- Cisco Community
- Technology and Support
- Networking
- Network Management
- Re: 5506-X in packet tracer can't configure global policy/policy map
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
5506-X in packet tracer can't configure global policy/policy map
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-01-2021 12:46 PM - edited 08-01-2021 12:49 PM
I am working on a project in Packet Tracer, and I'm running into an issue where I am unable to edit the global policy of the 5506 firewalls I have configured.
When I issue the command "policy-map global_policy", it returns "ERROR: policy-map/policy-map of different type exists."
Is there any way to fix this? I have posted the config below
ASA Version 9.6(1)
!
hostname CambridgeFW
names
!
interface GigabitEthernet1/1
nameif OUTSIDE
security-level 0
ip address 10.1.1.1 255.255.255.0
duplex full
speed 1000
!
interface GigabitEthernet1/2
nameif INSIDE
security-level 100
ip address 192.168.129.2 255.255.255.0
duplex full
speed 1000
!
interface GigabitEthernet1/3
nameif DMZ
security-level 50
ip address 192.168.131.1 255.255.255.0
duplex full
speed 1000
!
interface GigabitEthernet1/4
nameif WIRELESS
security-level 25
ip address 192.168.132.2 255.255.255.0
duplex full
speed 1000
!
interface GigabitEthernet1/5
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/6
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/7
no nameif
no security-level
no ip address
shutdown
!
interface GigabitEthernet1/8
no nameif
no security-level
no ip address
shutdown
!
interface Management1/1
management-only
no nameif
no security-level
no ip address
shutdown
!
object network DMZ
subnet 192.168.131.0 255.255.255.0
object network INSIDE
subnet 192.168.128.0 255.255.255.0
object network WIRELESS
subnet 192.168.133.0 255.255.255.0
object network ftpserver
host 192.168.131.5
object network ftpserver-external-ip
host 10.10.10.10
!
!
access-list OUTSIDE extended permit icmp any any echo-reply
access-list OUTSIDE extended permit icmp any any unreachable
access-list OUTSIDE_acl extended permit icmp any any unreachable
access-list OUTSIDE_acl extended permit icmp any any echo-reply
access-list OUTSIDE_acl extended permit icmp any any echo
!
!
access-group OUTSIDE_acl in interface OUTSIDE
object network DMZ
nat (DMZ,OUTSIDE) dynamic interface
object network INSIDE
nat (INSIDE,OUTSIDE) dynamic interface
object network WIRELESS
nat (WIRELESS,OUTSIDE) dynamic interface
object network ftpserver
nat (DMZ,OUTSIDE) static 10.10.10.10
!
!
!
class-map inspection_default
match default-inspection-traffic
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect tftp
!
service-policy global_policy global
!
telnet timeout 5
ssh timeout 5
!
!
!
!
router rip
version 2
network 10.0.0.0
network 192.168.128.0
network 192.168.129.0
network 192.168.130.0
network 192.168.131.0
network 192.168.132.0
network 192.168.133.0
!
- Labels:
-
Network Management
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-08-2022 06:16 AM
I've just come across this issue myself, what I found worked was deleting the global policy on there, then remaking it using the same names and specifications, then using the "service-policy [global_policy] global" command to make that policy the global one for all interfaces.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-22-2022 02:42 PM - edited 09-22-2022 02:43 PM
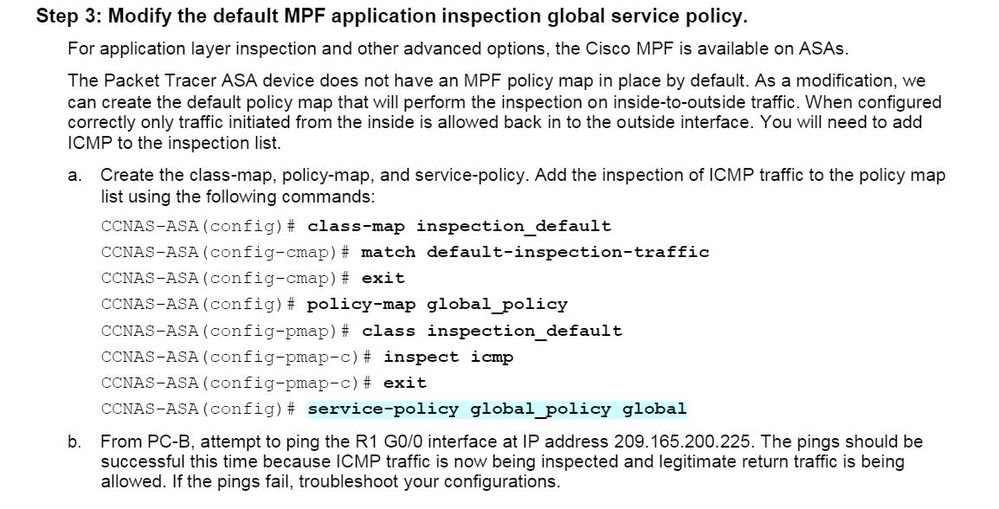
Hi Juno, i finally found how to proceed to deal with the default policy, here you are !
ASA#configure terminal
ASA(config)#class-map inspection_default
ASA(config-cmap)#match default-inspection-traffic
ASA(config-cmap)#exit
ASA(config)#policy-map global_policy
ASA(config-pmap)#class inspection_default
ASA(config-pmap-c)#inspect icmp
ASA-(config-pmap-c)#exit
ASA-(config)#service-policy global_policy global
WARNING: Policy map global_policy is already configured as a service policy
ASA-#write memory
Building configuration...
Cryptochecksum: 7f7e5eff 17ca58f0 3e980f41 6195021d
1929 bytes copied in 1.427 secs (1351 bytes/sec)
[OK]
ASA-#
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-26-2022 12:02 AM
ciscoasa#conf t
ciscoasa(config)#policy
ciscoasa(config)#policy-map global_policy
ERROR: policy-map/policy-map of different type exists.
ciscoasa(config)#class-map
ciscoasa(config)#class-map inspec
ciscoasa(config)#class-map inspection-default ?
<cr>
ciscoasa(config)#class-map inspection-default
ciscoasa(config-cmap)#match default-ins
ciscoasa(config-cmap)#match default-inspection-traffic
ciscoasa(config-cmap)#exit
ciscoasa(config)#policy-map
ciscoasa(config)#policy-map global_policy
ERROR: policy-map/policy-map of different type exists.
ciscoasa(config)#
How can you config global_policy? I've tried in PKT 8.2 and not working
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-26-2022 09:08 AM
Hi, Sorry but the version i used 8.2 seems to be buggy.
I finally just deleted the policy and recreated it
It seems we cant update the present one.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-26-2022 09:12 AM
I face same issue
delete the policy global default
add it again with add inspection you need
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-21-2022 07:56 AM
Thank you Juno !!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide