- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Re: Console Server TTY/Port Control with ISE
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-07-2022 01:57 PM
Good Evening, All,
Does anyone know how I might refer to a particular TTY line or range of TTY lines on a device to use as an authorization condition for TACACS device administration in ISE? We are providing console services via an async module with a few octa cables, and I would like to limit access for a certain LDAP group to the async lines or specific async lines only. It is not clear to me how to reference those lines in a network condition. I have been able to see that when I connect to one of these lines and authenticate, which allows me access to a console or serial device connected to the other end, ISE receives a "Device Port" authentication attribute from the authenticating console server with a value of "tty<something>" (i.e. 0/1/1 or 0/1/0).
Any help is appreciated.
Thank you,
Nathan
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-06-2023 12:51 PM - edited 04-06-2023 12:52 PM
@Mike.Cifelli , I apologize for not replying for so long, but I just wanted to provide an update. This fell on the back burner but came back up again in the last few weeks. I ultimately ended up doing it in TACACS and used a "Device Port Network Condition" with an entry like "<network device name>,tty0/1/12" on the "Devices" tab of the condition set. I then used that condition in a device admin policy authorization rule.
Thank you!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-08-2022 03:59 AM
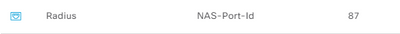
I think what you are looking for condition wise is something like this:
NAS Port ID - tty1
Taking a look at a detailed radius live log will show you this information:
Then authz condition:
HTH!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-09-2022 03:26 AM
Thank you, @Mike.Cifelli ,
I'll try this as soon as I get an opportunity and let you know the outcome. My only doubt comes from not seeing "NAS-Port-Id" in the session logs.
Regards,
Nathan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-09-2022 04:28 AM
My only doubt comes from not seeing "NAS-Port-Id" in the session logs.
-NAS-Port-ID is a radius attribute. Take a look at this: ISE Profiling Design Guide - Cisco Community - Device Sensor 'Configuring Radius Probe' section. The RADIUS probe collects attributes sent in RADIUS accounting packets by the Device Sensor feature.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-06-2023 12:51 PM - edited 04-06-2023 12:52 PM
@Mike.Cifelli , I apologize for not replying for so long, but I just wanted to provide an update. This fell on the back burner but came back up again in the last few weeks. I ultimately ended up doing it in TACACS and used a "Device Port Network Condition" with an entry like "<network device name>,tty0/1/12" on the "Devices" tab of the condition set. I then used that condition in a device admin policy authorization rule.
Thank you!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide