- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Configuring ACS 5.4 to authenticate Role Based Access Control (RBAC) users on a Nexus 5000 via TACAC...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Configuring ACS 5.4 to authenticate Role Based Access Control (RBAC) users on a Nexus 5000 via TACACS+
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-21-2014 11:30 AM - edited 03-10-2019 09:18 PM
There is a great document on the site for configuring ACS 5.X to authenticate voa TACACS+ but with 5.4 - there is possibly an extra step required.
https://supportforums.cisco.com/docs/DOC-14273
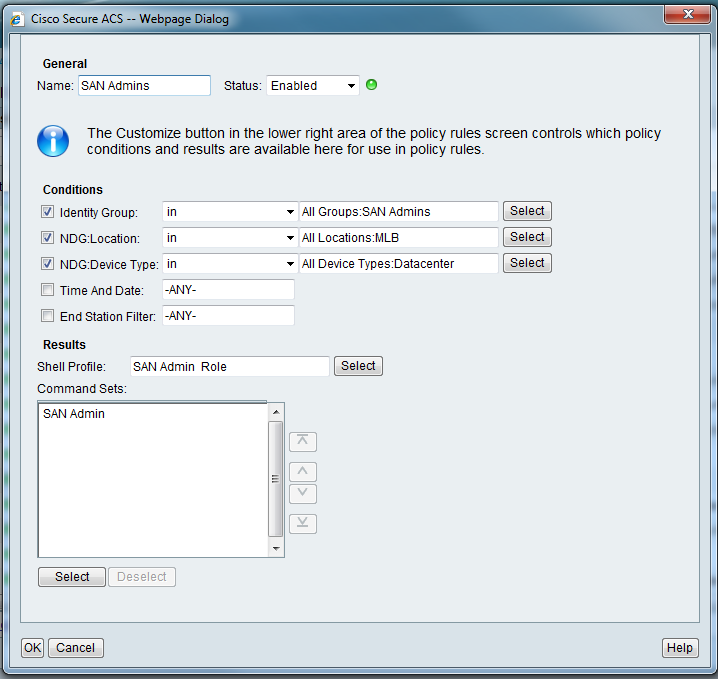
In 5.4 where you map the Shell Profile to the Authorization Policy – you are now required to specify a Command Set undert eh Shell Profile, whihch 5.2 didnt have. Trying to accomplish using the default san-admin role in NX-OS.
- Labels:
-
AAA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-21-2014 09:20 PM
I think the command set does not matter.
Because the Nexus takes only the role and does not use per-command authorization (AFAIK), then it will take the role from the shell profile but selecting the command set does not matter because it does not use per command authorization.
I used command sets with CRS-1 and they had no effect. Only the shell profile configuration matters.
What is the situation at your end? do things work fine with/without selecting the command set? or putting empty command set in place?
Rating useful replies is more useful than saying "Thank you"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-22-2014 07:53 AM
Amjad - thank you for post.
The first thing I found was the Command Set feature is customizeable - it can be removed by:
“On Access Policies>Authorization> Click customize, and remove the command set from the selected side, as you do not wish to use commands sets.”
The second thing is when both the Shell Profile and the Command Set are used together - the most restrictive takes precedence. I applied a PermitAll command set but was still limited tothe premsisions set forth inthesan-admin NX-OS role,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-22-2014 09:14 PM
Jenny - Thanks for the info.
So, if you are mentioning taht the most restrictive takes place, does that mean if you choose DenyAll then you will not be able to issue any command regardless of your role?
Rating useful replies is more useful than saying "Thank you"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-23-2014 12:40 PM
In this instance with the Nexus 5K - if I chose DenyAll as the CommandSet - I get denied right away.
SWITCH2# conf t
Error: AAA authorization failed AAA_AUTHOR_STATUS_METHOD=16(0x10)
SWITCH# sh run
Error: AAA authorization failed AAA_AUTHOR_STATUS_METHOD=16(0x10)
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide