- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Re: DACL is not applied well in ISE.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-28-2020 12:13 AM
DACL is not applied well in ISE.
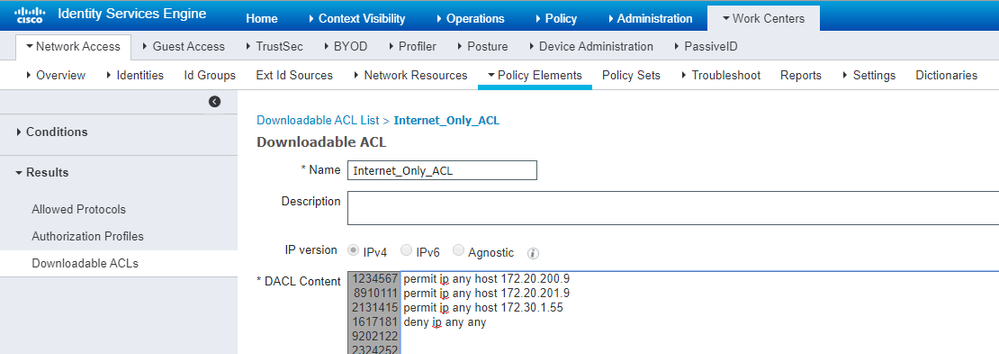
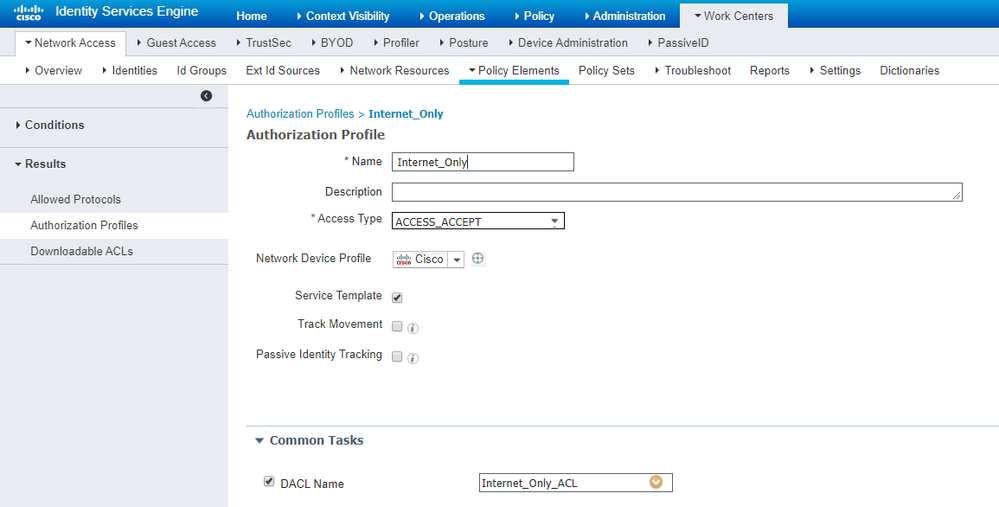
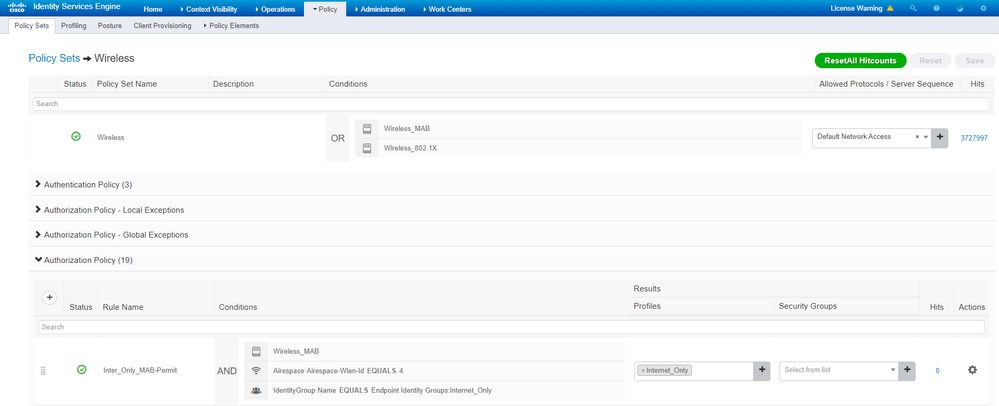
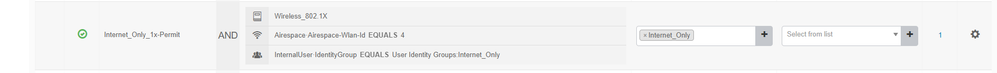
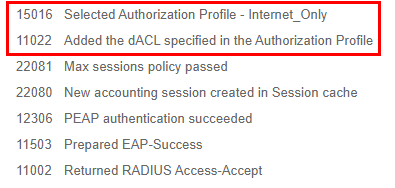
I configured dACL as above.
However, you can ping anywhere.
If you look at the log, it appears that dACL is applied.
What is the problem ??
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-28-2020 03:40 AM
Is this a Cat 9800 WLC? In that case I don’t know much about it because it’s IOS-XE based.
But in the classic AireOS there is no dACL. The ACL lives on the WLC and RADIUS only sends the ACL name in the Access-Accept.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-04-2020 05:10 AM
dACL is only used in Cisco LAN Switches - not Cisco WLAN Controller (at least, not on the "legacy" AireOS stuff like your 5520)
The principle here is that you must configure all the ACLs on the 5520 itself. e.g. if the WLAN is centrally switched, then it's under Security > ACLs (somethig like that) - beware that for FlexConnect you must choose the Flex ACL (because the ACLs then get applied on the APs themselves, and not on the Central Controller).
ISE's job is to send the ACL Name to the WLC during the Access-Accept. That applies the ACL for that Session. Make sure the name in the ISE Result is identical to that configured on the WLC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-28-2020 02:51 AM
Have you checked the status of the session on the switch? Are you sure the dACL has been downloaded?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-28-2020 03:05 AM
The switch is not registered with ISE.
WLC-ISE environment.
I want to control clients with ACLs in a wireless environment.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-28-2020 03:40 AM
Is this a Cat 9800 WLC? In that case I don’t know much about it because it’s IOS-XE based.
But in the classic AireOS there is no dACL. The ACL lives on the WLC and RADIUS only sends the ACL name in the Access-Accept.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-28-2020 05:39 AM
I agree with @Arne Bier . In regard to AireOS you configure the ACLs on the controller. I know on the 5520 WLC this can be found under security->access control lists. Then reference which specific airespace acl in the respective authz profile.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-03-2020 10:36 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-04-2020 05:10 AM
dACL is only used in Cisco LAN Switches - not Cisco WLAN Controller (at least, not on the "legacy" AireOS stuff like your 5520)
The principle here is that you must configure all the ACLs on the 5520 itself. e.g. if the WLAN is centrally switched, then it's under Security > ACLs (somethig like that) - beware that for FlexConnect you must choose the Flex ACL (because the ACLs then get applied on the APs themselves, and not on the Central Controller).
ISE's job is to send the ACL Name to the WLC during the Access-Accept. That applies the ACL for that Session. Make sure the name in the ISE Result is identical to that configured on the WLC
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide