network.
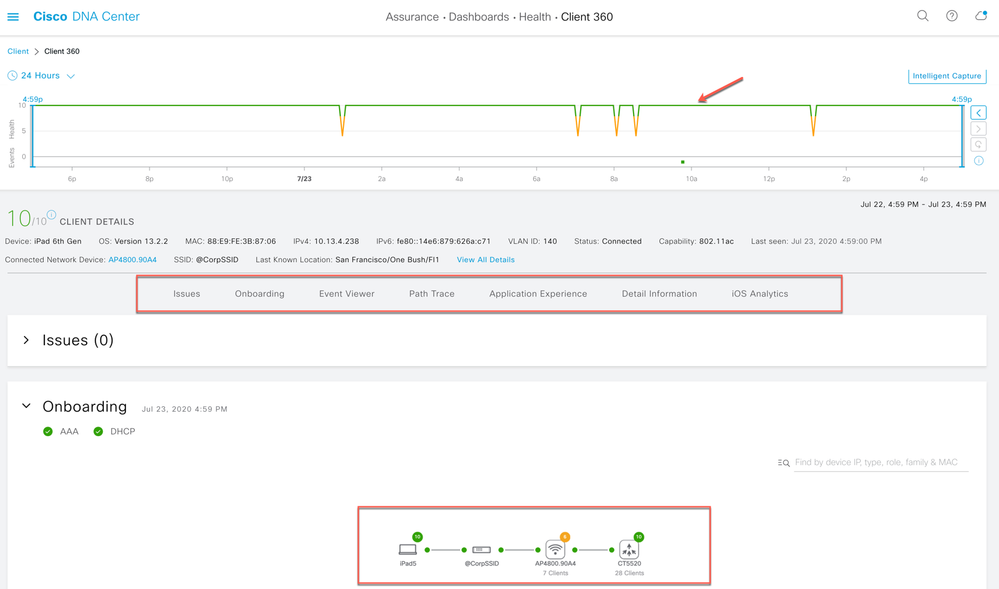
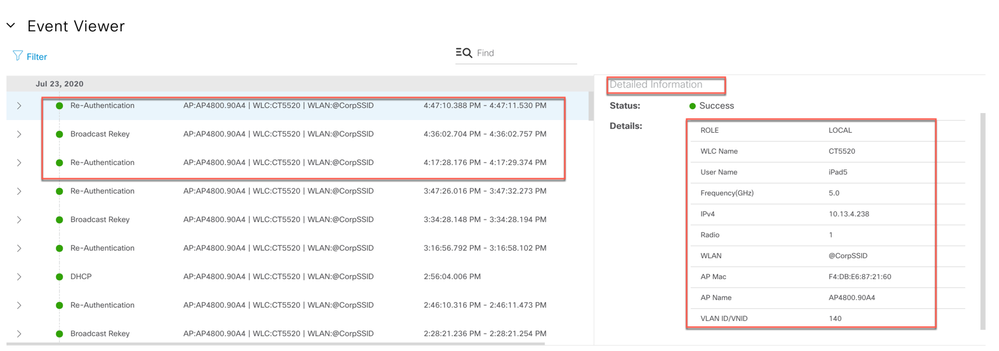
The client 360 view provides the holistic view about client statistics and details, on how client is onboarded, any issues being seen and detail onboarding events through Event Viewer.
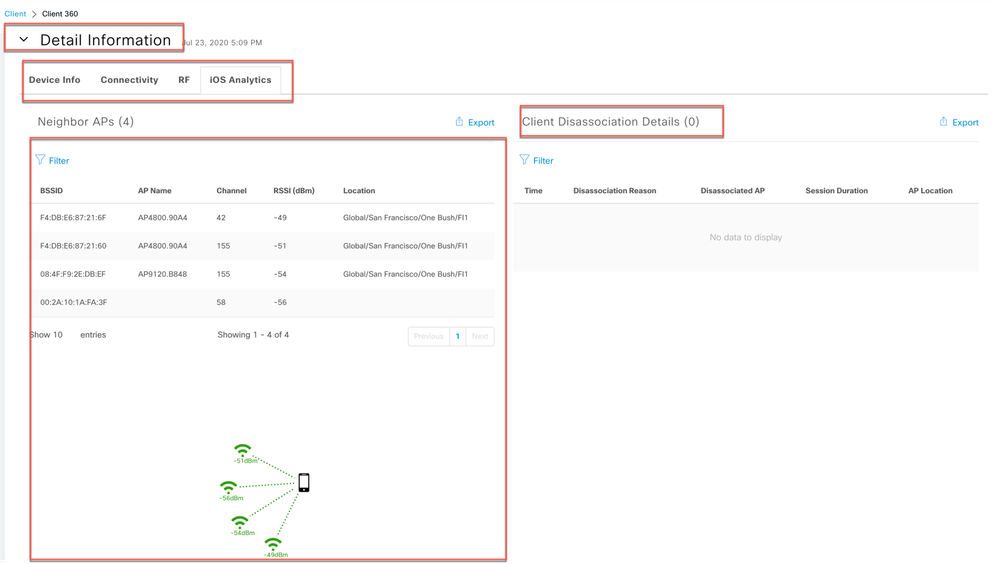
For client detail stats admin can view the Details Information view which comprises of (device info, Connectivity, RF stats and iOS Analytics) iOS Analytics is specifically for iOS devices to visualize how the iOS device is seeing the WiFi network.
Note: iOS Analytics is not supported on C9105, C9115 and C9120 Access Points
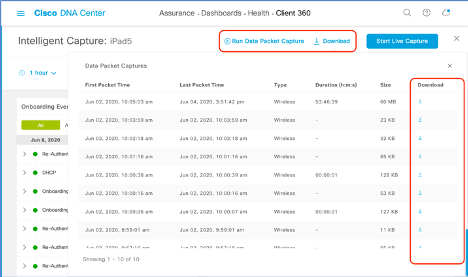
For more comprehensive and detail troubleshooting admin can leverage intelligent capture (iCAP) feature to run packet capture for the device. The Intelligent Capture is located on device 360 page as shown. Click on the Intelligent capture.
It opens the Intelligent Capture Client page and admin can run the live packet capture or anomaly PCAP, or run a data packet capture.
Note: Data packet capture is available on C9130 and 4800 Series APs
Once the packet capture is complete user can download the pcap file to perform further analysis.
Reference documents and VODs
-
OEAP Configuration Guide (AireOS 8.5): https://www.cisco.com/c/en/us/td/docs/wireless/controller/8-5/config-guide/b_cg85/configuring_officeextend_access_points.html
-
OEAP Configuration Guide (AireOS 8.8):https://www.cisco.com/c/en/us/td/docs/wireless/controller/8-8/config-guide/b_cg88/configuring_officeextend_access_points.html
-
OEAP WLC guided configuration VOD:https://www.youtube.com/watch?v=1GL3q7mCiqI
-
OEAP Cisco Validated Design ( AireOS):https://www.cisco.com/c/dam/en/us/td/docs/solutions/CVD/Aug2014/CVD-CiscoOfficeExtendDesignGuide-AUG14.pdf
- OEAP AireOS Split Tunnel configuration:https://www.cisco.com/c/en/us/support/docs/wireless-mobility/wireless-lan-wlan/215928-flexconnect-oeap-with-split-tunneling-co.html
-
1815T Deployment Guide:https://www.cisco.com/c/en/us/td/docs/wireless/controller/technotes/8-5/b_Cisco_Aironet_1815_Teleworker_Access_Point.html
-
Cisco DNA Assurance User Guide, Release 2.1.1:https://www-author3.cisco.com/c/en/us/td/docs/cloud-systems-management/network-automation-and-management/dna-center-assurance/2-1-1/b_cisco_dna_assurance_2_1_1_ug/b_cisco_dna_assurance_2_1_1_ug_chapter_01110.html
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: