- Cisco Community
- Technology and Support
- Data Center and Cloud
- Application Centric Infrastructure
- Single BD with Multilple Subnet integrate with single EPG
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Single BD with Multilple Subnet integrate with single EPG
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-12-2022 03:24 AM
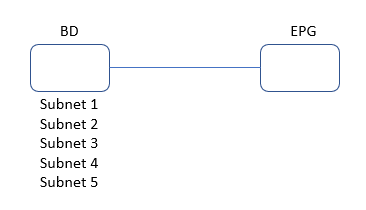
We have configured Single Bridge Domain(BD) with Multiple Gateway(i.e.; Multiple Subnet) and integrate with Single EPG.
Does it works on Network Centric .However, it is working on Application Centric on ACI Controller.
- Labels:
-
Cisco ACI
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-12-2022 03:44 AM
Hi @otgnwp ,
Firstly - the answer to your question is YES
But you need to understand that Network Centric and Application Centric are just human ideas that people use to explain one approach to another.
When you walk towards a building, do you walk from the south or the east? - It doesn't matter. You still get to the building
When you configure ACI, it doesn't matter - Network Centric, Application Centric - it is all the same to ACI. ACI does not understand those concepts any more than it understands south or east.
So if you use a single Bridge Domain with multiple gateways - it works in ACI. ACI does not even know that some people call this Application Centric - ACI does NOT CARE. You can call it Amazing Centric, or Green Centric whatever you want. None of those terms have any meaning to the APIC
Some people (and I think I may be one of them soon) declare there IS NO SUCH THING AS APPLICATION CENTRIC OR NETWORK CENTRIC
So the real question is
"Why do you care if your configuration works with Network Centric?"
If you answer that question, I may be able to give more advice.
Forum Tips: 1. Paste images inline - don't attach. 2. Always mark helpful and correct answers, it helps others find what they need.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-15-2022 08:04 AM
Just to add to Chris' comment - Network vs. App centric is about policy design rather than anything else. When we refer to Network Centric the design goal is to mimic what's currently deployed in your environment. 1 xEPG & 1 xBD typically get created on a VLAN/Subnet basis. Benefit here is it's simple and more or less maintains the legacy approach. The drawback here is its harder to improve your security posture like this when all endpoints are lumped into the same VLANs and/or Subnets. There's also little value to using multiple Application profiles with this design choice as your endpoints aren't really grouped together by Application, but more on VLANs/Subnet -hence "Network Centric".
Where App centric designs shine is where you have the ability to deploy policy as Greenfield where you may not be constrained by existing VLAN & subnet constraints. In this form, we aren't really concerned about VLANs or Subnets for that matter - the end goal is zero trust. App centric designs decouple any policy desing from the underlying networking contrusts such as VLANs & Subnets. With this approach you typically try and group endpoints into Application Tiers (EPGs), which belong to a common Application Profile. This allows for more granular control & visibility as you can apply things like SLA/QoS at the Application Profile level, as well as monitor the overall health of your endpoints by Application Profile groupings.
At the end of the day as mentioned, both designs work. There are some additional benefits with application centric designs. Where I find many customers struggle to move to Application centric designs are two hurdles:
1) Unknown Application Dependency Mappings - To truly get to that zero-trust model that App centric is all about it requires you to build your security policy within ACI (Contracts) according to what the application requires, and nothing more. For common off-the-shelf apps this may be easy to figure out, but for many legacy in-house apps those inter-app-tier communication requirements may not be well known (or forgotten).
2) Lack of understanding. Network centric follows the status quo. If you understand VLANs and Subnets in your existing network, than keeping that format in ACI is appealing. It does lessen the learning curve.
Where I see the most sucess in customers starting off with ACI is they will deploy ACI as network centric. Then as they gain confort and framiliarity with the solution they will deploy a new Greenfield app in an app centric design (no issues leveraging both designs together). This allows them to test the water with a zero-trust app deployment, see the benefits and adopt a new methodolgy to application deployment.
Apologies for the winded repsonse, but I'd really like to encourage more customers to explore app-centric deployements and evolve their DCs towards more of a zero-trust security model.
Robert
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide