- Cisco Community
- Technology and Support
- Security
- Endpoint Security
- Re: Preventing Lsass Dump with Cisco Secure Endpoint
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-24-2021 03:16 PM
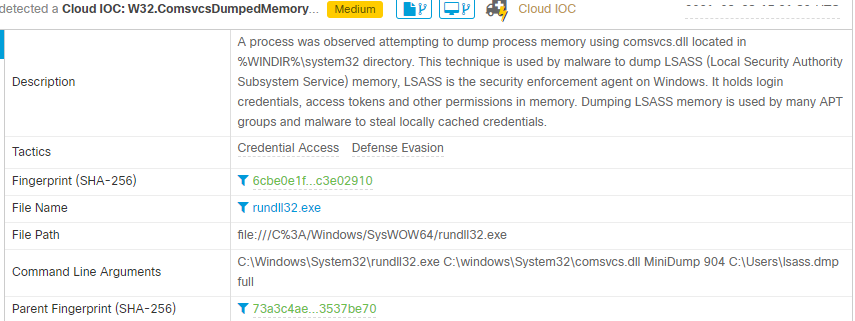
Cisco Secure Endpoint flags Lsass dump as Cloud IOC. EDR tool did not stop the dump, most likely because Windows native tools were used. I have ticketing in place to alert on the event. Does anybody know how do I blacklist the activity(command line in the snip below)?
Solved! Go to Solution.
- Labels:
-
AMP for Endpoints
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2021 06:01 AM
Hello Paladin,
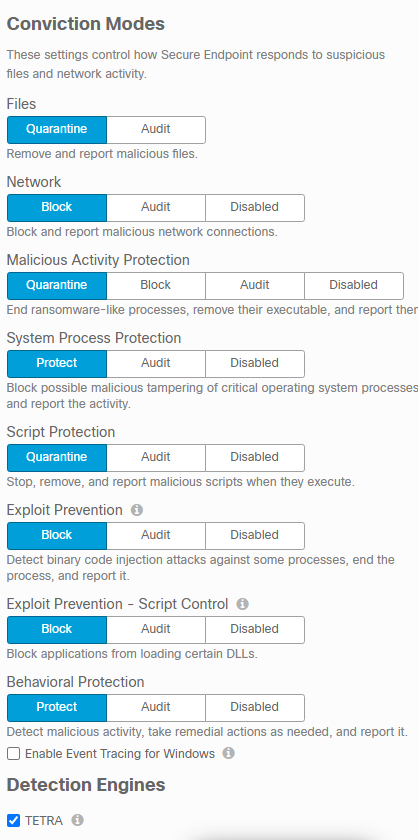
while you have System Process Protection engine enabled, Cisco Secure Endpoint most likely stopped lsass dump, even though it didn't report it to AMP console. I have quickly checked that in my lab:
-- when Secure Endpoints is enabled - lsass.dmp file has 0KB
-- when Secure Ednpoints is disabled - lsass.dmp file is expected memory dump.
To confirm that, here is snippet from Secure Endpoint logs (sfc.exe.log) when it blocks memory dump with mentioned command (you need Secure Endpoints debugs enabled to see that):
Aug 25 14:30:02 [6988]: SDEventHandler::HandleSDBlockEvent: src_pid: [7912] src_path: [\\?\C:\Windows\System32\rundll32.exe] mod_path: [\\?\C:\Windows\System32\rundll32.exe] region_type: [0x1000000] victim_pid: [712] victim_path: [\\?\C:\Windows\System32\lsass.exe] SF: [0xF] RF: [0xF]
-Wojciech
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2021 06:01 AM
Hello Paladin,
while you have System Process Protection engine enabled, Cisco Secure Endpoint most likely stopped lsass dump, even though it didn't report it to AMP console. I have quickly checked that in my lab:
-- when Secure Endpoints is enabled - lsass.dmp file has 0KB
-- when Secure Ednpoints is disabled - lsass.dmp file is expected memory dump.
To confirm that, here is snippet from Secure Endpoint logs (sfc.exe.log) when it blocks memory dump with mentioned command (you need Secure Endpoints debugs enabled to see that):
Aug 25 14:30:02 [6988]: SDEventHandler::HandleSDBlockEvent: src_pid: [7912] src_path: [\\?\C:\Windows\System32\rundll32.exe] mod_path: [\\?\C:\Windows\System32\rundll32.exe] region_type: [0x1000000] victim_pid: [712] victim_path: [\\?\C:\Windows\System32\lsass.exe] SF: [0xF] RF: [0xF]
-Wojciech
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2021 09:06 AM
Thank you for your response!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2021 09:10 AM - edited 08-25-2021 09:15 AM
Hello @Paladin,
some info about the Cloud IOC. This engine is processing file activity, network activity, command line activity and process activity in the backend. So Cloud IOCs will never block directly on the endpoint. But, Cloud IOCs can be used to trigger Post Infection tasks like isolating the endpoint from the backend, generating a forensic snapshot and others.
Behavioral Protection Engine is able to actively block complex attack scenarios on the endpoint, this means bringing Cloud detections to endpoint protection.
As @Wojciech Cecot explained, you may check your endpoint to see if SPP Engine blocked the LSASS dump.
Forgot to mention, if the CloudIOC is generated by a legitimate application, we will provide Cloud IOC exclusions in future releases of Secure Endpoint.
Greetings,
Thorsten
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-13-2022 12:46 PM
I am having THIS ISSUE with a legitimate application - Qualys scans. HOW do I WHITELIST THIS?
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide