- Cisco Community
- Technology and Support
- Data Center and Cloud
- Data Center and Cloud Knowledge Base
- Configuring TACACS+ Authentication to ACI Fabric with Cisco ACS
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
12-10-2017 06:55 PM - edited 03-01-2019 06:06 AM
This document will provide screenshots to outline the steps to setup TACACS+ configuration to ACI and also the configuration required on Cisco ACS server.
Please find the official Cisco guide for configuring TACACS+ Authentication to ACI: https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/apic/sw/2-x/Security_config/b_Cisco_APIC_Security_Guide/b_Cisco_APIC_Security_Guide_chapter_0100.html
ACS Configuration
*Note only specific web browsers and version are supported on Cisco ACS, check the release notes of your ACS versions to find the supported browsers. Using unsupported browsers can lead to configuration loss in ACS.
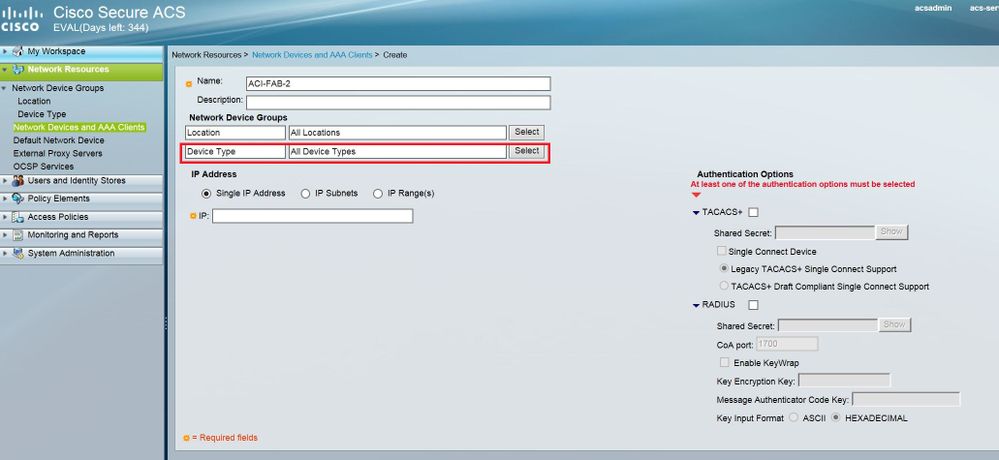
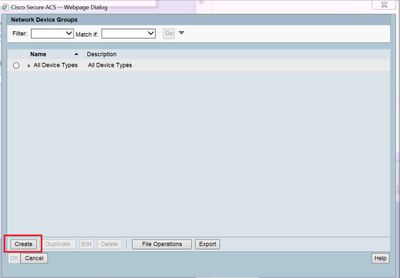
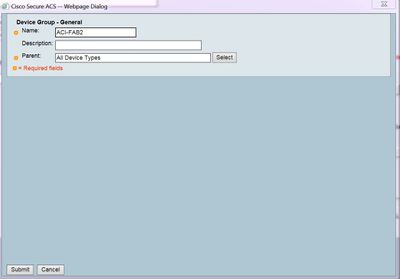
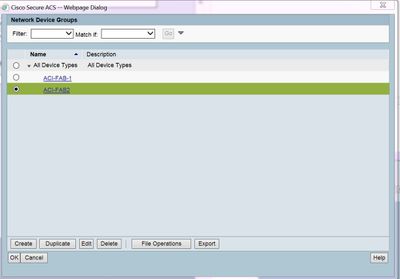
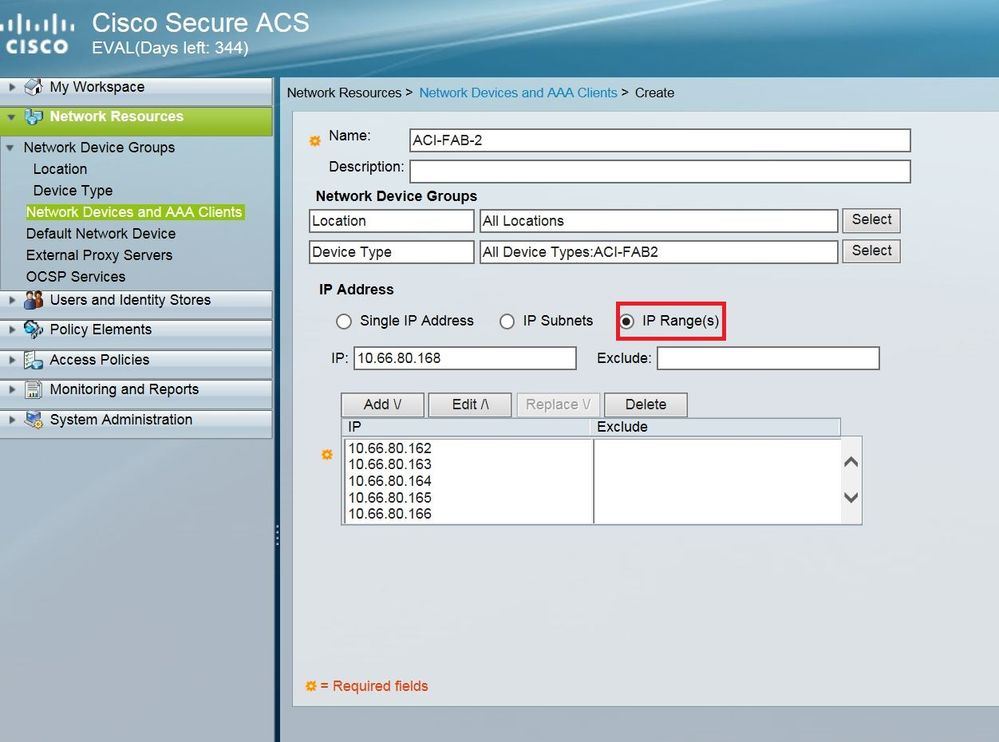
- First step is to configure the APIC and fabric node devices on the ACS. Navigate to Network Resource > Network Devices Groups > Network Devices and AAA Clients
Specify the client name, and create a device type.
Add the Cisco APIC and fabric node Ip Addresses (out-band or INB), ensure to select IP range to add multiple node addresses.
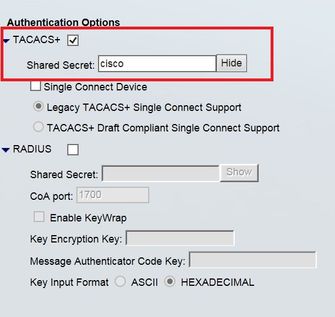
Select TACACS+ under the authentication options, the shared secret will be used for the Cis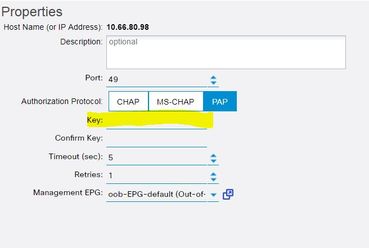
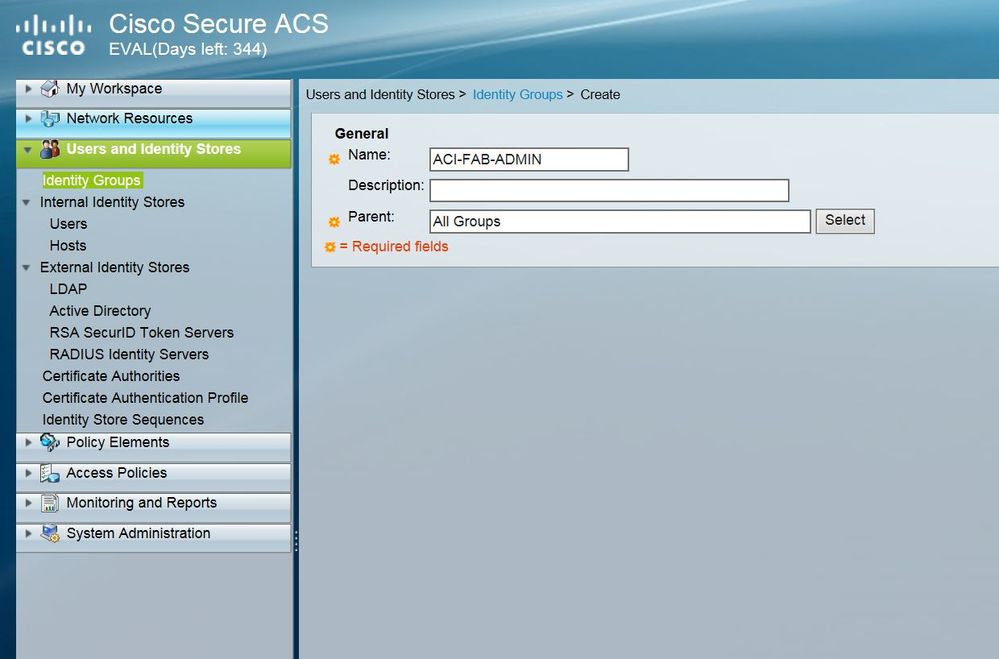
2. Next step is to configure users and Identity groups. Navigate to Users and Identity Stores > Identity Groups.
The identity group will group different types of users together, in the example below I have created an ADMIN Identity-group to group all users who will have admin privileges.
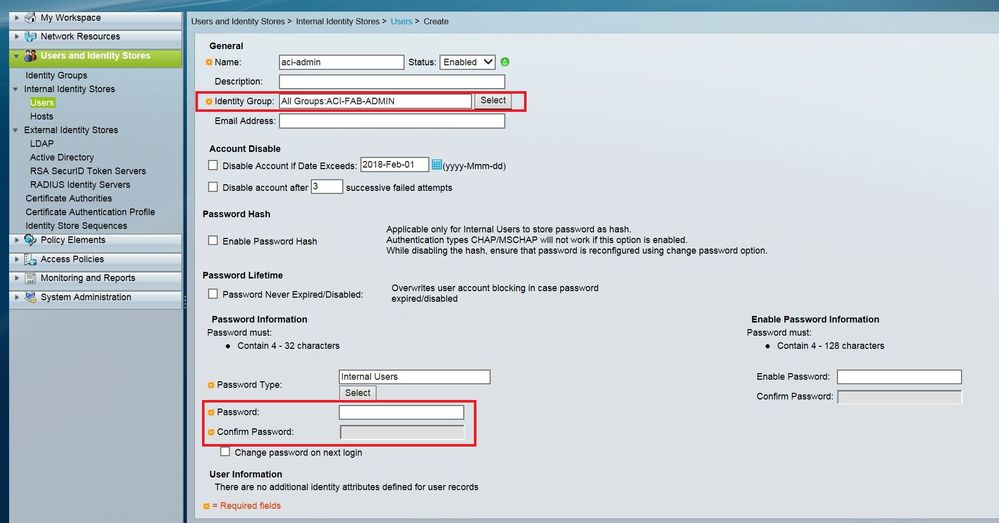
3. You can now configure the users, (these can be internal or external uses such as from Active Directory) navigate to Users and Identity Stores > Internal Identity Stores > Users. Create an admin user, map this user to the identity group, and configure a password.
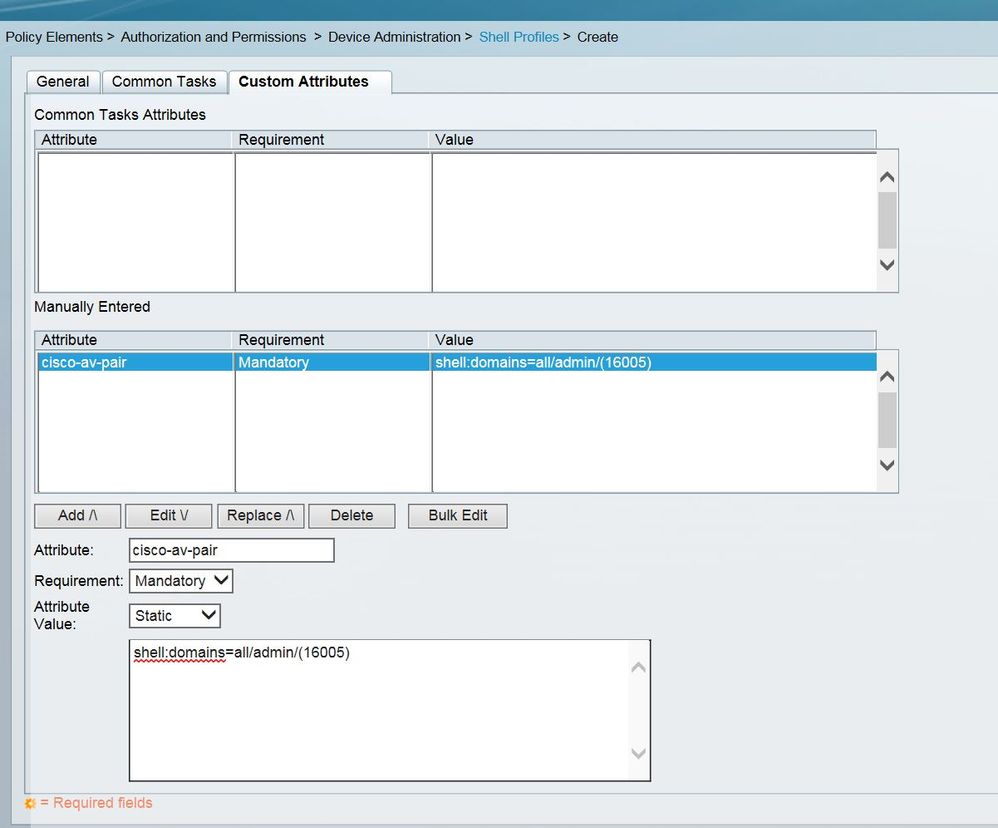
4. Create the policy elements, this is where we configure the Cisco AV pair, to specify the APIC required RBAC roles and privileges for different users
The AV pair are configured in the following format:
shell:domains = domainA/writeRole1|writeRole2|writeRole3/readRole1|readRole2,
domainB/writeRole1|writeRole2|writeRole3/readRole1|readRole2(16003) * Unix ID
Below are some examples of the av-pair strings for some different types of users:
- For users with admin access to entire fabric:
shell:domains = all/admin/(16002)
- For users with read-only access to fabric:
shell:domains = all//read-all (16003)
*note readonly users do not have access to leaf’s or spines, admin write privilege is required.
- For a user with admin access to tenants under security domain mydomain, and read only access to the rest of the tenants.
shell:domains = mydomain/admin/,all//read-all(16004)
* As best practice, Cisco recommend that you assign a unique UNIX user id in the range 16000-23999.If the UNIX user ID is not specified, ID 23999 is applied by the APIC system. There is a known bug if unique UNIX ids are not used.
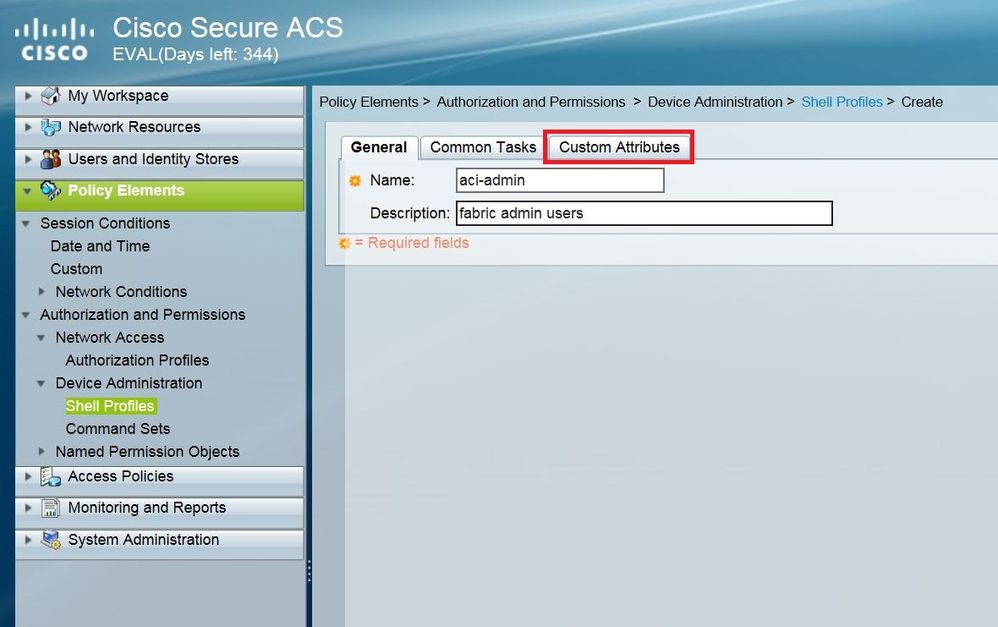
Navigate to Policy elements > Device Administration > Shell Profiles and create a new shell profile. Name the profile, and navigate to the ‘Custom attributes’ tab, here you can add the av-pair string.
5. Last step is to configure the access policies, this is where you tie it all together, mapping the user to the shell profile to the AAA clients. Navigate to Access Policies > Default Device Admin > Authorization.
Create a new Rule, mapping the identity group, the device type and shell profile.
Configuring APIC for TACACS+ ACCESS
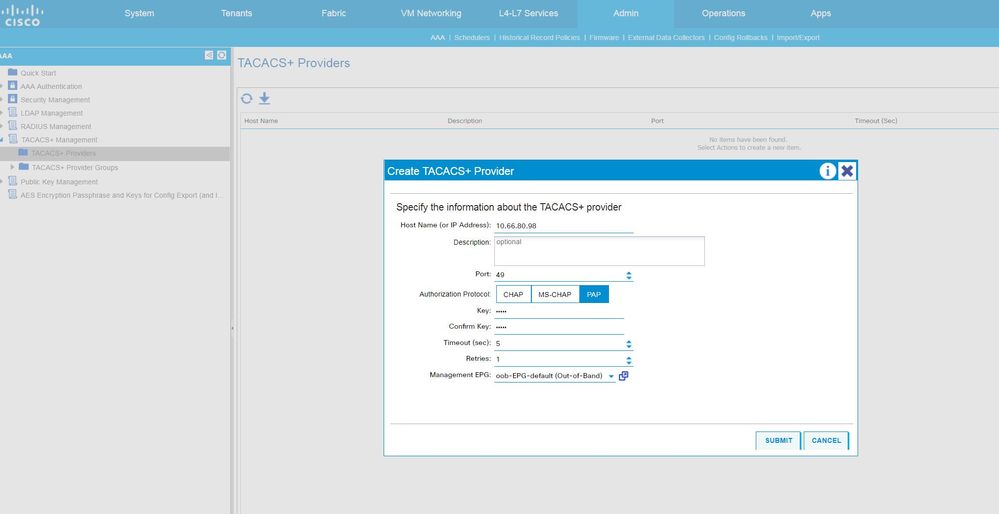
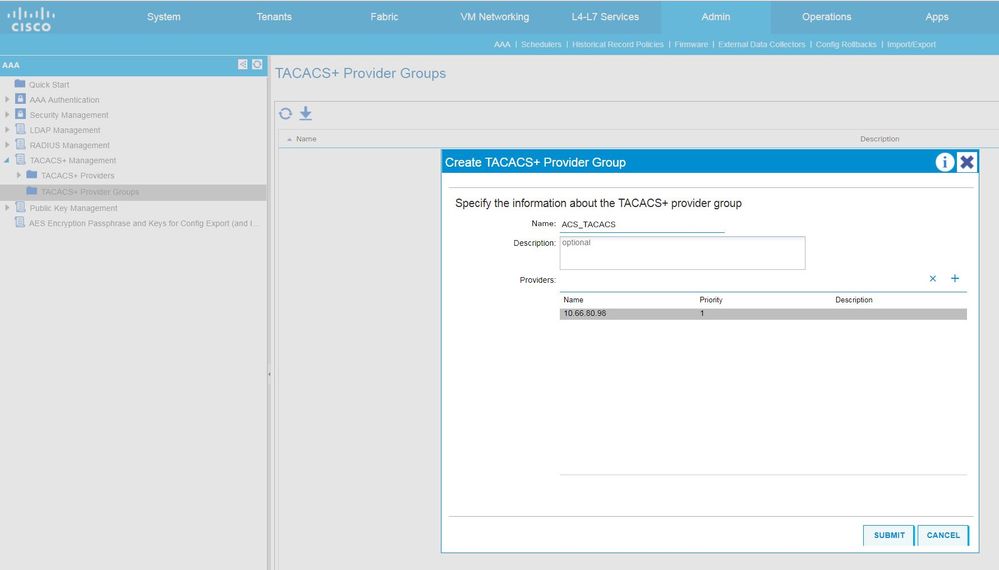
- First create the TACACS+ Provider, navigate to Admin > AAA > TACACS+ Management > TACACS+ Providers.
Here you will need to specify the ACS hostname (ensure DNS is setup in your fabric if using hostname) or IP, the port, (default is 49), the key (this should match the ‘shared secret’ configured on ACS) and also the management endpoint (Inb or OOB)
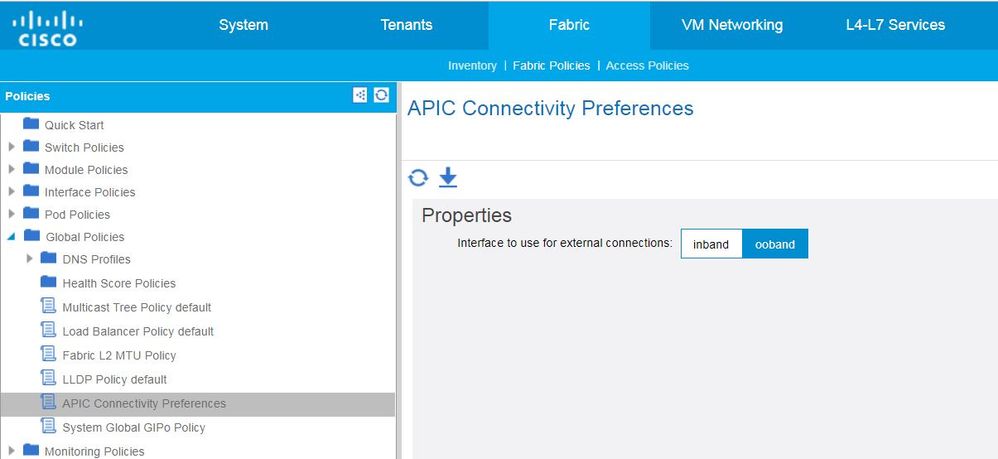
*Note if the APIC has INB management configured, choosing the OOB management EPG for the TACACS+ provider does not take effect as INB is the default preferred by APIC. In versions 2.1(1x) and higher there is an option to toggle between INB and OOB so to make OOB as the default management connectivity. Find this under Fabric > Fabric Policies > Global Policies > APIC Connectivity Preferences.
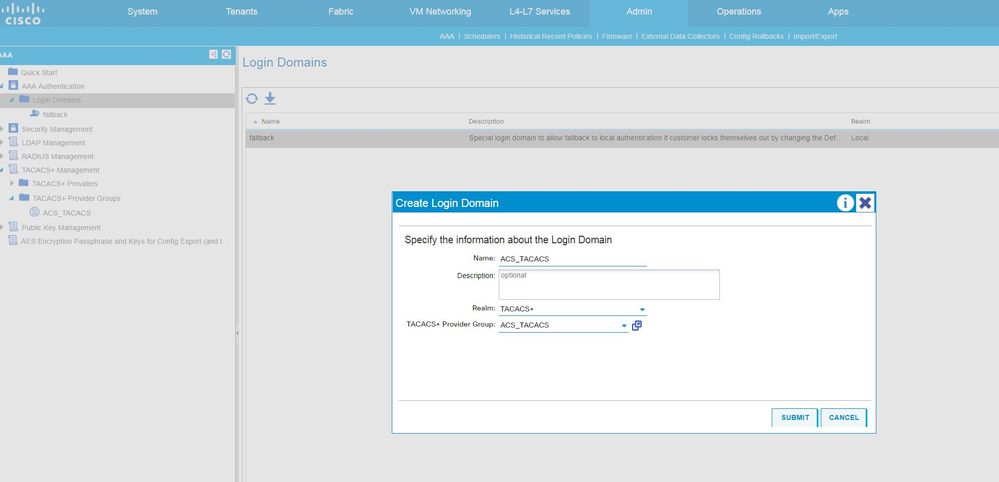
3. Create the Login Domain and map to TACACS+ Provider group. Navigate to Admin > AAA > AAA Authentication > Login Domains.
*You will notice a ‘fallback’ login domain is already created by default, this is the local domain to allow local authentication in case you are locked out of your fabric if the default authentication settings are changed.
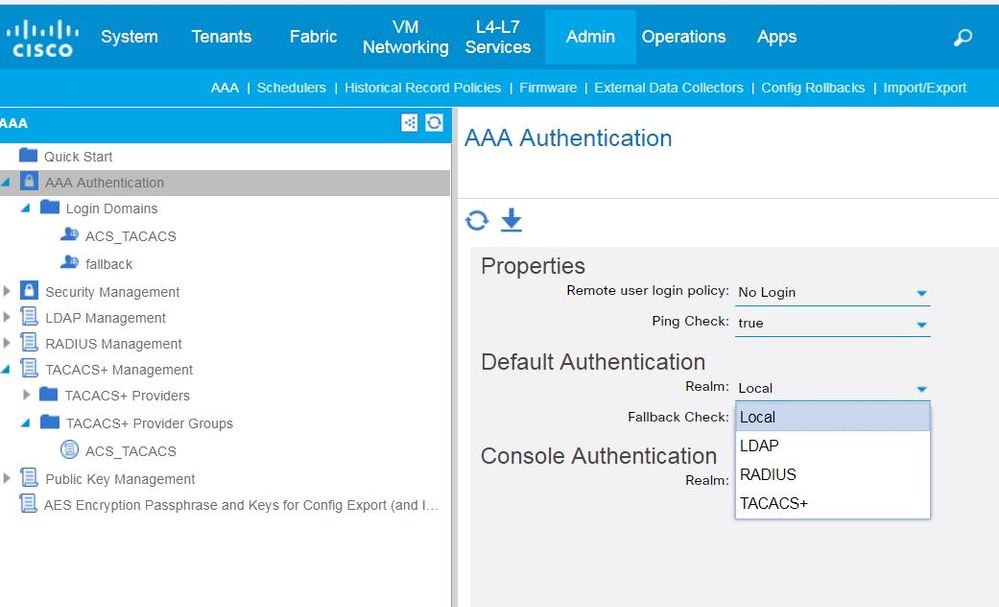
Changing the Default Authentication to your fabric.
If you would like TACACS+ to be the default authentication method when accessing the fabric you can make this change under the AAA authentication tab.
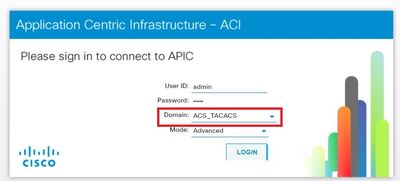
If TACACS+ is not configured as the default authentication method, (local is the default) you will need to explicitly select the login domain when logging in via GUI, or use the below format to access nodes using TACACS+ logins via cli.
Login format: ssh apic#domain\\username@ip
Recovering with Local Fallback User
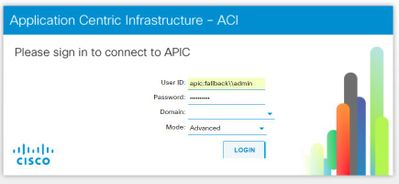
In the event that connectivity is lost to the TACACS+ server and you are locked out of your fabric you can use the local admin fallback user. Below is the format to do this:
From the GUI, use apic:fallback\\admin.
From Cli, use ssh apic#fallback\\admin
Always ensure under Default Authentication that ‘Fallback Check’ is set to false, otherwise you will not be able to recover with local login credentials.
Verification
A couple of check to make sure your configuration is correct:
1. First check to make sure you can ping the TACACS+ Server from both Apic and Leaf nodes. This can rule out any network issues.
2. Check the configuration has been correctly pushed to the Leafs and APICs:
Leaf101# show tacacs-server groups
total number of groups:1
following TACACS+ server groups are configured:
group ACS_TACACS:
server: 10.66.80.98 on port 49
deadtime is 0
Leaf101# show aaa authentication
default: local
console: local
3. Check the nginx logs and search for the TACACS+ provider IP to confirm reachability, these logs can sometimes give you a clue to why TACACS connectivity is not working.
leaf101# grep 10.66.80.98 /var/log/dme/log/nginx.log | less
34703||17-12-11 10:40:33.239+08:00||aaa||DBG4||||Received response from 10.66.80.98 - notifying callback handler (IPv4)||../dme/svc/extXMLApi/src/gen/ifc/app/./ping/lib_ifc_ping.cc||757
34703||17-12-11 10:40:33.239+08:00||aaa||DBG4||||Received update on status of 10.66.80.98 (DN uni/userext/tacacsext/tacacsplusprovider-10.66.80.98) - status is \ ALIVE||../dme/svc/extXMLApi/src/gen/ifc/app/./pam/PamWorker.cc||1448
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Awesome write up!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Great write up! I would have loved to have had this document when we initially set up our fabric. Took us a while to figure out the correct av-pair. The official docs at the time had some formatting issues that was clobbering proper whitespacing.
I would like to point on that the steps are the same for ISE 1.2+ instead of ACS, locations have just moved to Work Centers > Device Administration.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: