- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: ASA Transparent mode ACL
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ASA Transparent mode ACL
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-07-2018 01:50 AM - edited 02-21-2020 08:26 AM
Hi.
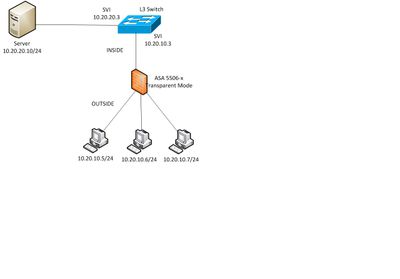
I have the following ASA in Transparent mode. No external access from the network, it simply to segregate the devices shown.
I need to allow the 3 devices on the outside interfaces to access a server / port off the inside interface. Think I’ve got the config correct (please correct me if not). I’m not sure on the last statement, i.e. where to apply the access group to the inside interface, is traffic entering the Inside Interface from outside devices classed as In or Out to the Inside Interface and the rest of the network.
interface bvi 1
ip address 10.20.10.10 255.255.255.0
interface gigabitethernet 1/1
bridge-group 1
nameif inside
security-level 100
no shutdown
interface gigabitethernet 1/3
bridge-group 1
nameif outside_1
security-level 0
no shutdown
interface gigabitethernet 1/4
bridge-group 1
nameif outside_2
security-level 0
no shutdown
interface gigabitethernet 1/5
bridge-group 1
nameif outside_3
security-level 0
no shutdown
object-group network Outside_Servers
network-object host 10.20.10.5
network-object host 10.20.10.6
network-object host 10.20.10.7
object-group network Internal_Server
network-object host 10.20.20.10
access-list INBOUND extended permit tcp object-group Outside_Servers object-group Internal_Server eq <port I specify>
access-group INBOUND in interface inside
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-07-2018 02:29 AM - edited 11-07-2018 03:03 AM
Hi,
IN >> will examine all traffic RECEIVES on the interface through an ACL
OUT >> will examine all traffic LEAVES on the interface through an ACL
With extended ACL, the general best practice is as close to the source as possible. So that it would be inbound on the ingress interface.
object-group network Inside_Servers
network-object host X.X.X.X
!
object-group network Outside_Servers
network-object host X.X.X.X
!
access-list INBOUND extended permit tcp object-group Outside_Servers object-group Inside_Servers eq <port I specify>
!
access-group INBOUND in interface outside
HTH
Abheesh
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-07-2018 02:37 AM
Hi Abheesh. Thanks for the reply. So the statements I have are correct then? and follow best practice?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-07-2018 02:45 AM
The requirement is:
"I need to allow the 3 devices on the outside interfaces to access a server / port off the inside interface"
So the ACL needs to be applied inbound on the outside?
Regards, mk
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-07-2018 02:50 AM
Hi. So as I have 3 outside interfaces, I guess I need to apply this Inbound on each of the 3 outside interfaces individually, i.e outside_1, outside_2, outside_3?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-07-2018 02:54 AM - edited 11-07-2018 02:56 AM
if you can apply ACLs like that in this mode then yes! tbh I don't know enough about the transparent firewall implementation, ive always installed ASAs in default routed mode - up to now anyway
regards, mk
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-07-2018 02:58 AM
Hi,
For extended ACL general best practice is as close to the source as possible, So that it would be inbound on the ingress interface. In your case if the source is from OUTSIDE zone, then bind to outside interface
HTH
Abheesh
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-07-2018 02:32 AM
ive always used routed mode but im sure the ACLs work the same way
the access-group cmd has to applied to the outside interface/s as they are the ingress ports for traffic from the PCs
regards, mk
please rate if helpful or solved :)
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide