- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Wired Device not authenticating
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Wired Device not authenticating
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-31-2018 08:29 AM
this is a device that i am just trying to mab into an endpoint group. As soon as I put the mab/dot1x port configuration on the interface I can't reach the device, and show auth sess doesn't have a session for the interface. If i debug radius authentication i get no output for that device either. as soon as I default the interface and put it into the data vlan the device is reachable
I've tried adding authentication open and removing dot1x pae authenticator to the port.
Is there something else i could do to get the device to authenticate?
here's the standard port configuration i'm using.
interface GigabitEthernet2/0/8
switchport access vlan 1049
switchport mode access
switchport voice vlan 2049
authentication event fail action next-method
authentication event server dead action authorize vlan 1049
authentication event server dead action authorize voice
authentication event no-response action authorize vlan 1049
authentication event server alive action reinitialize
authentication host-mode multi-auth
authentication order dot1x mab
authentication priority dot1x mab
authentication port-control auto
authentication periodic
authentication timer reauthenticate server
authentication timer inactivity server dynamic
authentication violation restrict
mab
dot1x pae authenticator
dot1x timeout tx-period 3
dot1x max-reauth-req 3
spanning-tree portfast
spanning-tree bpduguard enable
- Labels:
-
Identity Services Engine (ISE)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-31-2018 08:58 AM
Please follow our best practice configuration guidance and troubleshooting steps in the ISE Wired Access Deployment Guide.
You have not included the ISE LiveLog status/details to know how ISE is authorizing the endpoint.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-31-2018 02:24 PM
I don't think this is your problem, but you cannot use this command when doing multiauth:
authentication event server dead action authorize vlan 1049
So your fail open will not work. In multiauth, you should be using:
authentication event server dead action reinitialize vlan 1049
That may have changed but I don't think so. If you are in open mode then those commands aren't needed.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-31-2018 07:06 PM
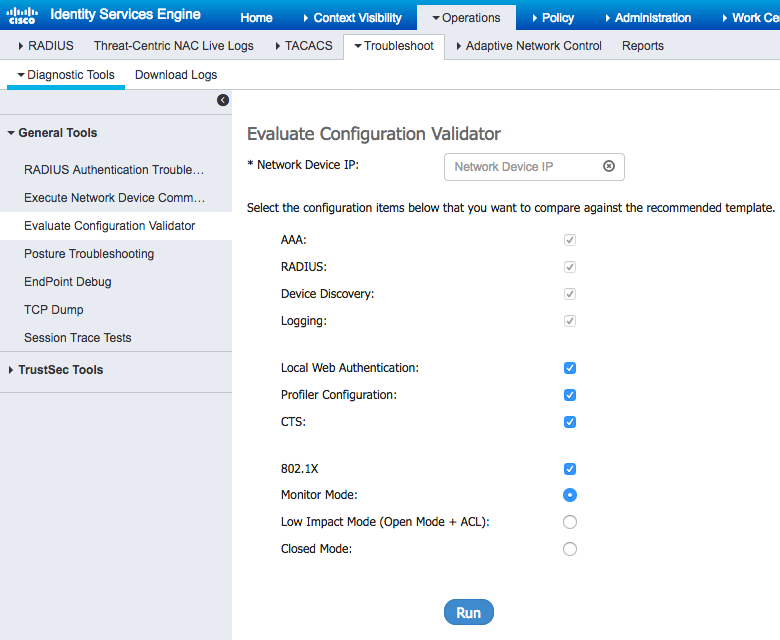
If the switch is one of the classic 3K models and running an older IOS release (e.g. 12.2(55)SE10), then you may try this ISE tool "Evaluate Configuration Validator"
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide