- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: ASA-5585-X SSP20
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2020 12:04 AM - edited 06-30-2020 12:10 AM
Dear Experts
I am replacing the 5585-X firewall with the newest NGFW,, actually i want to know the current throughput ( i am not mentioning sh cpu history information which will display the how much high the cpu went in peak hrs ) on 5585-X SSP20 instead a command that will show me throughput currently the firewall is utilizing.
Awaiting expert advise
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2020 03:12 AM
The "show traffic" command that @balaji.bandi mentioned is the best cli command we have available for this purpose. It's only a snapshot though so an NMS graph is generally a much better indicator.
If you have a good feel for the current and expected overall throughput needed we (partners or Cisco SEs) can plug it into a tool to tell you which model is recommended.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2020 01:04 AM
#show traffic - show you the traffic on an interface,
if you have any NMS and you monitoring the ASA interface that also gives you historic information.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2020 01:45 AM
Dear Balaji
Thanks for the reply,
lets assume the interface utilization for all FW interface for a 12 months is 25% then what will be your suggestion i should reduced the sizing of the firewall???
Apart from the sh cpu history i was also having interface utilization summary as well in my mind but i m looking for one command output to show the throughput , i m just asking on fly i am not sure it is available in Cisco thats the reason i m looking for experts advise.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2020 03:12 AM
The "show traffic" command that @balaji.bandi mentioned is the best cli command we have available for this purpose. It's only a snapshot though so an NMS graph is generally a much better indicator.
If you have a good feel for the current and expected overall throughput needed we (partners or Cisco SEs) can plug it into a tool to tell you which model is recommended.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-30-2020 04:00 AM
lets assume the interface utilization for all FW interface for a 12 months is 25% then what will be your suggestion i should reduced the sizing of the firewall???
May not be the case the way you thinking, we need to see always Peak point when we look performance point of view (rather average) - this is what i will be thinking right approach, But different people have different approaches.
As @Marvin Rhoads suggested here, if you are not sure about new model is not right choice,Contacting Local Cisco SE probably best person for you to suggest the model, since they understand your network and requirement.
we only suggest based on the input you provided, some time may not be workable for you. Best to protect your investment buying new models, involve your cisco partner.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-01-2020 10:16 AM
Dear Balaji and Marvin
Thanks for the reply.
you both are on the leaders board and have good experience for me you both are the online cisco SE , can you tell me what will the questionnaire that will be asked to me (customer) by an local SE for proposing the Core firewall.
Please advise.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-01-2020 10:33 AM
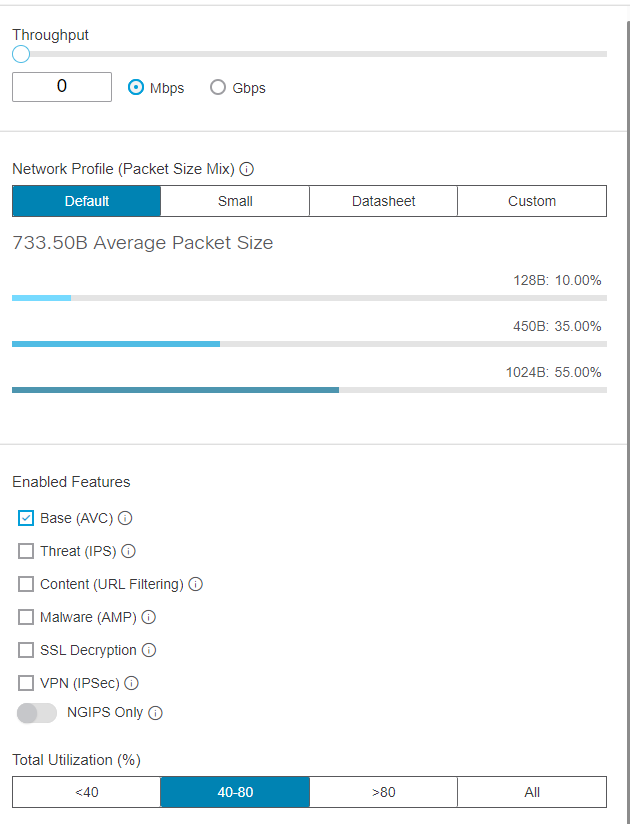
The primary inputs are overall throughput and enabled features.
Here's the tool's input section FYI:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-01-2020 01:22 PM
Dear Marvin
Can you share the link for the sizing, i will try to get access from my local cisco.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-02-2020 12:58 AM
@adamgibs7 the tool is restricted to users with staff or partner level access only. It uses your cisco.com credentials (CCO ID) to confirm.
It is at https://ngfwpe.cisco.com
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-03-2020 01:51 PM
Dear Marvin
thanks for the reply and link
one question in my my mind if I have 10 web server in my DMZ the uplink from these DMZ switches should be 10G or 1G, on basis of what factors this is been decided. Pls correct me if I m wrong one factor is that hence my internet bandwidth
is 500mbps so is it 10G connection from DMZ switches to firewall make sense??? Also I would like to understand we shld not forget that my internal users will also access web server so is it good to keep 10G.
Also remembering the thumb of rule Cisco says when u have 48 port switch the uplink shld be of mathematics 20:1 that means 20 user port than 1G uplink is sufficient.so if we have 48 port switch than 3G uplink is more than enough.
pls advise
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-03-2020 07:46 PM
If the primary users of your web servers are Internet-based and your Internet link is 500 Mbps then a 1 Gbps uplink from your DMZ switch is more than enough. If the internal users are the primary users then you might want to consider making the DMZ switch to firewall uplink 10 Gbps (and the inside network to DMZ as well). Ideally you would have a baseline of current traffic (like from an NMS like PRTG or SolarWinds Orion NPM) to better inform your design decisions going forward.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-04-2020 08:21 AM - edited 07-05-2020 09:24 PM
Dear Marvin
Thanks for the reply,, Please share your experience. One last query and then i will marked as answered
Does in real world scenario the front end web servers on DMZ are accessible from internal users as well ??? or for internal corporate users organization can have a different front end server with different server IP address but with same html web page contents but in back end the DMZ web server and the internal Web Server are hitting to the same application server and then the database server.
As per the attached Diagram what is the key factors that has to be considered when deciding the interfaces ( speed 10G or 1G) between the DC firewall and intermediate switch and from intermediate switch to the perimeter firewall.
thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-05-2020 04:09 AM
How the servers are laid out depends a lot on what the application and services architecture looks like. Security best practices would have public-facing servers in a DMZ serving only external users.
In the "real world". whether or not they serve content to both internal and external users varies. Smaller organizations may not have the resources for separate servers. Some designs may require internal and external users access the same content on the same servers.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-05-2020 09:26 PM
Dear Marvin
you missed my 2nd question in my previous post.
As per the attached Diagram what is the key factors that has to be considered when deciding the interfaces ( speed 10G or 1G) between the DC firewall and intermediate switch and from intermediate switch to the perimeter firewall.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-05-2020 10:33 PM
The key factor when choosing interface type and number in a design is the required throughput, both current and including margin for anticipated growth during the expected lifetime of the design.
Secondary factors include budget, existing available interfaces (if any), physical constraints (availability of fiber runs, expansion capacity of the devices etc.), logical constraints (i.e. do both sides of a link support Etherchannels, how might that work with any HA scheme also in the design) etc.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide