- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Cisco ISE web redirect not working
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 02:41 AM
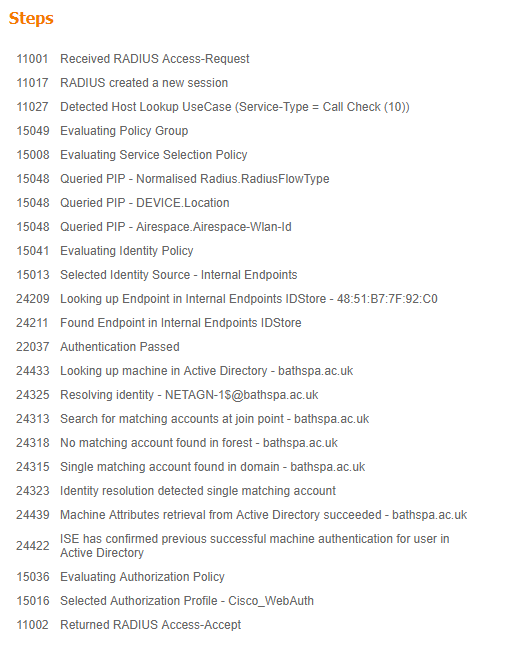
Can anyone help with this. I have an open SSID doing MAC filtering to ISE with the following auth rules;
My devices is hitting correct rule for the unknown MAC but it is not redirecting me to the guest portal & is allowing me access in the associated VLAN assigned to the WebAuth policy.
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 05:35 AM
Ok. Check the ACL on the WLC and ensure the case is the same as defined on ISE and spelling.
Check this page and double check the configuration of the WLC configuration.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 07:16 AM
Hi,
Glad to hear it's working now. I haven't used Guest for a log time, but does this link do what you want? This is to configure approval request email to a sponsor.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-07-2019 12:18 AM
After applying the cert to the admin role & restarting ISE all portals on all browsers are now accepting the certificate. Seems strange that they didn't when we applied it to the portal role because that doesn't require a restart.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 02:54 AM
Just to add, I can browse to the redirect link from the device.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 03:19 AM
When you access the link from the device is it via FQDN or IP address?....can the device resolve the dns hostname of the ISE PSN?
Can you confirm the redirect ACL been applied to the interface?...what is the output of "show authentication session interface Gi x" ?
What is the configuration of your called ACL_WEBAUTH_REDIRECT?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 04:52 AM
Hi,
Accessing the link works using the FQDN & the client can resolve this.
What interface would the ACL be applied to being this a wireless connection?
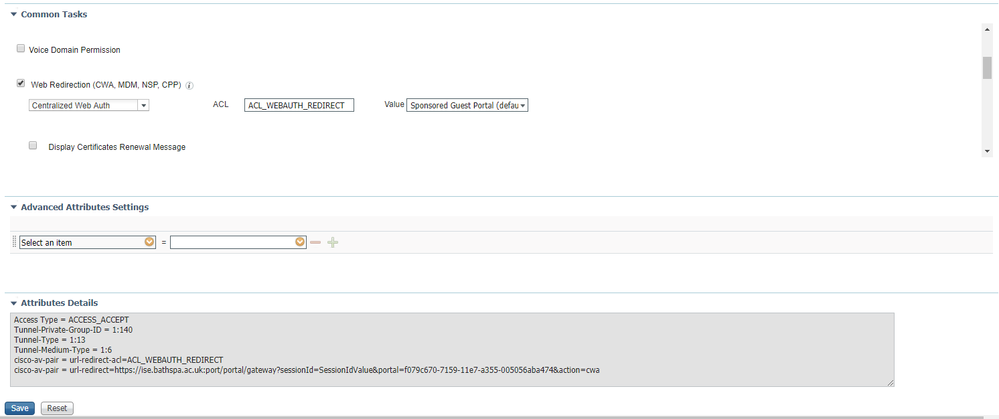
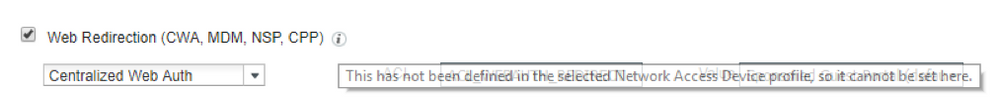
Below show the attribute of the Cisco_WebAuth profile but where to I find the configuration of the ACL_WEBAUTH_REDIRECT.
There is also a "!" withe the following note;
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 05:02 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 05:26 AM - edited 03-01-2019 05:33 AM
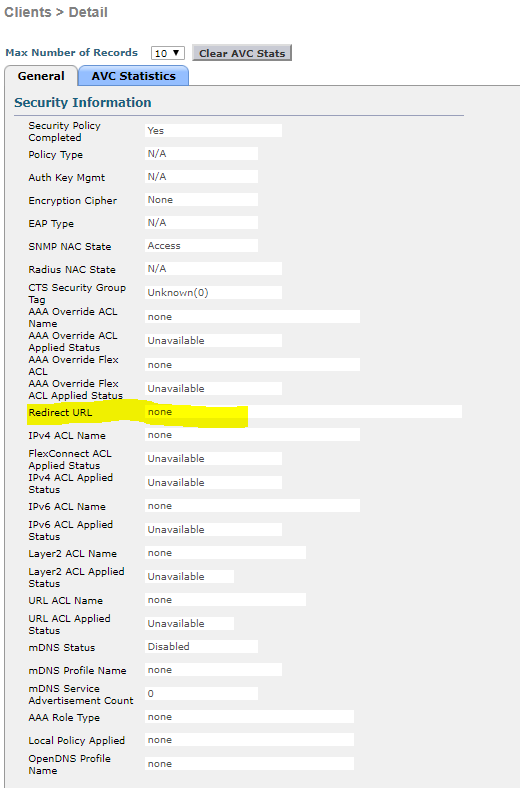
It doesn't look like it is applying the ACL. Do I need to create the ACL on the WLC as well?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 05:35 AM
Ok. Check the ACL on the WLC and ensure the case is the same as defined on ISE and spelling.
Check this page and double check the configuration of the WLC configuration.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 06:17 AM
Awesome thank you. It works. Wish I had this guide before.
I've another question now.
A guest theoretically could enter any details they like on the registration page to get access. Is there a way to verify them by email or any other methods? We sometimes have minors on site & they might need a different level of access or URL filtering, either way, for compliance we would have to be able to identify the users.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 07:16 AM
Hi,
Glad to hear it's working now. I haven't used Guest for a log time, but does this link do what you want? This is to configure approval request email to a sponsor.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 09:41 AM
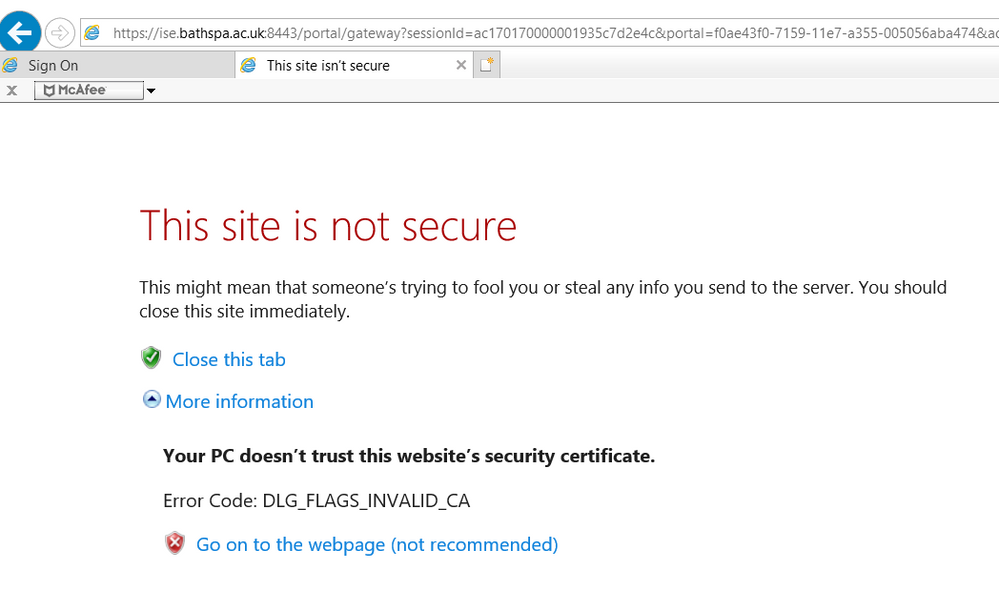
Only issue is the web page only seems to work with IE or edge. Is there support for other browsers & mobile devices?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-01-2019 12:23 PM
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-04-2019 06:08 AM - edited 03-04-2019 06:09 AM
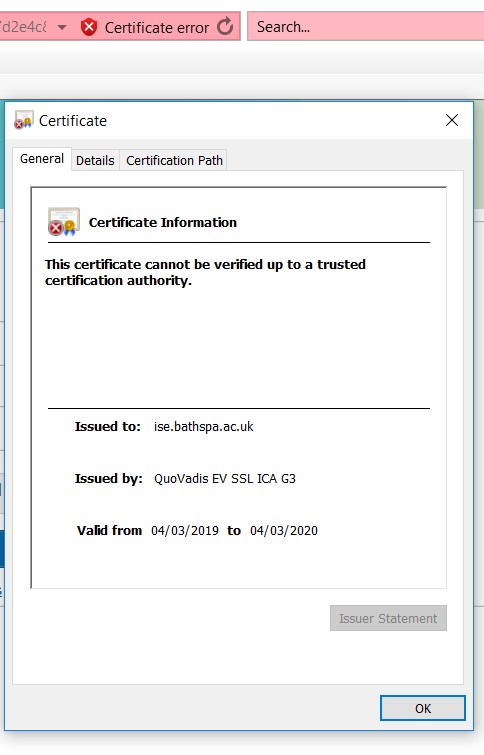
We have imported the full certificate chain that has been signed by a CA authority & bound the original cert request. It has being used by the default portal certificate group and we can confirm in the browser when redirected that is is using this certificate but it is still saying it is not trusted.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-04-2019 07:16 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-04-2019 08:59 AM
No it doesn't
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-04-2019 09:03 AM
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide