- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Modification of Self-Register Portal Workflow
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-07-2019 01:45 AM - edited 02-07-2019 01:48 AM
Hi Cisco Community,
i've a question regarding to the guest portals strategy of the Cisco ISE. None of the existing workflows really fit our needs. We're a university with several locations and buildings. At the moment we provide a WLAN SSID on demand of the conference owner. This SSID is limited in time and location (we use AP Groups on our WLAN controller). All these steps are done manually. To take a step into future, we want to broadcast a single guest WLAN SSID all over our campus. To minimize the administrative work we want to use a self-register portal. As we want to broadcast the SSID everywhere, everyone would be able to register himself on our wlan. To prevent this, we think about something like a 'Conference Code'. A password which is different from conference to conference. This 'Conference Code' should be visible (printed on paper i.e.) on the locations of the conference.
This conference code will be generated and distributed by our IT staff to the organization of the conference, which need to have access to the guest wlan.
After the guest enters the conference code, he/she must go through the self-register portal procedure as it might be necessary to track guests in case of law violation.
I saw that it is possible the set a AUP password. But only in the HotSpot Mode, where no self-register process is linked.
Maybe someone of you have a clue to solve my problem.
Thank you and best regards from Germany
Florian
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-07-2019 07:55 AM
https://community.cisco.com/t5/security-documents/ise-guest-amp-web-authentication/ta-p/3657224#toc-hId--2096579123
Linking one guest portal to another guest portal (ability to choose another portal)
ISE Hotspot portal with links to employee or vendor portals
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-07-2019 02:24 AM
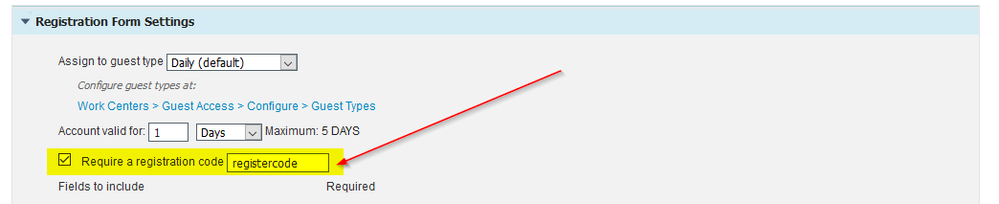
Ok. I found a first possible step to solution. You can set a register code at the self-service registration form settings.
Maybe i'm able to set to set the code via rest-api.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-07-2019 03:32 AM
Hey @florian.hahner1
Another slightly related option to your multi-factor Guest network, might be to use a Pre-Shared Key WLAN Profile instead of an Open SSID. Since the user has to type in *something* anyway, why not make them type the PSK of the SSID in? That has the positive side effect of encrypting the connection as well (PSK only known to people who physically see the key written down, and not the hacker in the car park)
Just a thought. And that PSK can be localised per location, and per WLC in that location. I don't know if WLC supports REST API (I doubt it) but it could be scripted via ssh commands.
Once the user has typed in the PSK, they are redirected immediately to the self registration portal.
Another benefit of this method is that you don't get hundreds of MAB auths on your Radius server, because the client has to associate to the SSID first before the MAB auth can be done. It's a protection layer for your ISE platform too :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-07-2019 07:55 AM
https://community.cisco.com/t5/security-documents/ise-guest-amp-web-authentication/ta-p/3657224#toc-hId--2096579123
Linking one guest portal to another guest portal (ability to choose another portal)
ISE Hotspot portal with links to employee or vendor portals
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-07-2019 08:07 AM
https://community.cisco.com/t5/security-documents/ise-guest-amp-web-authentication/ta-p/3657224#toc-hId--1043955036
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide