- Cisco Community
- Technology and Support
- Security
- Network Access Control
- ISE - VPN profiling with Apple iPhone devices
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2017 05:25 PM
Hi,
I got an issue with Apple devices such as iPhone and iPADs when connecting through VPN the ISE is not doing profiling with the Apple devices.
With Android is working well. We create a policy for Android devices that connect through AnyConnect VPN for limited access with a DACL.
We are trying to do the same with Apple Devices connecting through VPN.
Hope you can help.
Regards.
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-23-2017 10:12 AM
How are you profiling them? What methods are you relying on?
Is it at least profiling as an apple-device?
Are you redirecting to a portal to get the http user agent string for intitial login to help profile them? With ASA we don’t have DHCP or HTTP Sensor we don’t even see the correct MAC Address (that I know of)
Have you opened a tac case to help you debug?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-23-2017 10:12 AM
How are you profiling them? What methods are you relying on?
Is it at least profiling as an apple-device?
Are you redirecting to a portal to get the http user agent string for intitial login to help profile them? With ASA we don’t have DHCP or HTTP Sensor we don’t even see the correct MAC Address (that I know of)
Have you opened a tac case to help you debug?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-24-2017 06:27 PM
I would expect the same issue with Android 6 and above due to the newer mobile operating systems are not permitting AnyConnect to access the device's real MAC addresses.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-28-2017 08:38 AM
Thanks hslai and Jason.
I found this guide.
https://communities.cisco.com/docs/DOC-68156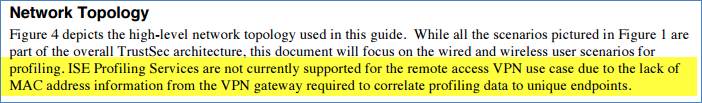
Doing some tests today to find out if ISE does not support profiling in Androids and iOS via AnyConnect VPN.
Any other feedback is welcomed.
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-28-2017 02:01 PM
For Androids it will depend on whether the client connects over mobile wireless or local WiFi. Depending on Android version, we may be able to capture MAC address for latter. The attributes are sent from AnyConnect through ASA and communicated to ISE as RADIUS TLVs. If unable to capture MAC address, then we cannot correlate to specific endpoint in ISE. We are looking at different methods to correlate endpoints over VPN, but shorter term client type may prevent more detailed profiling. You can leverage the mdm-tlv attributes sent in the RADIUS request to provide custom access based on OS type (windows, ios, mac os, android).
/Craig
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

